好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解其主要观点。 文章主要讨论了2022年和2026年恶意软件在32位和64位架构上的分布情况。作者在2022年写了一篇日记,指出尽管64位计算机普及,但32位恶意软件仍然是主流。现在到了2026年,作者再次分析数据,发现情况有所变化。 根据提供的统计数据,从2020年到2026年,总共分析了34万多份样本,其中31万多是32位的,3万多是64位的。但最近的数据显示,64位恶意软件的比例在上升,接近50%。这说明威胁行为者可能在调整策略,以适应更多64位系统。 接下来,我需要将这些信息浓缩到100字以内。要突出时间变化、数据对比以及趋势的变化。同时避免使用“这篇文章”或“内容总结”这样的开头。 可能会这样组织:指出时间跨度(从2020到2026),分析结果(31万32位 vs 3.4万64位),但最近的趋势显示64位比例上升接近50%,说明威胁行为者正在适应更多64位系统。 检查字数是否符合要求,并确保信息准确无误。 </think> 文章分析了从 2020 年到 2026 年的恶意软件架构分布情况。数据显示 31.8 万份为 32 位样本,而 3.5 万份为 64 位样本,占比约 11%。然而,近期数据显示 64 位恶意软件比例显著上升,接近50%。这表明威胁行为者正在逐步适应更多使用 64 位系统的环境。 2026-2-16 07:46:36 Author: isc.sans.edu(查看原文) 阅读量:11 收藏
In 2022 (time flies!), I wrote a diary about the 32-bits VS. 64-bits malware landscape[1]. It demonstrated that, despite the growing number of 64-bits computers, the "old-architecture" remained the standard. In