
BforeAI researchers analyzed approximately 6000 retail industry domains registered in t 2024-11-14 19:31:45 Author: bfore.ai(查看原文) 阅读量:12 收藏
BforeAI researchers analyzed approximately 6000 retail industry domains registered in the last 90 days to uncover significant trends in the threat landscape. The retail industry transformed drastically during and after the Covid-19 pandemic, when most retailers more fully adopted an online presence. Naturally, this rise in ecommerce provided cybercriminals increased opportunities for attack, as compared to pre-pandemic situations.
Around the holiday season, an annual surge in DNS abuse is observed, mostly through the promotion of spoofed and shoddily-created websites. Furthermore, fake phishing applications under the name of popular ecommerce retailers, and distributed via unauthorized app distribution platforms.
Of the over 6000 retail domains registered, 4036 domains leveraged prominent retail keywords and brand names, including Walmart, IKEA, Amazon, Flipkart, Lululemon, and 7-Eleven. Scammers attempted to mimic the exact website name by appending the brand name with terms such as “shop,” “sale,” “deal,” or incorporating numerical sequences (e.g., ebay-088, flipkart01) to emphasize on shopping occasions.
There is a notable use of .com, .shop, .vip, and .xyz domains. These top level domains (TLDs) are inexpensive and commonly used in scams. Additionally, a generic association with “shop” makes it easier to believe that victims are accessing a legitimate website.
Some of the domains date back several years (e.g., walmartgiftcard0[.]godaddysites[.]com, 2013), highlighting the longevity of the scams and introducing a new subdomain for a new campaign, while generic root domains remain a common method of evading detection. However, many of these domains were registered in October 2024, suggesting a recent surge in scam activity likely aligned with upcoming shopping seasons or promotional events.
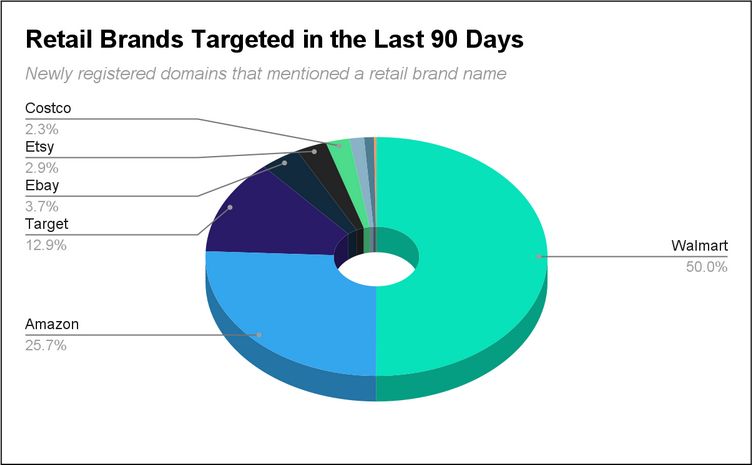
In fact, in 60% of the domains analyzed in this report (3687 domains), retail brand names were mentioned in a domain name that was newly registered and active. These are strong indicators that a domain can be considered “suspicious”. Here is a list of top brand names that were analyzed and how many domains were created in this fashion:
- Walmart 1844
- Amazon 947
- Target 474
- Ebay 138
- Etsy 107
- Costco 83
- Ikea 51
- Home Depot 34
- Tesco 9
Various string manipulation techniques, as well as popular typosquatting methods, were observed during the research, in which notable mentions were lengthy names (e.g., ajjaab-shoppiinng1xsaalleess[.]today). These often included the addition of numbers, non-standard characters, and manipulated spellings.
Technical Threat Analysis:
Fake Apps spreading Malware and harvesting credentials
Out of the confirmed 185 active malicious websites identified in this report, some of the spoofed instances were found to be promoting applications that were downloading apps suspicious in nature. In a phishing campaign, especially in holiday themed emails, ads, and downloads, cybercriminals aim to infect users’ devices with malware.
The retail industry endures a consistent trend in which fraudsters often create fake shopping or discount apps that mimic legitimate platforms. These apps are designed to steal login credentials or credit card information, compromising users’ financial data and access to other accounts.
