好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是CISA警告Roundcube Webmail的两个漏洞被积极利用,要求美国联邦机构在三周内修复。Roundcube是一个基于网络的邮件客户端,自2008年起成为cPanel的默认界面。第一个漏洞CVE-2025-49113是远程代码执行,被利用后影响了84,000多个实例。第二个漏洞CVE-2025-68461是XSS攻击,通过SVG的animate标签。CISA将这两个漏洞加入已知被利用的漏洞目录,并要求联邦机构在3月13日前修复。 现在我要把这些信息浓缩到100字以内。重点包括:CISA警告、两个漏洞、远程代码执行和XSS、影响范围、修复期限。确保语言简洁明了,不使用开头词。 可能的结构:CISA警告Roundcube Webmail存在两个被积极利用的漏洞,涉及远程代码执行和XSS攻击,影响大量实例。要求联邦机构三周内修复以应对威胁。 检查字数是否符合要求,并确保所有关键点都涵盖。 </think> CISA警告Roundcube Webmail存在两个被积极利用的安全漏洞,涉及远程代码执行和XSS攻击,影响大量在线实例。要求美国联邦机构在三周内修复以应对恶意网络活动风险。 2026-2-23 11:45:18 Author: www.bleepingcomputer.com(查看原文) 阅读量:18 收藏
CISA flagged two Roundcube Webmail vulnerabilities as actively exploited in attacks and ordered U.S. federal agencies to patch them within three weeks.
Roundcube Webmail is a web-based email client that has been the default mail interface for the widely used cPanel web hosting control panel since 2008.
The first vulnerability tagged as actively abused by threat actors is a critical remote code execution flaw tracked as CVE-2025-49113, which was first flagged as exploited days after it was patched in June 2025, when Internet security watchdog Shadowserver warned that over 84,000 vulnerable Roundcube webmail installations were vulnerable to attacks.
Roundcube patched the second one (CVE-2025-68461) two months ago, in December 2025, warning that remote, unauthenticated attackers can exploit it through low-complexity cross-site scripting (XSS) attacks that abuse the animate tag in SVG documents.
"We strongly recommend to update all productive installations of Roundcube 1.6.x and 1.5.x with this new versions," the Roundcube security team warned when it released versions 1.6.12 and 1.5.12 that address this security flaw.
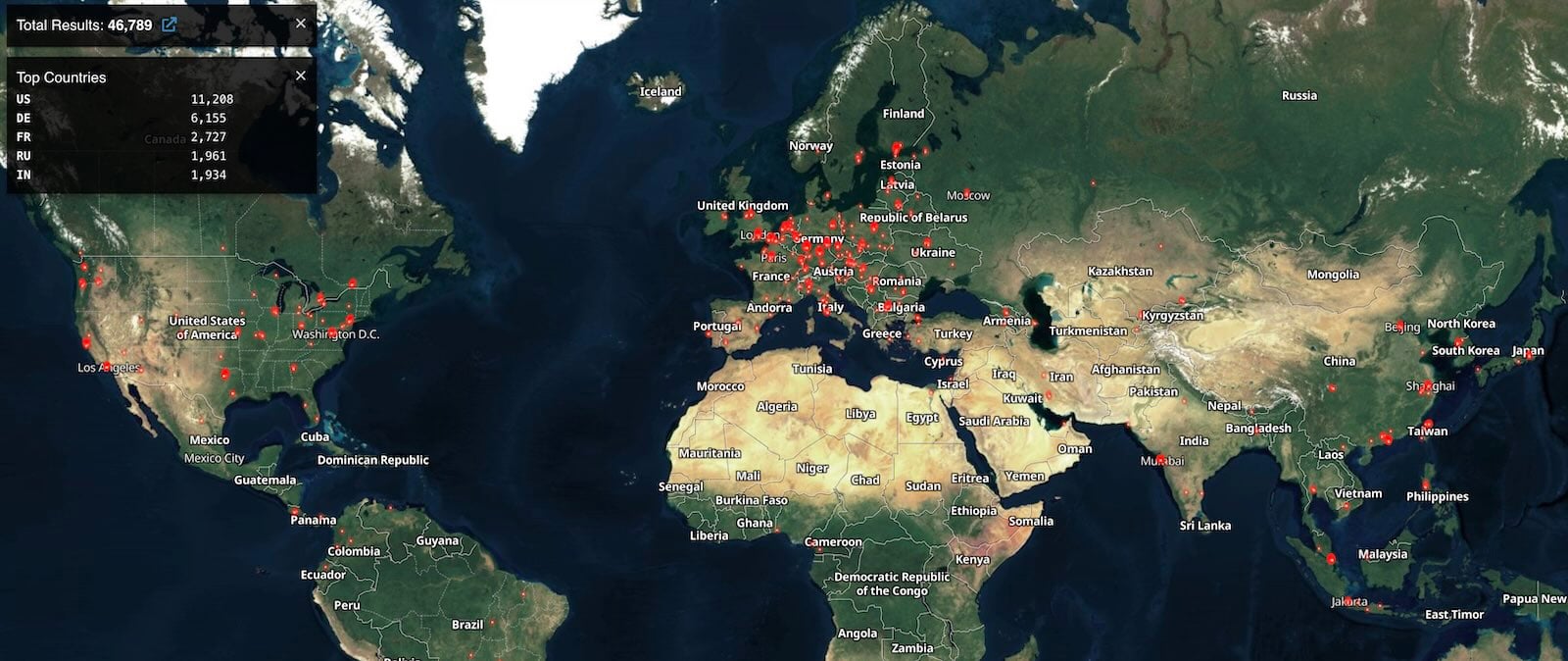
Shodan currently tracks over 46,000 Roundcube instances accessible on the internet. However, there is no information on how many of them are vulnerable to CVE-2025-49113 or CVE-2025-68461 attacks.
While it didn't provide any details on attacks exploiting these two security flaws, CISA added them to its Known Exploited Vulnerabilities (KEV) Catalog on Friday, warning that they are "frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise."
CISA also tracks ten other Roundcube Webmail vulnerabilities that are either actively exploited in attacks or have been abused in the past.
The U.S. cybersecurity agency has ordered Federal Civilian Executive Branch (FCEB) agencies to secure their systems against these security bugs within three weeks, by March 13, as mandated by a binding operational directive (BOD 22-01) issued in November 2021.
Roundcube vulnerabilities have been a popular target for cybercrime and state-sponsored threat groups, the most recent being a stored cross-site scripting (XSS) vulnerability (CVE-2023-5631) exploited by the Winter Vivern (TA473) Russian hacking group in zero-day attacks targeting European government entities and by the Russian APT28 cyber-espionage group to breach Ukrainian government email systems.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

