好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,理解主要内容。 文章讲的是Arkanix Stealer,这是一种信息窃取恶意软件,出现在2025年底。它被推广在暗网论坛上,作为MaaS(恶意软件即服务)提供。研究人员认为它是AI辅助的实验,开发时间短,很快就停止了运营。 文章提到Kaspersky的研究人员在10月发现了广告,里面有Discord服务器作为沟通渠道。传播方式可能是钓鱼攻击,利用社会工程学手段。这个恶意软件用C++编写,嵌入了ChromElevator来窃取数据,并且有Python版本。它能收集系统信息、浏览器数据、加密钱包信息等,并加密外发数据。 此外,Arkanix Stealer支持动态功能更新,使用了反分析技术,并且有自毁机制。它的基础设施包括两个Cloudflare保护的域名。开发者还运行了一个公开论坛,有更新、调查和推荐计划,看起来像一个市场化的软件产品。 最后,Kaspersky提供了IoCs列表。 现在我要把这些要点浓缩到100字以内:Arkanix Stealer是2025年出现的AI辅助信息窃取恶意软件,在暗网推广为MaaS服务。它通过钓鱼攻击传播,支持多种浏览器和钱包的数据窃取,并使用加密技术隐藏自身。由于AI辅助开发时间短,在运行一段时间后关闭。 </think> Arkanix Stealer是一种于2025年底出现的AI辅助信息窃取恶意软件,在暗网论坛上作为MaaS服务推广。它通过钓鱼攻击传播,支持多种浏览器和加密钱包的数据窃取,并使用加密技术隐藏自身。由于AI辅助开发时间短,在运行一段时间后关闭。 2026-2-24 10:52:56 Author: securityaffairs.com(查看原文) 阅读量:18 收藏
Arkanix Stealer: AI-assisted info-stealer shuts down after brief campaign
Pierluigi Paganini
February 24, 2026

Arkanix Stealer surfaced in late 2025 as a short-lived info-stealer, likely built as an AI-assisted experiment and quickly abandoned.
Arkanix Stealer emerged in late 2025 as a short-lived information-stealing malware promoted on dark web forums. Researchers believe it was likely created as an AI-assisted experiment, suggesting the operators were testing automated development techniques rather than running a long-term, large-scale cybercriminal operation.
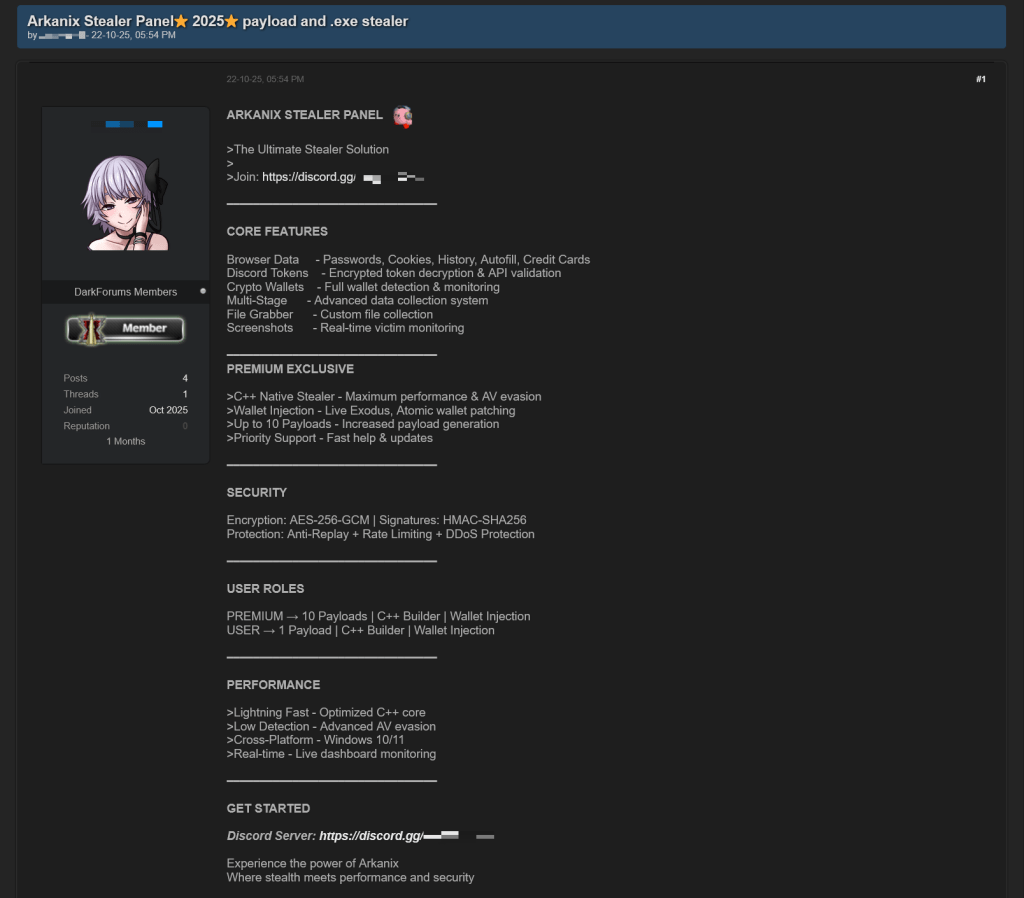
In October 2025, Kaspersky researchers spotted dark web ads for ‘Arkanix Stealer,’ a MaaS offering with a control panel and configurable payloads. It used a C++ build embedding ChromElevator to steal system and crypto wallet data, plus a packed Python version with dynamic configuration. Likely spread via phishing-themed lures, the operation appeared short-lived, and its affiliate program was later shut down.
The ads include a link to a Discord server used as the primary communication channel.
The initial infection vector remains unclear, but phishing-themed loaders suggest social-engineering attacks. A Python loader downloads and runs the Arkanix stealer after installing required packages, registering the victim machine with its C2, and fetching the payload. The stealer supports dynamic feature updates from the panel and deploys an additional dropper before data theft. It collects extensive system details, browser data (passwords, cookies, crypto-related info), Telegram sessions, Discord credentials, VPN data, and selected user files, packing results into archives for exfiltration.
