Microsoft has revealed that it observed a multi‑stage intrusion that involved the threat actors exploiting internet‑exposed SolarWinds Web Help Desk (WHD) instances to obtain initial access and move laterally across the organization's network to other high-value assets.
That said, the Microsoft Defender Security Research Team said it's not clear whether the activity weaponized recently disclosed flaws (CVE-2025-40551, CVSS score: 9.8, and CVE-2025-40536, CVSS score: 8.1), or a previously patched vulnerability (CVE-2025-26399, CVSS score: 9.8).
"Since the attacks occurred in December 2025 and on machines vulnerable to both the old and new set of CVEs at the same time, we cannot reliably confirm the exact CVE used to gain an initial foothold," the company said in a report published last week.
While CVE-2025-40536 is a security control bypass vulnerability that could allow an unauthenticated attacker to gain access to certain restricted functionality, CVE-2025-40551 and CVE-2025-26399 both refer to untrusted data deserialization vulnerabilities that could lead to remote code execution.
Last week, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2025-40551 to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. Federal Civilian Executive Branch (FCEB) agencies were ordered to apply the fixes for the flaw by February 6, 2026.
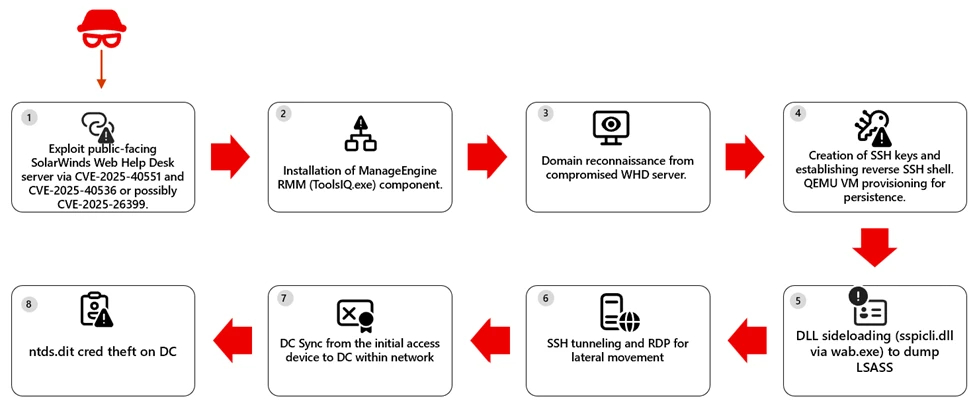
In the attacks detected by Microsoft, successful exploitation of the exposed SolarWinds WHD instance allowed the attackers to achieve unauthenticated remote code execution and run arbitrary commands within the WHD application context.
"Upon successful exploitation, the compromised service of a WHD instance spawned PowerShell to leverage BITS [Background Intelligent Transfer Service] for payload download and execution," researchers Sagar Patil, Hardik Suri, Eric Hopper, and Kajhon Soyini noted.
In the next stage, the threat actors downloaded legitimate components associated with Zoho ManageEngine, a legitimate remote monitoring and management (RMM) solution, to enable persistent remote control over the infected system. The attackers followed it up with a series of actions -
- Enumerated sensitive domain users and groups, including Domain Admins.
- Established persistence via reverse SSH and RDP access, with the attackers also attempting to create a scheduled task to launch a QEMU virtual machine under the SYSTEM account at system startup to cover up the tracks within a virtualized environment while exposing SSH access via port forwarding.
- Used DLL side-loading on some hosts by using "wab.exe," a legitimate system executable associated with the Windows Address Book, to launch a rogue DLL ("sspicli.dll") to dump the contents of LSASS memory and conduct credential theft.
In at least one case, Microsoft said the threat actors conducted a DCSync attack, where a Domain Controller (DC) is simulated to request password hashes and other sensitive information from an Active Directory (AD) database.
To counter the threat, users are advised to keep the WHD instances up-to-date, find and remove any unauthorized RMM tools, rotate service and admin accounts, and isolate compromised machines to limit the breach.
"This activity reflects a common but high-impact pattern: a single exposed application can provide a path to full domain compromise when vulnerabilities are unpatched or insufficiently monitored," the Windows maker said.
"In this intrusion, attackers relied heavily on living-off-the-land techniques, legitimate administrative tools, and low-noise persistence mechanisms. These tradecraft choices reinforce the importance of defense in depth, timely patching of internet-facing services, and behavior-based detection across identity, endpoint, and network layers."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.