文章探讨了内部威胁对组织的影响及其演变趋势。2025年数据显示,电信、金融和科技行业成为主要目标。内部威胁通过社交工程和技术手段招募员工或利用人为错误获取敏感信息。识别异常行为、财务变化和网络流量异常是防范的关键。未来,随着AI技术发展和平台迁移,内部威胁风险将持续增加。 2026-1-15 19:35:10 Author: flashpoint.io(查看原文) 阅读量:2 收藏
Every organization houses sensitive assets that threat actors actively seek. Whether it is proprietary trade secrets, intellectual property, or the personally identifiable information (PII) of employees and customers, these datasets are the lifeblood of the modern enterprise—and highly lucrative commodities within the illicit underground.
In 2025, Flashpoint observed 91,321 instances of insider recruiting, advertising, and threat actor discussions involving insider-related illicit activity. This underscores a critical reality—it is far more efficient for threat actors to recruit an “insider” to circumvent multi-million dollar security stacks than it is to develop a complex exploit from the outside.
An insider threat, any individual with authorized access, possesses the unique ability to bypass traditional security gates. Whether driven by financial gain, ideological grievances, or simple human error, insiders can potentially compromise a system with a single keystroke. To protect our customers from this internal risk, Flashpoint monitors the illicit forums and marketplaces where these threats are being solicited.
In this post, we unpack the evolving insider threat landscape and what it means for your security strategy in 2026. By analyzing the volume of recruitment activity and the specific industries being targeted, organizations can move from a reactive posture to a proactive defense.
By the Numbers: Mapping the 2025 Insider Threat Landscape
Last year, Flashpoint collected and researched:
- 91,321 posts of insider solicitation and service advertising
- 10,475 channels containing insider-related illicit activity
- 17,612 total authors
On average, 1,162 insider-related posts were published per month, with Telegram continuing to be one of the most prominent mediums for insiders and threat actors to identify and collaborate with each other. Analysts also identified instances of extortionist groups targeting employees at organizations to financially motivate them to become insiders.
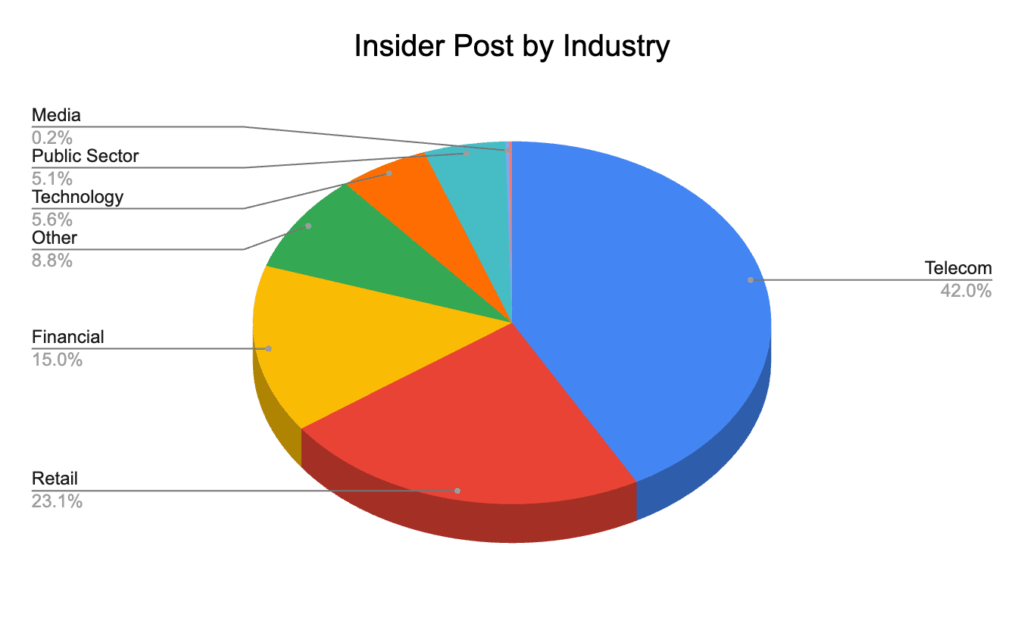
Insider Threat Landscape by Industry
The telecommunications industry observed the most insider-related activity in 2025. This is due to the industry’s central role in identity verification and its status as the primary target for SIM swapping—a fraudulent technique where threat actors convince employees of a mobile carrier to link a victim’s phone number to a SIM card controlled by the attacker. This allows the threat actor to receive all the victim’s calls and texts, allowing them to bypass SMS-based two-factor authentication.

Flashpoint analysts identified 12,783 notable posts where the level of detail or the specific target was particularly concerning.