Mobile malware are often known to persist stealthily in the system, sharing a batch of sensitive information with the attacker, or by implanting itself as ransomware in the device.
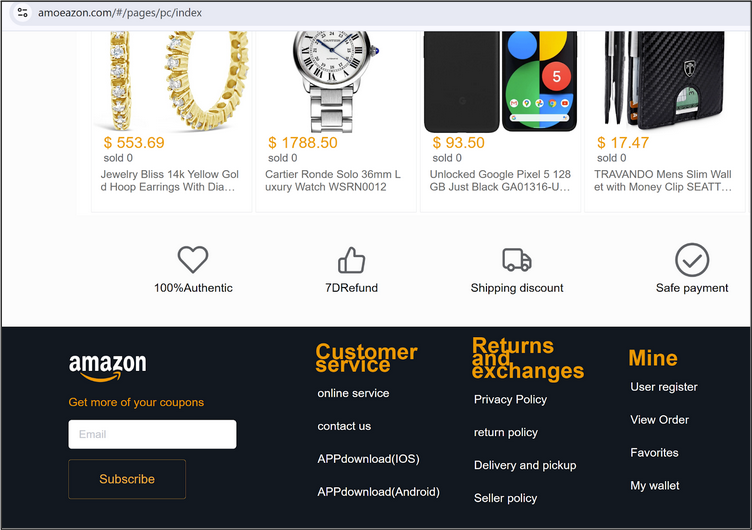
Figure 1: External links provided by phished Amazon website in which apps for IOS and Android were provided.
This obvious phishing website (see Figure 1) is targeting Amazon by offering iOS and Android applications distributed through unofficial third-party channels.
Likewise, the Flipkart phishing attempt (see Figure 2) clearly mentions external links to download the application Flipkart Pulse, which is a diagnostic app to evaluate the hardware and software conditions of used mobile phones.
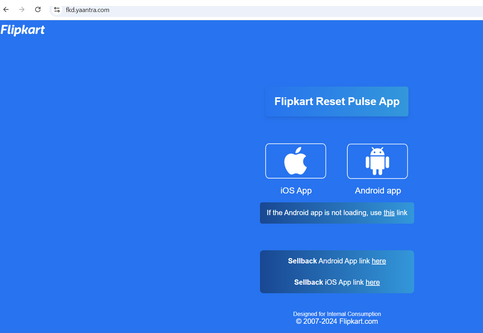
Figure 2: Multiple links diverting users to illegitimate app distribution platforms.
Poorly Constructed Websites
Fraudulent and poorly-built websites often surface during the holiday season, mostly due to the utilization of open-source code repositories and hastily-generated bulk templates of popular retail sites. These sites resemble the originals but are filled with noticeable flaws in appearance and security. Despite these flaws, shoppers tend to overlook these mistakes and engage due to attractive offers, such as time-sensitive deals, gift card promotions, and other perceived bargains..
One tactic that works well for cybercriminals during the holiday season is fake free gift card offers (prominently observed in Walmart scams, like in Figure 3). These offers require users to submit personally identifiable information (PII) before being able to claim the reward.

Figure 3: Gift card scams try to harvest sensitive user information in exchange for lucrative offers.
Other gift card scams may involve counterfeit gift cards, gift card generators, or phishing schemes requesting gift card codes, all aimed at stealing the card’s value before the recipient can use it.
Biggest Sale of the Year Banners and Seasonal Sale Themes
With the holiday season around the corner, phished websites often showcase banners advertising “biggest sale of the year” deals. These include unique keywords used by specific retailers, such as, the “Big Billion Days” associated with Flipkart sale promotions (see Figure 4). Approximately 1510 domains were observed to be registered in October with similar content and page titles.
