Cisco published advisories and a supplemental post about three zero-day vulnerabilities, two of which were exploited in the wild by an advanced threat actor associated with the ArcaneDoor campaign.
Update September 25: This FAQ blog has been updated to include a reference to an NCSC report on associated malware linked to this campaign.
Background
Tenable’s Research Special Operations (RSO) team has compiled this blog to answer Frequently Asked Questions (FAQ) regarding newly disclosed zero-day vulnerabilities in Cisco Adaptive Security Appliance (ASA) Software and Firewall Threat Defense (FTD) Software that were exploited.
FAQ
When were these vulnerabilities first disclosed?
On September 25, Cisco published advisories [1, 2, 3] and a supplemental post regarding three zero-day vulnerabilities in Cisco Adaptive Security Appliance (ASA) Software, Firewall Threat Defense (FTD) Software, IOS XE Software, and IOS XR Software.
What are the vulnerabilities that were disclosed?
The following three vulnerabilities were disclosed. Two (CVE-2025-20333, CVE-2025-20362) were exploited in the wild.
| CVE | Description | CVSSv3 | Exploited |
|---|---|---|---|
| CVE-2025-20333 | Cisco ASA and FTD Software VPN Web Server Remote Code Execution Vulnerability (RCE) | 9.9 | Yes |
| CVE-2025-20362 | Cisco ASA and FTD Software VPN Web Server Unauthorized Access Vulnerability | 6.5 | Yes |
| CVE-2025-20363 | Cisco ASA and FTD Software, IOS Software, IOS XE Software, and IOS XR Software Web Services RCE | 9.0 | No |
Were these vulnerabilities exploited as zero-days?
Yes, according to Cisco, CVE-2025-20333 and CVE-2025-20362 were exploited in the wild as zero-days. Both of these vulnerabilities, when chained together, allow an attacker to take over a vulnerable device.
Which threat actors are exploiting these vulnerabilities?
According to Cisco, the malicious activity associated with CVE-2025-20333 and CVE-2025-20362 is linked to UAT4356, also known as Storm-1849, the same threat actor behind the ArcaneDoor campaign from April 2024.
Did UAT4356/Storm-1849 exploit any vulnerabilities in the ArcaneDoor campaign?
Yes, UAT4356 leveraged two vulnerabilities in the ArcaneDoor campaign:
CVE-2024-20353
Cisco ASA and Firepower Threat Defense (FTD) Software Web Services Denial of Service Vulnerability
Campaign
ArcaneDoor
Threat Actors
UAT4356 STORM-1849
Associated Malware
LINE DANCER LINE RUNNER
Source: talosintelligence.com
CVE-2024-20359
Cisco ASA and FTD Software Persistent Local Code Execution Vulnerability
Campaign
ArcaneDoor
Threat Actors
UAT4356 STORM-1849
Associated Malware
LINE DANCER LINE RUNNER
Source: talosintelligence.com
Was any malware used by UAT4356/Storm-1849 in this recent campaign?
The National Cyber Security Centre (NCSC) published an alert and a malware analysis report (MAR) detailing two pieces of malware associated with this campaign. The first malware, RayInitiator, is a multi-stage bootkit designed for persistence even if a device is rebooted or upgraded. The second malware, LINE VIPER, is a user-mode shellcode loader that deploys modular payloads to enable various post-compromise activities. It can be tasked and controlled through either HTTPS-based WebVPN sessions or ICMP.
Is there a proof-of-concept (PoC) available for these vulnerabilities?
At the time this blog was published, there were no public proof-of-concept (PoC) exploits for any of the vulnerabilities associated with this campaign.
Cisco also patched CVE-2025-20363. Was this also exploited in the wild?
No. Cisco did not specifically call out CVE-2025-20363 as being exploited in the wild. According to the advisory, Cisco says it was found by members of Cisco’s Advanced Security Initiatives Group (ASIG) as part of a support case.
Are patches or mitigations available for CVE-2025-20333, CVE-2025-20362, CVE-2025-20363?
