![]()
The world of mobile security is getting its very first dedicated online conference – and you’re invited! Get ready for summit dedicated entirely to mobile hacking, organized by Mobile Hacking Lab – a one of leading platform for offensive mobile security training and hands‑on exploitation labs. This free, online, two‑day event will be held on March 3 and 4, 2026, streamed live in the CET time zone. Whether you’re a mobile security researcher, pentester, malware analyst, DFIR expert, developer, student, or just curious, this conference brings you deep technical insights from top industry experts.
Register Now
Interest in the event is already impressive – over 2,000 participants have registered for the conference. “See you” on March 3 – 4, 2026!
Register for free here.
Giveaways & Interactive Activities
The Mobile Hacking Conference isn’t just about learning – it’s built for hands‑on engagement and rewards.
Premium Course Giveaway After Every Talk
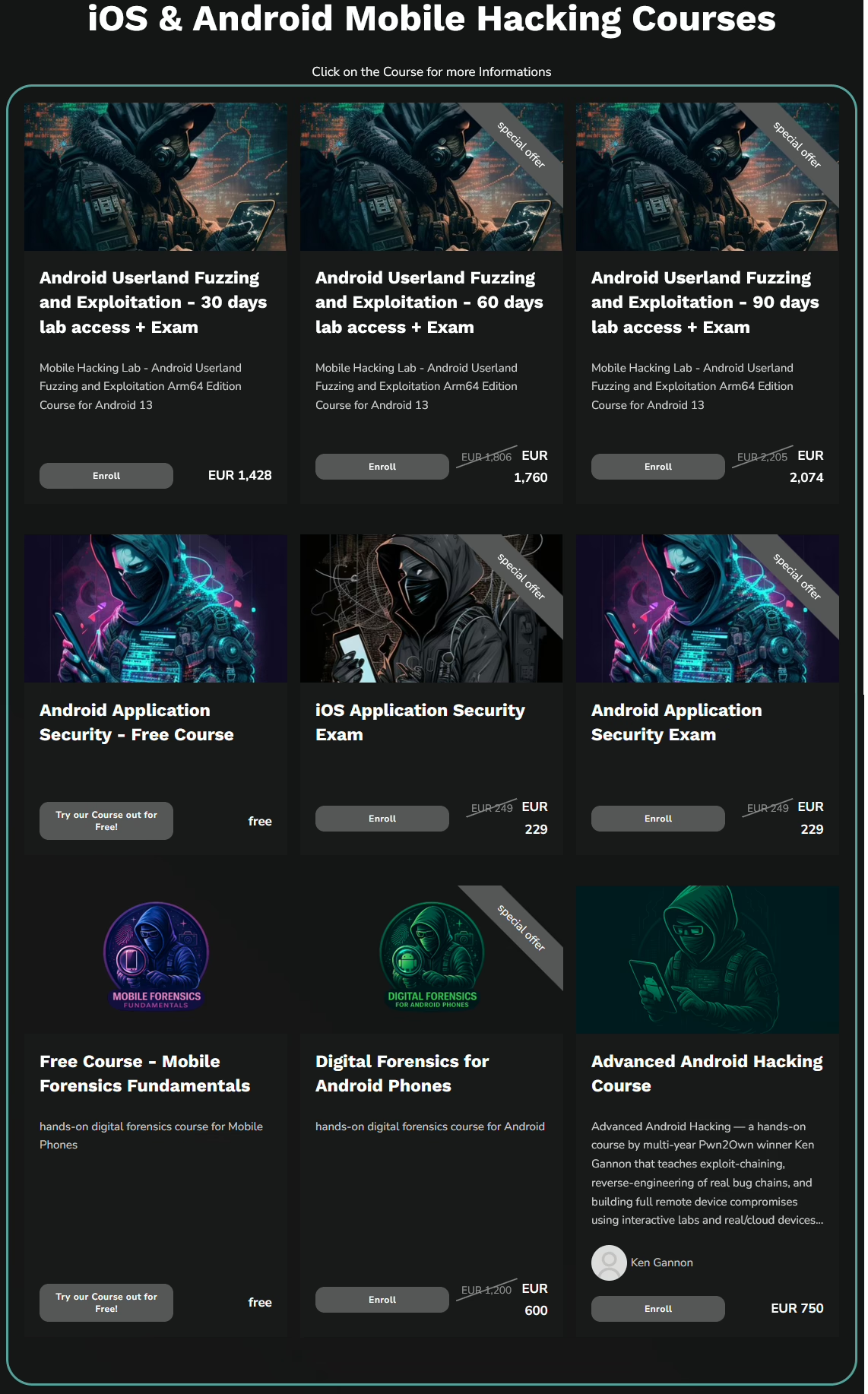
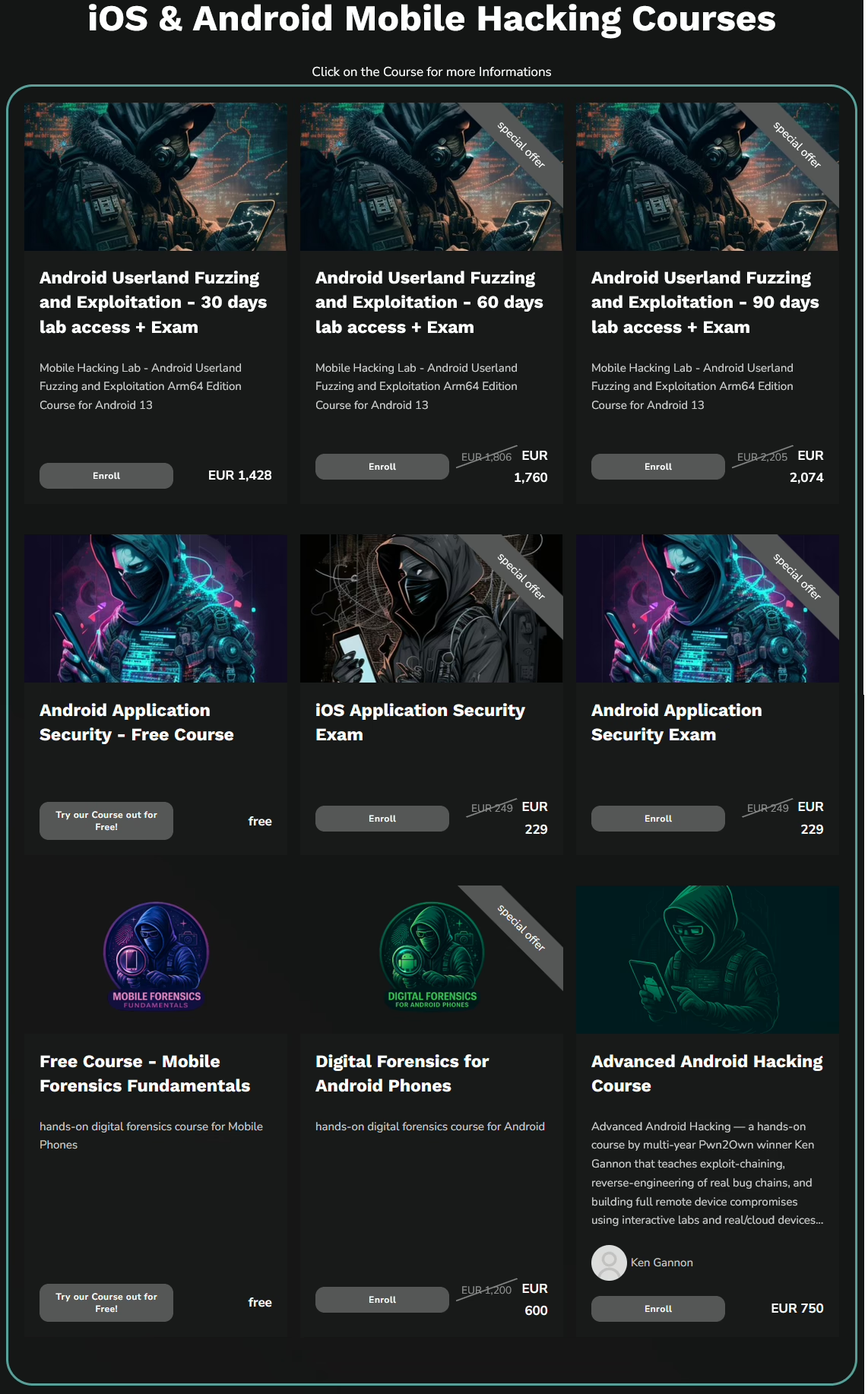
After each presentation, attendees can win a free premium course from MobileHackingLab (see Figure 1), known for its advanced mobile exploitation and application security training.
Capture‑the‑Flag (CTF) Competitions
