Threat actors have started to exploit a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products, according to watchTowr.
"Overnight we observed first in-the-wild exploitation of BeyondTrust across our global sensors," Ryan Dewhurst, head of threat intelligence at watchTowr, said in a post on X. "Attackers are abusing get_portal_info to extract the x-ns-company value before establishing a WebSocket channel."
The vulnerability in question is CVE-2026-1731 (CVS score: 9.9), which could allow an unauthenticated attacker to achieve remote code execution by sending specially crafted requests.
BeyondTrust noted last week that successful exploitation of the shortcoming could allow an unauthenticated remote attacker to execute operating system commands in the context of the site user, resulting in unauthorized access, data exfiltration, and service disruption.
It has been patched in the following versions -
- Remote Support - Patch BT26-02-RS, 25.3.2 and later
- Privileged Remote Access - Patch BT26-02-PRA, 25.1.1 and later
The use of CVE-2026-1731 demonstrates how quickly threat actors can weaponize new vulnerabilities, significantly shrinking the window for defenders to patch critical systems.
CISA Adds 4 Flaws to KEV Catalog
The development comes as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added four vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The list of vulnerabilities is as follows -
- CVE-2026-20700 (CVSS score: 7.8) - An improper restriction of operations within the bounds of a memory buffer vulnerability in Apple iOS, macOS, tvOS, watchOS, and visionOS that could allow an attacker with memory write capability to execute arbitrary code.
- CVE-2025-15556 (CVSS score: 7.7) - A download of code without an integrity check vulnerability in Notepad++ that could allow an attacker to intercept or redirect update traffic to download and execute an attacker-controlled installer and lead to arbitrary code execution with the privileges of the user.
- CVE-2025-40536 (CVSS score: 8.1) - A security control bypass vulnerability in SolarWinds Web Help Desk that could allow an unauthenticated attacker to gain access to certain restricted functionality.
- CVE-2024-43468 (CVSS score: 9.8) - An SQL injection vulnerability in Microsoft Configuration Manager that could allow an unauthenticated attacker to execute commands on the server and/or underlying database by sending specially crafted requests.
It's worth noting that CVE-2024-43468 was patched by Microsoft in October 2024 as part of its Patch Tuesday updates. It's currently unclear how this vulnerability is being exploited in real-world attacks. Nor is there any information about the identity of the threat actors exploiting the flaw and the scale of such efforts.
The addition of CVE-2024-43468 to the KEV catalog follows a recent report from Microsoft about a multi‑stage intrusion that involved the threat actors exploiting internet‑exposed SolarWinds Web Help Desk (WHD) instances to obtain initial access and move laterally across the organization's network to other high-value assets.
However, the Windows maker said it's not evident if the attacks exploited CVE-2025-40551, CVE-2025-40536, or CVE-2025-26399, since attacks occurred in December 2025 and on machines vulnerable to both the old and new sets of vulnerabilities.
As for CVE-2026-20700, Apple acknowledged that the shortcoming may have been exploited in an extremely sophisticated attack against specific targeted individuals on versions of iOS before iOS 26, raising the possibility that it was leveraged to deliver commercial spyware. It was fixed by the tech giant earlier this week.
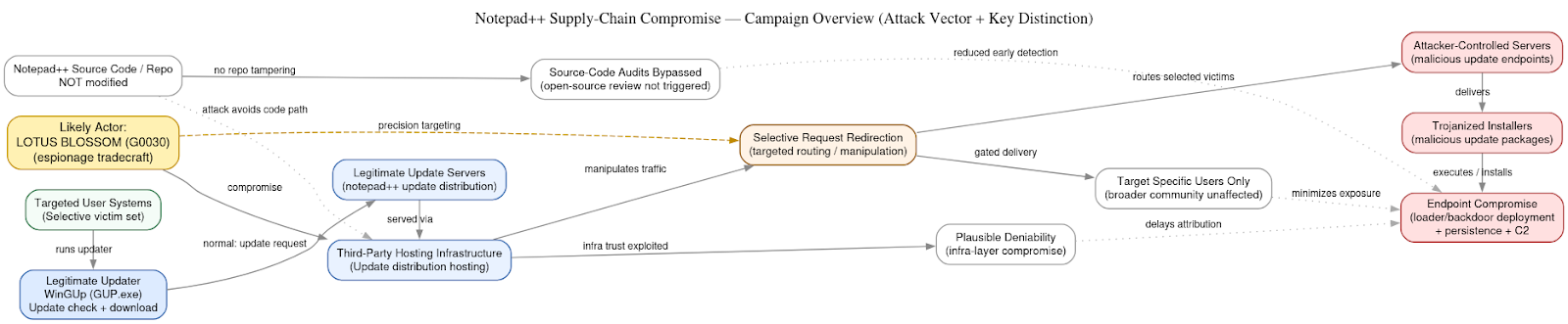
Lastly, the exploitation of CVE-2025-15556 has been attributed by Rapid7 to a China-linked state-sponsored threat actor called Lotus Blossom (aka Billbug, Bronze Elgin, G0030, Lotus Panda, Raspberry Typhoon, Spring Dragon, and Thrip). It's known to be active since at least 2009.
The targeted attacks have been found to deliver a previously undocumented backdoor called Chrysalis. While the supply chain attack was fully plugged on December 2, 2025, the compromise of the Notepad++ update pipeline is estimated to have spanned nearly five months between June and October 2025.
The DomainTools Investigations (DTI) team described the incident as precise and a "quiet, methodical intrusion" that points to a covert intelligence-gathering mission designed to keep operational noise as low as possible. It also characterized the threat actor as having a penchant for long dwell times and multi-year campaigns.
An important aspect of the campaign is that the Notepad++ source code was left intact, instead relying on trojanized installers to deliver the malicious payloads. This, in turn, allowed the attackers to bypass source-code reviews and integrity checks, effectively enabling them to stay undetected for extended periods, DTI added.
"From their foothold inside the update infrastructure, the attackers did not indiscriminately push malicious code to the global Notepad++ user base," it said. "Instead, they exercised restraint, selectively diverting update traffic for a narrow set of targets, organizations, and individuals whose positions, access, or technical roles made them strategically valuable."
"By abusing a legitimate update mechanism relied upon specifically by developers and administrators, they transformed routine maintenance into a covert entry point for high-value access. The campaign reflects continuity in purpose, a sustained focus on regional strategic intelligence, executed with more sophisticated, more subtle, and harder-to-detect methods than in prior iterations."
In light of active exploitation of these vulnerabilities, Federal Civilian Executive Branch (FCEB) agencies have until February 15, 2026, to address CVE-2025-40536, and till March 5, 2026, to fix the remaining three.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.