Top Industries for Insiders Advertising Services (Supply):
- Telecom
- Financial
- Retail
- Technology
Top Industries for Threat Actors Soliciting Access (Demand):
- Technology
- Financial
- Telecom
- Retail
5 Notable Insider Threat Cases of 2025
The following cases highlight the variety of ways insiders impacted enterprise systems this year, ranging from intentional fraud to massive technical oversights.
| Type of Incident | Description |
| Malicious | Approximately nine employees accessed the personal information of over 94,000 individuals, making illegal purchases using changed food stamp cards. |
| Nonmalicious | An unprotected database belonging to a Chinese IoT firm leaked 2.7 billion records, exposing 1.17 TB of sensitive data and plaintext passwords. |
| Malicious | An employee working for a foreign military contractor was bribed to pass confidential information to threat actors. |
| Malicious | A third-party contractor for a cryptocurrency firm sold customer data to threat actors and recruited colleagues into the scheme, leading to the termination of 300 employees and the compromise of 69,000 customers. |
| Malicious | Two contractors accessed and deleted sensitive documents and dozens of databases belonging to the Internal Revenue Service and US General Services Administration. |
Catching the Warning Signs Early
Potential insiders often display technical and nontechnical behavior before initiating illicit activity. Although these actions may not directly implicate an employee, they can be monitored, which may lead to inquiries or additional investigations to better understand whether the employee poses an elevated risk to the organization.
Flashpoint has identified the following nontechnical warning signs associated with insiders:
- Behavioral indicators: Observable actions that deviate from a known baseline of behaviors. These can be observed by coworkers or management or through technical indicators. Behavioral indicators can include increasingly impulsive or erratic behavior, noncompliance with rules and policies, social withdrawal, and communications with competitors.
- Financial changes: Significant and overlapping changes in financial standing—such as significant debt, financial troubles, or sudden unexplained financial gain—could indicate a potential insider threat. In the case of financial distress, an employee can sell their services to other threat actors via forums or chat services, thus creating additional funding streams while seeming benign within their organization.
- Abnormal access behavior: Resistance to oversight, unjustified requests for sensitive information beyond the employee’s role, or the employee being overprotective of their access privileges might indicate malicious intent.
- Separation on bad terms: Employees who leave an organization under unfavorable circumstances pose an increased insider threat risk, as they might want to seek revenge by exploiting whatever access they had or might still possess after leaving.
- Odd working hours: Actors may leverage atypical after-hours work to pursue insider threat activity, as there is less monitoring. By sticking to an atypical schedule, threat actors maintain a cover of standard work activity while pursuing illicit activity simultaneously.
- Unusual overseas travel: Unusual and undocumented overseas travel may indicate an employee’s potential recruitment by a foreign state or state-sponsored actor. Travel might be initiated to establish contact and pass sensitive information while avoiding raising suspicions in the recruit’s home country.
The following are technical warning signs:
- Unauthorized devices: Employees using unauthorized devices for work pose an insider threat, whether they have malicious intent or are simply putting themselves at higher risk of human error. Devices that are not controlled and monitored by the organization fall outside of its scope of operational security, while still carrying all of the sensitive data and configuration of the organization.
- Abnormal network traffic: An unusual increase in network traffic or unexplained traffic patterns associated with the employee’s device that differ from their normal network activity could indicate malicious intent. This includes network traffic employing unusual protocols, using uncommon ports, or an overall increase in after-hours network activity.
- Irregular access pattern: Employees accessing data outside the scope of their job function may be testing and mapping the limits of their access privileges to restricted areas of information as they evaluate their exfiltration capabilities for their planned illicit actions.
- Irregular or mass data download: Unexpected changes in an employee’s data handling practices, such as irregular large-scale downloads, unusual data encryption, or uncharacteristic or unauthorized data destinations, are significant indicators of an insider threat.
Insider Threats: What to Expect in 2026
As 2026 unfolds, insider threat actors will continue to be a major threat to organizations. Ransomware groups and initial access threat actors will continue recruiting interested insiders and exploiting human vulnerabilities through social engineering tactics. Following Telegram’s recent bans on many illicit groups and channels, Flashpoint assesses that threat actors are likely to migrate to different platforms, such as Signal, where encrypted chats make their activity harder to monitor.
As AI technologies continue to advance, organizations will be better equipped to identify and mitigate insider risks. At the same time, threat actors will likely increasingly abuse AI and other tools to access sensitive information.
Is your organization equipped to spot the warning signs? Request a demo to learn more and to mitigate potential risk from within your organization.
如有侵权请联系:admin#unsafe.sh