嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要用“文章内容总结”这样的开头。我得先仔细读一下这篇文章,理解它的主要内容。 文章讲的是作者收到的日本语系的钓鱼邮件,这些邮件冒充了ANA、DHL和myTOKYOGAS等公司。虽然作者自己没受影响,但对日语使用者可能有威胁。邮件中的链接和发件地址都用了.cn的域名,并且邮件头显示使用了Foxmail,这些都是相同的特征,说明是同一团伙所为。 接下来,我需要把这些要点浓缩到100字以内。要注意包括钓鱼邮件的目标、冒充的公司、使用的域名以及相同的技术特征。同时,语言要简洁明了。 可能的结构是:描述现象、提到冒充的公司、指出共同点(如.cn域名和Foxmail)、以及潜在威胁。这样就能在有限的字数内传达所有关键信息。 最后检查一下是否符合用户的要求:中文、100字以内、没有特定开头。确保没有遗漏重要信息。 </think> 作者收到多封冒充日本企业(如ANA、DHL和myTOKYOGAS)的钓鱼邮件,这些邮件使用.cn域名作为发件地址和钓鱼链接,并带有相同的技术特征(如X-mailer: Foxmail)。尽管作者未受影响,但这些邮件可能对日语使用者构成威胁。 2026-2-21 06:3:36 Author: isc.sans.edu(查看原文) 阅读量:24 收藏
Introduction
For at least the past year or so, I've been receiving Japanese-language phishing emails to my blog email addresses at @malware-traffic-analysis.net. I'm not Japanese, but I suppose my blog's email addresses ended up on a list used by the group sending these emails. They're