0x00 Powershell ExecutionPolicy(执行策略)
设置执行策略(Set-ExecutionPolicy)
Powershell默认的权限策略是:“Restricted”
查看当前执行策略:
PS C:> Get-ExecutionPolicy
Restricted
查看所有执行策略:
PS E:> [System.Enum]::GetNames([Microsoft.PowerShell.ExecutionPolicy])
Unrestricted # 权限最高,可以不受限制执行任何脚本。
RemoteSigned # 本地脚本无限制,但是对来自网络的脚本必须经过签名
AllSigned # 所有脚本都必须经过签名才能在运行
Restricted # Powershell默认的策略,不允许任何脚本执行
Default # 为Powershell默认的策略
Bypass # 无任何限制策略,不警告、不提示
Undefined # 当前范围中没有设置执行策略
设置执行策略:
Set-ExecutionPolicy -ExecutionPolicy <PolicyName>
设置执行策略,并设置影响对象:
Set-ExecutionPolicy -ExecutionPolicy <PolicyName> -Scope <scope>
执行策略影响范围(Scope)
影响范围:Scope ,设置策略时选择影响对象。
PS C:>Get-ExecutionPolicy -List
Scope ExecutionPolicy
----- ---------------
MachinePolicy Undefined
UserPolicy Undefined
Process Undefined
CurrentUser RemoteSigned
LocalMachine AllSigned
- CurrentUser:执行策略仅影响当前用户。它存储在HKEY_CURRENT_USER注册表子项中。
- Process : 执行策略仅影响当前会话(当前的PowerShell进程)。
- LOCALMACHINE :执行策略会影响当前计算机上的所有用户。它存储在HKEY_LOCAL_MACHINE注册表子项中。
修改执行策略需要管理员权限
删除执行策略
Set-ExecutionPolicy Undefined
Set-ExecutionPolicy Undefined -Scope LocalMachine
设置会话执行策略
powershell -ExecutionPolicy Bypass ...
0x01 Nishang
Nishang is a framework and collection of scripts and payloads which enables usage of PowerShell for offensive security, penetration testing and red teaming. Nishang is useful during all phases of penetration testing.
0x02 Usage
Import all the scripts in the current PowerShell session (PowerShell v3 onwards).
如何使用:导入所有的脚本到当前的Powershell会话中,但是Powershell的版本必须是version 3。
导入命令:
PS C:\nishang> Import-Module .\nishang.psm1
单独导入:
PS C:\nishang> . C:\nishang\Gather\Get-Information.ps1
PS C:\nishang> Get-Information
获取函数的帮助信息可以这样输入:
To get help about any script or function, use:
PS C:\nishang> Get-Help [scriptname] -full
0x03 模块分类
Scripts
Nishang currently contains the following scripts and payloads.
ActiveDirectory
Modify AD objects to provide minimal permissions required for DCShadow.
Antak - the Webshell
Execute PowerShell scripts in memory, run commands, and download and upload files using this webshell.
Backdoors
A backdoor which can receive instructions from third party websites and execute PowerShell scripts in memory.
A backdoor which can receive commands and PowerShell scripts from DNS TXT queries, execute them on a target, and be remotely controlled using the queries.
A backdoor which can execute PowerShell scripts at a given time on a target.
A backdoor which can receive commands and scripts from a WLAN SSID without connecting to it.
A backdoor which can use Windows screen saver for remote command and script execution.
A backdoor which can use alternate data streams and Windows Registry to achieve persistence.
A backdoor which uses well known Debugger trick to execute payload with Sticky keys and Utilman (Windows key + U).
Modify permissions of DCOM and WMI namespaces to allow access to a non-admin user.
Modify permissions of PowerShell remoting to allow access to a non-admin user.
Bypass
Implementation of publicly known methods to bypass/avoid AMSI.
Client
Create infected CHM files which can execute PowerShell commands and scripts.
Create Word files and infect existing ones to run PowerShell commands and scripts.
Create Excel files and infect existing ones to run PowerShell commands and scripts.
Create a HTA file which can be deployed on a web server and used in phishing campaigns.
Create signed JAR files which can be used with applets for script and command execution.
Create shortcut files capable of executing PowerShell commands and scripts.
Create IQY files for phishing credentials and SMB hashes.
Create JS files capable of executing PowerShell commands and scripts.
Create SCT files capable of executing PowerShell commands and scripts.
Create a SCF file which can be used for capturing NTLM hash challenges.
Escalation
When SYSTEM privileges are required.
Introduce vulnerabilities by removing patches.
Bypass UAC.