Yes, Cisco has released the following fixes for Cisco ASA and FTD.
| CVE | Affected Product | Affected Versions | Fixed Version |
|---|---|---|---|
| CVE-2025-20333 | Cisco ASA Software | 9.16, 9.17, 9.18, 9.19, 9.20, 9.22 | 9.16.4.85, 9.17.1.45, 9.18.4.47, 9.19.1.37, 9.20.3.7, 9.22.1.3 |
| CVE-2025-20333 | Cisco FTD Software | 7.0, 7.2, 7.4, 7.6 | 7.0.8.1, 7.2.9, 7.4.2.4, 7.6.1 |
| CVE-2025-20363 | Cisco ASA Software | 9.16, 9.18, 9.19, 9.20, 9.22, 9.23 | 9.16.4.84, 9.18.4.57, 9.19.1.42, 9.20.3.16, 9.22.2, 9.23.1.3 |
| CVE-2025-20363 | Cisco FTD Software | 7.0, 7.2, 7.4, 7.6, 7.7 | 7.0.8, 7.2.10, 7.4.2.3, 7.6.1, 7.7.10 |
| CVE-2025-20362 | Cisco ASA Software | 9.16, 9.18, 9.20, 9.22, 9.23 | 9.16.4.85, 9.18.4.67, 9.20.4.10, 9.22.2.14, 9.23.1.19 |
| CVE-2025-20362 | Cisco FTD Software | 7.0, 7.2, 7.4, 7.6, 7.7 | 7.0.8.1, 7.2.10.2, 7.4.2.4, 7.6.2.1, 7.7.10.1 |
Cisco ASA Software:
- Cisco customers on the 9.17 branch must migrate to a fixed release to address CVE-2025-20363
- Cisco customers on the 9.17 and 9.19 branches must migrate to a fixed release to address CVE-2025-20362.
Cisco FTD Software:
- Cisco customers on the 7.1 and 7.3 branches must migrate to a fixed release to address all three vulnerabilities.
Has Tenable released any product coverage for these vulnerabilities?
A list of Tenable plugins for these vulnerabilities can be found on the individual CVE pages as they’re released:
This link will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.
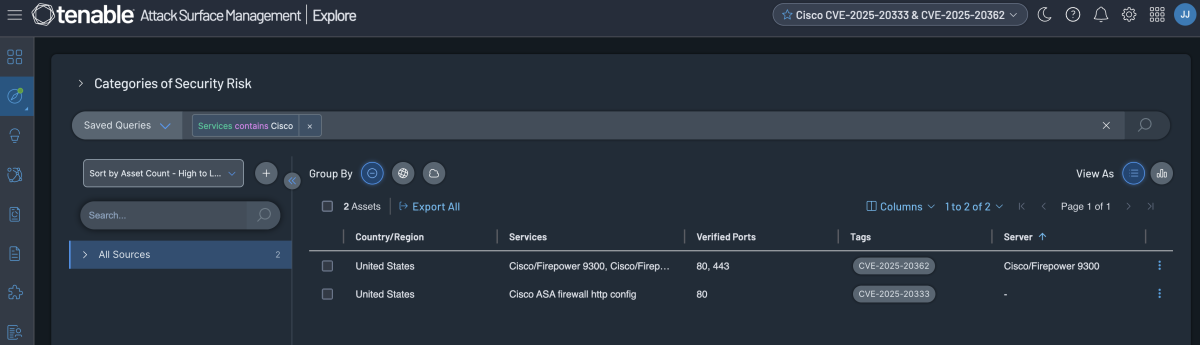
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing Cisco devices by using the following query:
Change Log
Update September 25: This FAQ blog has been updated to include a reference to an NCSC report on associated malware linked to this campaign.
Get more information
Join on Tenable Connect and engage with us in the for further discussions on the latest cyber threats.
Learn more about , the Exposure Management Platform for the modern attack surface.
*** This is a Security Bloggers Network syndicated blog from Tenable Blog authored by Satnam Narang. Read the original post at: https://www.tenable.com/blog/cve-2025-20333-cve-2025-20362-faq-cisco-asa-ftd-zero-days-uat4356