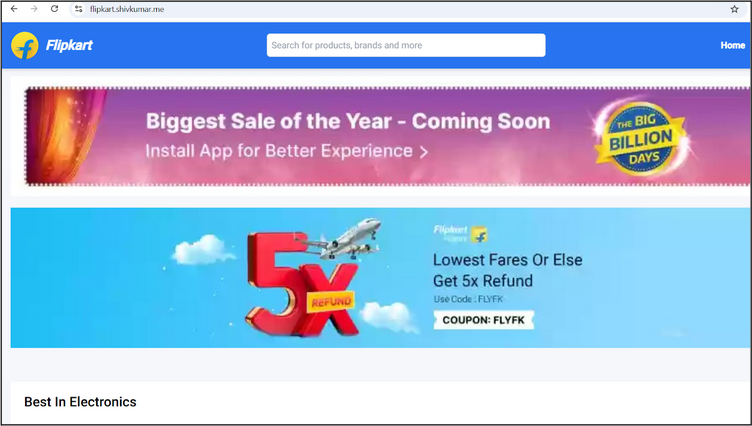
Figure 4: Unique keywords associated with retailers used in phishing websites help garner shopper’s trust.
Additionally, cybercriminals are exploiting seasonal trends, such as winter sales where popular brands are targeted (see Figure 5).
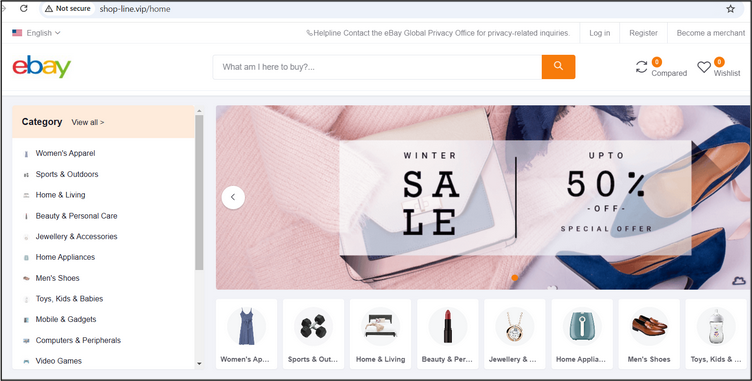
Figure 5: Seasonal phishing campaigns that typically offer sales to attract buyers.
Fraudulent Websites Featuring Chatbot Support
Our researchers also discovered how chatbots and support bots are being leveraged on phishing websites. The bots enhance the authenticity and facilitate harvesting of personal details and/or financial information of shoppers. These bots may offer fake links under the guise of “support,” which ultimately leads to additional phishing attempts (see Figure 6).
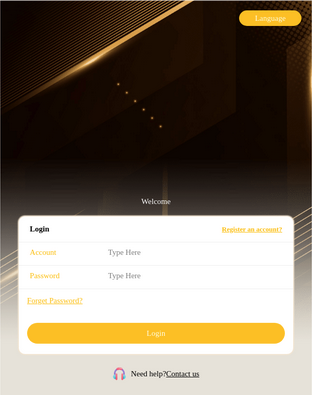
Figure 6: Malicious chatbot support to mimic a legitimate website’s functionality.
Merchant Login Compromises
Along with shoppers and employees, retail merchants are also at a risk. Websites that mimic merchant login panels (see Figure 7) are deployed to compromise merchant accounts. Once they have achieved an account takeover, the criminals can alter product listings, initiate unauthorized transactions, or harvest customer information, leading to significant financial and reputational damage for the business.
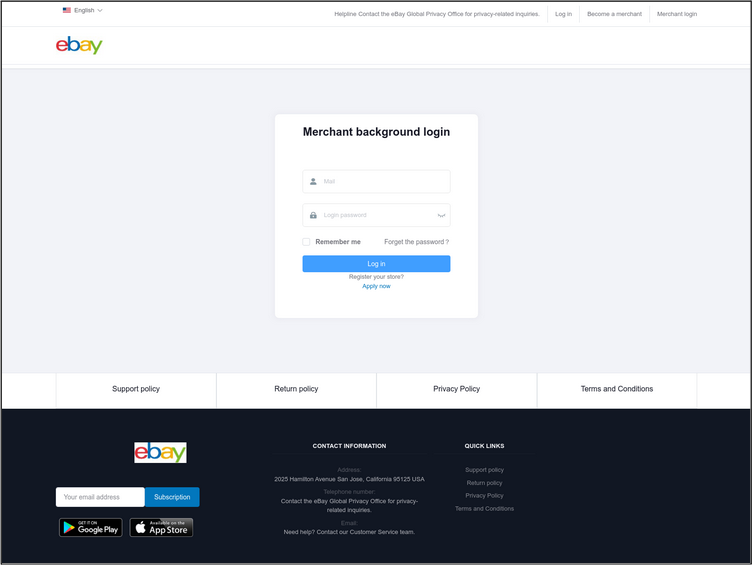
Figure 7: Fake login panels created for merchant login.