Execution
Download and execute a PowerShell script in memory.
Download an executable in text format, convert it to an executable, and execute.
Run PowerShell commands, native commands, or SQL commands on a MSSQL Server with sufficient privileges.
Execute shellcode in memory using DNS TXT queries.
Execute PowerShell commands and scripts or a reverse PowerShell session using rundll32.exe.
Gather
Check for a virtual machine.
Copy the SAM file using Volume Shadow Copy Service.
Trick a user into giving credentials in plain text.
A pair of scripts for egress testing
Get juicy information from a target.
Get LSA Secret from a target.
Get password hashes from a target.
Get WLAN keys in plain text from a target.
Log keystrokes from a target.
Invoke-MimikatzWdigestDowngrade
Dump user passwords in plain on Windows 8.1 and Server 2012
Get password hints of Windows users from a target.
Connect back and Stream target screen using MJPEG.
Load mimikatz in memory. Updated and with some customisation.
Extract juicy information from target process (like browsers) memory using regex.
Exfiltrate information like user credentials, using WLAN SSID.
Identify admin jump-boxes and/or computers used to access Unix machines.
MITM
A local HTTPS proxy for MITM attacks.
Pivot
Check credentials on multiple computers and create PSSessions.
Run-EXEonRemote Copy and execute an executable on multiple machines.
Invoke-NetworkRelay Create network relays between computers.
Prasadhak
Check running hashes of running process against the VirusTotal database.
Scan
Brute force FTP, Active Directory, MSSQL, and Sharepoint.
A handy port scanner.
Powerpreter
