
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。用户的要求很明确,不需要用“文章内容总结”之类的开头,直接写描述即可。 首先,我得仔细阅读文章。文章主要讲的是荷兰电信公司Odido被ShinyHunters勒索团伙入侵,导致数百万用户数据泄露。ShinyHunters在暗网上公布了这些数据,并声称窃取了近2100万条记录。 接下来,我需要提取关键信息:ShinyHunters负责攻击,Odido是荷兰大型电信公司,泄露了大量用户数据,包括姓名、地址、电话号码、电子邮件、银行账户等。Odido已经向当局报告,并采取措施应对。ShinyHunters还威胁要泄露更多数据,并索要赎金。 然后,我要确保内容简洁明了,不超过100字。同时,避免使用复杂的术语,让读者一目了然。 最后,组织语言,确保信息准确且符合用户的要求。 </think> 荷兰电信公司Odido遭ShinyHunters勒索团伙入侵,数百万用户数据泄露。攻击者窃取了包括姓名、地址、电话号码、电子邮件和银行账户等信息,并在暗网上公布。Odido已向当局报告并采取措施应对威胁。 2026-2-24 11:45:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:5 收藏

The ShinyHunters extortion gang has claimed responsibility for breaching Dutch telecommunications provider Odido and stealing millions of user records from its compromised systems.
Odido is one of the largest telecommunications companies in the Netherlands and offers mobile, broadband, and television services to millions of customers nationwide.
The company disclosed the breach on February 12, revealing that attackers downloaded the personal data of many of its users after gaining access to its customer contact system on February 7. However, Odido added that no Mijn Odido passwords, call details, location, data, billing data, or scans of identity documents were exposed during the incident.
According to the telecom firm, the exposed information varies per customer and may include a combination of full name, address and city of residence, mobile number, customer number, email address, IBAN (bank account number), date of birth, and some identification details (passport or driver's license number and validity).
It also told local media at the time that the data breach affected 6.2 million customers and that the threat actors reached out to say they had stolen millions of user records.
After discovering the incident, Odido has reported the breach to the Dutch Data Protection Authority, blocked the attackers' access to its systems, and hired external cybersecurity experts to assist with incident response and mitigation.
An Odido spokesperson didn't provide further information on the incident when asked about which threat group was behind the attack and whether they demanded a ransom "due to the ongoing investigations."