the SANS malware reversing training (FOR610[2]), we quickly cover the main differences between the two architectures. One of the conclusions is that 32-bits code is still popular because it acts like a comme denominator and allows threat actors to target more Windows computers. Yes, Microsoft Windows can smoothly execute 32-bits code on 64-bits computers. It is still the case in 2026? Did the situation evolved?
Last week, I make the exact same exercise and generated some statistics. I download the malware archive from Malware Bazaar[3] and re-executed my YARA rule.
Some basic numbers:
- 2.167 ZIP archives (one per day)
- 1.120.034.288.112 bytes (1.1TB)
- Time line covered: from 2020/02/24 - 2026/02/05
- 346.985 samples analyzed (only PE files)
- 312.307 32-bits samples
- 34.677 64-bits samples
- 11% of 64-bits samples
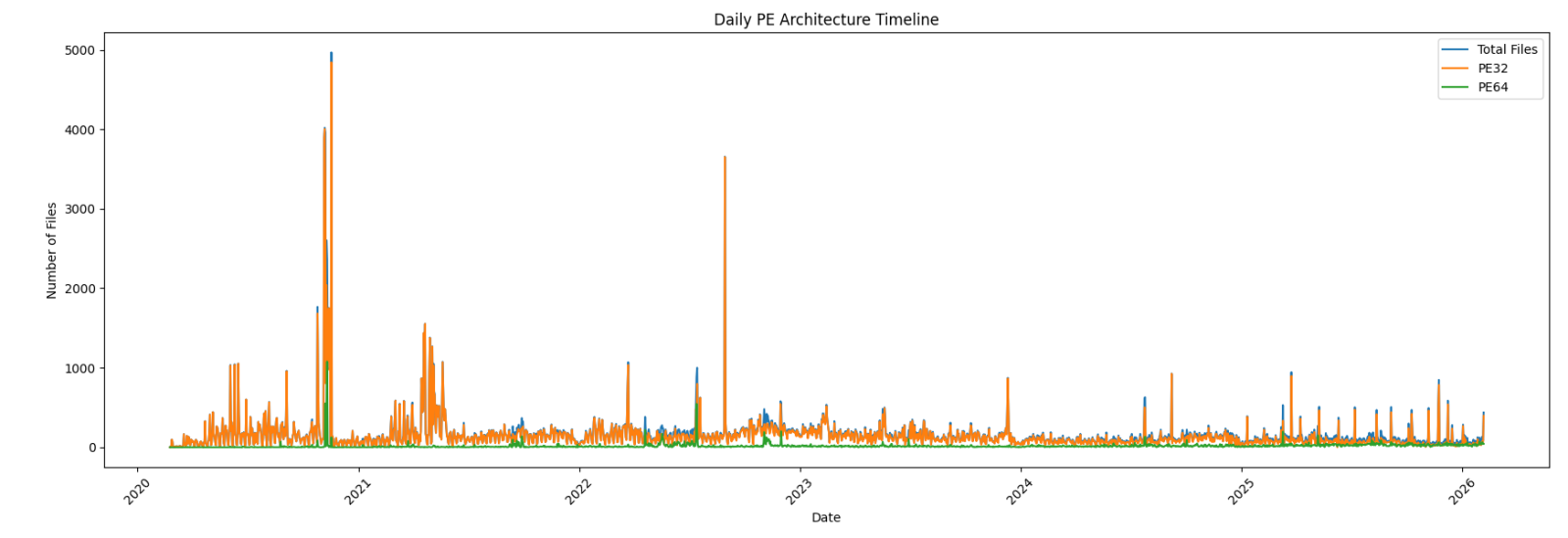