All the functionality of nishang in a single script module.
Shells
Send commands and scripts to specifed Gmail account to be executed by Invoke-PsGcatAgent
Execute commands and scripts sent by Invoke-PsGcat.
An interactive PowerShell reverse connect or bind shell
Stripped down version of Invoke-PowerShellTcp. Also contains, a skeleton version which could fit in two tweets.
Invoke-PowerShellTcpOneLineBind
Bind version of Invoke-PowerShellTcpOneLine.
An interactive PowerShell reverse connect or bind shell over UDP
Stripped down version of Invoke-PowerShellUdp.
Reverse interactive PowerShell over HTTPS.
Reverse interactive PowerShell over HTTP.
Clean the system after using Invoke-PoshRatHttps
Interactive PowerShell using WMI.
An interactive PowerShell reverse shell over ICMP.
An interactive PowerShell reverse shell over HTTP using rundll32.exe.
An interactive PowerShell reverse shell over HTTP using regsvr32.exe.
Utility
Add data exfiltration capability to Gmail, Pastebin, a web server, and DNS to any script.
Add reboot persistence capability to a script.
Remote persistence added by the Add-Persistence script.
| Pipe ( | ) this to any script to exfiltrate the output. |
Transfer a file to the target.
Parse keys logged by the keylogger.
Encode and compress a script or string.
Decode and decompress a script or string from Invoke-Encode.
Run a web server which logs Basic authentication and SMB hashes.
Encode a string to ROT13 or decode a ROT13 string.
Generate DNS TXT records which could be used with other scripts.
[Base64ToString]
[StringToBase64]
[ExetoText]
[TexttoExe]
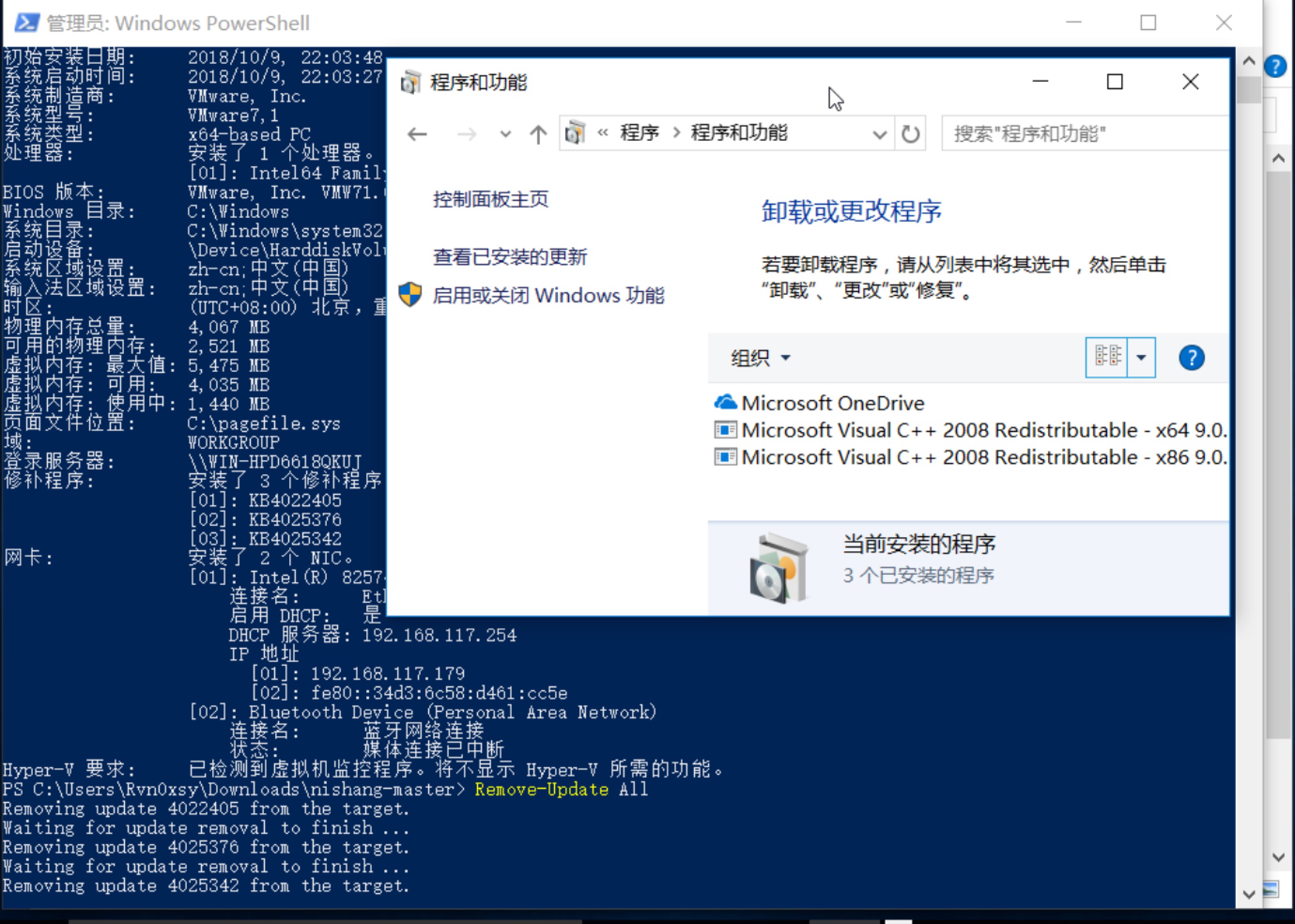
