嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要仔细阅读这篇文章,理解其主要内容。 文章讲的是Xavier Mertens发现了一个新的网络攻击活动,使用了与之前类似的技术。攻击链开始于一个附件,里面包含了一个旧的Equation Editor漏洞(CVE-2017-11882)。这个漏洞触发下载HTA文件,进而执行PowerShell脚本,最终加载DLL。 有趣的是,这次攻击中使用的图片和之前的文章中提到的一样,都是通过Base64编码,并用相同的标签分隔。提取出来的有效载荷是一个.NET二进制文件。作者还提到在VirusTotal上搜索类似图片时发现了大量相同的图片,但只有少数几个得分高。最后,他创建了一个YARA规则来追踪这些恶意软件。 现在我需要把这些信息浓缩到100字以内。要抓住关键点:新的活动、相同技术、旧漏洞、下载HTA和PowerShell、重复使用图片、Base64编码、提取DLL、VirusTotal结果和YARA规则。 可能的结构是:描述活动、技术细节、重复使用的图片和结果。确保语言简洁明了。 </think> Xavier Mertens发现了一个新的网络攻击活动,该活动使用与之前报道类似的技术。攻击链始于包含旧Equation Editor漏洞的附件(CVE-2017-11882),触发HTA文件下载并执行PowerShell脚本以加载DLL。恶意软件利用与之前相同的JPEG图片嵌入Base64编码的有效载荷,并重复使用相同的技术和标记。 2026-2-18 08:19:42 Author: isc.sans.edu(查看原文) 阅读量:12 收藏
A few days ago I wrote a diary called "Malicious Script Delivering More Maliciousness"[1]. In the malware infection chain, there was a JPEG picture that embedded the last payload delimited with "BaseStart-" and "-BaseEnd" tags.
