好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得快速浏览文章,抓住主要信息。 文章讲的是Kaspersky发现了一个名为Keenadu的Android后门程序,用于广告欺诈,并且可以完全控制设备。这个恶意软件可能预装在设备固件中,隐藏在系统应用里,甚至通过Google Play分发。它能将受感染的手机变成点击机器人,进行广告欺诈,同时还能远程控制设备。 接下来,我需要提取关键点:Keenadu的功能、传播方式、影响范围以及Kaspersky的发现。然后用简洁的语言把这些点整合起来。 要注意的是,用户要求不要以“文章内容总结”或“这篇文章”开头,直接描述内容。同时要控制在100字以内。 可能的结构是:介绍Keenadu是什么、它的功能、传播途径、影响范围以及Kaspersky的发现和数据。 现在开始组织语言: Kaspersky发现名为Keenadu的Android后门程序,用于广告欺诈并可完全控制设备。该恶意软件预装于设备固件或隐藏在系统应用中,甚至通过Google Play分发。它能将手机变为点击机器人,并允许攻击者远程控制。研究人员已检测到超过13,000台设备感染,主要分布在俄罗斯、日本等国。 检查字数是否符合要求,并确保没有使用禁止的开头。 </think> Kaspersky发现名为Keenadu的Android后门程序,用于广告欺诈并可完全控制设备。该恶意软件预装于设备固件或隐藏在系统应用中,甚至通过Google Play分发。它能将手机变为点击机器人,并允许攻击者远程控制。研究人员已检测到超过13,000台设备感染,主要分布在俄罗斯、日本等国。 2026-2-18 08:31:2 Author: securityaffairs.com(查看原文) 阅读量:1 收藏
Keenadu backdoor found preinstalled on Android devices, powers Ad fraud campaign
Pierluigi Paganini
February 18, 2026

Kaspersky uncovered Keenadu, an Android backdoor used for ad fraud that can even take full control of devices.
Kaspersky has identified a new Android malware called Keenadu. It can be preinstalled in device firmware, hidden inside system apps, or even distributed via official stores like Google Play. Currently used for ad fraud by turning infected phones into click bots, some variants also allow attackers to gain full remote control of compromised devices.
After uncovering the Triada backdoor in counterfeit Android firmware, researchers found another firmware-level threat called Keenadu. Like Triada, Keenadu embeds itself into the system during the build process, injects into the Zygote process, and infects every app launched on the device. It acts as a multi-stage loader, enabling full remote control, ad fraud, credential theft, and malicious payload delivery.
The researchers reported that some infected firmware was even pushed via OTA updates and built into core system apps. Investigators also linked Keenadu to major Android botnets, including Triada, BADBOX, and Vo1d.
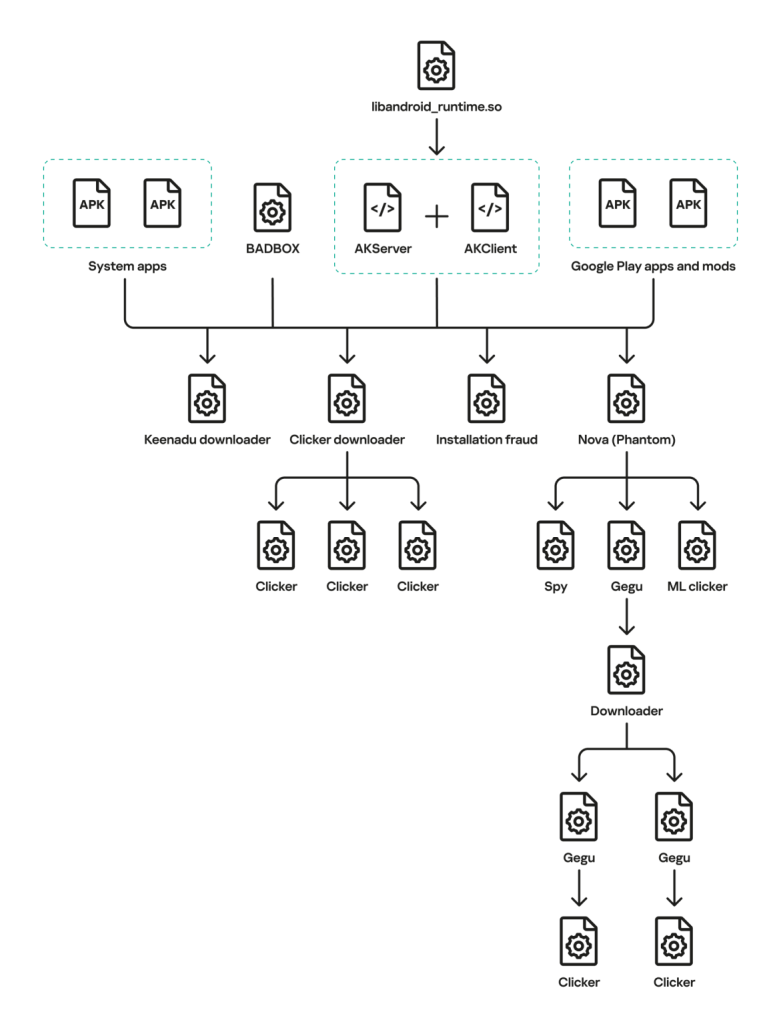
Researchers found that Keenadu was embedded inside Android’s core library, libandroid_runtime.so, acting as a hidden dropper. A modified logging function decrypted an RC4-encrypted payload and loaded it into every app via the Zygote process. The malicious code uses a client-server setup called AKClient and AKServer.
“We discovered a new backdoor, which we dubbed Keenadu, in the firmware of devices belonging to several brands. The infection occurred during the firmware build phase, where a malicious static library was linked with libandroid_runtime.so. Once active on the device, the malware injected itself into the Zygote process, similarly to Triada. In several instances, the compromised firmware was delivered with an OTA update.” reads the report published by Kaspersky. “A copy of the backdoor is loaded into the address space of every app upon launch. The malware is a multi-stage loader granting its operators the unrestricted ability to control the victim’s device remotely.”
