In a new campaign detected in March 2025, senior members of the World Uyghur Congress (WUC) living in exile have been targeted by a Windows-based malware that's capable of conducting surveillance.
The spear-phishing campaign involved the use of a trojanized version of a legitimate open-source word processing and spell check tool called UyghurEdit++ developed to support the use of the Uyghur language.
"Although the malware itself was not particularly advanced, the delivery of the malware was extremely well customized to reach the target population and technical artifacts show that activity related to this campaign began in at least May of 2024," the Citizen Lab said in a Monday report.
The investigation, according to the digital rights research laboratory based at the University of Toronto, was prompted after the targets received notifications from Google warning that their accounts had been at the receiving end of government-backed attacks. Some of these alerts were sent on March 5, 2025.
The email messages impersonated a trusted contact at a partner organization and contained Google Drive links, which, when clicked, would download a password-protected RAR archive.
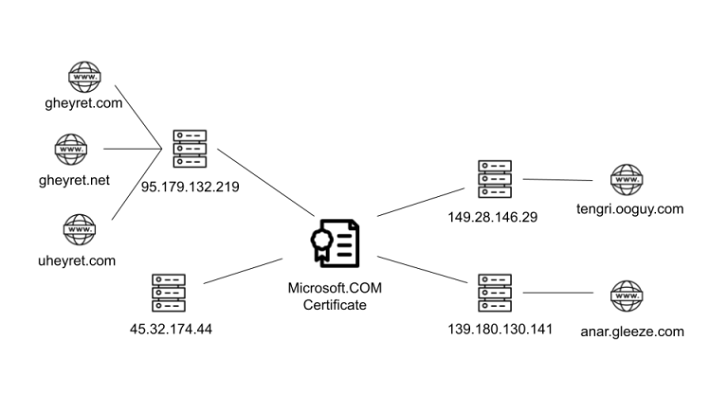
Present within the archive was a poisoned version of UyghurEdit++ that profiled the compromised Windows system and sent the information to an external server ("tengri.ooguy[.]com"). The C++ spyware also comes with capabilities to download additional malicious plugins and run commands against those components.
The findings are the latest in a series of highly-targeted attacks aimed at the Uyghur diaspora with the goal of conducting digital transnational repression.
It's not exactly known who was behind the attacks, although the threat actors' techniques, their "deep understanding of the target community," and targeting suggest they align with the Chinese government.
"China's extensive campaign of transnational repression targets Uyghurs both on the basis of their ethnic identity and activities," the Citizen Labs said.
"The goal of the surveillance of Uyghurs in the diaspora is to control their ties to the homeland and the cross-border flow of information on the human rights situation in the region, as well as any influence on global public opinion about the Chinese state's policies in Xinjiang."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.