嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头,直接写描述。好的,首先我得仔细阅读文章,抓住主要信息。 文章讲的是一个叫做PromptSpy的Android恶意软件,它利用了Google的Gemini AI来实现持久性和高级间谍功能。ESET的研究人员发现了这个恶意软件,它是第一个利用AI的Android恶意软件。它能捕获锁屏数据、阻止卸载、收集设备信息、截图和录屏。这些功能都让这个恶意软件变得非常危险。 另外,PromptSpy还使用了VNC模块进行远程控制,滥用Accessibility Services来阻止移除,并且使用加密的C2通信。它的传播主要通过伪装成Chase Bank的网站,并且主要针对阿根廷的用户。开发环境可能是在中文环境中完成的。 我还注意到,PromptSpy通过向Gemini发送屏幕快照和XML数据,让AI生成点击指令来保持在最近应用列表中,这样不容易被移除。这种利用AI的方式让恶意软件更加灵活和适应性强。 总结的时候要涵盖这些关键点:它是第一个利用Gemini AI的Android恶意软件,具备多种间谍功能,通过AI实现持久性,并且主要针对阿根廷用户。 </think> PromptSpy 是首个利用 Google 的 Gemini AI 的 Android 恶意软件,具备持久性和高级间谍功能。它能捕获锁屏数据、阻止卸载、收集设备信息、截图和录屏,并通过 VNC 模块实现远程控制。该恶意软件主要针对阿根廷用户,利用 AI 适应不同设备和界面以维持存在。 2026-2-20 07:49:37 Author: securityaffairs.com(查看原文) 阅读量:3 收藏
PromptSpy abuses Gemini AI to gain persistent access on Android
Pierluigi Paganini
February 20, 2026

PromptSpy is the first Android malware to abuse Google’s Gemini AI, enabling persistence and advanced spying features.
Security researchers at ESET have uncovered PromptSpy, the first known Android malware to exploit Google’s Gemini AI to maintain persistence. The malware can capture lockscreen data, block uninstallation attempts, collect device information, take screenshots, and record screen activity as video, marking a concerning evolution in AI-assisted mobile threats.
This is the second AI-powered malware discovered by ESET, following PromptLock in August 2025, the first known case of AI-driven ransomware.
Although AI is used only to keep the malicious app pinned in the recent apps list, it allows the malware to adapt to different devices and Android versions.
“Specifically, Gemini is used to analyze the current screen and provide PromptSpy with step-by-step instructions on how to ensure the malicious app remains pinned in the recent apps list, thus preventing it from being easily swiped away or killed by the system.” reads the report published by ESET. “The AI model and prompt are predefined in the code and cannot be changed. Since Android malware often relies on UI navigation, leveraging generative AI enables the threat actors to adapt to more or less any device, layout, or OS version, which can greatly expand the pool of potential victims.”
PromptSpy deploys a VNC module for remote control, abuses Accessibility Services to block removal, captures lockscreen data, records video, and uses encrypted C2 communications. The campaign appears to be driven by financial gain and mainly targets users in Argentina. The malware was likely developed in a Chinese-speaking environment. It is spread through a dedicated website rather than Google Play, and Google Play Protect can block known versions of it.
PromptSpy uses Google’s Gemini AI in a limited but clever way: to stay persistent. Instead of relying on fixed screen taps or coordinates, which often fail across different Android versions and device layouts, the malware sends Gemini a text prompt plus an XML dump of the current screen. This gives the AI a full view of buttons, text, and positions. Gemini then replies with JSON instructions telling the malware where to tap. PromptSpy repeats the process until the app is successfully locked in the recent apps list, preventing easy removal.
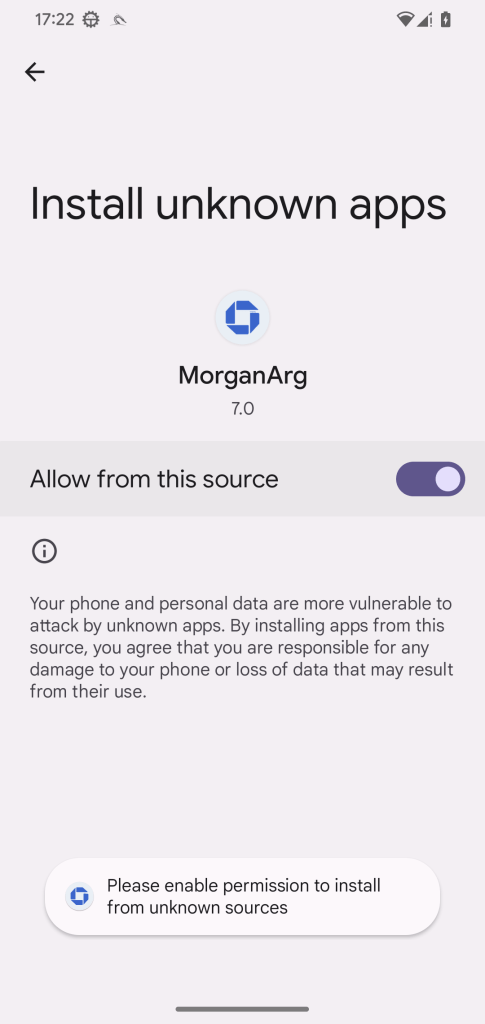
ESET discovered the threat in February 2026, PromptSpy evolved from an earlier variant called VNCSpy. Samples were uploaded from Hong Kong and later Argentina, suggesting regional targeting. The malware is distributed through malicious websites impersonating Chase Bank, using branding like “MorganArg.” A related phishing app, likely from the same actor, helps deliver the final payload.
Once installed, PromptSpy abuses Accessibility Services and includes a VNC module, giving attackers full remote control of the device. It can see the screen, perform gestures, and maintain control while staying hidden in the recent apps list.
The analysis of the malicious code revealed debug strings in simplified Chinese, along with functions handling Chinese Accessibility event types. A disabled debug method translated Android accessibility events into Chinese, suggesting with medium confidence that the malware was developed in a Chinese-speaking environment.
PromptSpy is delivered through a dropper that installs a hidden payload APK. After installation, it requests Accessibility permissions, shows a fake loading screen, and secretly contacts Gemini AI to lock itself in the Recent Apps list for persistence. It continuously sends screen data to Gemini and executes returned tap or swipe instructions.

The malware includes a VNC module for full remote control and communicates with its C2 server using AES-encrypted VNC traffic. It can steal PINs, record screens, take screenshots, and list installed apps. To prevent removal, it overlays invisible elements over uninstall buttons. Victims must reboot into Safe Mode to remove it.
PromptSpy shows a new evolution in Android malware. By using generative AI to read and interpret on-screen elements, it can adapt to almost any device or interface. Instead of fixed tap coordinates, it sends a screen snapshot to AI and receives step-by-step instructions, making its persistence more resilient to UI changes.
“More broadly, this campaign shows how generative AI can make malware far more dynamic and capable of real‑time decision‑making.” concludes the report. “PromptSpy is an early example of generative AI‑powered Android malware, and it illustrates how quickly attackers are beginning to misuse AI tools to improve impact.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, PromptSpy)
如有侵权请联系:admin#unsafe.sh