A live, mobile‑focused CTF is part of the event program, featuring real exploitation challenges and prizes for top performers.
Meet the Speakers & Explore the Topic Areas
The conference features 12 speakers.
Day 1
- Djini in a Bottle: Faster Exploits, Same Chaos — Ken Gannon (Mobile Hacking Lab)
- Practical Heap Exploitation Against Android’s Scudo — Simon Janz (CODE WHITE GmbH)
- Breaking into Mobile Phones for Law Enforcement — Gersi Hajrullahi (Digital Forensics Specialist)
- Evolution of NFC Threats — Lukáš Štefanko (ESET)
- KYC Security Review and Bypassing Techniques — Juan Urbano Stordeur (Just Mobile Security)
- Traditional Pentest Meets AI: New Challenges in Android Security — Gabrielle Botbol (Independent)
Day 2
- Mobile Security Theater: Common Issues in Mobile Products — Miłosz Gaczkowski (Reversec)
- Deeplinks, URIs, and WebViews: Common URI Validation Pitfalls and Their Consequences — Lyes Mouloudi (Mobile Hacking Lab)
- From Install to Exfil: An Android Malware Journey — Dario Durando (ThreatFabric)
- Rapid Response: Windows DFIR with Velociraptor — Andreas Flamino (FlaminoIR)
- How I Clone Myself Using AI 5 Years Later: From Research to $25M Heists — Tamaghna Basu (DeTaSECURE)
- SAST‑Genius – Hybrid LLM Framework for Code Scanning — Vaibhav Agrawal (Google)