好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读用户提供的文章内容。 文章主要讲的是最近收到的钓鱼邮件中包含了一些奇怪的URL。这些URL的参数部分出现了问题,比如参数格式不正确,包含类似“&*(Df”这样的无效字符。虽然浏览器会忽略这些错误,但恶意网站仍然会被访问。 接下来,作者提到这种技术已经有一段时间没见到了,但现在又重新出现。威胁行为者使用这种方法来绕过安全控制措施,因为很多安全系统假设参数是“key=value”的格式。这可能导致正则表达式检测、URL规范化或IOC提取失败。 最后,作者建议使用正则表达式提取最后一个参数来跟踪这些URL,并提供了自己的联系方式。 现在,我需要将这些信息浓缩到100字以内。重点包括:钓鱼邮件、奇怪URL、参数格式错误、浏览器忽略导致访问恶意网站、绕过安全控制的技术、影响检测机制。 可能的结构:最近收到钓鱼邮件,包含奇怪URL,参数格式错误导致安全措施失效,浏览器仍能访问恶意网站。 这样应该能准确概括文章内容,并且符合字数限制。 </think> 最近收到的钓鱼邮件中包含奇怪的URL,其参数格式错误(如“&*(Df”),尽管浏览器会忽略这些错误并访问恶意网站。这种技术用于绕过安全控制措施,可能破坏基于正则表达式的检测和IOC提取流程。 2026-2-5 08:43:2 Author: isc.sans.edu(查看原文) 阅读量:5 收藏
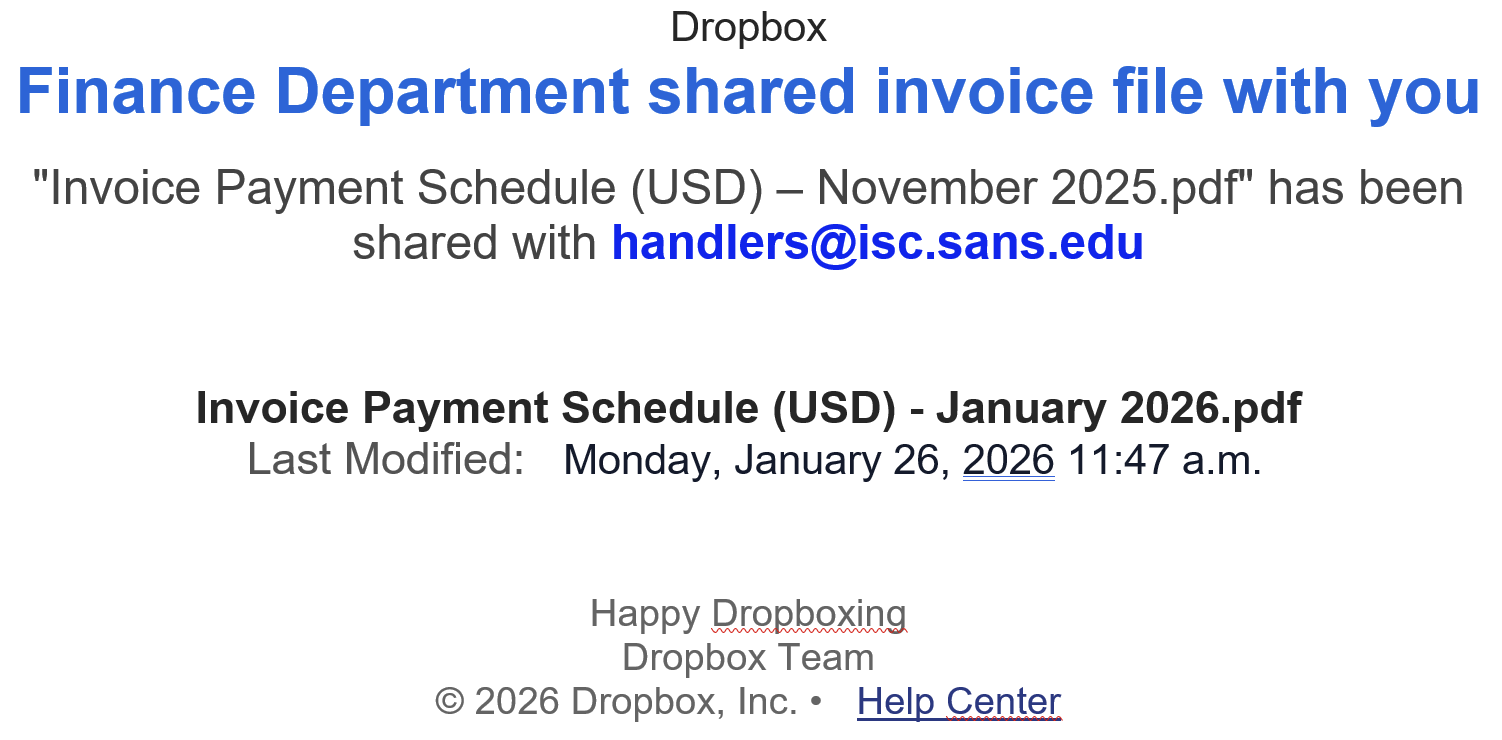
For a few days, many phishing emails that landed into my mailbox contain strange URLs. They are classic emails asking you to open a document, verify your pending emails, …
But the format of the URLs is broken! In a URL, parameters are extra pieces of information added after a question mark (?) to tell a website more details about a request; they are written as name=value pairs (for example “email=user@domain”), and multiple parameters are separated by an ampersand (&).