all easily caught by my spam filters, so they're not especially dangerous in my situation. However, they could be effective for the Japanese-speaking recipients with poor spam filtering.
Despite the different companies impersonated, they all follow a similar pattern for the phishing page URLs and email-sending addresses.
This diary reviews three examples of these phishing emails.
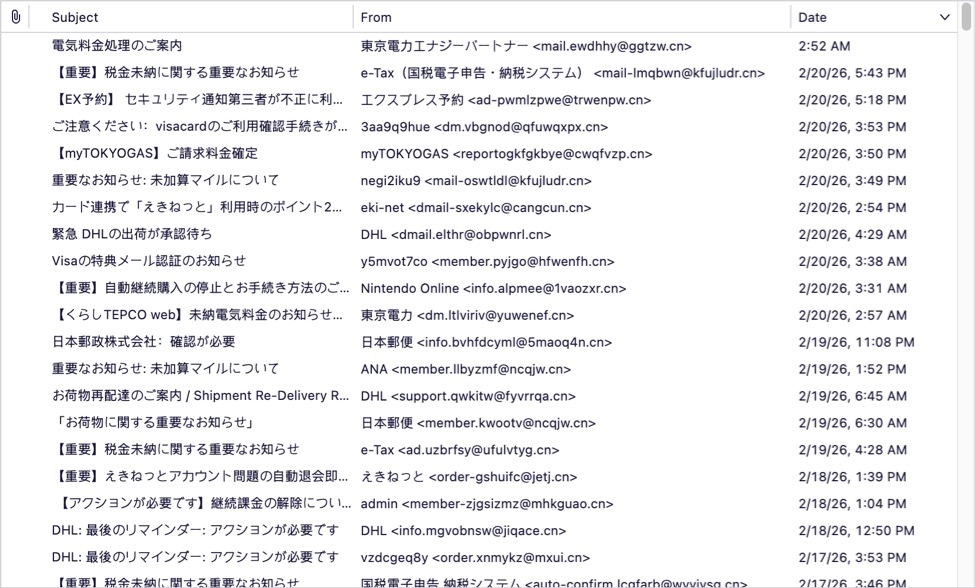
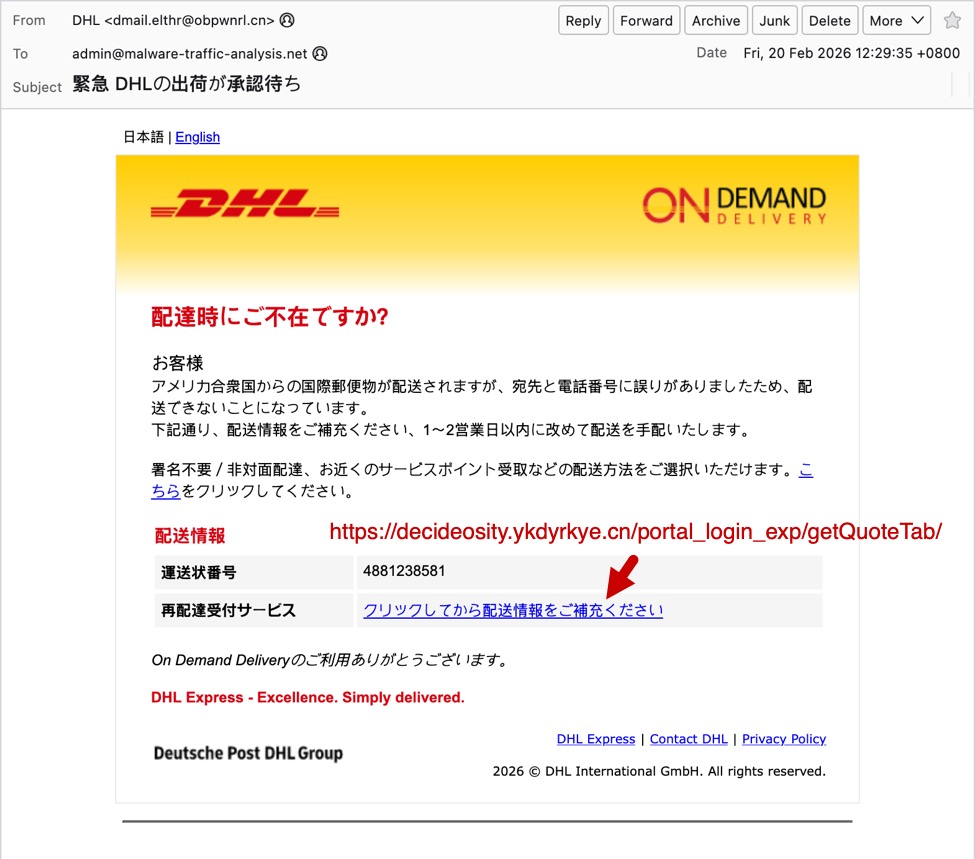
Shown above: The spam folder for my blog's admin email account.
Screenshots
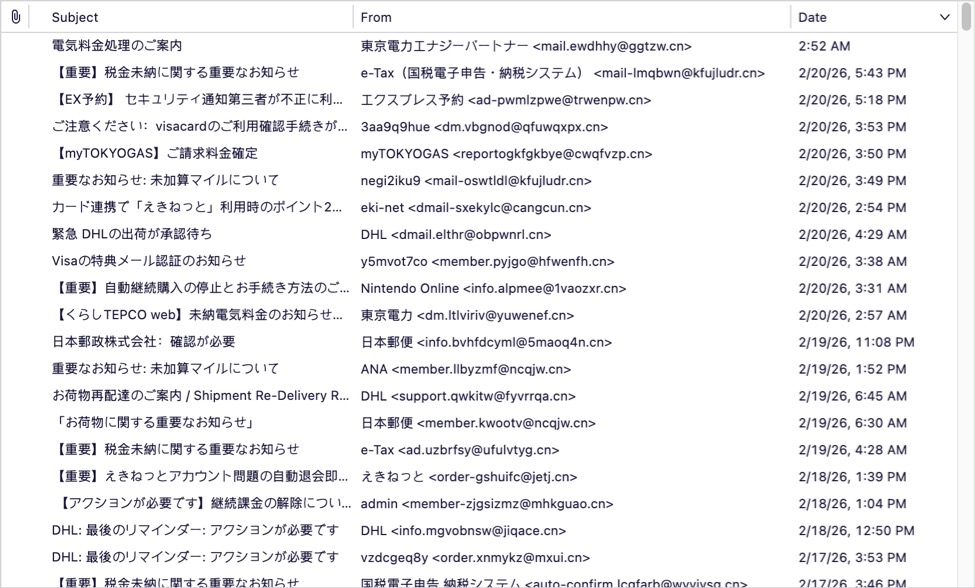
The first screenshot shows an example of a phishing email impersonating the Japanese airline ANA (All Nippon Airways). Both the sending email address and the link for the phishing page use domains with a .cn top-level domain (TLD).
Shown above: Example of a Japanese phishing email impersonating ANA.
