![]()
Commvault today added an ability to automatically recover the instances of Microsoft Active Directory (AD) that have become primary targets of cybersecurity attacks.
Company CTO Brian Brockway said Commvault Cloud Backup & Recovery for Active Directory Enterprise Edition automates the recovery of an Active Directory forest, which is the logical container in an Active Directory configuration that aggregates domains, users, computers and group policies.
If Microsoft AD is unavailable, many organizations are not going to be able to recover applications that depend on it to authenticate access, he added.
There are hundreds of millions of instances of Active Directory running in organizations and it can take days to manually recover one. In many instances, there is little to no documentation available that shows how these platforms were initially configured, noted Brockway.
Cybercriminals often make sure that Active Directory has been taken offline to ensure that organizations are unable to regain access to applications in the wake of a ransomware attack. The longer it takes for an organization to recover access to those applications the more likely it becomes they will comply with ransomware demands.
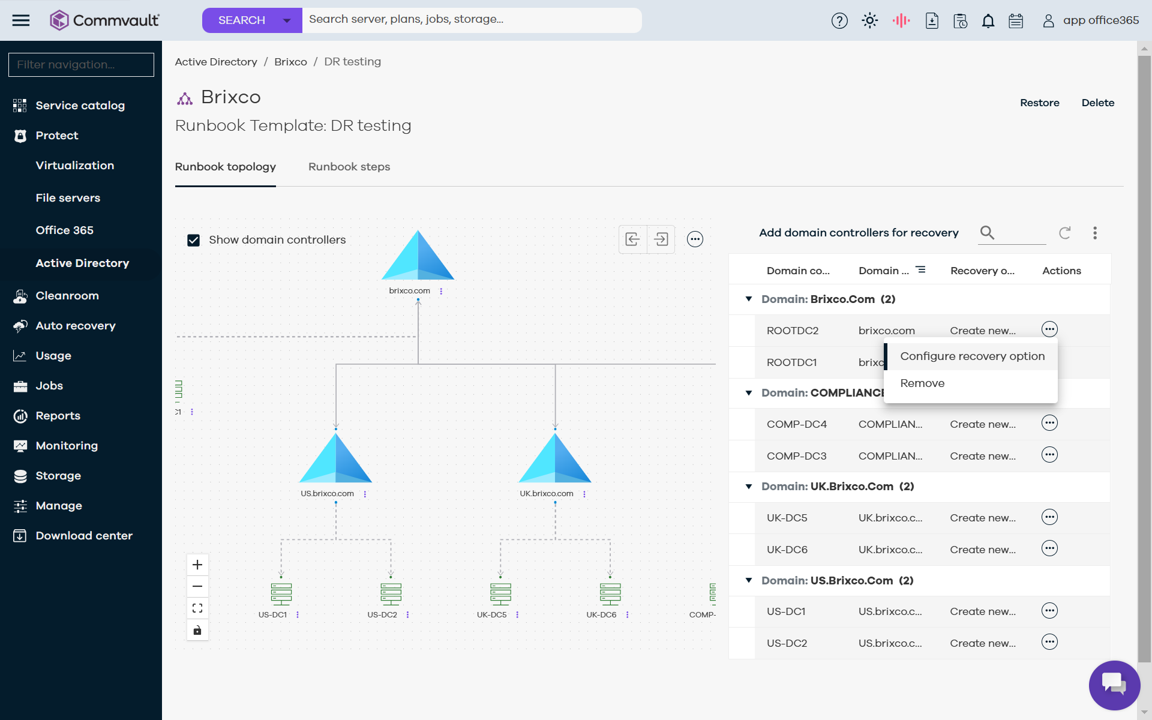
Commvault addresses that issue by initially backing up instances of Active Directory and then taking snapshots as forests are updated. IT teams can then use the Commvault platform to run automated runbooks to recover forests, including being able to transfer users to a different domain controller.
IT teams are also provided with visualization tools that make it easier to identify which domain controllers should be restored first given all the dependencies that might exist between forests.
As data protection continues to evolve it’s becoming increasingly feasible to backup and restore complex instances of software such as Active Directory, said Brockway. The overall goal is to reduce recovery times to the point where cyberattacks become much less disruptive than they are today, he added.
Active Directory is simultaneously one of the oldest and most complex platforms to be found in enterprise IT environments. The number of attack vectors that have been created span everything from simple password spraying to Kerberoasting, which exploits the ServicePrincipalName attribute on user objects to redirect authentications. It ranks among one of the most challenging IT platforms to secure so cybersecurity teams should assume that at some point they will need to work with internal IT teams to recover one or more instances of Active Directory.
Ideally, most organizations will remember to test their backup and recovery runbooks long before there is a cybersecurity incident. The moment to determine whether a runbook will reliably recover an instance of Active Director is not immediately after a cyberattack has commenced. It may not be possible to stop these attacks but the speed at which organizations can recover critical IT infrastructure makes all the difference. The issue, as always, is planning for all the possible scenarios that might involve a platform such as Active Directory that is critical for an organization to function.
Recent Articles By Author