嗯,用户让我用中文帮他总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头,直接写描述。好的,我得先仔细阅读文章内容。 文章讲的是一个新的安卓银行木马,叫Massiv,伪装成IPTV应用来窃取数字身份和访问在线银行账户。它使用屏幕覆盖和键盘记录来获取敏感数据,并能远程控制受感染的设备。研究人员在ThreatFabric观察到,Massiv针对葡萄牙政府的应用程序,该应用连接到葡萄牙的数字认证系统Chave Móvel Digital。这些服务包含用户数据,可以用来绕过KYC验证或访问银行账户和其他在线服务。 Massiv有两个远程控制模式:一个是屏幕实时流式模式,利用Android的MediaProjection API;另一个是UI树模式,从Accessibility Service提取结构化数据。后者特别有助于绕过银行、通讯等应用中的屏幕捕捉保护。 此外,文章提到IPTV应用作为恶意软件诱饵的情况越来越多,过去八个月有所增加。这些IPTV应用通常无法在Google Play上找到,因为它们涉及版权侵权。用户习惯于从非官方渠道下载APK文件。大多数情况下,IPTV应用是假的,无法访问盗版广播,APK只是一个释放恶意软件负载的工具。 研究人员报告说,伪装成IPTV的恶意软件释放器主要针对西班牙、葡萄牙、法国和土耳其的用户。建议安卓用户只从官方渠道下载经过验证的应用程序,并保持Play Protect功能开启。 现在我需要把这些信息浓缩到100字以内。重点包括:新的安卓木马Massiv伪装成IPTV应用窃取信息;利用屏幕覆盖和键盘记录;远程控制设备;针对葡萄牙政府应用;可能用于绕过KYC和访问银行账户;以及IPTV作为恶意软件诱饵的趋势。 所以总结应该是:新的安卓木马Massiv伪装成IPTV应用窃取数字身份和银行信息,并通过屏幕覆盖和键盘记录远程控制设备。它主要针对葡萄牙政府的应用程序,并可能用于绕过KYC验证或访问银行账户。 </think> 一种新的安卓银行木马Massiv伪装成IPTV应用窃取数字身份和银行信息,并通过屏幕覆盖和键盘记录远程控制设备。它主要针对葡萄牙政府的应用程序,并可能用于绕过KYC验证或访问银行账户。 2026-2-19 10:15:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:1 收藏

A new Android banking malware, which researchers named Massiv, is posing as an IPTV app to steal digital identities and access online banking accounts.
The malware relies on screen overlays and keylogging to obtain sensitive data and can take remote control of a compromised device.
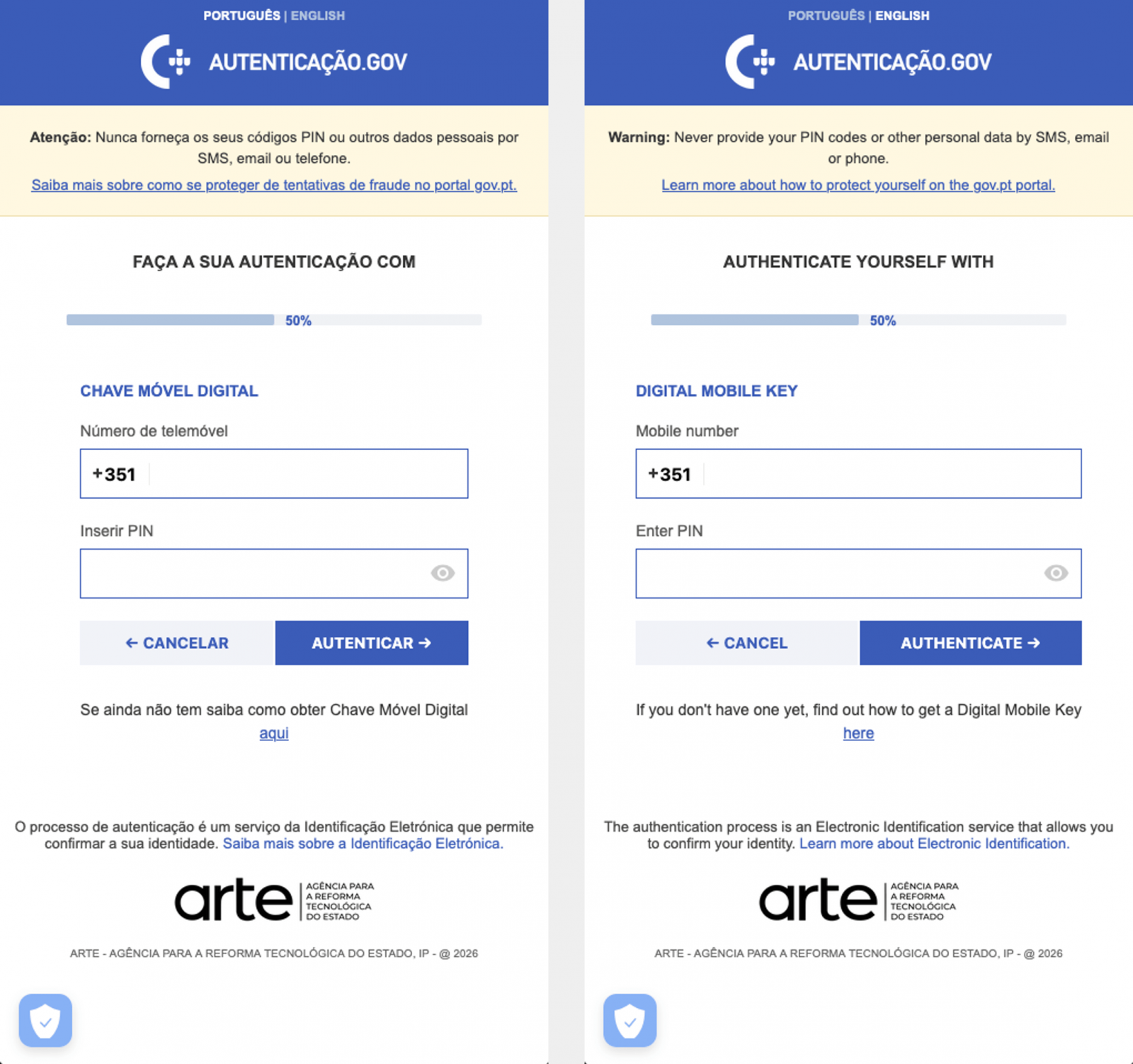
In a campaign observed by researchers at fraud detection and mobile threat intelligence company ThreatFabric, Massiv targeted a Portuguese government app that connects with Chave Móvel Digital - Portugal’s digital authentication and signature system.
The two service contain user data that could be used to bypass know-your-customer (KYC) verifications or to access banking accounts and other public and private online services.
.jpg)
Source: ThreatFabric
“MTI research identified cases where new accounts were opened in the name of the victim (user of the infected device) in new banks and services (not used by the victim),” describes the ThreatFabric report.
“Since those accounts are fully under fraudster control, they can further use them as a part of money laundering scheme as well as getting loans and cashing out the money, leaving unsuspecting victim in debts in the bank they never opened account themselves.”
Massiv provides two remote control modes for its operators: a screen live-streaming mode that leverages Android’s MediaProjection API, and a UI-tree mode that extracts structured data from the Accessibility Service.
The latter includes visible text, interface element names, screen coordinates, and interaction attributes, allowing attackers to click buttons, edit text fields, and more.
This second mode is particularly helpful for bypassing screen-capture protections commonly used in banking, communication, and other apps that host sensitive content.
IPTV lures on the rise
An interesting trend identified by ThreatFabric through the discovery of Massiv is the increasing use of IPTV apps as lures for Android malware infections, a technique that has increased over the past eight months.
