嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我得通读一下文章内容。文章讲的是永利度假村被黑客入侵,员工数据被盗。黑客来自ShinyHunters勒索团伙。永利已经启动了应急响应程序,并且在外部专家的帮助下进行调查。他们提到数据已经被删除,但没有说明是否支付了赎金。同时,永利为员工提供了免费的信用监控和身份保护服务。 接下来,我需要提取关键信息:公司名称、事件、数据类型、黑客组织、应对措施、赎金情况、影响范围和补救措施。然后把这些信息浓缩成一句话,确保不超过100字。 可能会遇到的问题是如何简洁地表达所有要点而不遗漏重要信息。比如,“员工数据”包括PII和社会安全号码等,这些细节可以简化为“员工数据”。同时,“启动调查”和“提供服务”是应对措施的关键点。 最后,确保语言流畅自然,避免使用过于正式或复杂的词汇。 </think> 永利度假村确认黑客入侵其系统并窃取员工数据后启动调查,并声称攻击者确认数据已被删除。公司未透露是否支付赎金,并为员工提供免费信用监控服务。 2026-2-24 22:0:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:12 收藏

Wynn Resorts has confirmed that a hacker stole employee data from its systems after the company was listed on the ShinyHunters extortion gang's data leak site.
In a statement shared today, the company said it activated its incident response procedures and launched an investigation, with assistance from external cybersecurity experts, after discovering the breach.
"We have learned that an unauthorized third party acquired certain employee data," reads a statement shared with BleepingComputer.
"Upon discovery, we immediately activated our incident response protocols and launched a thorough investigation with the help of external cybersecurity experts."
While Wynn has not stated whether it paid a ransom to prevent the data leak, the company said the attackers confirmed the stolen data had been deleted. In past extortion cases, threat actors have typically only claimed data was deleted after reaching an agreement with a victim.
"The unauthorized third party has stated that the stolen data has been deleted. We are monitoring and to date have not seen any evidence that the data has been published or otherwise misused," the statement continued.
The company added that the incident did not impact guest operations or its physical properties, which remain fully operational, and that it is offering complimentary credit monitoring and identity protection services to employees.
ShinyHunters leak site listing
This statement comes after Wynn Resorts appeared on the ShinyHunters data leak site on Thursday.
In the threat actors' post, the group claimed it had stolen "PII (SSNs, etc) and employee data" and warned the company to make contact before February 23, 2026, or the data would be published.
"Over 800k records containing PII(SSNs, etc) and employee data have been compromised," reads the now-deleted post on ShinyHunters data leak site.
"This is a final warning to reach out by 23 Feb 2026 before we leak along with several annoying (digital) problems that'll come your way. Make the right decision, don't be the next headling."
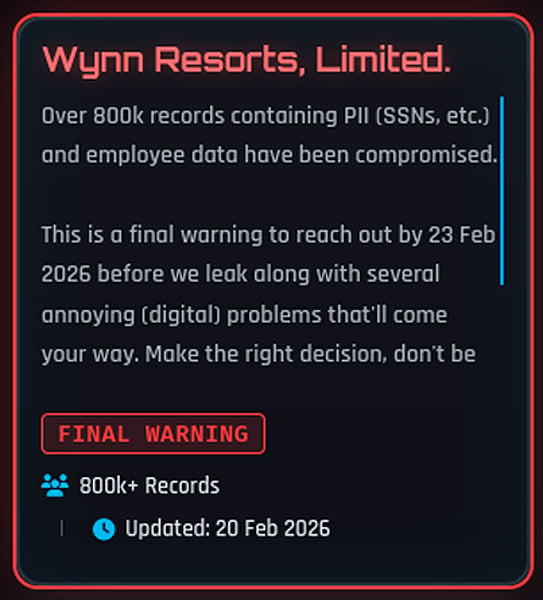
Shortly after, the Wynn entry was removed from the site, a move that often occurs when negotiations are underway or claims are disputed.
Wynn Resorts did not answer questions about whether a ransom was paid or how many people were affected. Similarly, ShinyHunters told BleepingComputer that they had no comment on whether they received a payment.
However, the threat actors did previously claim to have stolen the data from the company's Oracle PeopleSoft environment.
ShinyHunters is a data extortion group known for breaching organizations and threatening to publish stolen data unless a ransom is paid.
The group has previously claimed responsibility for multiple high-profile data theft incidents and has operated across various underground forums and extortion portals over the years.
Last year, ShinyHunters conducted a widespread campaign to steal Salesforce data, targeting numerous companies through social engineering and stolen third-party OAuth tokens.
In recent weeks, ShinyHunters has claimed responsibility for a wave of other security breaches, including Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, and online dating giant Match Group.
Some of the victims were compromised through voice phishing (vishing) attacks targeting single sign-on (SSO) accounts at Google, Microsoft, and Okta, where the threat actors posed as IT support staff to trick employees into entering credentials and multi-factor authentication (MFA) codes on phishing sites.
As BleepingComputer first reported, the ShinyHunters group more recently adopted device code vishing to obtain Microsoft Entra authentication tokens.
After stealing their targets' credentials and auth codes, the threat actors hijack the victims' SSO accounts to steal data from connected SaaS applications such as Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and many others.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

