好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读这篇文章,了解主要信息。 文章讲的是黑客利用仿冒的Oura MCP服务器来传播StealC恶意软件。他们创建了虚假的GitHub账户和项目,看起来很真实,目的是诱骗开发者下载被感染的版本。一旦安装,恶意软件就会窃取敏感信息,比如密码、加密钱包等。 接下来,我需要提取关键点:黑客克隆了Oura MCP项目,创建虚假GitHub生态系统,诱骗用户下载恶意软件,最终导致信息泄露。这些都是核心内容。 然后,我要把这些信息浓缩成一句话,不超过100字。确保涵盖攻击手段、目标和结果。避免使用复杂的术语,保持简洁明了。 最后检查一下字数和内容是否准确传达了文章的核心信息。 </think> 黑客通过伪造Oura MCP服务器和GitHub项目,诱导开发者下载包含StealC恶意软件的版本。该软件窃取敏感数据如密码、加密钱包和API密钥。攻击者利用AI生成虚假账户制造可信度,并将恶意程序提交至公共MCP注册表以扩大传播范围。 2026-2-17 18:54:31 Author: securityaffairs.com(查看原文) 阅读量:0 收藏
SmartLoader hackers clone Oura MCP project to spread StealC malware
Pierluigi Paganini
February 17, 2026

Hackers used a fake Oura MCP server to trick users into downloading malware that installs the StealC info-stealer.
Straiker’s AI Research (STAR) Labs team uncovered a SmartLoader campaign in which attackers cloned a legitimate MCP server linked to Oura Health to spread the StealC information stealer. The fake project appeared credible, complete with bogus forks and contributors, to trick users into downloading a trojanized version. Once installed, it deployed malware designed to steal sensitive data.
“Our investigation revealed the threat actors cloned a legitimate Oura MCP Server—a tool that connects AI assistants to Oura Ring health data—and built a deceptive infrastructure of fake forks and contributors to manufacture credibility. The trojanized version of the Oura MCP server delivers the StealC infostealer, targeting developer credentials, browser passwords, and cryptocurrency wallets.” reads the report published by Straiker. “This campaign signals a significant shift in the threat landscape: traditional threat actors who have long targeted software supply chains are now pivoting to MCP ecosystems, bringing their proven tactics and operational sophistication to this emerging attack surface.”
Researchers say the SmartLoader operators spent months building a fake GitHub ecosystem to make their malware look trustworthy. They first chose a popular developer tool: the Oura MCP Server, a project created by an OpenAI engineer that connects AI assistants to Oura Ring data. The target was attractive because productivity-focused developers are likely to hold valuable credentials.
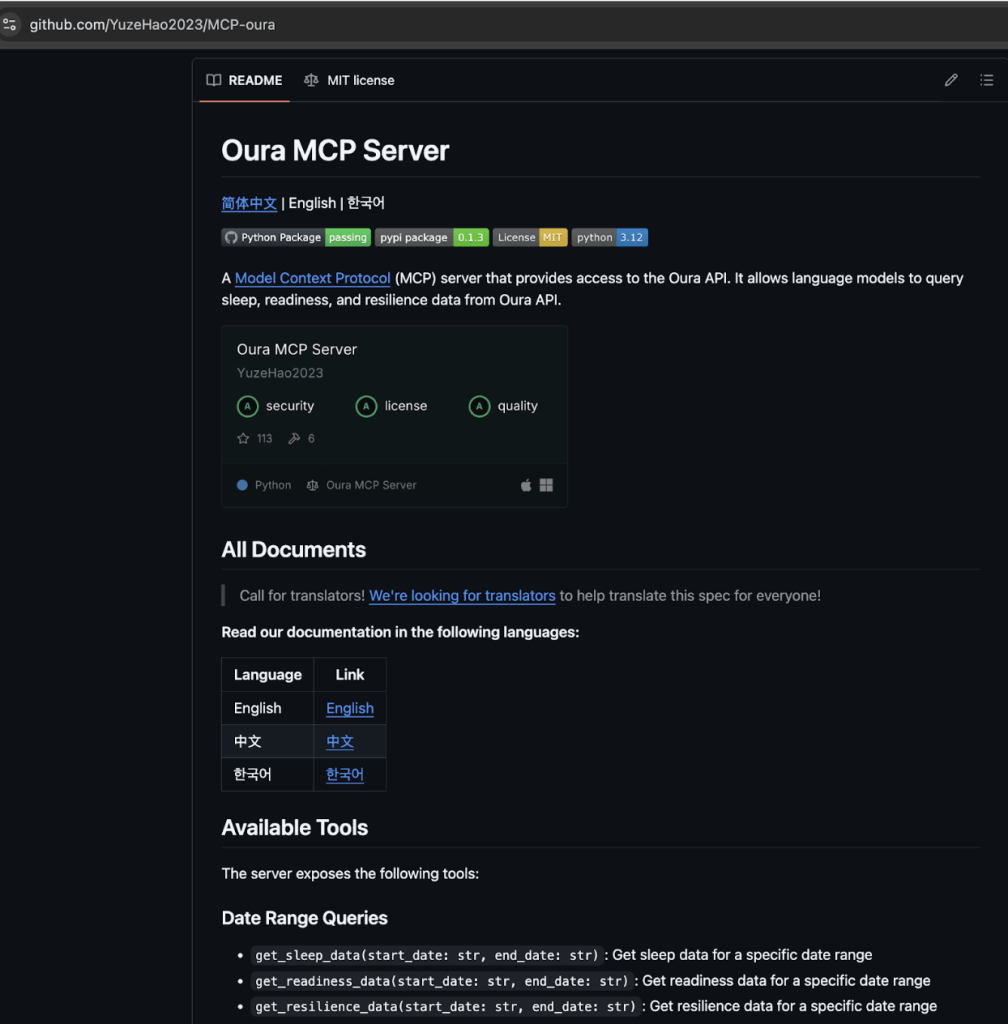
Next, the attackers created a network of fake GitHub accounts, forking the legitimate project to simulate real community interest. The main account, YuzeHao2023, created the initial clean fork:
Four additional accounts then forked the same project to make it appear popular and legitimate:
- https://github.com/yzhao112/MCP-oura
- https://github.com/punkpeye/MCP-oura
- https://github.com/dvlan26/MCP-oura
- https://github.com/halamji/MCP-oura
“These accounts exhibit characteristics consistent with AI-generated personas: recent creation dates, similar activity patterns, and commits concentrated in the same timeframe. The fake accounts also forked other projects from YuzeHao2023, creating a web of cross-references designed to make each account appear more established.” continues the report. “Any organization deploying MCP-enabled AI tools is vulnerable to supply chain compromise”
The researchers believe the accounts were AI-generated and cross-linked each other’s activity to appear established.
Once credibility was built, they launched a separate repository containing a trojanized version, deliberately excluding the original author to avoid scrutiny.
Finally, they submitted the malicious package to public MCP registries, so developers searching for Oura integrations would unknowingly download the infected version.
SmartLoader, a malware group known for spreading info-stealers through fake installers, has shifted tactics from targeting piracy users to compromising developers via the supply chain. The malware used LuaJIT, heavy virtual machine obfuscation, scheduled tasks disguised as Realtek drivers, and ultimately deployed StealC to steal passwords, crypto wallets, API keys, and cloud credentials. The infrastructure and techniques match known SmartLoader patterns, with indicators pointing to China-based operations. Security experts warn that developer environments are now prime targets and urge stronger vetting of AI tooling and MCP servers.
“SmartLoader’s campaign against the MCP ecosystem should serve as a wake-up call for security leaders. Threat actors have moved beyond opportunistic malware distribution and they are now investing in elaborate social engineering infrastructure to compromise developer supply chains.” concludes the report. “As AI assistants become integral to enterprise workflows, the MCP servers that extend their capabilities become a critical attack surface. Organizations that fail to secure this vector expose themselves to credential theft, data exfiltration, and supply chain compromise.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, malware)
如有侵权请联系:admin#unsafe.sh