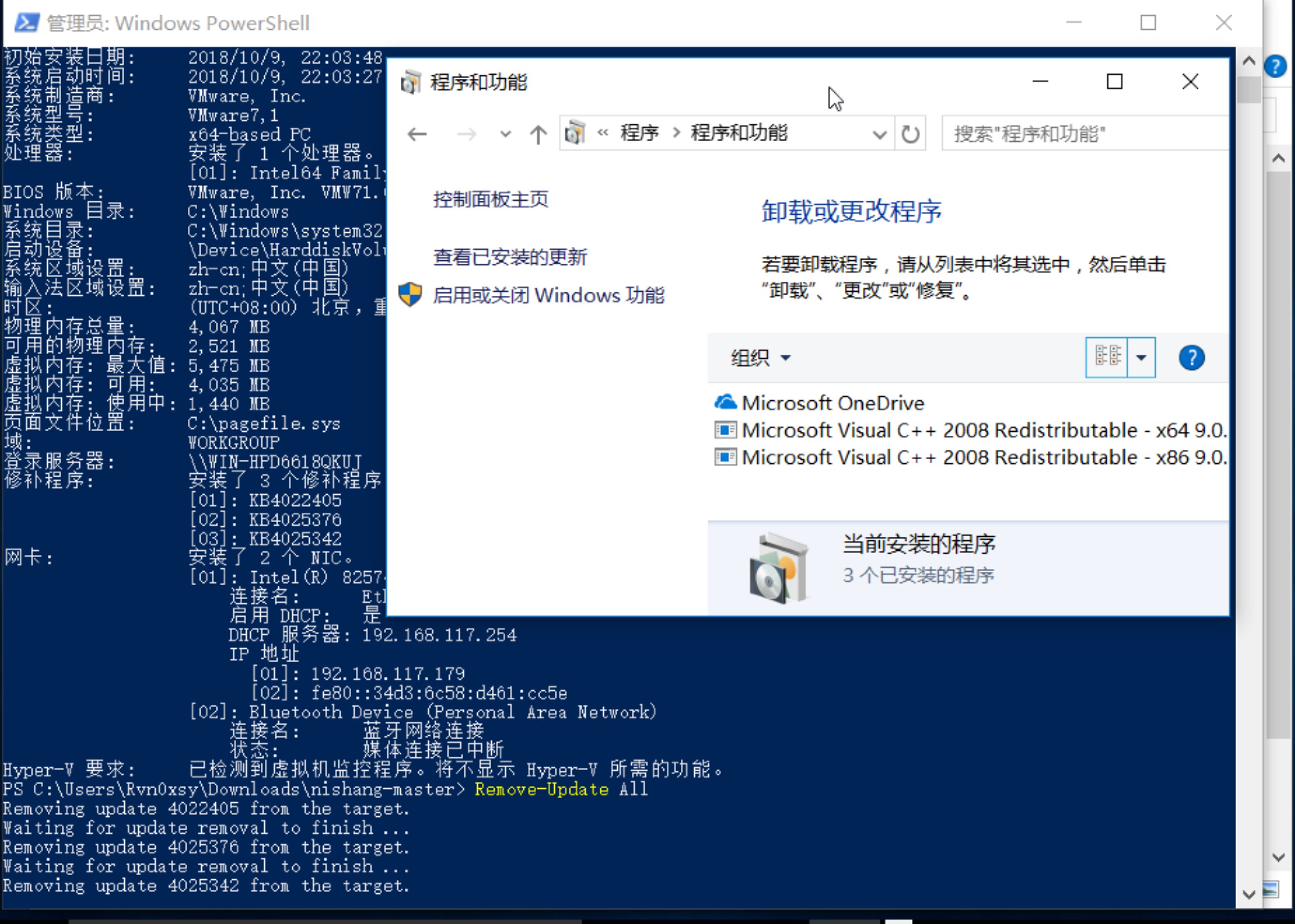
0x04 卸载系统补丁
PS C:\Users\Rvn0xsy\Downloads\nishang-master> systeminfo
主机名: DESKTOP-7KT7GL1
OS 名称: Microsoft Windows 10 企业版
OS 版本: 10.0.15063 暂缺 Build 15063
OS 制造商: Microsoft Corporation
OS 配置: 独立工作站
OS 构件类型: Multiprocessor Free
注册的所有人: Windows 用户
注册的组织:
产品 ID: 00329-00000-00003-AA343
初始安装日期: 2018/10/9, 22:03:48
系统启动时间: 2018/10/9, 22:03:27
系统制造商: VMware, Inc.
系统型号: VMware7,1
系统类型: x64-based PC
处理器: 安装了 1 个处理器。
[01]: Intel64 Family 6 Model 158 Stepping 10 GenuineIntel ~259
BIOS 版本: VMware, Inc. VMW71.00V.6997262.B64.1710270607, 2017/10/27
Windows 目录: C:\Windows
系统目录: C:\Windows\system32
启动设备: \Device\HarddiskVolume1
系统区域设置: zh-cn;中文(中国)
输入法区域设置: zh-cn;中文(中国)
时区: (UTC+08:00) 北京,重庆,香港特别行政区,乌鲁木齐
物理内存总量: 4,067 MB
可用的物理内存: 2,521 MB
虚拟内存: 最大值: 5,475 MB
虚拟内存: 可用: 4,035 MB
虚拟内存: 使用中: 1,440 MB
页面文件位置: C:\pagefile.sys
域: WORKGROUP
登录服务器: \\WIN-HPD6618QKUJ
修补程序: 安装了 3 个修补程序。
[01]: KB4022405
[02]: KB4025376
[03]: KB4025342
网卡: 安装了 2 个 NIC。
[01]: Intel(R) 82574L Gigabit Network Connection
连接名: Ethernet0
启用 DHCP: 是
DHCP 服务器: 192.168.117.254
IP 地址
[01]: 192.168.117.179
[02]: fe80::34d3:6c58:d461:cc5e
[02]: Bluetooth Device (Personal Area Network)
连接名: 蓝牙网络连接
状态: 媒体连接已中断
Hyper-V 要求: 已检测到虚拟机监控程序。将不显示 Hyper-V 所需的功能。
PS C:\Users\Rvn0xsy\Downloads\nishang-master> Remove-Update All
Removing update 4022405 from the target.
Waiting for update removal to finish ...
Removing update 4025376 from the target.
Waiting for update removal to finish ...
Removing update 4025342 from the target.
Waiting for update removal to finish ...
0x05 others
可以参考:https://github.com/samratashok/nishang/blob/master/README.md