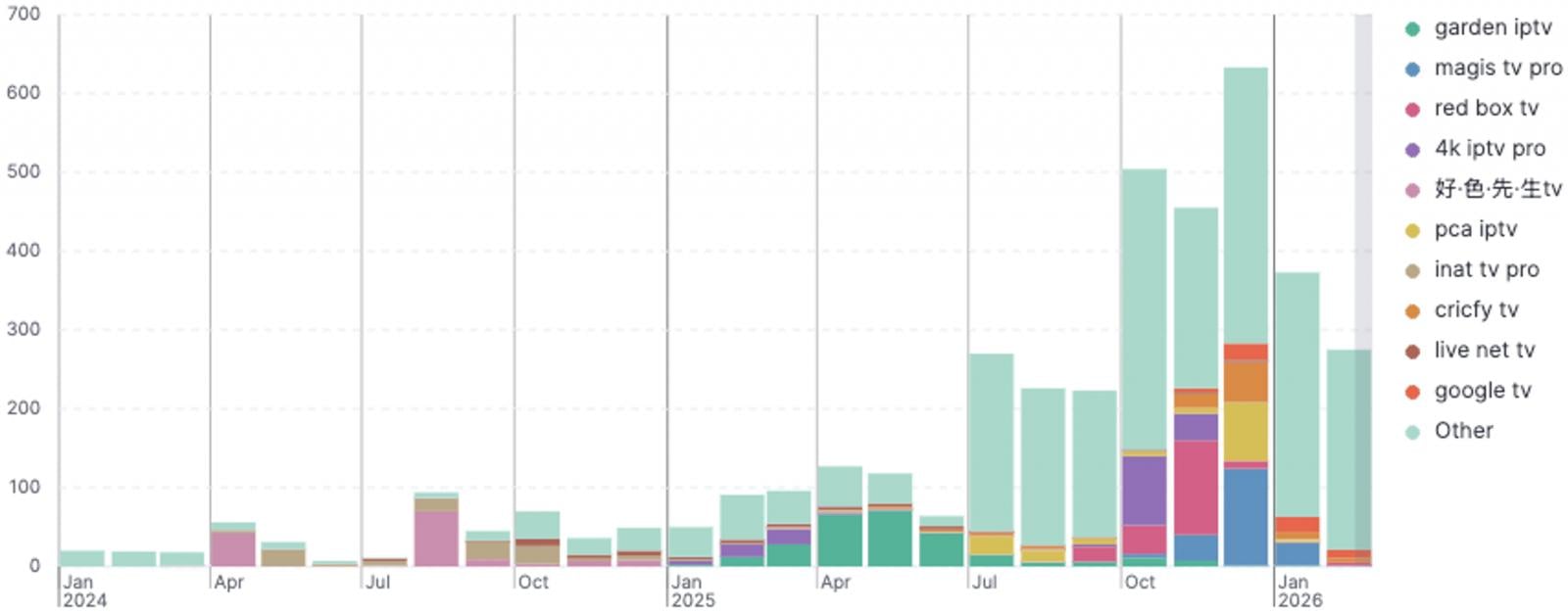
Source: ThreatFabric
These apps typically play a key role in copyright infringement, so they cannot be found on Google Play due to policy violations. Sourcing them as APKs from unofficial channels is considered normal for their users, who are accustomed to sideloading them.
In most cases, the IPTV app is fake, does not offer access to pirated broadcasts, and the APK is a dropper that installs the malware payload. In some cases, the app displays a legitimate IPTV website in a WebView to maintain the illusion.