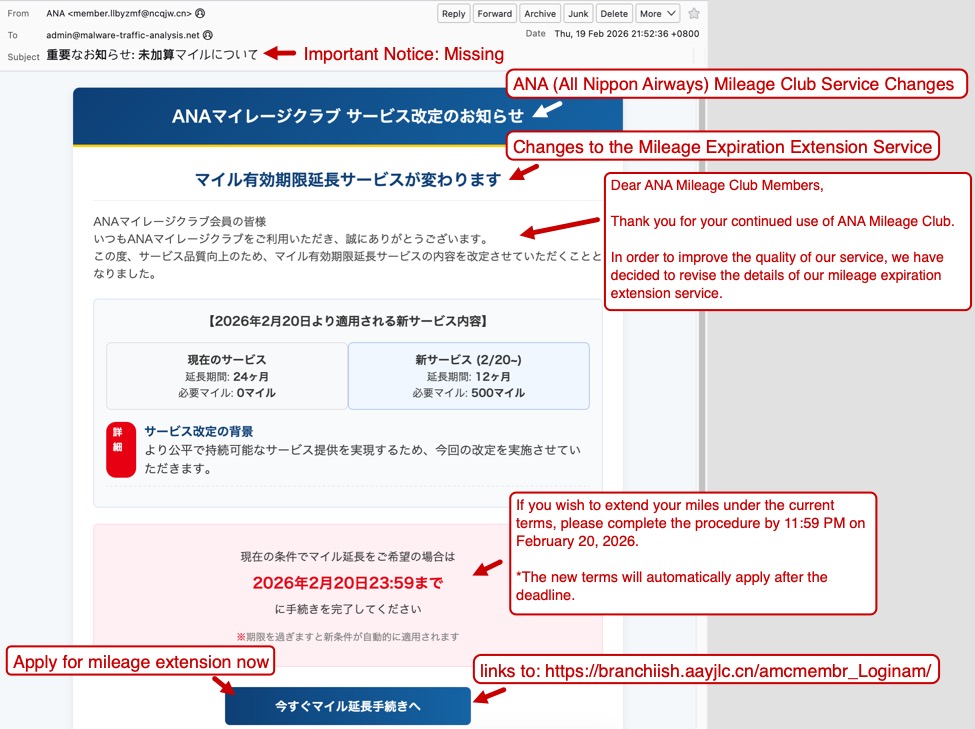
The second screenshot shows an example of a phishing email impersonating the shipping/logistics company DHL. Like the previous example, both the sending email address and the link for the phishing page use domains with a .cn top-level domain (TLD).
Shown above: Example of a Japanese phishing email impersonating DHL.
Finally, the third screenshot shows an example of a phishing email impersonating the utilities company myTOKYOGAS. Like the previous two examples, both the sending email address and the link for the phishing page use domains with a .cn top-level domain (TLD).

Shown above: Example of a Japanese phishing email impersonating myTOKYOGAS.
As noted earlier, these emails have different themes, but they have similar patterns that indicate these were sent from the same group.
Indicators of the Activity
Example 1:
- Received: from ncqjw[.]cn (unknown [150.5.129[.]136])
- Date: Thu, 19 Feb 2026 21:52:36 +0800
- From: "ANA" <member.llbyzmf@ncqjw[.]cn>
- X-mailer: Foxmail 6, 13, 102, 15 [cn]
- Link for phishing page: hxxps[:]//branchiish.aayjlc[.]cn/amcmembr_Loginam/
Example 2:
- Received: from obpwnrl[.]cn (unknown [101.47.78[.]193])
- Date: Fri, 20 Feb 2026 12:29:35 +0800
- From: "DHL" <dmail.elthr@obpwnrl[.]cn>
- X-mailer: Foxmail 6, 13, 102, 15 [cn]
- Link for phishing page: hxxps[:]//decideosity.ykdyrkye[.]cn/portal_login_exp/getQuoteTab/
Example 3:
- Received: from cwqfvzp[.]cn (unknown [150.5.130[.]42])
- Date: Fri, 20 Feb 2026 23:50:56 +0800
- From: "myTOKYOGAS" <reportogkfgkbye@cwqfvzp[.]cn>
- X-mailer: Foxmail 6, 13, 102, 15 [cn]
- Link for phishing page: hxxps[:]//impactish.rexqm[.]cn/mtgalogin/
Final Words
The most telling indicator that these emails were sent from the same group is the X-mailer: Foxmail 6, 13, 102, 15 [cn] line in the email headers.
I'm not likely to be tricked into giving up information for accounts that I don't have, like for myTOKYOGAS or for DHL. Other recipients could be tricked by these, though, assuming they make it past a recipient's spam filter.
I'm curious how effective these phishing emails are, because the group behind this activity appears to be casting a wide net that reaches non-Japanese speakers.
If anyone else has received these types of phishing emails, feel free to leave a comment or submit an example via our contact page.
Bradley Duncan
brad [at] malware-traffic-analysis.net
如有侵权请联系:admin#unsafe.sh