While Odido has yet to attribute the attack, the ShinyHunters extortion gang has now added the company to its dark web leak site, claiming they've stolen nearly 21 million records containing data the company already revealed as exposed in the breach.
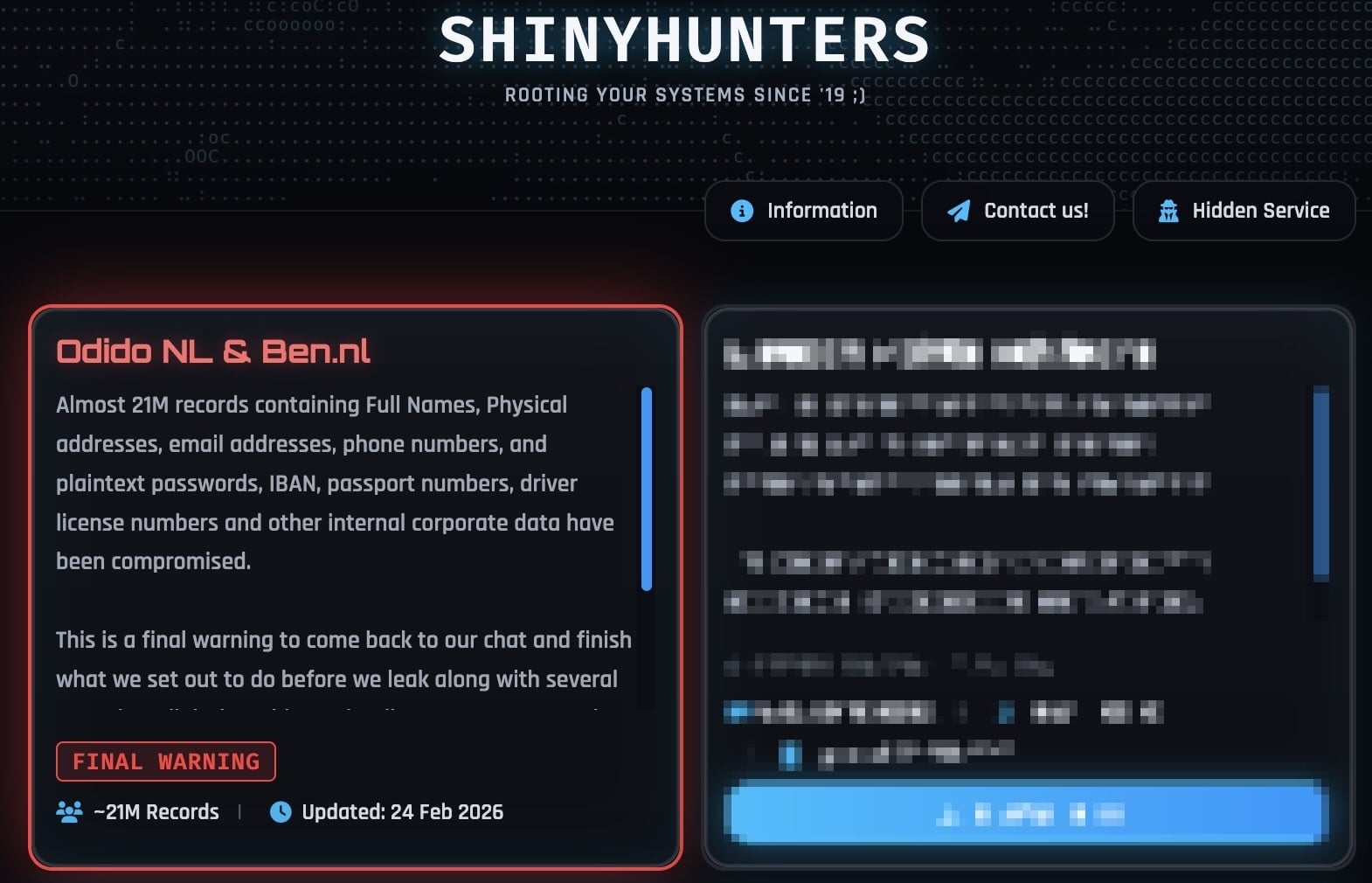
ShinyHunters also told BleepingComputer on Monday that the stolen data also contains internal corporate data and plaintext passwords.
"This is a final warning to come back to our chat and finish what we set out to do before we leak along with several annoying (digital) problems that'll come your way," the extortion gang says on the leak site. "Make the right decision, don't be the next headline. You know where to find us."
However, an Odido spokesperson denied their claims in a statement to BleepingComputer, reiterating that "no passwords, call details, social security numbers, or billing data are involved."
In recent weeks, ShinyHunters has claimed responsibility for a wave of other security breaches, including Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, and online dating giant Match Group (which owns the Tinder, Hinge, Meetic, Match.com, and OkCupid dating platforms).
Some of their victims had their systems compromised in voice phishing (vishing) attacks targeting single sign-on (SSO) accounts at Google, Microsoft, and Okta, where the threat actors call employees while impersonating IT support staff and trick them into entering credentials and multi-factor authentication (MFA) codes on phishing sites that mimic their companies' login portals.
As BleepingComputer first reported, the ShinyHunters group has also recently adopted device code vishing, abusing the OAuth 2.0 device authorization grant flow to obtain Microsoft Entra authentication tokens.
After stealing their targets' credentials and auth codes, the threat actors hijack the victims' SSO accounts to breach connected enterprise services like Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and many others.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

