好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得通读全文,抓住主要信息。 文章开头提到OWASP在2010年将“未验证的重定向和转发”加入Top 10列表,后来在2013年合并到“敏感数据泄露”中。这说明这是一个重要的安全问题。 接下来,文章讨论了开放重定向常被忽视,影响不被理解。最初看起来不严重,但其实有风险。比如用户点击可信链接后被重定向到恶意网站,这可能导致钓鱼攻击。特别是OAuth依赖重定向URL传递授权令牌,如果允许列表不严格,可能被利用。 然后,文章提到最近honeypots检测到大量针对重定向URL的扫描请求,例如/continue、/redirect等路径。图表显示2月份相关请求增加。大部分请求来自一个特定的IP地址,属于AS202425公司,注册在塞舌尔,被称为“保镖”主机提供商,因为其宽松的滥用政策。 最后,作者建议可能需要封禁该ASN,并提供了参考链接。 现在我要把这些信息浓缩到100字以内。需要包括OWASP的历史、开放重定向的风险、OAuth的影响、最近的扫描活动以及IP地址的情况。 可能的结构:OWASP在2010年加入的问题及其影响;开放重定向的风险;最近检测到的扫描活动;涉及的IP地址和建议封禁。 这样组织起来应该能在字数限制内涵盖主要内容。 </think> 文章讨论了未验证重定向和转发的安全风险及其演变。开放重定向常被忽视,但可能导致钓鱼攻击或敏感数据泄露。随着OAuth的普及,允许列表配置不当可能引发令牌泄露。近期检测到针对多种重定向URL的扫描增加,部分来自“保镖”主机提供商IP Volume(AS202425),建议封禁该ASN以降低风险。 2026-2-24 18:4:1 Author: isc.sans.edu(查看原文) 阅读量:24 收藏
In 2010, OWASP added "Unvalidated Redirects and Forwards" to its Top 10 list and merged it into "Sensitive Data Exposure" in 2013 [owasp1] [owasp2]. Open redirects are often overlooked, and their impact is not always well understood. At first, it does not look like a big deal. The user is receiving a 3xx status code and is being redirected to another URL. That target URL should handle all authentication and access control, regardless of where the data originated.
Historically, one of the main concerns was phishing. A user clicks on a link to a trusted URL, and is immediately redirected to a malicious phishing URL. The issue becomes trickier if trusted data sent via the URL is now forwarded to an untrusted destination with minimal user interaction. The vulnerability has become more important with the ubiquitous use of OAUTH. OAUTH relies on "redirect URLs" to pass an authorization token from the authorization server to the client. Best practice requires allowlisting specific URL patterns for the redirect URL, but an open redirect within the allow-listed URL range may be used to subvert the token.
Interestingly, recently our honeypots detected an increase in scans for various redirect-related URLs. For example:
/continue?url=http://testdomain.com
/redirect?url=http://testdomain.com
/away?url=http://testdomain.com
/goto?url=http://testdomain.com
/jump?url=http://testdomain.com
and others.

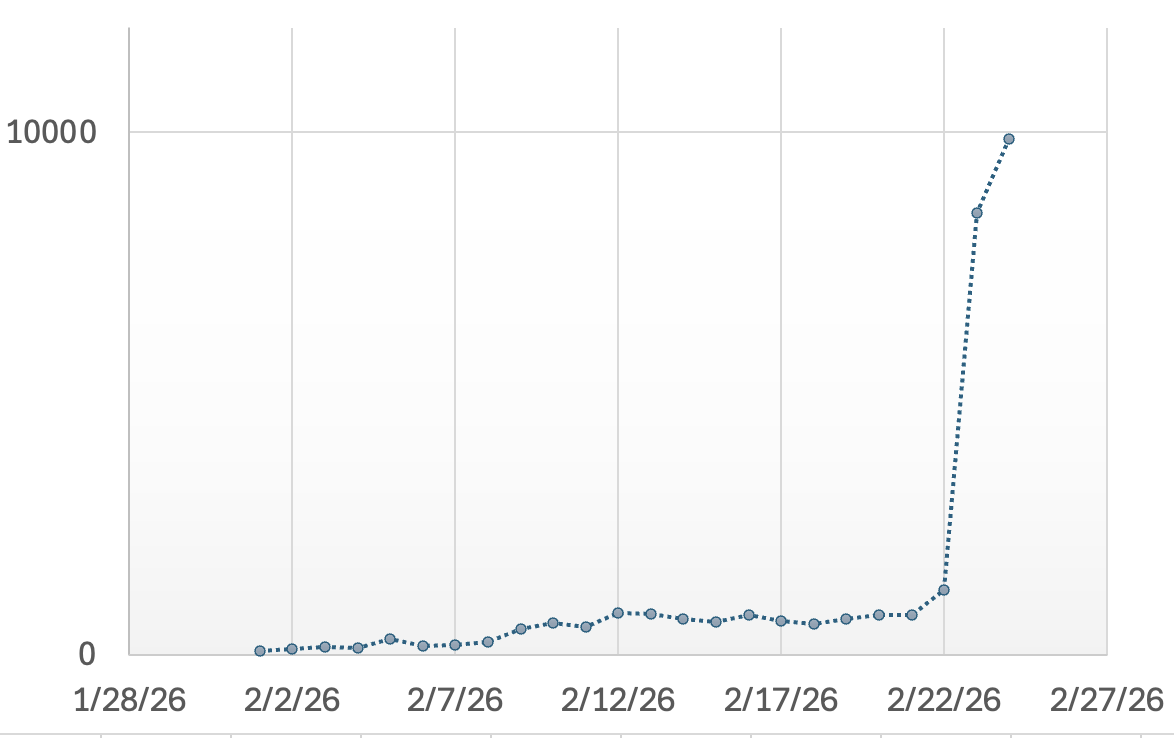
The graph shows the increase of redirect-related requests for February (only some of the URLs are captured in the graph).
Most of the requests currently originate from a single IP address, 89.248.168.239, registered to AS202425, IP Volume, a company registered in the Seychelles. IP Volume is often called a "bulletproof" hoster, preferred by various actors for their relaxed abuse policy. Not just because of these latest scans, a block of AS202425 may still be advisable [nytimes].
[[owasp1] https://github.com/OWASP/Top10/blob/master/2010/OWASP%20Top%2010%20-%202010%20English.pdf
[owasp2] https://cheatsheetseries.owasp.org/cheatsheets/Unvalidated_Redirects_and_Forwards_Cheat_Sheet.html
[nytimes] https://www.nytimes.com/interactive/2019/12/22/us/child-sex-abuse-websites-shut-down.html
--
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
如有侵权请联系:admin#unsafe.sh