好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。用户已经给出了文章的详细内容,我需要先通读一遍,理解主要信息。 这篇文章主要讲的是研究人员发现恶意的npm和PyPI包与Lazarus APT组织的假招聘活动有关。Lazarus Group是朝鲜支持的黑客组织,他们通过伪装成区块链公司的招聘任务来诱骗开发者下载带有恶意软件的包。这个活动被命名为graphalgo,从2025年5月开始活跃,分为五个阶段,包括创建假公司、发布面试任务、吸引受害者、利用恶意依赖以及最终释放远程控制木马。 我需要将这些关键点浓缩到100字以内。首先,指出恶意包与Lazarus Group的关联。然后描述他们的手段:伪装成区块链公司发布招聘任务,利用npm和PyPI分发恶意软件。接着提到活动的时间和目标群体:自2025年5月起活跃,针对JavaScript和Python开发者。最后说明最终目标是植入远程控制木马。 现在组织语言:确保信息准确且简洁,避免冗余词汇。可能的结构是先介绍事件,然后描述手段和影响。 总结一下: 研究人员发现恶意npm和PyPI包与Lazarus APT组织的假招聘活动有关。该活动伪装成区块链公司发布招聘任务,诱导开发者下载包含恶意软件的包。自2025年5月起活跃,针对JavaScript和Python开发者,并植入远程控制木马。 检查字数是否在100字以内,并确保没有使用“文章内容总结”等开头。 </think> 研究人员发现恶意npm和PyPI包与Lazarus APT组织的假招聘活动有关。该活动伪装成区块链公司发布招聘任务,诱导开发者下载包含恶意软件的包。自2025年5月起活跃,针对JavaScript和Python开发者,并植入远程控制木马。 2026-2-15 18:13:28 Author: securityaffairs.com(查看原文) 阅读量:0 收藏
Malicious npm and PyPI packages linked to Lazarus APT fake recruiter campaign
Pierluigi Paganini
February 15, 2026

Researchers found malicious npm and PyPI packages tied to a fake recruitment campaign linked to North Korea’s Lazarus Group.
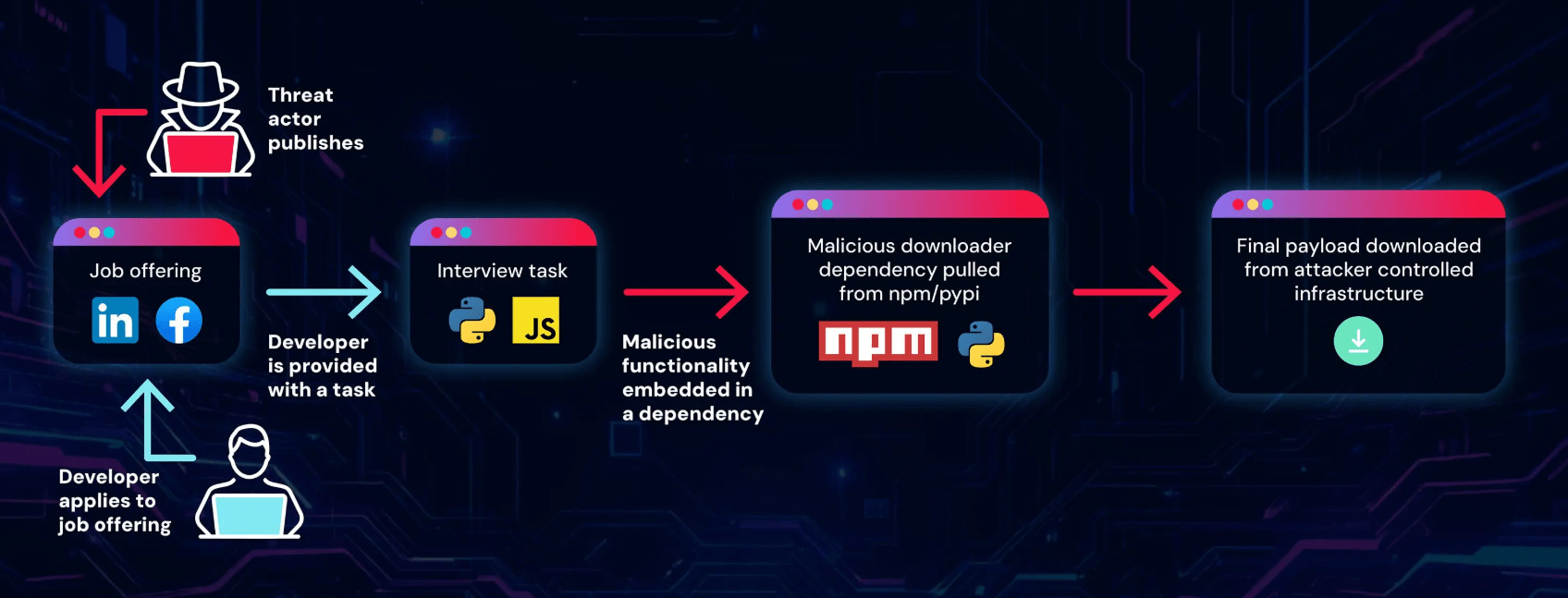
ReversingLabs researcher uncovered new malicious packages on npm and PyPI connected to a fake job recruitment campaign attributed to the North Korea-linked Lazarus Group. The campaign uses deceptive hiring themes to trick developers into downloading infected packages, continuing the group’s efforts to target the software supply chain.