First, an overview of the global malware trend over the complete time period:
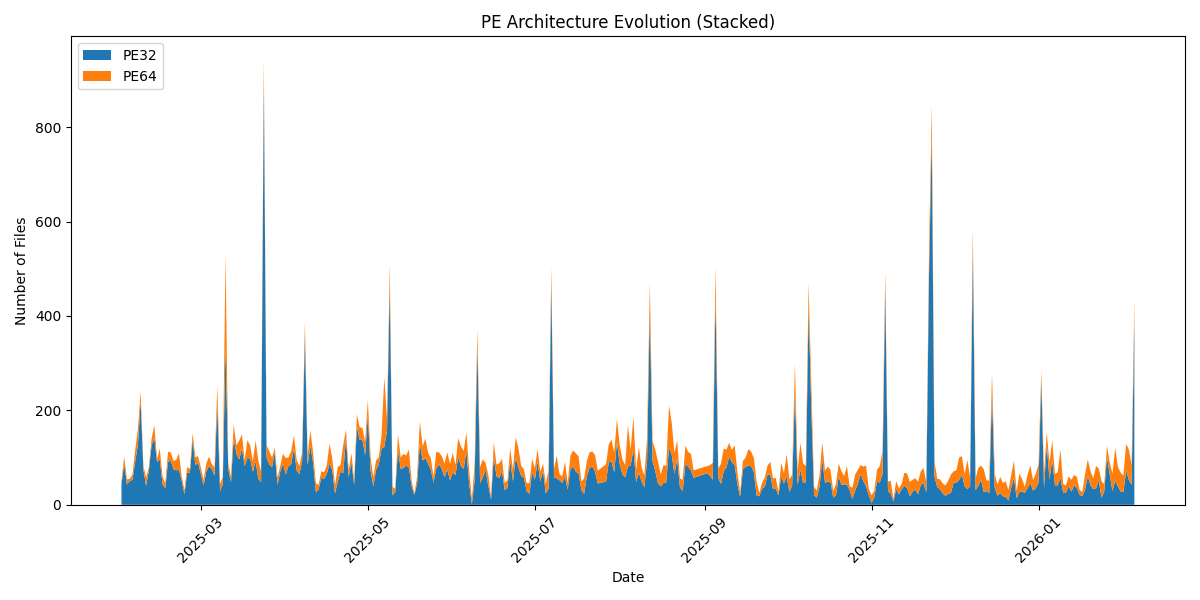
Zoom on the last year:
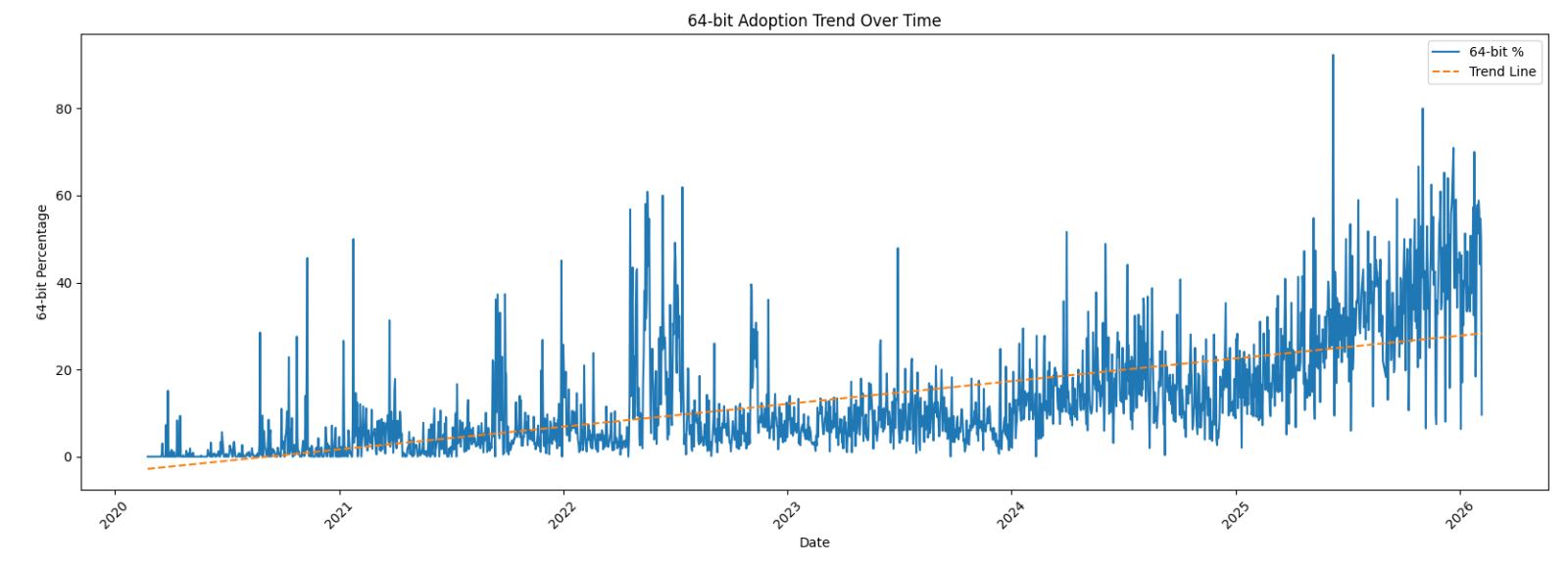
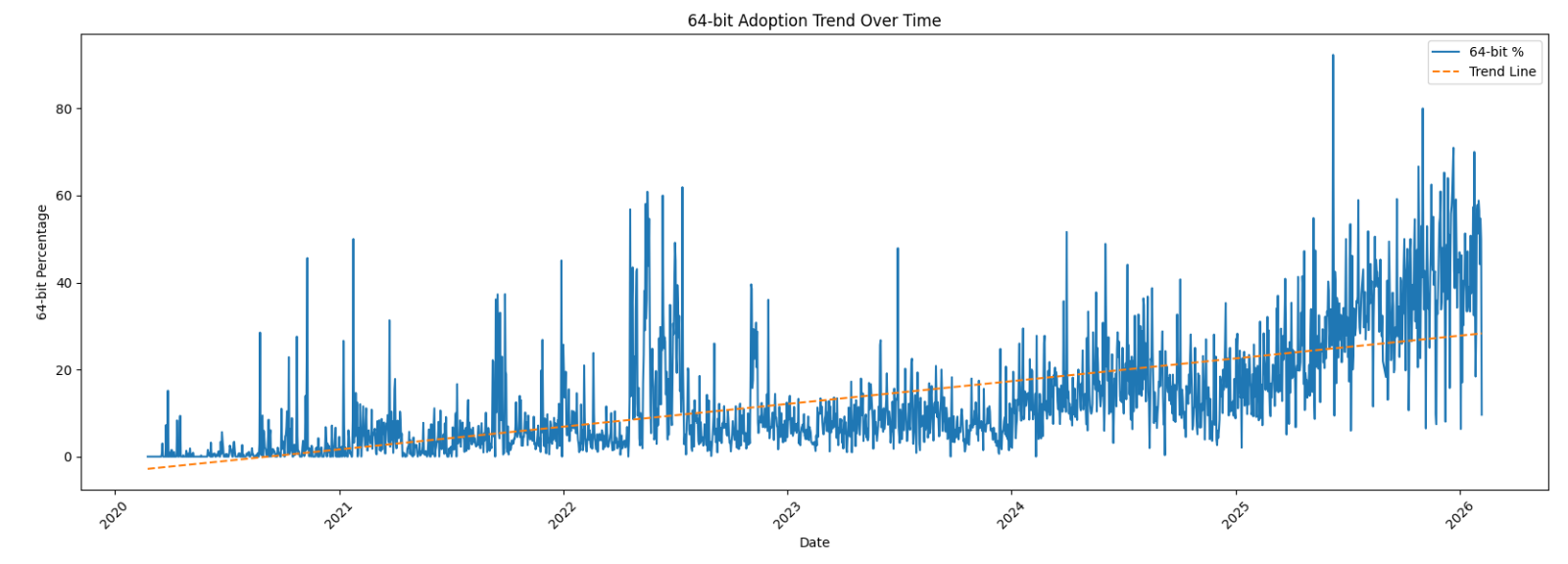
Now the interesting graph: the 64-bits sample trend over the complete period:
Zoom on the last year:
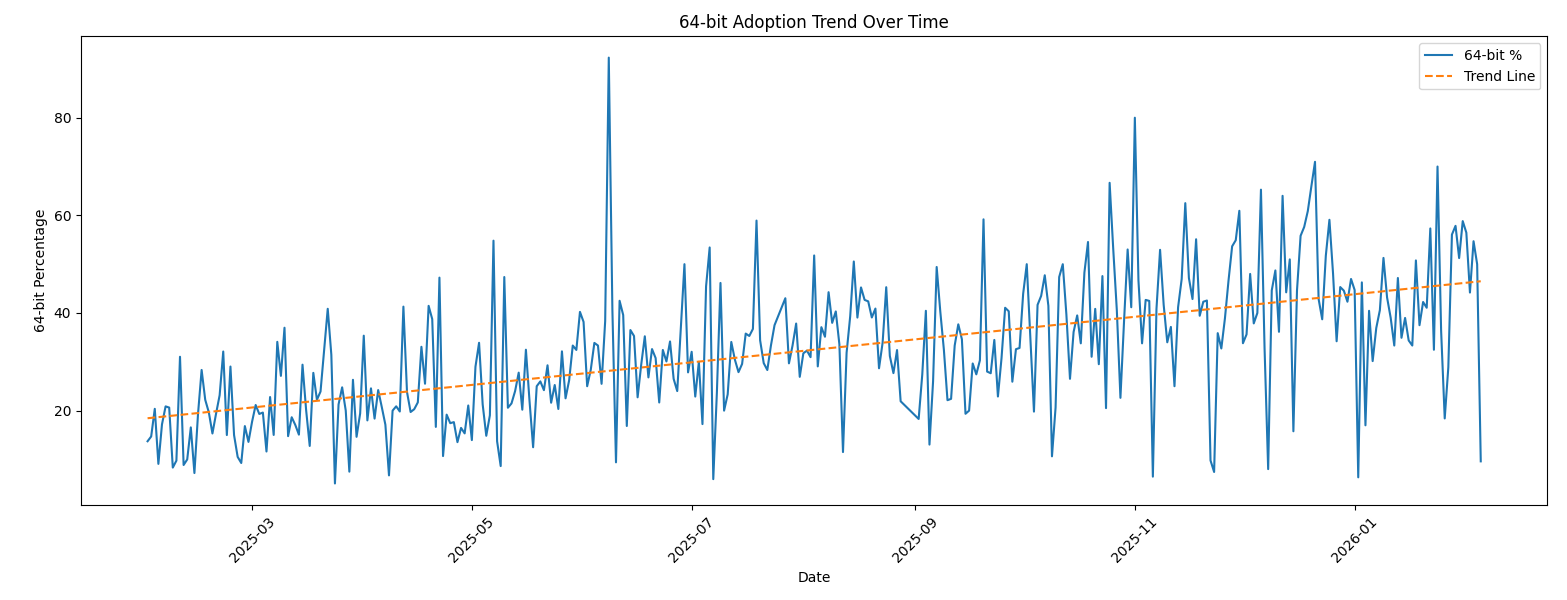
We can clearly see that, compared to 2022, there is now a trend in 64-bits code! Have a look at the last 30 days:
| Date | Total Files | 32-bits | 64-bits |
| 2026-01-07 | 65 | 41 | 24 |
| 2026-01-08 | 69 | 41 | 28 |
| 2026-01-09 | 117 | 57 | 60 |
| 2026-01-10 | 44 | 25 | 19 |
| 2026-01-11 | 41 | 25 | 16 |
| 2026-01-12 | 60 | 40 | 20 |
| 2026-01-13 | 53 | 28 | 25 |
| 2026-01-14 | 63 | 41 | 22 |
| 2026-01-15 | 59 | 36 | 23 |
| 2026-01-16 | 32 | 21 | 11 |
| 2026-01-17 | 27 | 18 | 9 |
| 2026-01-18 | 65 | 33 | 32 |