“This stealer is capable of extracting various types of data from supported browsers (22 in total, ranging from the widely popular Google Chrome to the Tor Browser). The list of supported browsers is hardcoded, and unlike other parameters, it cannot be modified during execution.” reads the report published by Kaspersky. “In addition to a separate Chrome grabber module (which we’ll discuss later), the stealer itself supports the extraction of diverse information, such as:
- In case of Chromium-based browsers, 0Auth2 data is also extracted”
- Browser history (URLs, visit count and last visit)
- Autofill information (email, phone, addresses and payment cards details)
- Saved passwords
- Cookies”
Extra modules, including wallet tools and HVNC, can be decrypted and deployed. After completing operations, it deletes itself and related artifacts.
Researchers analyzed both debug and release builds of the native C++ Arkanix Stealer. The release version used VMProtect and the arkanix[.]pw C2, while the debug build relied on a Discord bot and extensive logs. The malware supports anti-analysis checks, patches AMSI and ETW, and steals system, RDP, gaming, browser and screenshot data. It embeds the ChromElevator browser extractor for credential theft and encrypts exfiltrated data with AES-GCM + PBKDF2. The infrastructure observed by the experts included two domains behind Cloudflare hosting a protected panel that was taken offline later.
The group promoted the stealer via Discord with marketing tactics, a referral program and promises of a crypter, suggesting short-lived, possibly AI-assisted development.
“Referrers were promised an additional free hour to their premium license, while invited customers received seven days of free “premium” trial use.” continues the report. “As stated in forum posts, the premium plan included the following features:
- C++ native stealer
- Exodus and Atomic cryptocurrency wallets injection
- Increased payload generation, up to 10 payloads
- Priority support
The stealer targeted users of cryptocurrency, gaming, and online banking, collecting sensitive data. Likely aided by LLMs, it was a quick, one-shot campaign for fast gains. The developers ran a public forum with updates, surveys, and a referral program, making Arkanix appear more like a marketed software product than a hidden malware operation.
“While being quite functional, it contains probable traces of LLM-assisted development which suggests that such assistance might have drastically reduced development time and costs.” concludes the report. “Hence it follows that this campaign tends to be more of a one-shot campaign for quick financial gains rather than a long-running infection.”
Kaspersky provides a list of indicators of compromise (IoCs).
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, malware)
如有侵权请联系:admin#unsafe.sh


