嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章讲的是Amnesty International报告说,2024年5月,安哥拉记者Teixeira Cândido的iPhone被Intellexa公司的Predator间谍软件感染了。这个间谍软件是通过WhatsApp发送的恶意链接传播的。Predator是一种强大的移动间谍软件,通常被政府用于 surveillance。这次攻击显示了对记者进行监视的行为。 接下来,我需要提取关键点:时间、人物、事件、工具、影响。然后用简洁的语言把这些点连起来,确保不超过100字。 可能的结构是:时间+事件+工具+影响。例如,“2024年5月,安哥拉记者Teixeira Cândido的iPhone被Intellexa公司的Predator间谍软件感染,该软件通过WhatsApp恶意链接传播,显示对记者监视行为。” 检查一下字数是否在限制内,并且确保信息准确无误。 </think> 2024年5月,安哥拉记者Teixeira Cândido的iPhone被Intellexa公司的Predator间谍软件感染,该软件通过WhatsApp恶意链接传播,显示对记者监视行为。 2026-2-19 08:17:16 Author: securityaffairs.com(查看原文) 阅读量:21 收藏
Intellexa’s Predator spyware infected Angolan journalist’s device, Amnesty reports
Pierluigi Paganini
February 19, 2026

Amnesty reports Angolan journalist’s iPhone was infected by Intellexa’s Predator spyware via a WhatsApp link in May 2024.
Amnesty International reports that in May 2024, Intellexa’s Predator spyware infected the iPhone of Teixeira Cândido, an Angolan journalist and press freedom advocate, after he opened a malicious link sent via WhatsApp. This incident highlights how attackers actively target journalists for surveillance.
Predator is a powerful mobile spyware by Intellexa, sold to governments for surveillance. Investigations over five years documented abuses worldwide, despite Intellexa rebranding and shifting its corporate structure. The Angola case marks the first confirmed Predator attack there, showing the spyware remained active through 2025. Amnesty International and partners exposed Intellexa’s operations, but the responsible customers remain unknown.
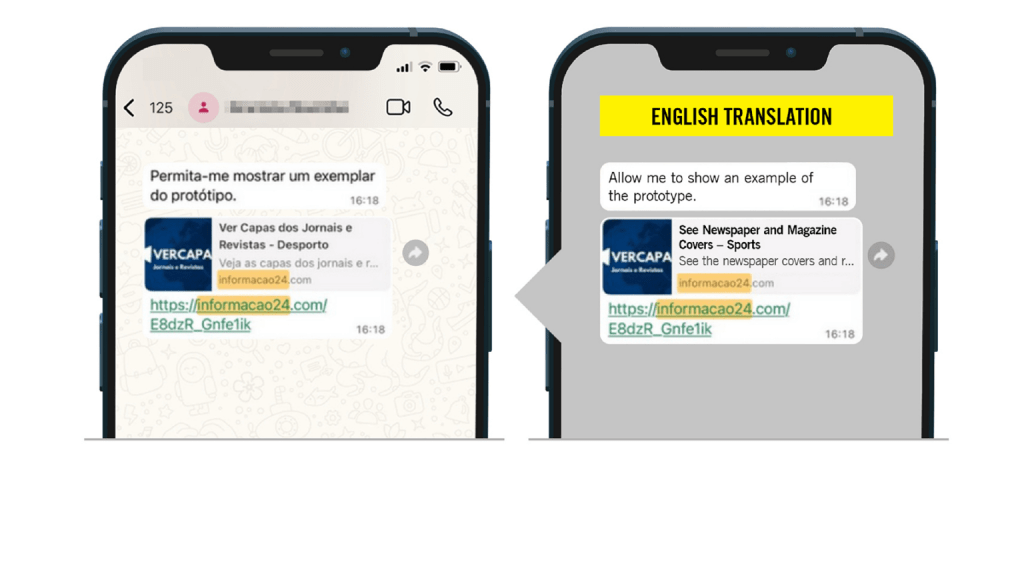
Since 2022, Angolan journalist Teixeira Cândido faced multiple attacks and break-ins, raising suspicions of surveillance. From April to June 2024, an attacker posing as students sent him WhatsApp messages to gain his trust, eventually sending malicious links. On 4 May 2024, he clicked one link, infecting his iPhone with Intellexa’s Predator spyware. Once installed, the spyware gave attackers full access to his device, including messages, calls, emails, location, camera, microphone, passwords, and other sensitive data, illustrating a targeted and highly invasive surveillance operation.
“Through forensic analysis of the links and associated domain names, Amnesty International’s Security Lab determined with high confidence that all the links sent to Teixeira Cândido to this WhatsApp number were attempts to infect his phone with the Predator spyware. All infection domains matched a network fingerprint used to track Intellexa infection servers.” reads the report published by Amnesty International. “On 4 May 2024, one day after the first Predator infection link was received (Figure 4), Teixeira Cândido appears to have opened the infection link received, which would have resulted in the successful infection of the journalist’s phone with the Predator spyware.

On 4 May 2024, Amnesty International confirmed Predator spyware ran on Teixeira Cândido’s iPhone, executing from the directory /private/var/containers/Bundle/ under the name “iconservicesagent” to impersonate a system process.
His device ran the outdated iOS 16.2, potentially exposing it to known exploits, though Intellexa could also use zero-day vulnerabilities. The spyware remained active less than a day, but attackers sent 11 further malicious WhatsApp links through mid-June 2024. Forensic traces, network activity, and infection domains confirm this attack as Predator.
Amnesty International’s research shows Intellexa’s Predator spyware has targeted Angola since at least early 2023, with the attack on journalist Teixeira Cândido representing just part of broader activity. Predator communicates with spyware servers via domain names, many in Portuguese, revealing a regional focus. Technical analysis linked the domains used against Cândido to Predator, with earlier Angola-linked domains dating back to March 2023. Predator grants total access to devices, making independent audits nearly impossible.
Amnesty considers such spyware fundamentally incompatible with human rights. The Angola attack violates journalists’ rights to privacy and free expression, chilling civil society in a context of growing authoritarianism under President João Lourenço. Amnesty’s inquiries to Intellexa about its role and access to customer systems remain unanswered, raising concerns over the company’s legal and ethical responsibility in these abuses.
“While it remains unclear if Intellexa could access the specific Angolan deployment in 2024, the finding from Intellexa Leaks that the company had potential visibility into active surveillance operations of their customers, including seeing technical information about the targets, raises new legal questions about Intellexa’s role in relation to the spyware and the company’s potential legal or criminal responsibility for unlawful surveillance operations carried out using their products.” concludes the report. “This new case of spyware use against a journalist in Angola makes clear – yet again – that the unchecked sale and use of surveillance technologies continue to facilitate human rights abuses at a global scale. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Intellexa’s Predator spyware)
如有侵权请联系:admin#unsafe.sh