An ongoing campaign targeting LinkedIn accounts has led to victims losing control of their accounts, or being locked out following repeated login attempts.
Whether the attackers are using brute force methods or credential stuffing isn't known, but because some victims are being being locked out following a great number of failed attempts, you might suspect brute force methods. It’s also not unthinkable that the attackers are using a combination of attack methods. Credential stuffing is a popular tactic of attempting to access online accounts using username-password combinations acquired from breached data. In a brute force attack attackers typically try a lot of common passwords.
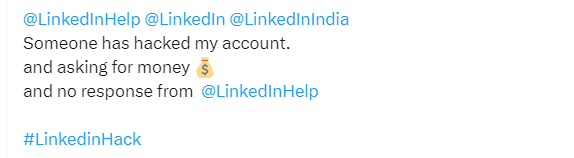
Either way, victims are complaining about slow response times.
The campaign is targeting LinkedIn users all over the world. It pressures the victims that have lost control of their accounts into paying a ransom to avoid having their accounts deleted by the attackers.

The X account of LinkedIn Help is swamped with similar messages
Victims are usually made aware of the take-over by a notification that the email address associated with their account has changed. In many of the examples we saw the new email address was linked to the Russian “rambler.ru” service. This does not necessarily mean the attack is originating from Russia, but it’s not unthinkable that the accounts will be used in disinformation campaigns. According to one victim we spoke to the attackers added fake accounts to their connections.
But the accounts could also be used to distribute malware, phishing campaigns, or other types of fraud. And if that’s the case, the deletion of the account sounds better to me than having your reputation damaged.
From complaints seen by BleepingComputer, LinkedIn support has not been helpful in recovering the breached accounts, with users just getting frustrated by the lack of response.
The LinkedIn Help account has pinned a message to say:
“Hey there! 👋 We're experiencing an uptick in questions from our members, causing longer reply times. Rest assured, we're doing our best to assist you! For account-specific inquiries, please DM us the details and your email address. We appreciate your patience. Thanks! 🙌”
The best defence against brute force attacks, credential stuffing, and other password attacks, is to set up two-step verification.
Setting up MFA for LinkedIn with Okta turned out to be painful because LinkedIn does not provide a QR code but a secret key which is so long that it’s hard to get it right the first, or second time. But since it’s safer than using the SMS 2FA, this is how it’s done:
- Open Settings & Privacy
- Under Sign in & security
- Select Two-step verification
- Set the option to on and you will be presented with two choices
- Choose the Authenticator app method and follow the instructions from there
You will receive an email confirming the change that tells you: From now on, you can use your authenticator app to get a verification code whenever you want to sign in from a new device or browser.
Malwarebytes EDR and MDR removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.