IntroductionMalware for mobile devices is something we come across very often. In 202 2024-3-20 19:0:34 Author: securelist.com(查看原文) 阅读量:28 收藏
Introduction
Malware for mobile devices is something we come across very often. In 2023, our technologies blocked 33.8 million malware, adware, and riskware attacks on mobile devices. One of 2023’s most resonant attacks was Operation Triangulation, targeting iOS, but that was rather a unique case. Among the mobile platforms, Android remains the most popular target operating system for cybercriminals. Last month, we wrote a total of four private crimeware reports on Android malware, three of which are summarized below.
To learn more about our crimeware reporting service, you can contact us at [email protected].
Tambir
Tambir is an Android backdoor that targets users in Turkey. It disguises itself as an IPTV app, but does not manifest any such functionality. Instead, it is a full-fledged spyware application that collects SMS messages, keystrokes, etc.
Upon starting, the application shows a screen that asks the user in Turkish to enable the accessibility service. Once it is granted all the permissions, the app obtains a C2 address from a public source, such as Telegram, ICQ or Twitter/X. Next, the application shapeshifts by changing its icon to that of YouTube.
Tambir supports more then 30 commands that it can retrieve from the C2. These include starting and stopping the keylogger, running an application specified by the attacker, sending SMS messages, dialing a number and so on.
We found certain similarities between Tambir and the GodFather malware. They both target users in Turkey and both support Telegram for retrieving a C2 server address. However, Tambir has a much richer feature set.
Dwphon
In November 2023, we stumbled upon an Android malware variant targeting mobile phones by various Chinese OEM manufacturers. Their products were primarily intended for the Russian market. The same malware earlier had been found in the firmware of a kids’ smart watch by an Israeli manufacturer distributed mainly in Europe and the Middle East.
Dwphon comes as a component of the system update application and exhibits many characteristics of pre-installed Android malware. For example, it collects device and personal information, as well as information about third-party applications installed on the device. The exact infection path is unclear, but there is an assumption that the infected application was incorporated into the firmware as a result of a possible supply chain attack.
The malware itself consists of a number of modules that provide a range of functions:
- Main module. Collects system information (e.g. IMSI, system language, etc.) and sends it to the C2. Commands that can be received are related to installing, downloading and deleting apps on the device, downloading files, and showing popups, among others.
- DsSdk module. Another module that collects device information. The module has its own C2 and is unable to receive commands.
- ExtEnabler module. This module starts and monitors other applications. Part of the module’s functionality is sending a broadcast message when an application is started. Some of the samples we investigated did not contain any receiver code. We did, however, find one sample that contained it. This sample includes the Triada Trojan, which suggests a link between Dwphon and Triada, although there is insufficient evidence to support this.
Gigabud
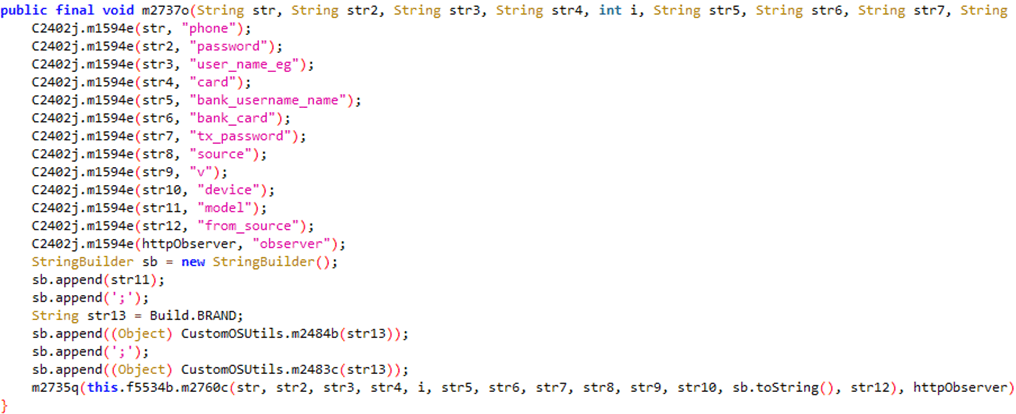
Gigabud is an Android RAT (Remote Access Trojan), active since at least mid-2022 and first discovered in January 2023. Focused on stealing banking credentials from individuals in Southeast Asia, it initially mimicked a local airline app, but later crossed borders into other countries, such as Peru, and also changed functionality to fake loan malware.
Gigabud is written in Kotlin, and obfuscated with Dexguard and later Virbox. Its various versions mimic apps created by companies in Thailand and Peru among others. Upon starting, the application shows the login screen of the app it mimics and subsequently sends the credentials, along with device information, to the C2. Next, it shows a virtual assistant, which guides the victim to apply for a loan.
It then continues by requesting the accessibility feature to be enabled – if it isn’t already. It needs this to steal credentials and mimic touch events for bypassing 2FA.
Apart from stealing credentials, Gigabud embeds a screen recording module. The main functionality is stealing credentials from the infected device. It does this by streaming the screen to the C2 over WebSocket or RTMP.
Gigabud contains various Chinese language artifacts. For example, the log messages are written in Chinese, the APK signature is in Chinese, and the C2 servers are located in China.
Conclusion
In 2023, we detected more than 1.3 million unique malicious installation packages targeting the Android platform and distributed in various ways. Users can protect themselves by not downloading apps from unofficial app marketplaces and by carefully reviewing the permissions that apps request. Frequently, apps do not embed any exploitation functionality and thus solely rely on the user giving them permissions. Additionally, antimalware tools help to keep your Android device clean.
If you would like to stay up to date on the latest TTPs being used by criminals, or if you have questions about our private reports, you can contact us at [email protected].
Indicators of compromise
Gigabud
043020302ea8d134afbd5bd37c05d2a8
0960de9d425b5157720f59c2901d4e3b
0677a090eb28837b1bbf3e6ab1822fdd
Dwphon
042f041108a79ac07d7b3165531faa9a
1796e678498bf9a067c43769f4096488
274b8d86042d94a6ca6823841fec6d2c
Tambir
04807757a54ce0fbc8326ea8b11f8169
06148a2e5828e6844c2a1a74030d22b6
098dac0668497d9707045bc1e10ced93
如有侵权请联系:admin#unsafe.sh