“The ReversingLabs research team has identified a new branch of a fake recruiter campaign conducted by the North Korean hacking team Lazarus Group.” reads the report published by ReversingLabs. “The campaign, which the team named graphalgo, based on the first package included in this campaign in the npm repository, has been active since the beginning of May 2025.”
The campaign, tracked as ‘graphalgo’, has been active since May 2025 and targets JavaScript and Python developers with fake cryptocurrency recruiter tasks. Attackers approach victims on LinkedIn, Facebook, and Reddit, posing as a blockchain company. Malicious code is hidden through multiple public platforms, including GitHub, npm, and PyPI. The researchers noticed that one npm package, bigmathutils, gained over 10,000 downloads before attackers pushed a malicious update.
The Graphalgo campaign is a modular, multi-stage operation designed to stay active even if parts are exposed:
Phase 1 – Fake company:
Attackers created a fake blockchain firm, Veltrix Capital, with websites and GitHub organizations that look legitimate but lack real leadership details. When one setup risks exposure, they spin up a new company, domains, and AI-generated content to rebuild trust.
Phase 2 – Interview tasks:
The fake company publishes GitHub “job interview” repositories in Python and JavaScript. These projects look harmless, but they secretly depend on malicious npm or PyPI packages. When candidates run the tasks, the malicious dependency executes on their systems.
Phase 3 – Recruiting:
Victims are lured through Reddit, Facebook groups, LinkedIn, and direct recruiter messages. Some recruiters appear real, adding credibility, but disengage when questioned about the company.
Phase 4 – Malicious dependencies:
The backend relies on malicious open-source packages hosted on npm and PyPI. Early “graph-” packages impersonate popular libraries, while later “big-” packages build user trust first, then deliver malware in delayed updates.
Phase 5 – Final payload:
Infected systems download a RAT that supports file access, command execution, and process control. The malware uses token-protected C2 communication and checks for crypto wallets like MetaMask, pointing to financial theft motives.

North Korean threat actors, widely linked to the Lazarus Group, have a long track record of abusing npm and PyPI. In 2023, researchers exposed the VMConnect campaign, where fake PyPI packages tied to sham GitHub repos delivered malware. A year later, the operation evolved into fake recruiter coding tests: victims ran malicious packages disguised as interview tasks, triggering second-stage downloads. Reports from other cybersecurity firms, including Phylum, Unit 42, Veracode, and Socket, documented similar npm campaigns.
Attribution to Lazarus is based on repeated patterns: fake job interviews, crypto-focused lures, multistage encrypted malware, delayed malicious updates, token-protected C2, and GMT+9 timestamps. The campaign’s modular design allows attackers to swap fake “frontends” while reusing backend infrastructure. With new package waves and payload variants still emerging, the operation appears ongoing and highly sophisticated.
“Evidence suggests that this is a highly sophisticated campaign. Its modularity, long-lived nature, patience in building trust across different campaign elements, and the complexity of the multilayered and encrypted malware point to the work of a state-sponsored threat actor.” concludes the report. “Fake interviews as the initial contact vector, as well as a cryptocurrency-focused story and malware, together with other techniques mentioned in this blog post, point to North Korea’s Lazarus Group. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – malware, graphalgo campaign)
如有侵权请联系:admin#unsafe.sh
