0x01 恶意文件
动调动调
OD直接动调,更具xxx的流程图可以看到程序的整体结构,然后结合流程图使用OD动调
最终ip地址是存在了[ebp+ecx-0x14]的位置


将这一处跳转和两处的exit nop掉
跟踪到[ebp+ecx-0x14]在内存中的位置,一直F8就可以了


这里是端口,小端排序 1F 57,转换成十进制就是8023,前边在存储ip地址的时候就已经存到[ebp-0x1D0]的位置了,所以最终ip:1.15.228.170:8023
flag{1.15.228.170:8023}
0x02 攻击行为还原
FlaG.txt有密文
c=1566077545968868311749088444723100549024925747577903610033503
Id_rsa有
-----n=1606938044309278499168642398192229212629290234347717645487123-----
-----e=65537-----
在线分解n

#coding:utf-8
import binascii
from libnum import n2s,s2n
import base64
def gcd(a, b):
if a < b:
a, b = b, a
while b != 0:
temp = a % b
a = b
b = temp
return adef egcd(a, b):
if a == 0:
return (b, 0, 1)
else:
g, y, x = egcd(b % a, a)
return (g, x - (b // a) * y, y)
def modinv(a, m):
g, x, y = egcd(a, m)
if g != 1:
raise Exception('modular inverse does not exist')
else:
return x % m
p = 1267650600235241044365044382487
q = 1267650600260888172240281085029
e = 65537
# tmp = base64.b64decode("qzogS7X8M3ZOpkUhJJcbukaRduLyqHAPblmabaYS**iatuulrHcEpBmil7V40N7gbsQXwYx5EBH5r5V2HRcEIOXjgfk5vpGLjPVxBLyXh2DajHPX6KvbFpQ8jNpCQbUNq8Hst00yDSO/6ri9dk6bk7+uyuN0b2K1bNG5St6sCQ4qYEA3xJbsHFvMqtvUdhMiqO7tNCUVTKZdN7iFvSJqK2IHosIf7FqO24zkHZpHi31sYU7pcgYEaGkVaKs8pjq6nbnffr4URfoexZHeQtq5UAkr95zD6WgvGcxaTDKafFntboX9GR9VUZnHePiio7nJ3msfue5rkIbISjmGCAlj+w==")
# =
d = modinv(e, (p - 1) * (q - 1))
# c=s2n(tmp)
c = 1566077545968868311749088444723100549024925747577903610033503
#c = 225031483444634056931067907865853799650197225351377050632290334721073031287701730297815850654473721939907812470206115171738967740183098960272963323728747481560137205796840356532306950935686580268408289864109695494835661414073083573249882362332920722000099781994315336570711188934565379141406727420346806389405536474102730682155998263607095718543239272202402139286809779368710600842078606046563228470023546348908618719147790859257980882643030144242048154566691808688844513142261099020381730517293884263384819159874220288293023868919557980548807831273449743064237407705987056818011286315950476959812697067649075359373253
n = p*q
m=pow(c,d,n)
print n2s(m)

后半段直接google
没想到真对了,非预期。
flag{SSH_Brute_Force}
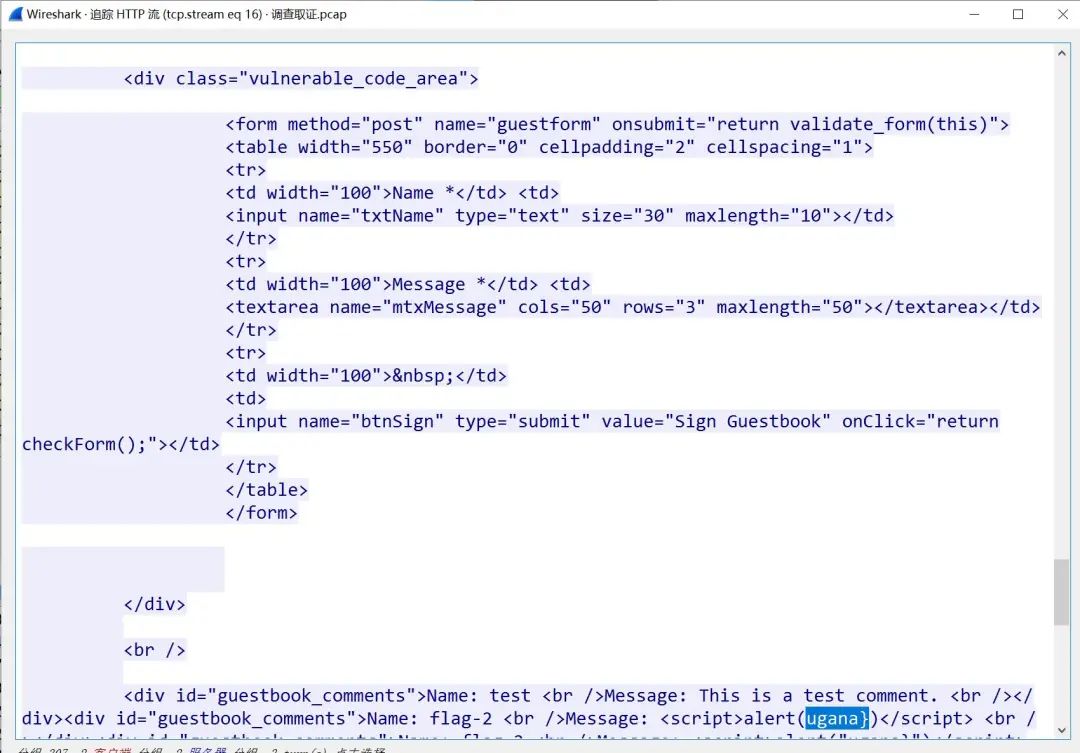
0x03 留痕取证
前半段

凯撒密码解密

后半段

flag{bufujiugana}
0x04 漏洞挖掘
Linux运行随便输个密码

Base16+栅栏解密得到flag
flag{d5000loginpassis[email protected]}
0x05 密文破解
根据残缺的密文和MD5写脚本爆破
s = '[email protected]#$%^&*`~()_+-=[]{};:,.<>?/'"\|'
for i in s:
for j in s:
for k in s:
for l in s:
for m in s:
#print(1)
md5 = hashlib.md5()
c = str(i) + '1_1001_10_600_600_' + str(j) + str(k) + '00' + str(l) + str(m) + '7_202103301539'
#print(c)
md5.update(c.encode('utf-8'))
d = md5.hexdigest()
#print(c)
if d[:4] == 'b9fd' and d[6:9] =='9d5':
print(c)
print(d)

flag{1500.87}
0x06 文件格式分析
使用binwalk查看文件发现文件是一个zip压缩包,于是使用010editor修改文件头为504B,修改后缀为zip并解压文件,解压后打开文件

使用basecrack工具进行解码,得到flag

flag{W3lc0Me_t0_Xinx1}
E
N
D
本文作者:TideSec
本文为安全脉搏专栏作者发布,转载请注明:https://www.secpulse.com/archives/190144.html
如有侵权请联系:admin#unsafe.sh