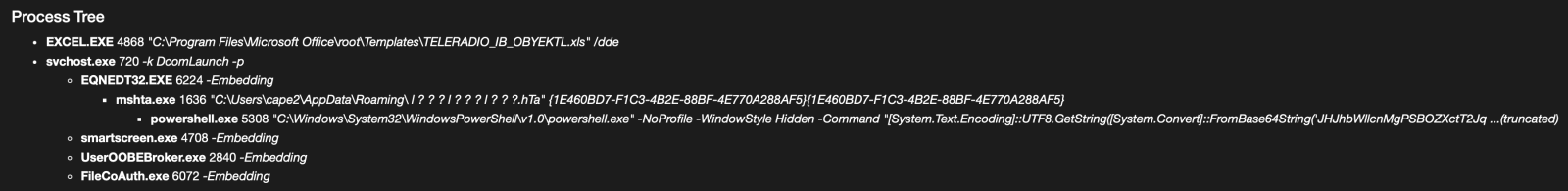
Today, I discovered anoher campaign that relies exactly on the same technique. It started with an attachment called "TELERADIO_IB_OBYEKTLRIN_BURAXILIS_FORMASI.xIs" (SHA256:1bf3ec53ddd7399cdc1faf1f0796c5228adc438b6b7fa2513399cdc0cb865962). The file in itself is not interesting, it contains a good old Equation Editor exploit (CVE-2017-11882). The exploit triggers the download of an HTA payload that executes a PowerShell payload and finally a DLL:
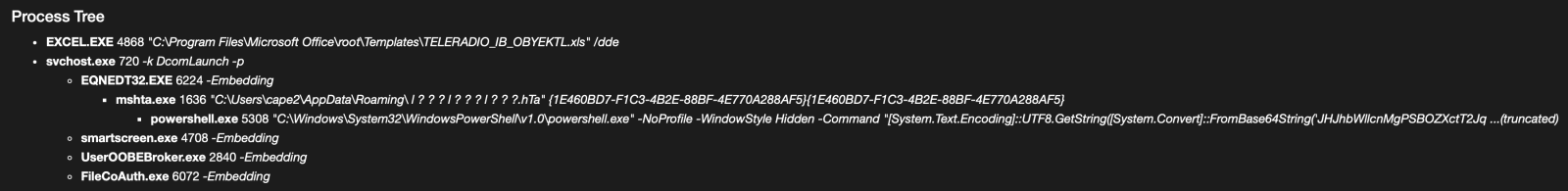
When I investigated the different payload, there was pretty simple to deobfuscated, the interesting code was polluted with Unicode characters. First the HTA file was downloaded from:
hxxp://192[.]3[.]101[.]19/31/sd878f23823878428348fd8g8g8384838f3453dfg.hta
The interesting code is here and you can easily spot the "powershell" string, no need to use AI for this :-)
The Powershell payload will fetch another file:
