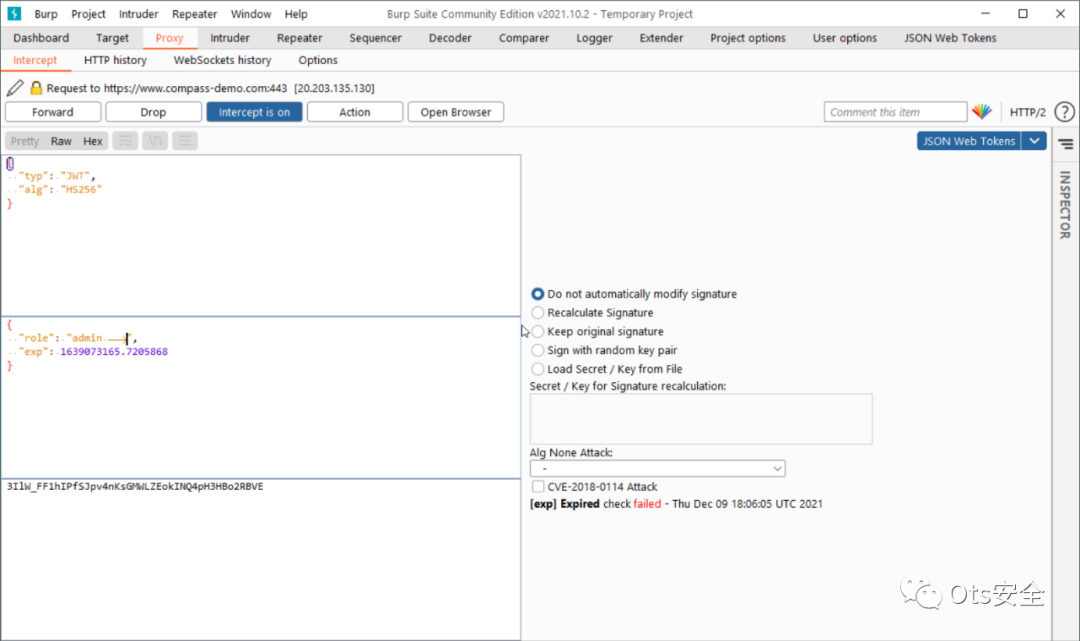
JSON Web 令牌 (JWT) 支持 Burp 拦截代理。JWT4B 将允许您即时操作 JWT,自动执行针对 JWT 的常见攻击,并在代理历史记录中为您解码。JWT4B 自动检测“授权承载”标头形式的 JWT 以及可自定义的帖子正文参数和正文内容。
以下 url 包含指向四个页面的链接,这些页面模拟通过 XHR 或作为 cookie 发送的 JWT。 https://oz-web.com/jwt/
将在“%user.home%.JWT4B\config.json”下创建一个配置文件,内容如下:
{"resetEditor": true,"highlightColor": "blue","interceptComment": "Contains a JWT","jwtKeywords": ["Authorization: Bearer","Authorization: bearer","authorization: Bearer","authorization: bearer"],"tokenKeywords": ["id_token","ID_TOKEN","access_token","token"],"cveAttackModePublicKey": "MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAuNCJ/1Tawe8DUIbQDxjRr+bVSoIdcOjJm5wskbMUjHopTWERzLo65yLPjCVcRudQ8DNJIs3yb+hzxi0b8uyKXK6nYTaxdwtRN61NMgI/ecNYw1A3nMLRJ4KetLCUqCehVV+OavJqwGXb0k4OhJu7VefLD9PxOQxLd/MxJLMTChqYYQWY069oNTB9uRaBRLwcEv3i8uiM3HAdx4di0FZLHN5yAt6Zq7TR53CUDSI74q/AH4zeuo+D/UscVTq2bInfJmN3NdA6XqPdjnu6DtT7VQZif+06sFXgnoieuUaeRE0Jn8ZY72hljToFZmsLUPPhTSzmFTgko4+MGnS29w1rbQIDAQAB","cveAttackModePrivateKey": "MIIEvwIBADANBgkqhkiG9w0BAQEFAASCBKkwggSlAgEAAoIBAQC40In/VNrB7wNQhtAPGNGv5tVKgh1w6MmbnCyRsxSMeilNYRHMujrnIs+MJVxG51DwM0kizfJv6HPGLRvy7IpcrqdhNrF3C1E3rU0yAj95w1jDUDecwtEngp60sJSoJ6FVX45q8mrAZdvSTg6Em7tV58sP0/E5DEt38zEksxMKGphhBZjTr2g1MH25FoFEvBwS/eLy6IzccB3Hh2LQVksc3nIC3pmrtNHncJQNIjvir8AfjN66j4P9SxxVOrZsid8mY3c10Dpeo92Oe7oO1PtVBmJ/7TqwVeCeiJ65Rp5ETQmfxljvaGWNOgVmawtQ8+FNLOYVOCSjj4wadLb3DWttAgMBAAECggEBALF/J2ngNxEW2loWf/Bf59NGoQakHF56VFZtEakFEvEvykcUuSGkojmmhyqUHyHBu0xWFSGmJfcwizCD1lnir6f/3aVR//LTHbeZa5Bh9FCfOrqqah7WREXr/zyOctdk6F+0HHW+SKRrr0k1yl+1qaABtFaJOR2PH1Qebs5OZjTGXvKtm5H7G4FeNPDjprCKB5vRiWPY5F3sRJOFp8TwkH5