Attackers believed to have ties to Russia's Foreign Intelligence Service (SVR) are using Microsoft Teams chats as credential theft phishing lures. Microsoft Threat Intelligence has posted details about the perceived attacks targeted at fewer than 40 unique global organizations. The targeted organizations are mostly found among government, non-government organizations (NGOs), IT services, technology, discrete manufacturing, and media sectors.
According to Microsoft the attackers are part of the same group that was behind the attacks against SolarWinds, the Sunburst backdoor, TEARDROP malware, GoldMax malware, and other related components. Malwarebytes tracks that group as APT29/Cozy Bear. A group well-known for finding and deploying novel tactics, techniques, and procedures (TTPs).
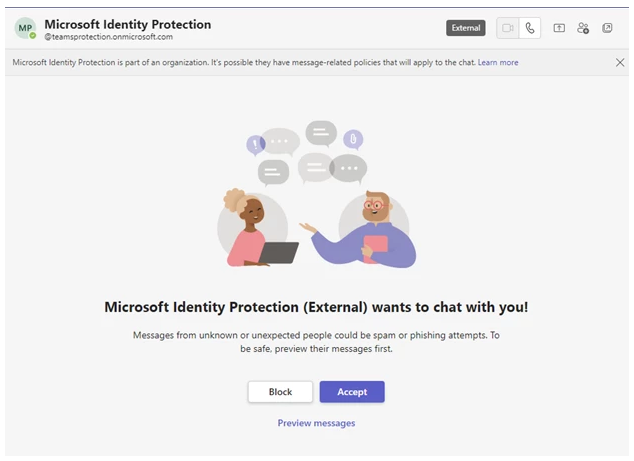
In the phishing attacks the group leverages previously compromised Microsoft 365 instances, mostly owned by small businesses, to create new domains that look like technical support accounts. From these instances the group reaches out through Teams messages and persuades targets to approve multi-factor authentication (MFA) prompts initiated by the attacker.
The compromised instances are renamed and used to set up a new onmicrosoft.com subdomain. Onmicrosoft.com domains are legitimate Microsoft domains which are automatically used by Microsoft 365 for fallback purposes in case a custom domain is not created.
The attackers often use security terms or product-specific names in these subdomain names to give credibility to the technical support themed messages which are sent out as a lure.
 example image courtesy of Microsoft
example image courtesy of Microsoft
The objective is to target users with passwordless authentication configured on their account, or accounts for which they have obtained credentials previously. In both cases they require the user to enter a code that is displayed during the authentication flow into the prompt on the Microsoft Authenticator app on their mobile device.
Once the target has done this, the attacker can use the gained access to further compromise the account. Typically, this involves information theft from the now compromised Microsoft 365 tenant. In some cases, the actor attempts to add a device to the organization as a managed device via Microsoft Entra ID (formerly Azure Active Directory), likely an attempt to circumvent conditional access policies configured to restrict access to specific resources to managed devices only.
Microsoft says it has successfully blocked the Russian threat group from utilizing the compromised instances in other attacks and is now actively working to address and limit the impact of the campaign.
How to avoid tech support scammers
In the blog Microsoft provides a very important ground rule to remember: Authentication requests not initiated by the user should be treated as malicious.
As a security provider with a good reputation, we do get a lot of impersonators. Maybe we should be flattered, but frankly we are annoyed. So here are a few tell-tale signs that you are dealing with an impersonator:
- The company gives you any name at all other than Malwarebytes. Malwarebytes does not outsource support. We have our own Support team. There are no third parties “authorized” to provide support. Nobody is “licensed” to use our name, logo, or any other intellectual property.
- The company can’t or won't take your credit card the first time you ask. Reputable organizations don’t do this. Period. Malwarebytes has a credit card processor that takes payments for all transactions. Credit card processors do things like vet clients for risk, fraud, and abuse. So any company having trouble doing business with one, probably fits into one of those three categories. Credit cards also have reasonably robust consumer fraud protection, so if you’re being steered away from using one, that is also a red flag that the company is about to do something they probably shouldn’t.
- The company makes outbound support calls. Malwarebytes, and Microsoft, do not do this. Tech support companies that make outbound unsolicited calls tend to do so because they bought your personal information from a data broker who classified you as a vulnerable target. How would they know you have a problem with your computer? How would they even know you own a computer? Generally speaking, if someone calls you out of the blue claiming your computer has a problem, hang up.
Malwarebytes EDR and MDR removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.