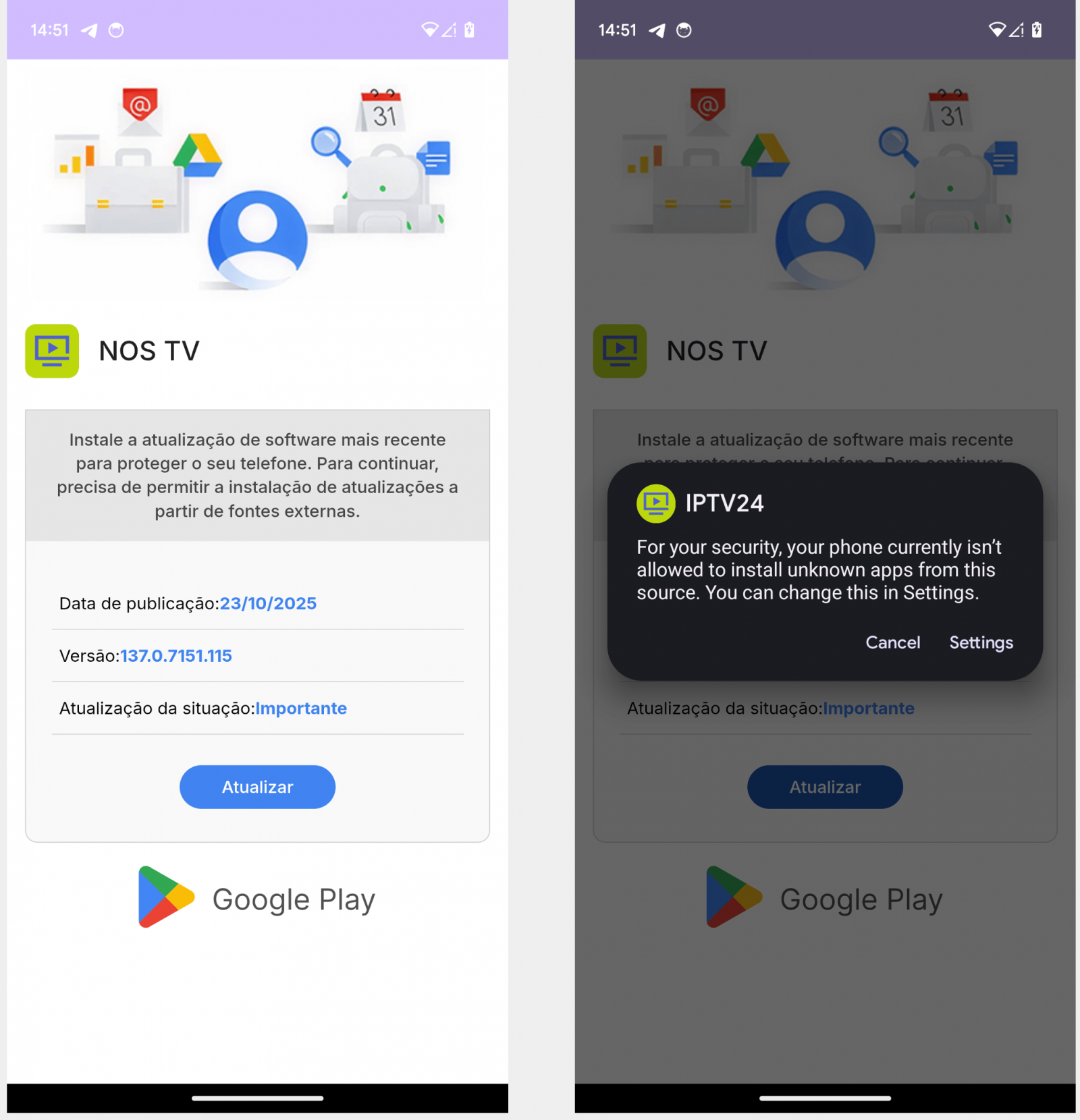
Source: ThreatFabric
The researchers report that fake IPTV-masking malware droppers have primarily targeted users in Spain, Portugal, France, and Turkey.
Android users are recommended to only download vetted apps from reputable publishers available on official channels (Google Play), keep Play Protect active, and use it to regularly scan the device.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