Cryptocurrency Investment Pitches on Retail Sites
This trend is comparatively new, appearing around the time the retail industry adopted cryptocurrency transactions for payments. Adhering to this growing interest in the crypto-retail sector, cybercriminals use retail websites to allow users to connect their wallet to their shopping accounts, capturing their passwords in the process, while the money is being transacted to false accounts (see Figure 8). Such sites encourage purchases through cryptocurrency, as transactions are difficult to trace and nearly impossible to reverse, leaving victims with significant, irreplaceable losses.

Figure 8: Phishing websites promoting users to connect their wallets to harvest credentials
Investment Scams
Around 50 domains originated as investment scams, aimed at causing financial loss to victims. Initially the potential victims are lured with offers like getting a job or investment via social media and job search portals (see Figure 9).
Victims are contacted through Whatsapp or Telegram and asked to complete tasks in order to earn money. They may also be asked to invest their own money into schemes shown on these investment scam websites. This is generally followed by the victim being added to group chats where other members post profits they have made from the investments. This provides the victims with assurance and social proof that these schemes “work” and are not a scam. Once the victim has “invested” a considerable amount of money, their accounts are frozen and they are restricted from withdrawing their money.
While the specifics of each scam may vary, the modus operandi has remained relatively consistent.

Figure 9: Investment scam leverages the Walmart brand by claiming to originate from review and hiring websites.
Other notable observations:
Cybercriminals have formed various channels on different social media platforms like YouTube, Facebook Marketplace and Telegram, where regular deals and offers are posted. Different keywords used are, deals, telegram, groups, offer, shop, tickets, supply, deals, market, bank, reseller, etc., are used to attract victims to such groups.
A common technique is targeted phishing in which cybercriminals are particular about the geography and target audience. This method offers conditional loading of a malicious domain only when certain criteria are met. One example of how this works is when the success of a phishing attempt requires the victim to use a specific operating system (OS). The malicious actor will do an OS detection check before launching an attack.. In other cases, the intended phishing domain would simply not load because it fails on the detection parameters set by the cybercriminals.
Free hosting platforms such as Vercel and Cloudflare, continue to be actively exploited to minimize investment and maximize the impact of temporary campaigns.
Impact
The inclusion of AI and emerging technologies such as chatbots and cryptocurrencies continues to be exploited by cybercriminals, as these options didn’t previously coincide with retailers. Overall, there are now different angles from which customers, employees, and merchants associated with any major retailer could be at risk of phishing, especially to collect credentials and financial data. AI-powered phishing helps to set up adversarial infrastructure and mimic trustworthy elements like social media presence to boost the fake website’s credibility.
Mitigation
The retail industry serves a vast, diverse range of customers with varying levels of technical knowledge, and therefore needs to prioritize cybersecurity measures to protect these customers and themselves against brand-based attacks. It is essential for retailers to utilize solutions that have the ability to monitor, predict, disrupt and take down adversarial infrastructure attacks preemptively, even before they launch.
Additionally, customer awareness, such as monthly cybersecurity and scam awareness newsletters, is more important than ever. With the latest threats vectors targeting shoppers, sharing steps to mitigate them can help with customer retention and to foster trust.
It is recommended to:
- Shop on Verified Sites: Stick to trusted, reputable retailers or verify the website’s legitimacy before making purchases.
- Beware of Deals Too Good to Be True: Extremely low prices on popular items are often red flags.
- Use Secure Payment Methods: Choose secure payment options, like credit cards, which offer better fraud protection.
- Check for Secure Connections: Ensure the site has “https” in the URL and a padlock icon before entering payment information.
- Be Cautious with Unsolicited Emails and Ads: Avoid clicking on ads or links in emails that seem suspicious, especially those promising deep discounts.
如有侵权请联系:admin#unsafe.sh