Cybersecurity researchers have disclosed details of a new Android trojan called Massiv that's designed to facilitate device takeover (DTO) attacks for financial theft.
The malware, according to ThreatFabric, masquerades as seemingly harmless IPTV apps to deceive victims, indicating that the activity is primarily singling out users looking for the online TV applications.
"This new threat, while only seen in a limited number of rather targeted campaigns, already poses a great risk to the users of mobile banking, allowing its operators to remotely control infected devices and perform device takeover attacks with further fraudulent transactions performed from the victim's banking accounts," the Dutch mobile security company said in a report shared with The Hacker News.
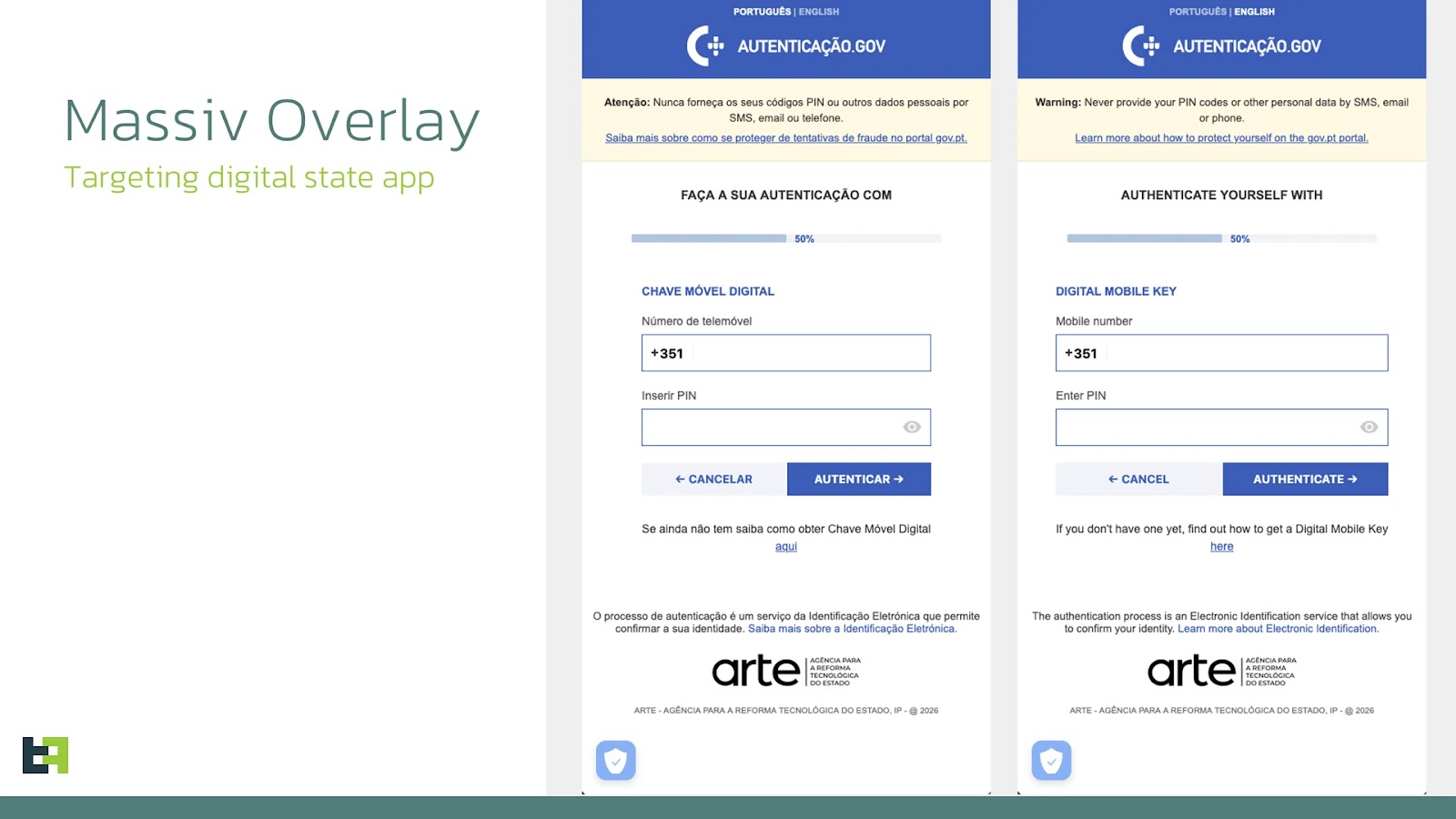
Like various Android banking malware families, Massiv supports a wide range of features to facilitate credential theft through a number of methods: screen streaming through Android's MediaProjection API, keylogging, SMS interception, and fake overlays served atop banking and financial apps. The overlay asks users to enter their credentials and credit card details.