This design lets the attackers bypass Android permissions, give apps special privileges, steal data, install extra plugins, and connect to encrypted command-and-control servers. The malware also avoids infecting devices set to the Chinese language or devices that do not have Google services installed.
The researchers discovered that the backdoor was preinstalled in the firmware for Alldocube tablets. The malicious code traced to a rogue static library added during the build process. Attackers used valid digital signatures, a circumstance that suggests this was a supply chain compromise, likely introduced before devices reached the market, and affecting multiple vendors.
Keenadu’s backdoor gives attackers near-total control of infected Android devices and loads extra malicious modules from its C2 server. To avoid detection, the server waits about 2.5 months after activation before delivering payloads. The modules are downloaded from Amazon AWS, verified with MD5 and DSA signatures, then decrypted and executed.
Kaspersky identified multiple plugins: a loader targeting Amazon, SHEIN and Temu apps that can install hidden APKs; clicker modules injected into apps like YouTube, Facebook and system components to generate ad fraud; a Chrome module that steals search queries and hijacks results; and “Nova,” a clicker using advanced techniques to interact with ads.
Other modules monetize app installs, collect device data, retrieve advertising IDs, and may deploy spyware or additional droppers. Some victims reported tablets adding shopping cart items without their knowledge.
Researchers found Keenadu spreading beyond the original firmware compromise. The loader was embedded inside legitimate system apps, including a facial recognition service, launchers, and content center apps, where it was triggered by normal system events. Some variants relied on a native library to load modules and silently install APKs.
Other samples were deployed through a separate backdoor linked to BADBOX, suggesting cooperation between malware platforms. Keenadu was also distributed via modified popular apps from unofficial stores and even Google Play, where trojanized smart camera apps with over 300,000 downloads secretly launched the Nova clicker under specific conditions.

As of February 2026, Kaspersky detected more than 13,000 Android devices infected with Keenadu. Most victims were located in Russia, Japan, Germany, Brazil, and the Netherlands, although infections were reported in other countries as well.
” During the investigation, we were surprised by the scope of the Keenadu campaigns: beyond the primary backdoor in firmware, its modules were found in system apps and even in apps from Google Play.” concludes the report. “This places the Trojan on the same scale as threats like Triada or BADBOX. The emergence of a new pre-installed backdoor of this magnitude indicates that this category of malware is a distinct market with significant competition.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, backdoor)
如有侵权请联系:admin#unsafe.sh
