
The Good | Interpol-Led Operation Cracks Down on West African Cybercrime SyndicatesThe axe has fal 2024-7-19 21:0:32 Author: www.sentinelone.com(查看原文) 阅读量:33 收藏
The Good | Interpol-Led Operation Cracks Down on West African Cybercrime Syndicates
The axe has fallen hard on West African crime syndicates as part of Operation Jackal III, a months-long law enforcement effort run across 21 countries. This week, Interpol reported some 300 arrests, the identification of over 400 suspects, 720 blocked bank accounts, and the seizure of $3 million in illicit funds, all to dismantle multiple criminal networks globally.
Amongst the affected crime syndicates, Black Axe has been a prominent plague within Africa and across the world. Their operations span human trafficking, drug smuggling, violent crimes, and significant cases of cyber fraud where victims were forced to sell their homes as a result of the scams. Believed to have been in operation for decades, Black Axe is closely linked to business email compromise (BEC) schemes, ‘romance’ fraud, and other identity scams.

In Argentina, authorities cracked down on a Nigerian-based transnational criminal infrastructure using millions in ‘supernotes’, counterfeit banknotes of very high quality, to open bank accounts in various countries in South America. Portuguese authorities similarly dismantled another Nigerian group that was laundering funds from online scam victims all across Europe. The data found on the seized devices revealed a mass network of cryptocurrency transactions indicative of a sophisticated money laundering operation.
The financial fraud industry is a dangerous and extensive one in West Africa, highlighting the success of the operation in reducing the ability for organized crime leaders to develop and extend their reach. Cross-border collaboration continues to be instrumental in combating deep-rooted criminal networks. Interpol currently has 196 member countries and works with national police forces to exchange intelligence and provide real-time access to databases leading to more efficient arrests.
The Bad | Flaws in SAP AI Core Expose Sensitive Customer Data & Allow Service Takeovers
Cybersecurity researchers this week reported on five critical security flaws in SAP AI Core, a cloud-based platform for creating and deploying AI workflows, which could be exploited to access tokens and customer data. The flaws, dubbed “SAPwned”, could allow attackers to infiltrate customers’ data and contaminate internal artifacts, potentially spreading to other services and environments.
Before being addressed by SAP, the flaws enabled unauthorized access to private artifacts and cloud credentials, including those for AWS, Microsoft Azure, and SAP HANA Cloud. They allowed modifications to Docker images on SAP’s internal and Google Container registries, making it possible to facilitate supply chain attacks on SAP AI Core services.
Attackers could also gain cluster administrator privileges on SAP AI Core’s Kubernetes cluster, leading to theft of sensitive data such as AI models, datasets, and code, and manipulating AI data and models’ inference. The issues stem from inadequate isolation and sandboxing mechanisms, allowing malicious AI models and training procedures to run in shared environments.
Since AI infrastructures require access to vast amounts of customer data, this makes AI service providers lucrative targets for attack. As AI training continues to rise in popularity amongst organizations, so has their susceptibility to tenant isolation vulnerabilities – an equivalent to executing arbitrary code.
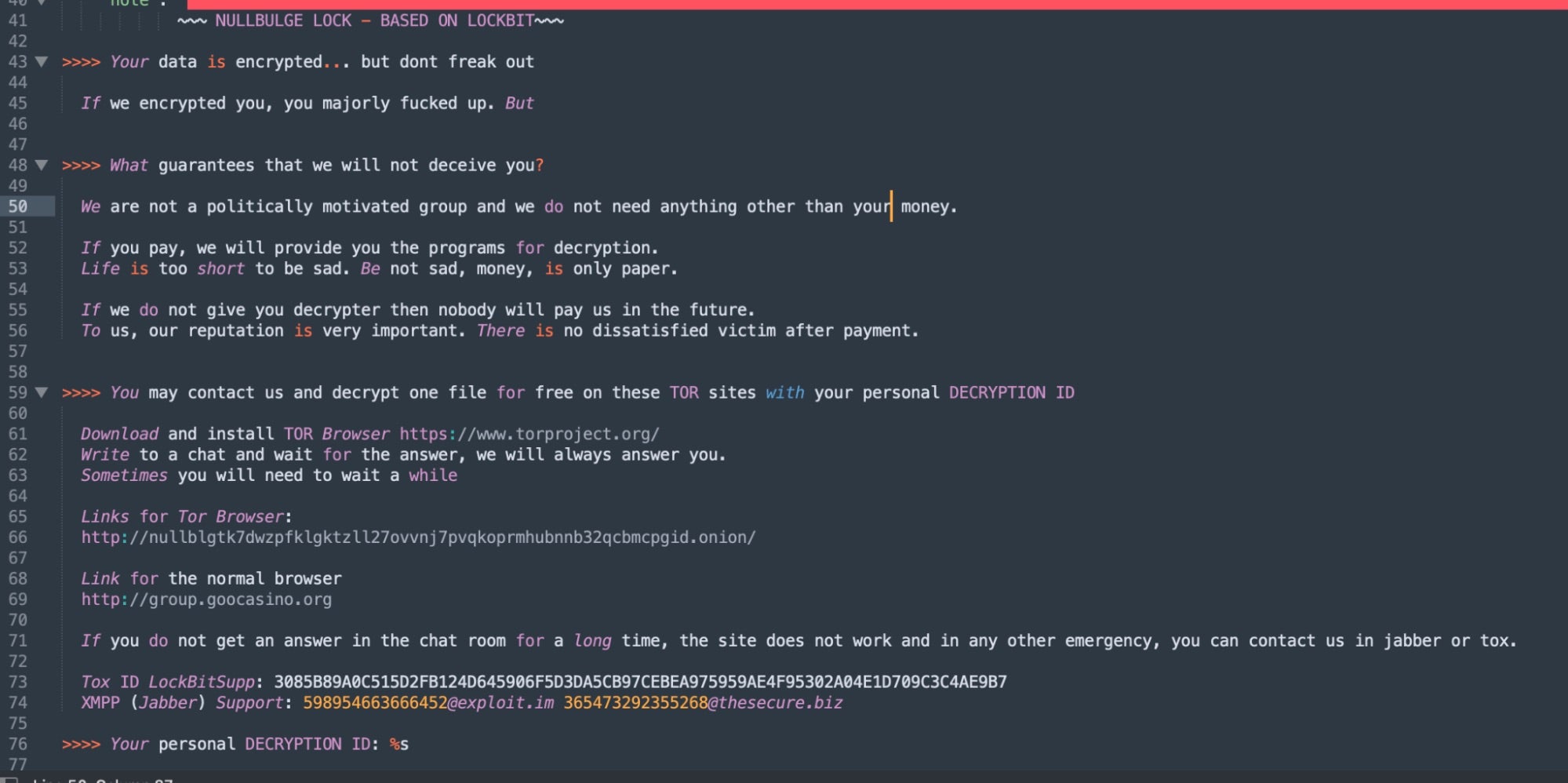
These findings follow the emergence of a new cybercriminal threat group, NullBulge, which targets AI- and gaming-focused entities through software supply chain attacks. The rise in generative AI use has prompted companies to implement data loss prevention tools and other measures to mitigate risks. Groups like NullBulge illustrate the ongoing threat of low-barrier ransomware and infostealer infections now done through attacking unsecured AI workflows.
The Ugly | FIN7 Sells Latest Version of EDR-Tampering Tool to Ransomware Operators on Dark Markets
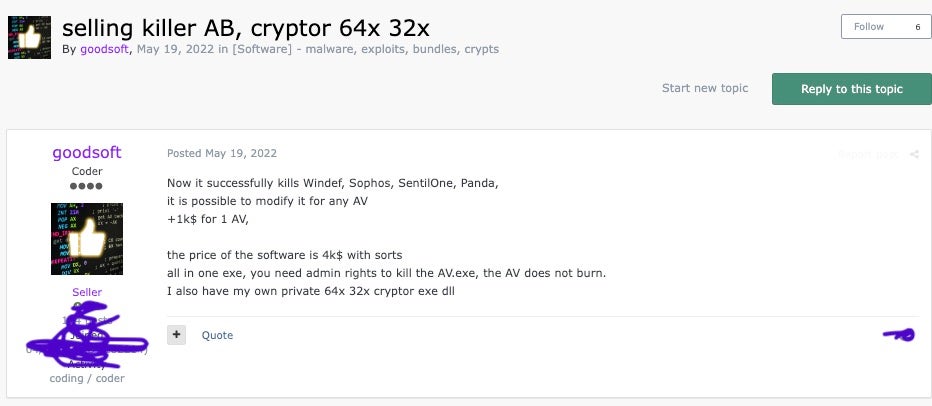
Elusive and persistent Russia-linked threat group, FIN7, is now using multiple pseudonyms to mask its identity and develop their criminal operations across dark markets. In tandem, SentinelLabs has discovered a new version of a highly specialized and popular tool called AvNeutralizer (aka AuKill) being marketed in the criminal underground. This tool, initially developed by FIN7 to tamper with security solutions, is now capable of leveraging the Windows built-in driver ProcLaunchMon.sys (TTD Monitor Driver) to disable endpoint solutions.
FIN7 has been active since 2013, initially tied to financial fraud before expanding into ransomware, linking up with DarkSide, BlackMatter, and likely, BlackCat. The financially motivated outfit is also known for their sophisticated phishing and social engineering attacks, most notably through their fake security company ‘Bastion Secure’, which hired unwitting developers and pentesters for later attacks campaigns.
SentinelLabs reports that AuKill was first used in BlackBasta ransomware attacks back in 2022. Since then, the tool has been used by several other ransomware operations, indicating widespread distribution. The latest version of the tool now utilizes the Windows ProcLaunchMon.sys driver to hang processes, ultimately leading to a denial of service condition. Other than AuKill, the researchers identified additional custom tooling specific, currently, only to FIN7. Their arsenal includes Powertrash (a PowerShell backdoor), Diceloader (a lightweight backdoor), Core Impact (a commercial penetration testing toolkit), and an SSH-based backdoor.
SentinelLabs warns that FIN7’s continuous innovation in evading security measures and selling their tools poses a significant threat to enterprises globally. The group’s advanced techniques and collaboration with other cybercriminals complicate attribution, demonstrating their sophisticated operational strategies.
如有侵权请联系:admin#unsafe.sh