嗯,用户让我帮忙总结一篇文章,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。直接写描述即可。好的,我先看看文章内容。 文章讲的是ZeroDayRAT这个间谍软件,它可以让攻击者完全控制安卓和iOS设备。支持实时摄像头访问、键盘记录,还能窃取银行和加密货币数据。它通过Telegram销售,攻击者自己搭建服务器,生成恶意应用感染受害者。控制面板功能强大,能实时监控位置、通知、消息等,还能窃取各种账户信息和进行金融盗窃。 用户的需求是简短的总结,所以我要抓住关键点:ZeroDayRAT是什么、它的功能、传播方式以及威胁。还要注意字数限制,大约100字左右。 可能的结构是:介绍ZeroDayRAT的功能和影响,然后提到它的传播方式和威胁性。比如:“ZeroDayRAT是一种商业间谍软件工具包,允许攻击者完全控制Android和iOS设备。它支持实时摄像头访问、键盘记录和数据窃取,并通过恶意应用感染用户。该工具包功能强大且易于使用,对个人和组织构成严重威胁。” 这样既涵盖了主要功能,又说明了传播方式和威胁性,符合用户的要求。 </think> ZeroDayRAT是一种商业间谍软件工具包,允许攻击者完全控制Android和iOS设备。它支持实时摄像头访问、键盘记录和数据窃取,并通过恶意应用感染用户。该工具包功能强大且易于使用,对个人和组织构成严重威胁。 2026-2-10 15:19:27 Author: securityaffairs.com(查看原文) 阅读量:4 收藏
ZeroDayRAT spyware grants attackers total access to mobile devices
Pierluigi Paganini
February 10, 2026

ZeroDayRAT is a commercial mobile spyware that grants full remote access to Android and iOS devices for spying and data theft.
ZeroDayRAT is a newly discovered commercial mobile spyware toolkit that gives attackers full control over Android and iOS devices. It supports live camera access, keylogging, and theft of banking and crypto data.
First spotted in February 2026 and analyzed by iVerify, it is sold on Telegram and rivals tools usually built by nation-states. Attackers host their own servers and generate malicious apps to infect victims.
The seller runs sales, support, and update channels and gives buyers an easy-to-use control panel. From it, attackers can fully control Android and iOS devices, watch users in real time, and steal money. ZeroDayRAT works on a wide range of phones and needs no technical skills. Attackers usually infect victims through smishing texts, phishing emails, fake apps, or malicious links shared on messaging platforms.
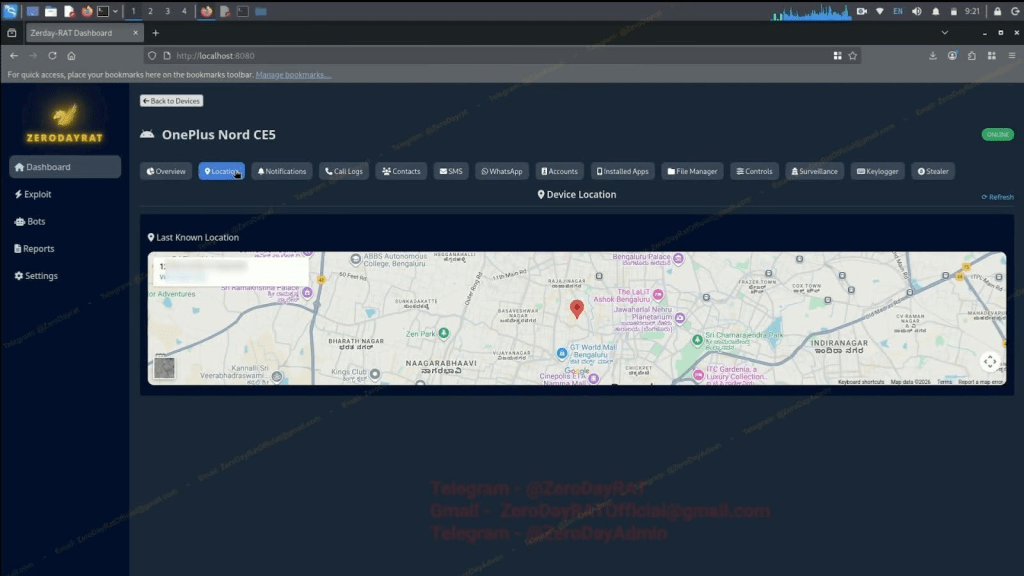
After infecting a mobile device, ZeroDayRAT shows operators a detailed overview of the device. The panel displays the phone model, operating system, battery level, country, SIM and carrier details, app usage, recent activity, and SMS previews on one screen. This already lets attackers profile the victim’s habits, contacts, and daily activity.
From there, operators can track real-time and historical GPS locations on a map, monitor notifications from all apps, and see alerts, messages, and missed calls without opening any app.

A dedicated accounts section lists every service linked to the device.
“One of the more problematic panels is the accounts tab. Every account registered on the device is enumerated: Google, WhatsApp, Instagram, Facebook, Telegram, Amazon, Flipkart, PhonePe, Paytm, Spotify, and more, each with its associated username or email.” reads the report published by iVerify. “This is basically everything an attacker needs to attempt account takeover or launch targeted social engineering.”
ZeroDayRAT also enables live surveillance, not just data collection. From one panel, operators can stream the phone’s camera, record the screen, and listen through the microphone in real time, while tracking the device’s location.
“The surveillance tab crosses into real-time physical access: live camera streaming (front or back), screen recording, and a microphone feed.” continues the report. “Combined with GPS tracking, an operator can watch, listen to, and locate a target simultaneously.”

A built-in keylogger records every action with precise timestamps, including keystrokes, gestures, app launches, and unlocks. A live screen preview lets attackers watch what the victim is doing as it happens.
ZeroDayRAT also supports direct financial theft. Its crypto stealer component scans the device for wallet apps, records wallet IDs and balances, and hijacks clipboard data to replace copied wallet addresses with the attacker’s own. A separate banking module targets mobile banking apps, UPI services, and payment platforms like Apple Pay and PayPal, using overlays to steal login details. From one control panel, operators can attack both crypto assets and traditional financial accounts.
“Taken together, this is a complete mobile compromise toolkit, the kind that used to require nation-state investment or bespoke exploit development, now sold on Telegram.” concludes the report. “A single buyer gets full access to a target’s location, messages, finances, camera, microphone, and keystrokes from a browser tab. Cross-platform support and active development make it a growing threat to both individuals and organizations.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, spyware)
如有侵权请联系:admin#unsafe.sh