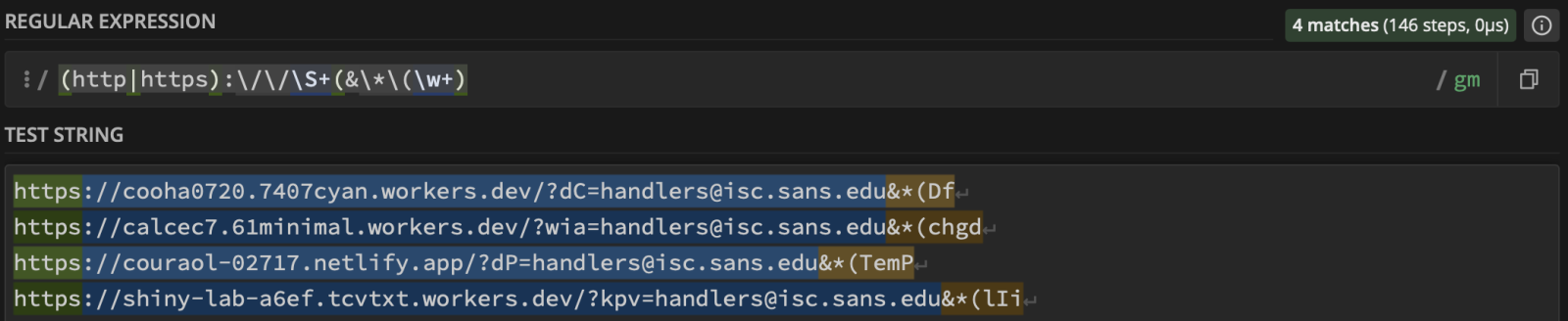
Here are some examples of detected URLs:
hxxps://cooha0720[.]7407cyan[.]workers[.]dev/?dC=handlers@isc[.]sans[.]edu&*(Df hxxps://calcec7[.]61minimal[.]workers[.]dev/?wia=handlers@isc[.]sans[.]edu&*(chgd hxxps://couraol-02717[.]netlify[.]app/?dP=handlers@isc[.]sans[.]edu&*(TemP hxxps://shiny-lab-a6ef[.]tcvtxt[.]workers.dev/?kpv=handlers@isc[.]sans[.]edu&*(lIi
You can see that the parameters are broken… “&*(Df” is invalid! It’s not an issue for browsers that will just ignore these malformed parameters, so the malicious website will be visited.
I did not see this for a while but it seems that the technique is back on stage. Threat actors implement this to break security controls. Many of them assume a “key=value" format. It may also break regex-based detectionn, URL normalization routines or IOC extraction pipelines…
Of course, we can track such URLs using a regex to extract the last param:
 ???????
???????
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
如有侵权请联系:admin#unsafe.sh