qbirgZh0KJiYuJMq9QtzjRHYjzALOSWldpqb8Xzcx7lHZbF8gNv3zeRJRJWTYATq8KVaZ3fs0mv9z37MPRC1AS9v4ylrwXsAviWvn21Q6E1jrxOxZfAhkoA2aLtFMr4kCgYEA68yc8mupFsRCwcfChauAExibU2lCmW1ImcWxGLQR0dVPyaEPlecwKxvdetWs7BPaxqogKppB71gsxXYASUntgwj1f7zXxo4rdSZv20B09eASo+I8qZpfDZWR1oM7HjXR40lWELtQhzD0QDQCUmQtCpVGgyheqPsrQntCeM5LEisCgYEAyKXD93Onevtg6K2GWmnIgCP8+PRvu9kYW+3yhN0BGzmJrVSlD6uw0SAsA7awd54Qs00gGcWoztDm7V+YHDcYy3oOzwip4Yw2S3kUPewupySLm1VrDBMdXVp1sQH/I5DE3B4c5OxgdCmiX+7hLkXBBjpOqbHS+2bsPs9qnO2M5McCgYAhj84G8yvuAaE+05/sRqzECwyQorrH+7YJrQm36mle5G2m1TXSsEU63Yx4n1EtiOXqwOwzJCGeX35/3HvN8qfLrsrCk65ipHmrAv2Ix3PeSzZb/SeFPGOrG07WqXcQpbhqEVYeq4qas20QdlaeQ4PlrbmLkYNnqdhObhzX9QTaYQKBgQDDa9/fpL8cIrWSKV/Ps3PaijKa7sfcd2coMiqgiPfI4lNbhDN3fcsrA2CbBVX+Su8NEzMOptrxA7nGu/JUmL0HgQvnTRLYYE2JWJYEcYJGvGtUkO8/xWY2RCKYkc9Dfn6dvJ57wFV5Dgvdz7V18e47+JIg6NcKkIXL7wxxZ1RwhQKBgQDd4nlMdJue4zA7hO2YGxUqX+ALVY6ikZ/SBOQIDrnI9aixwXYQ3t3Nwjim73/0uiLXLOpO92dBSym7GeSPYqWZhkyQ8C05tDyGvDI5b7bVmD1pxmnhG9sOktrkDVkOsYUnAhRwCgmuExkoeGWPvUt+85cmMpJfHHqbrb5FLqTeXQ=="}
更改配置需要重新加载扩展或 BURP。如果你搞砸了,只需删除该文件,它将使用默认值重新创建。注意:如果 resetEditor 设置为 false,则不会为每个新请求重置所有选项,例如 re-singing 和 alg attack。这在中继器中工作时可能很有用。
构建您自己的版本(使用 Eclipse)
克隆存储库并创建新的 Eclipse Java 项目
右键单击 -> 配置 -> 转换为 Maven 项目(下载所有需要的库)
打开Burp -> Extender -> APIs -> 保存接口文件 -> 将所有文件复制到JWT4B\src\burp
导出可运行的 fat JAR,包括库
通过 Extender Tab -> Extensions -> Add 在 Burp 中加载 JAR(提示:CTRL+单击扩展以重新加载它)
文章来源: http://mp.weixin.qq.com/s?__biz=MzAxMjYyMzkwOA==&mid=2247496372&idx=3&sn=33ba78265c95db612f336ccc27d1f491&chksm=9badbbffacda32e9cda99172cd00afd849be04dac411fc60b3cec0334ef7ce58c713a56251d4#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh