
2024-1-19 22:0:0 Author: www.tenable.com(查看原文) 阅读量:11 收藏
Find out why Uncle Sam is warning critical infrastructure facilities about drones made in China, while urging water treatment plants to beef up incident response plans. Plus, the challenges stressing out CISOs are also opening new doors for them. In addition, the latest on the Androxgh0st malware. And much more!
Dive into six things that are top of mind for the week ending January 19.
1 - Critical infrastructure orgs warned about using Chinese drones
Here’s a warning from the U.S. government to critical infrastructure organizations: If the drones you’re using were made in China, be careful.
Why? These drones represent a “significant risk” because the data they collect could end up in the hands of the Chinese government, the U.S. Cybersecurity and Infrastructure Security (CISA) agency and the Federal Bureau of Investigation (FBI) said this week.
At issue are laws enacted by the People’s Republic of China (PRC) that give the government “expanded legal grounds” to access and control data held by firms in China, according to CISA and the FBI.

As a result, using unmanned aircraft systems UAS), more commonly known as drones, “requires careful consideration and potential mitigation to reduce risk to networks and sensitive information,” reads the joint advisory “Cybersecurity Guidance: Chinese-Manufactured UAS.”
“Without mitigations in place, the widespread deployment of Chinese-manufactured UAS in our nation’s key sectors is a national security concern, and it carries the risk of unauthorized access to systems and data,” Bryan A. Vorndran, Assistant Director of the FBI’s Cyber Division, said in a statement.
To mitigate this risk, the agencies recommendations include:
- Using drones built with secure-by-design principles, such as those manufactured in the U.S.
- Understanding where drones were manufactured and which laws the manufacturer must abide by
- Reviewing drones’ privacy policies, and in particular policies for data storage and sharing
- Subjecting drones to the same level of protection, monitoring and maintenance, including vulnerability management, as other IT and communications devices
- Adopting a zero trust framework for the drone fleet, as well as strong data-at-rest and data-in-transit procedures for encryption and storage
To get more details, check out:
- The announcement “Cybersecurity Guidance on Chinese-Manufactured UAS for Critical Infrastructure Owners and Operators”
- The joint advisory “Cybersecurity Guidance: Chinese-Manufactured UAS”
2 - The state of the CISO? A mix of anxiety and empowerment
What’s the current mindset of the average CISO? Apparently it’s a contrasting combination of stress over mounting challenges and enthusiasm over new opportunities.
That’s according to the “State of the CISO, 2023–2024 Benchmark Report” from IANS Research and Artico Search, which was announced this week and is based on a survey of 660 CISOs and on unstructured interviews with 100 CISOs.
For example, CISOs worry about tightening budgets, increasingly sophisticated cyberattacks, mounting cyber regulations, chilling personal liability risk, and the threat from malicious AI use.
But these and other challenges also raise CISOs’ profiles in their organizations, opening the door for them to play a larger role.
“Navigating an exceptionally complex landscape, CISOs are having to do more with less and risk personal legal exposure,” reads a blog post about the report.
“The upside? Increased pressure on organizations gives CISOs more leeway to influence business leadership along with an unprecedented opportunity to argue for a place in the executive ranks,” the blog adds.
Here are key findings from the report:
- Only half of CISOs engage with their board of directors at least quarterly, the frequency most CISOs desire.
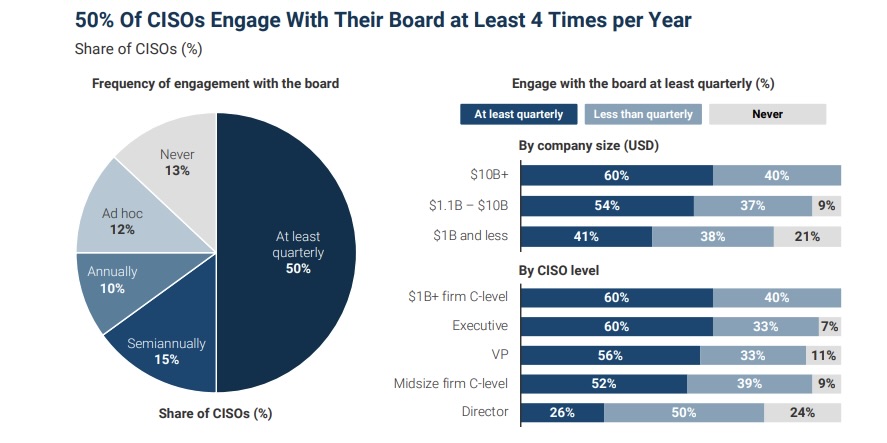
(Source: “State of the CISO, 2023–2024 Benchmark Report” from IANS Research and Artico Search, January 2024)
- Job satisfaction fell and the desire to switch jobs increased compared with 2022, a sign of increased anxiety. A factor in CISO satisfaction is their access to the board – only 28% of those without board engagement are satisfied, compared with 57% of those with at least infrequent board engagement
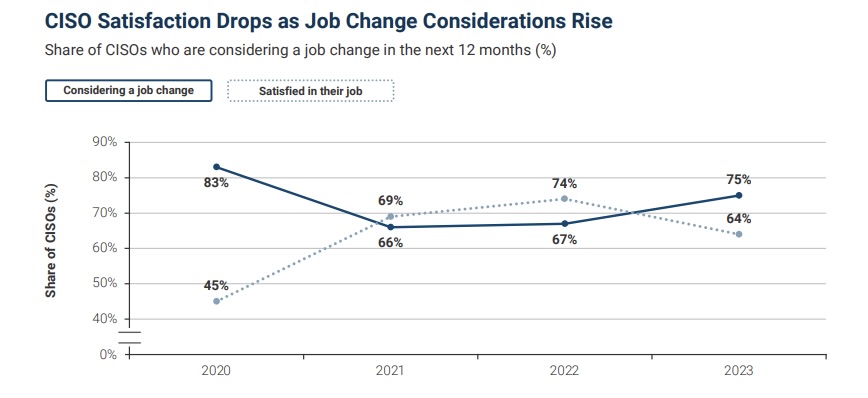
(Source: “State of the CISO, 2023–2024 Benchmark Report” from IANS Research and Artico Search, January 2024)
For more information about current CISO challenges and opportunities:
- “A tougher balancing act in 2024, the year of the CISO” (CSO Online)
- “CISO Planning for 2024 May Struggle When It Comes to AI” (Dark Reading)
- “Navigating CISOs' top 4 challenges” (Security Magazine)
- “Why 2024 will be the year of the CISO” (CSO Online)
- “CISOs’ crucial role in aligning security goals with enterprise expectations” (Help Net Security)
VIDEOS
CISO 2024 Predictions (CDM Media)
Achievements and Aspirations: Reflecting on 2023 and Predicting 2024 (CISO Global)
3 - Water treatment plants get guidance for incident response
A big target for cyber attackers, water and wastewater treatment organizations must have solid cyber incident response plans and capabilities. That’s why CISA, the FBI and the Environmental Protection Agency this week published the “Water and Wastewater Sector - Incident Response Guide.”
The 27-page document offers these critical infrastructure organizations a set of best practices for responding to cyberattacks; guidance for reporting cyber incidents; and information about available resources from the federal government.
The guide covers these core stages of incident response:
- Preparation, which includes having an incident response plan in place
- Detection and analysis, to accurately and quickly assess the scope and impact of an incident
- Containment, eradication and recovery
- Post-incident tasks, such as retaining evidence, using collected data and documenting lessons learned

The water and wastewater systems sector (WSS) faces significant cybers resilience challenges, including the need to comply with a mix of federal, state and local regulations; uneven cyber maturity levels among operators; and often insufficient cybersecurity resources.
“In the new year, CISA will continue to focus on taking every action possible to support ‘target-rich, cyber-poor’ entities like WWS utilities,” CISA Executive Assistant Director for Cybersecurity, Eric Goldstein said in a statement.
More than 25 partners contributed to the guide, including Tenable.
To get more details, read the announcement “CISA, FBI and EPA Release Incident Response Guide for Water and Wastewater Systems Sector” and the “Water and Wastewater Sector - Incident Response Guide.”
For more information about the cybersecurity of water plants:
- “Navigating Federal Cybersecurity Recommendations for Public Water Utilities” (Tenable)
- “Authorities raise alarm on threats against water, other critical sectors” (Cybersecurity Dive)
- “States and Congress wrestle with cybersecurity after Iran attacks small town water utilities” (Associates Press)
- “Your Water Supply is Under Cyber Attack” (HackerNoon)
VIDEO
Cyber group backed by Iran is taking credit for Pennsylvania water system cyberattack (ABC News)
4 - Report: Facial recognition lacks regulatory, legal guardrails
The U.S. urgently needs laws and regulations to govern the use of facial recognition technology, whose use has ballooned with little guidance over how to develop and deploy it responsibly to prevent abuses.
That’s the main takeaway from the National Academies of Sciences, Engineering and Medicine’s “Facial Recognition Technology: Current Capabilities, Future Prospects and Governance” report, published this week.
“Facial recognition technology generates novel and complex legal challenges and raises a variety of distinct, unsettled legal questions,” Jennifer Mnookin, co-chair of the committee that authored the report, said in a statement.
“It also raises complicated social questions about privacy and public and private surveillance, given the highly personal implications of the technology,” added Mnookin, who is chancellor of the University of Wisconsin-Madison.
Specifically, the report, which was sponsored by the U.S. Department of Homeland Security and the FBI, raises concerns around potential harm to people’s privacy and civil liberties from misuse of facial recognition tools, which increasingly are:
- Easy and inexpensive to deploy
- Managed by inexperienced and untrained operators
- Used for surveillance
- Less accurate for certain demographic groups
- The key to unlock a treasure trove of personal information
Recommendations include:
- The creation of a program for facial recognition technology testing and evaluation by the U.S. National Institute of Standards and Technology to improve accuracy and reduce bias
- A collaboration between the U.S. federal government and standards organizations to create industry-wide standards for facial recognition tools, in areas like performance, accuracy and data security
- The creation by the U.S. Department of Justice and U.S. Department of Homeland Security of a multi-disciplinary working group to establish guidelines for responsible law-enforcement use of facial recognition
- Adoption of a risk management framework by developers and deployers of facial recognition technology to assess appropriate use of facial recognition technology
- The publication of an executive order by the White House addressing responsible use of facial recognition technology by federal agencies and departments
- The passing of new federal laws to address concerns around facial recognition technology, limit its potential harms and prevent its misuse
The National Academies of Sciences, Engineering, and Medicine is a private, nongovernmental organization created by the U.S. Congress to provide independent, objective advice on technology, medicine and science issues.
For more information about the risks of facial recognition technology:
- “Rite Aid hit with five-year facial recognition ban over ‘reckless’ use” (The Verge)
- “TSA is testing facial recognition at U.S. airports. Here's what that means for you” (ZDNet)
- “Is Facial Recognition Technology Becoming a Privacy Risk?” (MakeUseOf)
- “Facial Recognition Software Is Everywhere, With Few Legal Limits” (Bloomberg)
- “Cops cuff pregnant woman for carjacking after facial recog gets it wrong, again” (The Register)
5 - Check out our ad-hoc poll on cloud security trends
During Tenable’s recent webinar “When, Why, and How Your Security Team Needs to Harness the Power of CNAPPs,” we took the opportunity to poll the audience about several cloud topics. Check out what they said about their cloud security challenges, app delivery models and security provider roster.