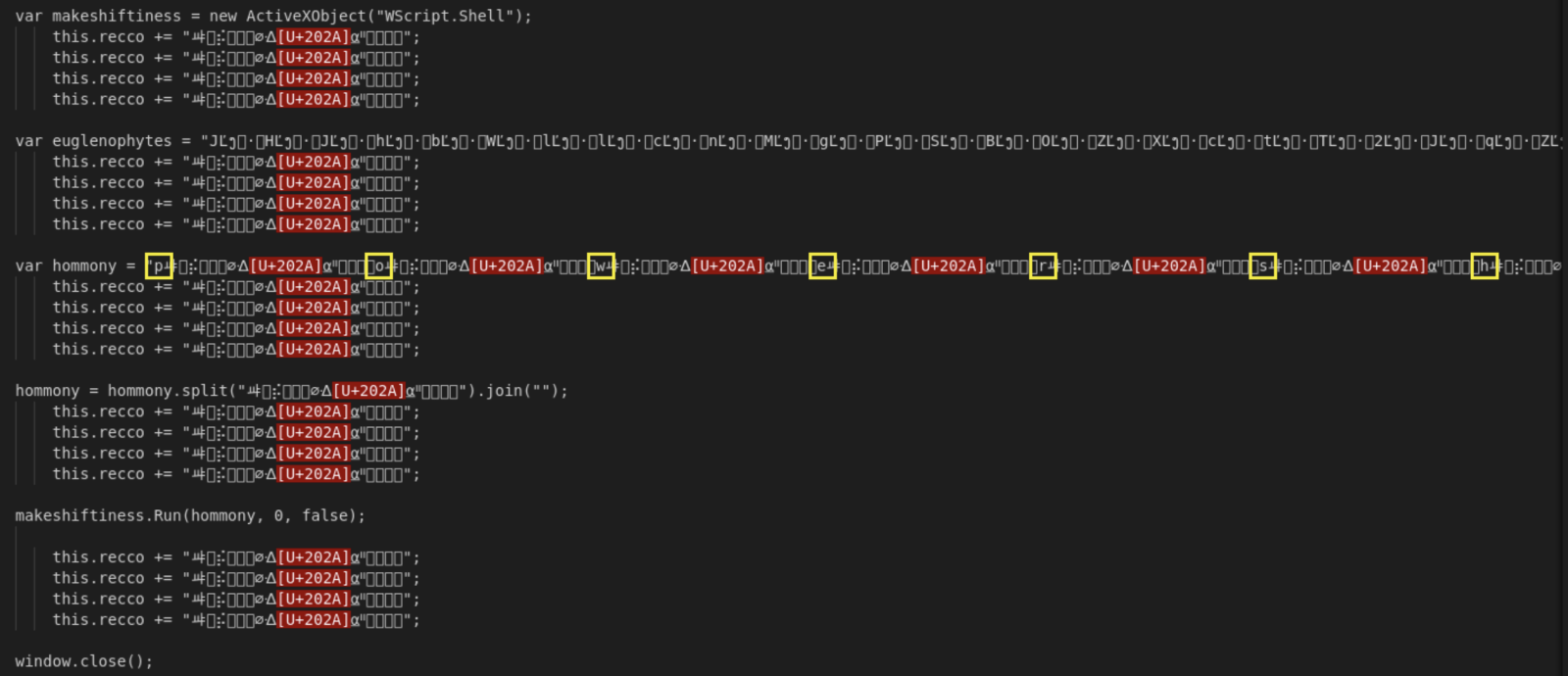
hxxps://172[.]245[.]155[.]116/img/optimized_MSI.png
Do you make the link with my previous diary? It's the same picture:

The technique is also exactly the same, the next stage is Base64-encoded and delimited by the same tags:
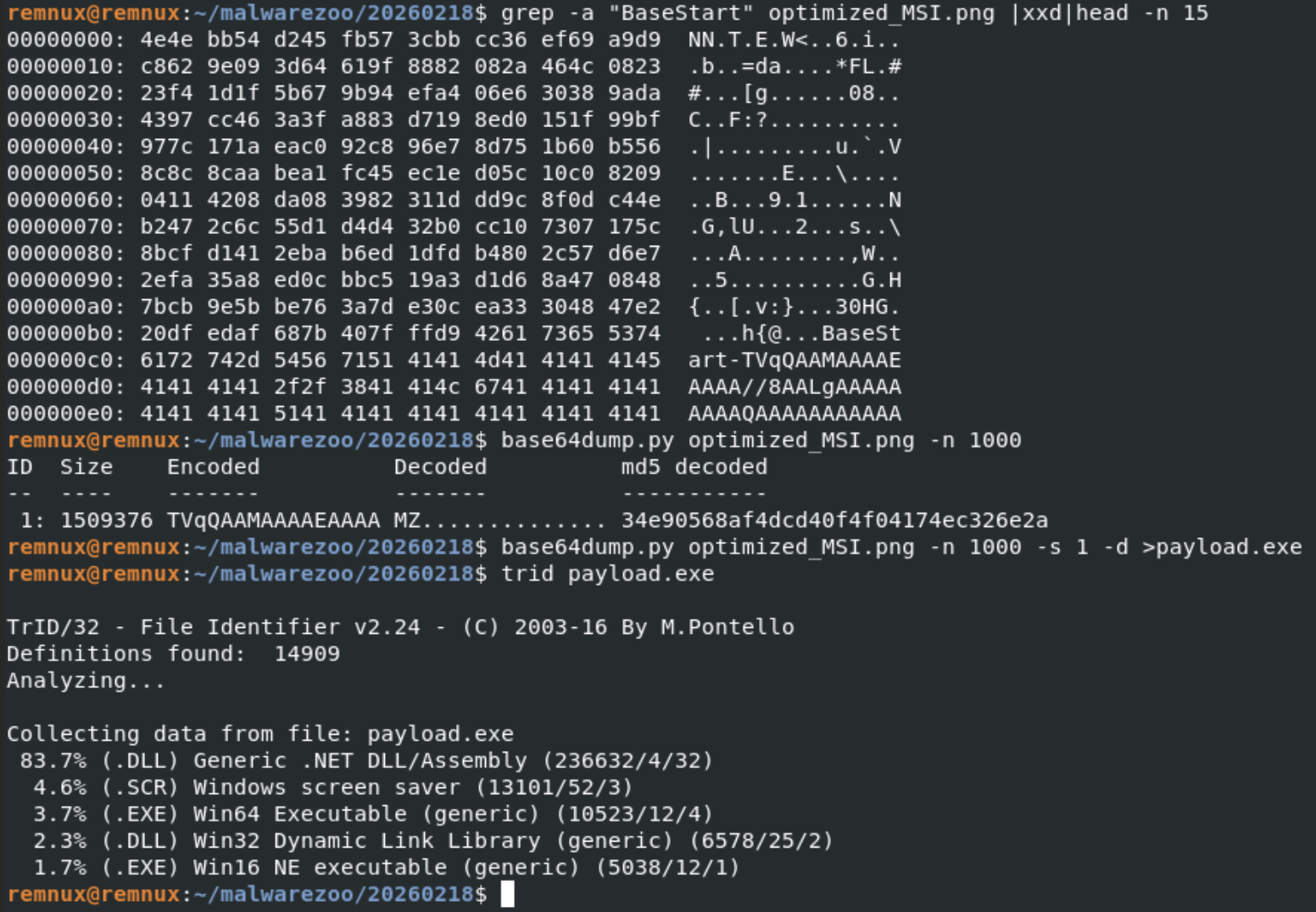
The extracted payload is a .Net binary (SHA256:adc2f550e7ff2b707a070ffaa50fc367af6a01c037f1f5b347c444cca3c9a650).
The fast that the same picture is re-used looks interesting! I did a quick search on VT and use the feature to search for similarities based on the icon/thumbnail and found a lot of identical pictures:
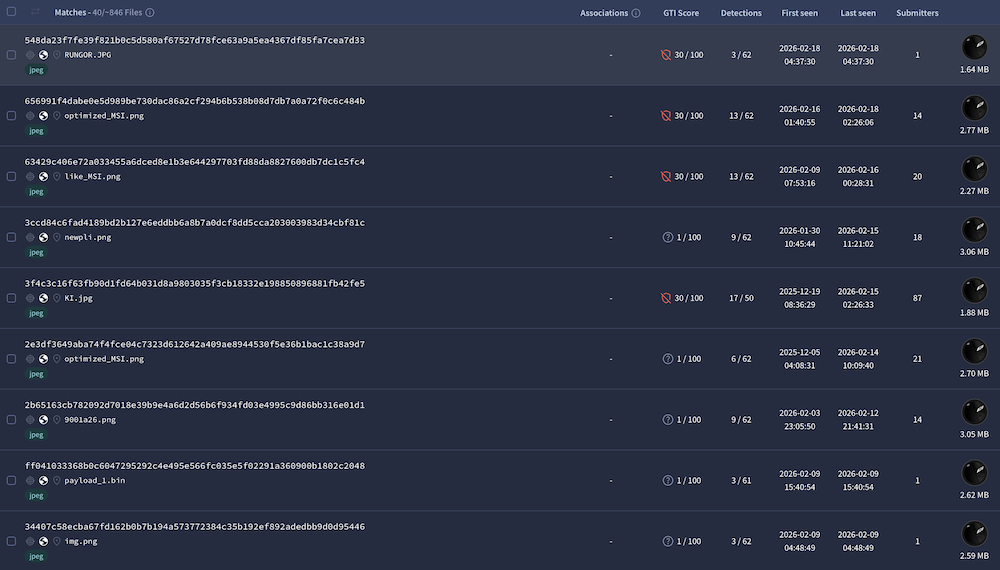
846 similar pictures have been reported but only 36 have a VT score above 5. I created a YARA rule to track them, just curious...
[1] https://isc.sans.edu/diary/Malicious+Script+Delivering+More+Maliciousness/32682
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
如有侵权请联系:admin#unsafe.sh