One such campaign has been found to target gov.pt, a Portuguese public administration app that allows users to store identification documents and manage the Digital Mobile Key (aka Chave Móvel Digital or CMD). The overlay tricks users into entering their phone number and PIN code, likely in an effort to bypass Know Your Customer (KYC) verification.
ThreatFabric said it identified cases where scammers used the information captured through these overlays to open new banking accounts in the victim's name, allowing them to be used for money laundering or getting loans approved without the actual victim's knowledge.
In addition, it serves as a fully functional remote-control tool, granting the operator the ability to access the victim's device stealthily while showing a black screen overlay to conceal the malicious activity. These techniques, realized by abusing Android's accessibility services, have also been observed in several other Android bankers like Crocodilus, Datzbro, and Klopatra.
"However, some applications implement protection against screen capture," the company explained. "To bypass it, Massiv uses so-called UI-tree mode -- it traverses AccessibilityWindowInfo roots and recursively processes AccessibilityNodeInfo objects."
This is done so as to build a JSON representation of visible text and content descriptions, UI elements, screen coordinates, and interaction flags that indicate whether the UI element is clickable, editable, focused, or enabled. Only nodes that are visible and have text are exported to the attacker, who can then determine the next course of action by issuing specific commands to interact with the device.
The malware is equipped to carry out a wide range of malicious actions -
- Enable black overlay, mute sounds and vibration
- Send device information
- Perform click and swipe actions
- Alter clipboard with specific text
- Disable black screen
- Turn on/off screen streaming
- Unlock device with pattern
- Serve overlays for an app, device pattern lock, or PIN
- Download ZIP archive with overlays for targeted applications
- Download and install APK files
- Open Battery Optimization, Device Admin, and Play Protect settings screens
- Rquest for permissions to access SMS messages, install APK packages,
- Clear log databases on the device
Massiv is distributed in the form of dropper apps mimicking IPTV apps via SMS phishing. Once installed and launched, the dropper prompts the victim to install an "important" update by granting it permissions to install software from external sources. The names of the malicious artifacts are listed below -
- IPTV24 (hfgx.mqfy.fejku) - Dropper
- Google Play (hobfjp.anrxf.cucm) - Massiv
"In most of the cases observed, it is just masquerading," ThreatFabric said. "No actual IPTV applications were infected or initially contained malicious code. Usually, the dropper that mimics an IPTV app opens a WebView with an IPTV website in it, while the actual malware is already installed and running on the device."
The majority of Android malware campaigns using TV-related droppers have targeted Spain, Portugal, France, and Turkey over the past six months.
Massiv is the latest entrant to an already crowded Android threat landscape, reflecting the continuing demand for such turnkey solutions among cybercriminals.
"While not yet observed being promoted as Malware-as-a-Service, Massiv's operator shows clear signs of going this path, introducing API keys to be used in malware communication with the backend," ThreatFabric said. "Code analysis revealed ongoing development, with more features likely to be introduced in the future."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.