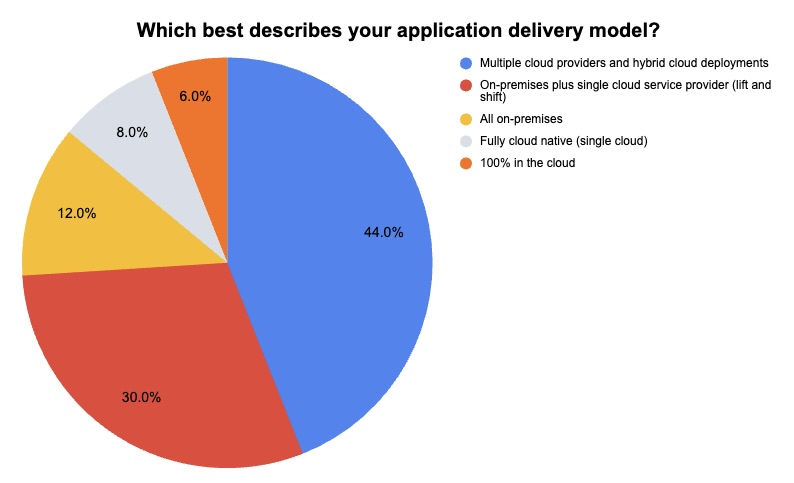
(50 respondents polled by Tenable, January 2024)
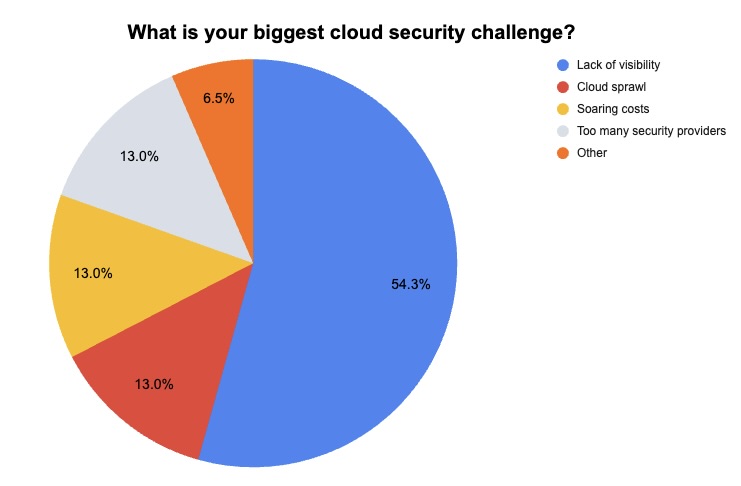
(46 respondents polled by Tenable, January 2024)
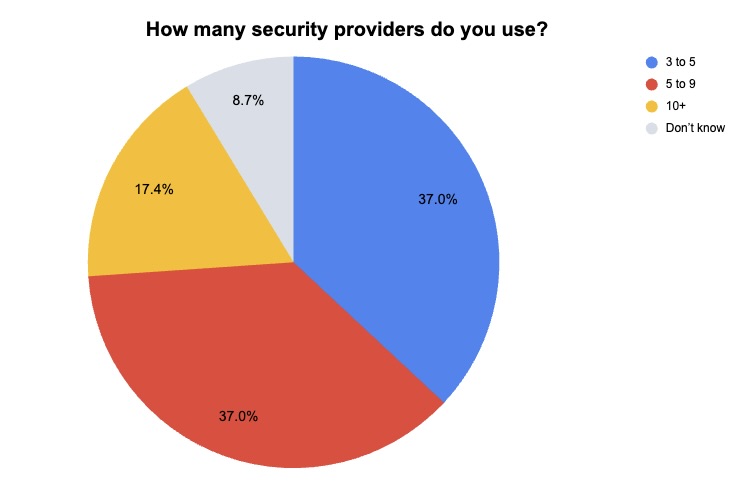
(46 respondents polled by Tenable, January 2024)
Want to get all the insights offered during the webinar about leveraging cloud native application protection platforms (CNAPPs) to improve security, agility and competitiveness? Watch it on demand!
6 - CISA and FBI issue warning about Androxgh0st malware
Is the Androxgh0st malware on your radar screen? A new advisory published this week by CISA and the FBI detail Androxgh0st indicators of compromise; techniques, tactics and procedures; and mitigation strategies.
“Androxgh0st malware establishes a botnet for victim identification and exploitation in vulnerable networks, and targets files that contain confidential information, such as credentials, for various high profile applications,” reads a CISA-FBI alert.
Specifically, attackers using Androxgh0st have been observed exploiting these vulnerabilities which can lead to remote code execution:
- CVE-2017-9841 (PHPUnit testing framework)
- CVE-2018-15133 (Laravel web application framework)
- CVE-2021-41773 (Apache web server)
“Androxgh0st malware also supports numerous functions capable of abusing the Simple Mail Transfer Protocol (SMTP), such as scanning and exploiting exposed credentials and application programming interfaces (APIs), and web shell deployment,” reads the advisory.
Mitigation recommendations include:
- Keep all operating systems, software and firmware updated, and prioritize patching known exploited vulnerabilities in internet-facing systems. Specifically make sure your Apache servers are not running versions 2.4.49 or 2.4.50.
- Ensure that all uniform resource identifiers (URIs) are configured by default to deny all requests.
- Make sure your live Laravel applications are not in debug or testing mode, and remove all cloud credentials from .env files.
- Scan servers’ file systems for unrecognized PHP files.
To get more details, read:
- The joint CISA-FBI alert “CISA and FBI Release Known IOCs Associated with Androxgh0st Malware”
- The joint CISA-FBI advisory “Known Indicators of Compromise Associated with Androxgh0st Malware”

Juan Perez
Juan has been writing about IT since the mid-1990s, first as a reporter and editor, and now as a content marketer. He spent the bulk of his journalism career at International Data Group’s IDG News Service, a tech news wire service where he held various positions over the years, including Senior Editor and News Editor. His content marketing journey began at Qualys, with stops at Moogsoft and JFrog. As a content marketer, he's helped plan, write and edit the whole gamut of content assets, including blog posts, case studies, e-books, product briefs and white papers, while supporting a wide variety of teams, including product marketing, demand generation, corporate communications, and events.
如有侵权请联系:admin#unsafe.sh