| 2026-01-19 | 96 | 60 | 36 |
| 2026-01-20 | 71 | 41 | 30 |
| 2026-01-21 | 56 | 33 | 23 |
| 2026-01-22 | 82 | 35 | 47 |
| 2026-01-23 | 77 | 52 | 25 |
| 2026-01-24 | 50 | 15 | 35 |
| 2026-01-25 | 44 | 28 | 16 |
| 2026-01-26 | 125 | 102 | 23 |
| 2026-01-27 | 90 | 64 | 26 |
| 2026-01-28 | 66 | 29 | 37 |
| 2026-01-29 | 121 | 51 | 70 |
| 2026-01-30 | 80 | 39 | 41 |
| 2026-01-31 | 68 | 28 | 40 |
| 2026-02-01 | 62 | 27 | 35 |
| 2026-02-02 | 129 | 72 | 57 |
| 2026-02-03 | 117 | 53 | 64 |
| 2026-02-04 | 84 | 42 | 42 |
| 2026-02-05 | 437 | 395 | 42 |
We are getting close to a 50-50 repartition!
???????
[1] https://isc.sans.edu/diary/32+or+64+bits+Malware/28968
[2] https://www.sans.org/cyber-security-courses/reverse-engineering-malware-malware-analysis-tools-techniques
[3] https://bazaar.abuse.ch
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
如有侵权请联系:admin#unsafe.sh